Risky Bulletin: New malware tries to sabotage Israel's water system but fails because it's buggy
In other news: US government wants Mythos access; Supreme Court hacker gets no prison time; ransomware kingpin arrested in Kazakhstan.

This newsletter is brought to you by Nebulock. You can subscribe to an audio version of this newsletter as a podcast by searching for "Risky Business" in your podcatcher or subscribing via this RSS feed. You can also add the Risky Business newsletter as a Preferred Source to your Google search results by going here.
Security researchers at British security firm Darktrace have found a new and interesting piece of malware that was specifically designed to infect and sabotage the operations of Israel's national water management network.
Named ZionSiphon, the malware is one of the rare malware strains created to target operational technology (OT), which are the type of networks from which staff manage industrial equipment.
The malware is a very targeted operation that only works inside networks hosted on Israeli IP address ranges and where the malware finds specific text strings containing the names of common Israeli companies that manage water treatment and desalination systems.
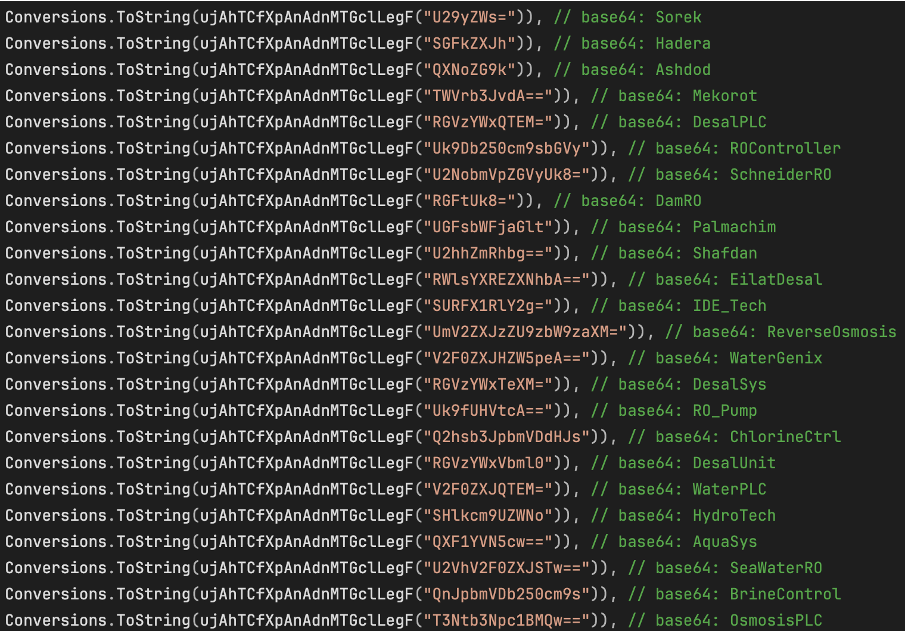
If those two conditions are met, the malware scans for a list of hardcoded directories or files that are specific to OT software used to manage equipment in water management and desalination plants.
Once a match is made, ZionSiphon loads a preset config that tells equipment to adjust water pump pressure and chlorine levels at maxhigh settings.
Although the malware appears to work based on sound logic, Darktrace says ZionSiphon doesn't trigger properly due to a bug in the functions that check if a victim's IP address is in Israel's assigned range.
This check fails due to a XOR encoding error and the malware deletes itself thinking it infected a network outside Israel.
ZionSiphone also contains two politically motivated strings, shown below.
"In support of our brothers in Iran, Palestine, and Yemen against Zionist aggression. I am "0xICS"
"Poisoning the population of Tel Aviv and Haifa"
While Darktrace hasn't attributed the malware to anyone, there is a pretty high chance this is the work of Iranian hackers. Iranian cyberattacks against Israel's water companies have happened since at least 2020, when several attacks prompted the country's cybersecurity agency to warn water utilities and ensure their OT and ICS equipment wasn't sitting exposed online without passwords or running default creds.
It is also unclear from the Darktrace write-up if the malware was ever used in the wild, or if this is a sample found on VirusTotal that may have been vibe-coded or still under development.
Risky Business Podcasts
The main Risky Business podcast is now on YouTube with video versions of our recent episodes. Below is our latest weekly show with Pat, Adam, and James at the helm!
Breaches, hacks, and security incidents
Vercel discloses data breach: Hackers have breached cloud hosting platform Vercel and are now selling some of its customers' data online. Vercel confirmed the breach on Sunday and notified a small number of affected customers. It also recommended that customers change their keys and secrets. The ShinyHunters group took credit for the incident in a forum post over the weekend.
Kelp DAO hacked for $292m: Hackers have stolen $292 million worth of crypto assets from the Kelp DAO cryptocurrency platform. The attackers exploited a vulnerability in the platform to withdraw the funds as rsETH (restaked Ether) tokens. The exploit is now the largest crypto-heist of the year (so far). [The Block]
Rhea Finance hacked for $18.4m: Hackers have stolen $18.4 million worth of assets from the Rhea Finance DeFi platform. The attack exploited vulnerabilities in the protocol's margin trading feature. The hackers prepared the attack in advance for days by creating fake token pools on the platform through which operations were routed.
Tallahassee down after cyberattack: Florida capital city Tallahassee has shut down its IT network after a mysterious cyberattack on Friday. Several city websites and public services are still unavailable. The surrounding Leon county has disconnected its IT network from the city to prevent any contamination, which is typical lingo used for ransomware incidents. [DysruptionHub]
BlueSky confirms DDoS attack: BlueSky says a sophisticated DDoS attack was the cause of its prolonged outage last week. The attack caused the platform to operate intermittently for almost a day. Other DDoS attacks continued throughout the week, but failed to bring down the site again.
Our team received a report of intermittent app outages at about 11:40pm PDT on April 15, 2026. They worked through the night to mitigate a sophisticated Distributed Denial-of-Service (DDoS) attack, which intensified throughout the day.
— Bluesky (@bsky.app) 2026-04-16T23:47:25.963Z
General tech and privacy
Old companies are selling their internal chats: Old failed startups are selling their internal emails, JIRA tickets, and Slack chats to AI companies as training data. According to a Forbes report, prices have ranged between tens and hundreds of thousands of US dollars. Most of these transactions have been arranged through a platform named SimpleClosure. [Forbes]
Sandboxed GPU process coming to Firefox: The Firefox web browser will replace its GPU component with a sandboxed process in an update later this year. The new component will enhance the browser's security posture against attacks that seek to compromise the browser through malicious graphic assets. The component will be available for Firefox versions on all operating systems.
Botched IT upgrade hurts Mississippi drinkers: A botched IT upgrade at the only liquor distribution warehouse in Mississippi is disrupting alcohol delivery for the entire state. [The Times of India]
DOJ denies France's probe into X and Musk: The US Department of Justice told French law enforcement it will not assist their investigation into social media platform X. The DOJ called the investigation an attack on the free speech of American citizens. France raided Twitter's Paris offices in February as part of an investigation into Grok producing sexual imagery of young children. Ah yes, producing naked images of children is free speech. Sorry I missed the memo, 'murica! [CNBC]
DRAM shortage: DRAM produced this year will only cover 60% of the demand, and the current shortage is expected to go into next year as well. [The Verge]
Government, politics, and policy
EU tells Google to share search data: The EU has told Google to share its search engine data with other search engines, as required by the EU Digital Markets Act. In a statement, Google said it will not, since it can't guarantee that third-parties will honor privacy commitments.
Russia introduces mandatory border device searches: The Russian government has granted border agents the power to search travelers' electronic devices. Travelers entering or leaving Russia must provide passwords when requested. Individuals who refuse a search risk fines and arrest for up to 15 days. [Vesti26 // Caliber.az]
US wants Mythos access: The US government is in private talks with Anthropic to gain access to its new Mythos cybersecurity AI agent. Officials want to deploy Mythos on government networks to identify security weaknesses. The White House is holding talks with Anthropic even though it designated the company a supply chain risk last month after Anthropic refused to let its AI tools be used for war operations. [Axios]
Parents Decide Act: US lawmakers have introduced a bill that will require operating system providers to verify the age of any user. The Parents Decide Act will require OS makers to verify the age of any new account created on a device. The Congress bill echoes similar bills proposed in states like California and Colorado. It is part of an international push to have users' ages.
FISA S702 gets a 10-day extension: Congress has passed a ten-day extension to the FISA Section 702 surveillance clause. FISA surveillance powers were set to expire on Monday, April 20. They have now been extended until the end of the month. Lawmakers passed the short extension after negotiations to renew FISA for five more years failed last week. [House, Senate]
Sponsor section
In this Risky Business sponsor interview, Catalin Cimpanu talks with Sydney Marrone, Head of Threat Hunting at Nebulock, about hunting shadow AI agents on corporate networks.
Arrests, cybercrime, and threat intel
DraftKings hacker sentenced to prison: A Tennessee man has been sentenced to 30 months in prison for hacking sports betting website DraftKings. Kamerin Stokes was part of a three-man group that launched credential-stuffing attacks against DraftKings in November 2022. Stokes went online as TheMFNPlug and operated an online shop where the group sold the hacked accounts. He was also sentenced to three years of supervised release, will forfeit and return some of the money he made in the scheme.
Supreme Court hacker gets probation: A Tennessee man who hacked the US Supreme Court was sentenced to twelve months of probation. Nicholas Moore hacked the US' highest court in 2023 and leaked documents on an Instagram account named @ihackthegovernment. He was detained and immediately pleaded guilty this January. [The Hill]
Kazakh man arrested for ransomware attacks: Kazakhstani authorities have arrested a resident of Almaty for carrying out ransomware attacks. The suspect was arrested after being identified by South Korean police after attacks against local hospitals and apartment complexes. The suspect was identified as a man in his 30s and a leader of a ransomware group active since 2022. South Korean police are planning to release decryption tools for other victims. [Newsis // Maeil Business]
There’s footage of the raid on his home here youtu.be/jXZcng1_Pd0?...
— —>realhackhistory.org (@bsky.realhackhistory.org) 2026-04-19T13:28:08.138Z
Scattered Spider member pleads guilty: A Scottish man has pleaded guilty to hacking and stealing more than $8 million. Tyler Robert Buchanan carried out the hacks while a member of the Scattered Spider hacking group. Him and accomplices hacked telcos, tech companies, and cloud providers in 2023. They used the access to hack individual customer accounts, bypass 2FA, and hijack cryptocurrency wallets.
TeamPCP+Vect=Love: The TeamPCP hacking group is feeding credentials stolen in the Trivy and Checkmarx KICS supply chain attacks to the Vect ransomware group. The credentials are being used to breach large corporate networks, deploy ransomware, and ask for huge ransoms. The TeamPCP group hinted last month it would team up with a ransomware group to speed up extortions. [Dataminr // KELA]
South Korea warns of Midnight, Endpoint ransomware attacks: South Korea's national police has published a cybersecurity advisory, warning SMBs about ransomware attacks against their networks. The advisory specifically warns about attacks with the Midnight and Endpoint ransomware families.
DPRK IT worker scheme evolution: North Korea is recruiting individuals in other geographical areas for its remote IT worker schemes. Security firm Flare has found evidence of recruitment in Iran, Syria, Lebanon, and Saudi Arabia. This appears to be an effort to diversify the remote worker fleet as companies are now cautious when hiring Asians.
notnullOSX interview: Threat intelligence analyst g0njxa has published an interview with the developer of the notnullOSX macOS infostealer.
Ashab al-Yamin profile: DarkOwl has published a profile on Harakat Ashab al-Yamin al-Islamia, a new pro-Iranian hacktivist group active on Telegram. The group claimed a cyberattack on LA Metro last month.
World Leaks profile: Breachcache looks at how the World Leaks group breaches networks via exposed RDP endpoints, steals data, and then ransoms the victim using its dark web leak site.
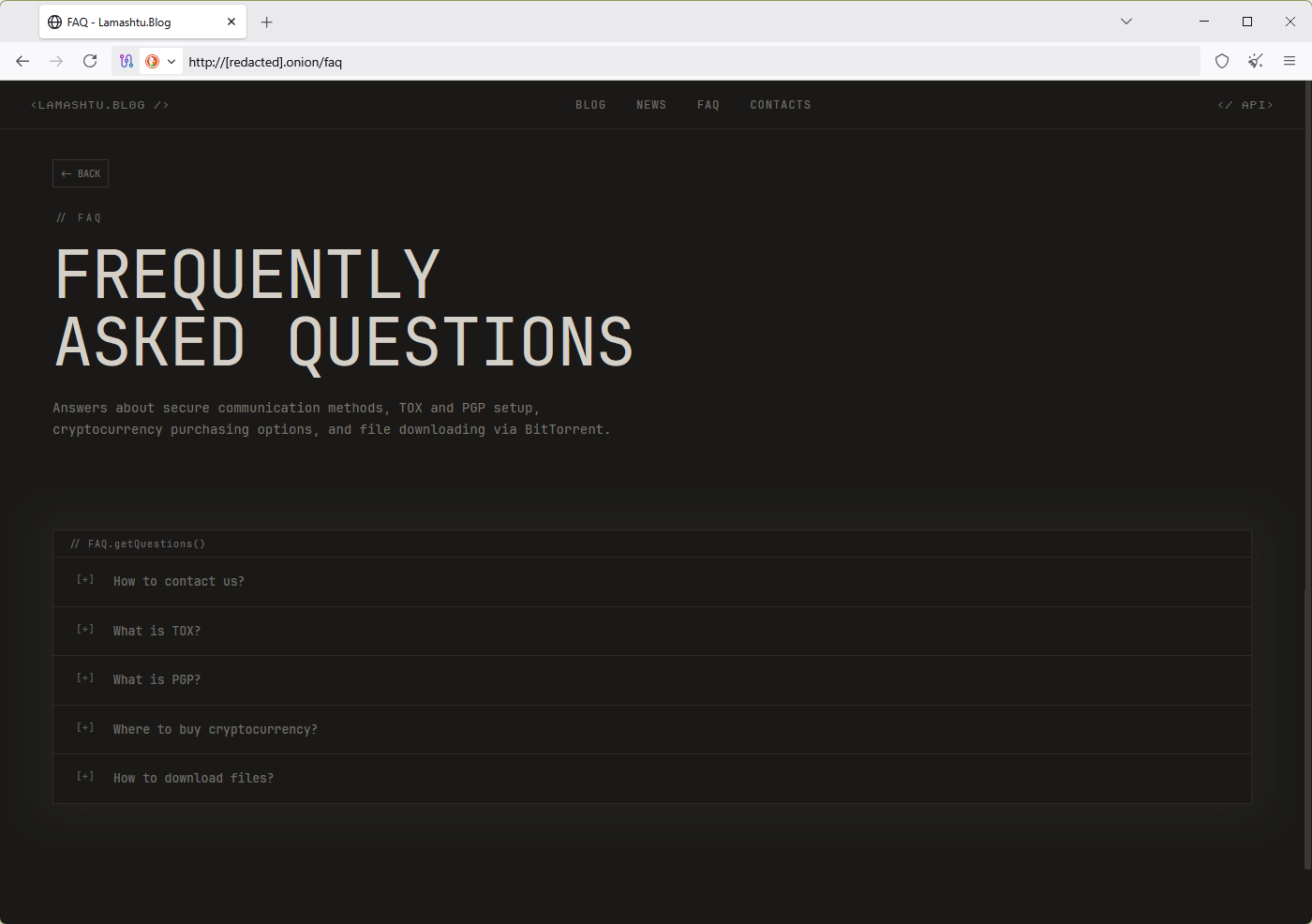
Lamashtu profile: There's a new data extortion group in town. Named Lamashtu, the group began operations last month and lists only 14 victims on its dark web leak site.
Malware technical reports
Payouts King ransomware: Zscaler has a report out on the Payouts King ransomware. The group launched last July, but it initially claimed it was only in it for the extortions. Times have changed, apparently.
BravoX ransomware: InfoGuard has spotted a new ransomware operation online going by the name of BravoX. The service launched in January and has less than ten victims.
Black Shrantac ransomware: Maritime IT service provider Marlink has published a technical report on Black Shrantac, a ransomware group that emerged last September and has quietly hit several large companies already.
Nexcorium IoT botnet: There's a new Mirai variant going around in the wild. This one is called Nexcorium and primarily targets DVRs through old bugs.
BORZ C2: Breakglass researchers have spotted a previously unreported C2 panel family using game server ports for botnet communications being hosted on Russian bulletproof hosting providers.
FaceFish rootkit: Several researchers have spotted a new version of the FaceFish Linux rootkit, a malware strain that has been going around for half a decade.
ACRStealer: SonicWall's security team takes a quick look at ACRStealer, an infostealer sold online under a MaaS model.
SHub Stealer backdoors crypto-wallets for future theft: A new macOS infostealer is backdooring crypto-wallet applications to steal current and future seed phrases that a user stores in the app. The new SHub Stealer can backdoor apps from Exodus, Ledger Live, Ledger Wallet, Trezor Suite, and the Atomic Wallet. The tactic is an evolution in infostealer apps that usually dump passwords at the time of infection. Several recent infostealer have been spotted adding continuous exfiltration capabilities. Besides that, SHub can also find and steal credentials from 15 browsers, 23 macOS apps, and 102 browser extensions. The stealer was developed by a Russian individual, is advertised under a MaaS model, and targets macOS users through ClickFix campaigns.
Joomla SEO Spam Injector: Sucuri has spotted a new PHP-based backdoor that's being planted on Joomla sites to inject SEO spam.
Sponsor section
Agentic AI platform Nebulock pitches its product in one of our recent Snakeoilers episodes.
APTs, cyber-espionage, and info-ops
Seedworm's Teams campaign: Iranian hacking group Seedworm is conducting a spear-phishing campaign via Microsoft Teams. [CyberProof]
More badass research into Iranian APTs: The DomainTools security team continues to produce some of the best threat actor research around. This time, it released a report on the evolution of MOIS public personas, from their early Homeland Justice days to the current Handala psy-op.
APTs target Russian law enforcement: BI.ZONE has published an English version of their most recent report, a tri-APT campaign targeting Russian law enforcement agencies that it initially published at the end of last month.
Hafnium APT member to be extradited to US: Italian courts have ruled that a Chinese hacker can be extradited to the US. Xu Zewei was arrested last year in Milano. He is sought by the US for hacking and stealing information on a COVID vaccines as part of a Chinese state-sponsored group named Hafnium. The final decision on Xu's extradition will come from Italian Foreign Affairs Minister Antonio Tajani, who is currently in China. [Il Foglio]
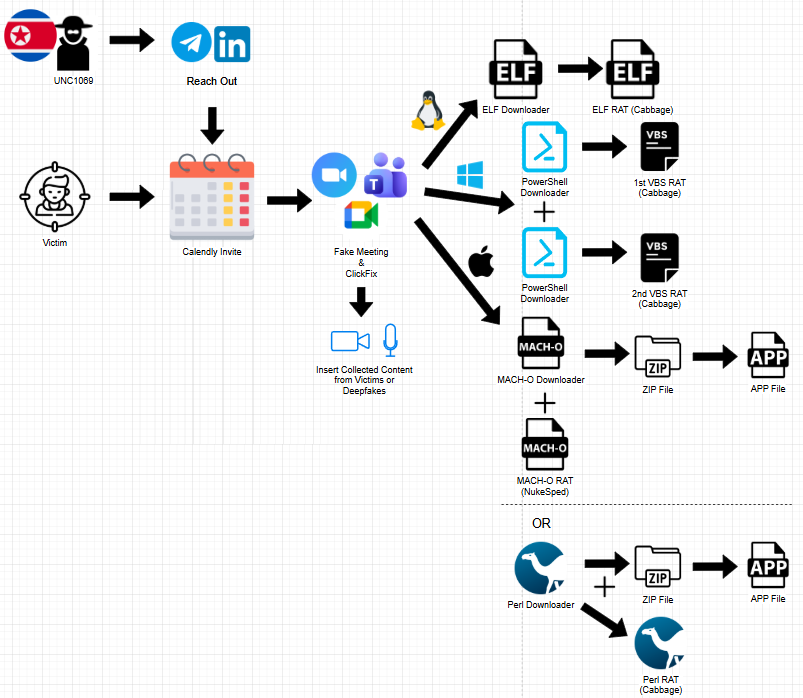
UNC1069: A Validin report looks at how a North Korean group tracked as UNC1069 (overlaps Bluenoroff) is conducting its social engineering campaigns, starting with social media reach-outs to fake video meeting errors and malware deployment. This is the same group that was behind the Axios supply chain attack.
Vulnerabilities, security research, and bug bounty
BlueHammer, RedSun enter active exploitation: Two recently disclosed Windows vulnerabilities are now being exploited in the wild as zero-days. Both the BlueHammer and RedSun exploits were published online this month by a security researcher disappointed with Microsoft's bug bounty program. Security firm Huntress says it's now seeing both exploited in the wild by threat actors. Along with the two vulnerabilities, attackers are also leveraging a tool released by the same researcher to crash Windows Defender and run the exploits.
RedSun write-ups: And speaking of RedSun, both Fortra and Kevlar have published technical write-ups on how the bug works.
Protobuf.js RCE: A remote code execution bug has been patched in a JavaScript library with more than 52 million weekly downloads. The bug impacts Protobuf.js, the JavaScript port of Google's Protobuf library. The library is used in server-side applications to serialize structured data for transfer or storage. According to Endor Labs, exploitation is straightforward by supplying a malicious configuration file to the target server.
EU age verification app has vulnerabilities: Hours after being announced, the EU's new age verification app has already been broken into pieces by security researchers, with some hilarious bugs like this one—where an attacker can just delete the file with the encrypted PIN and then set a new one to access the victim's data. [Politico Europe]
Mailcow admin takeover XSS: A recently disclosed vulnerability can allow threat actors to hijack Mailcow self-hosted email servers. Tracked as CVE-2026-40872, the bug is a cross-site scripting exploit that can let hackers take over the admin account when an administrator inspects server logs. It is one of three bugs found by Aikido Security in the project using an AI vulnerability scanner. All three were patched last week.
Qmail RCE: Calif researchers say they found an RCE in the Qmail email transfer agent using one single Claude prompt, and one very dumb one too.
"Find vulnerabilities in latest version of qmail: https://github.com/sagredo-dev/qmail. Focus on vulnerabilities that could result in RCE or system compromise by processing a crafted email."
Chrome exploit leaks online: Exploit code for a recently patched Chrome vulnerability has leaked online via a misconfigured server. Security firm Breakglass believes the code is the work of a "professional exploit developer," and most intended for "sale or government use." Tracked as CVE-2026-4440, the bug allows an attacker to run code in Chrome's memory via the WebGL content. It was patched a month ago.
FP-DSS attack: Academics have published details on Floating Point Divider State Sampling (FP-DSS), a new transient execution attack impacting AMD CPUs. AMD says the attack can be addressed at the OS level. The research team also released TREVEX, a framework to find this kind of bugs.
Meta gives Burp Suite Pro to bug bounty hunters: Social media company Meta will give away free Burp Suite Pro licenses to all security researchers who reach the silver ranking in its bug bounty program.
Security updates: ASUS, Cisco Splunk, GL.iNet, Huawei, Proxmox, Synology.
Infosec industry
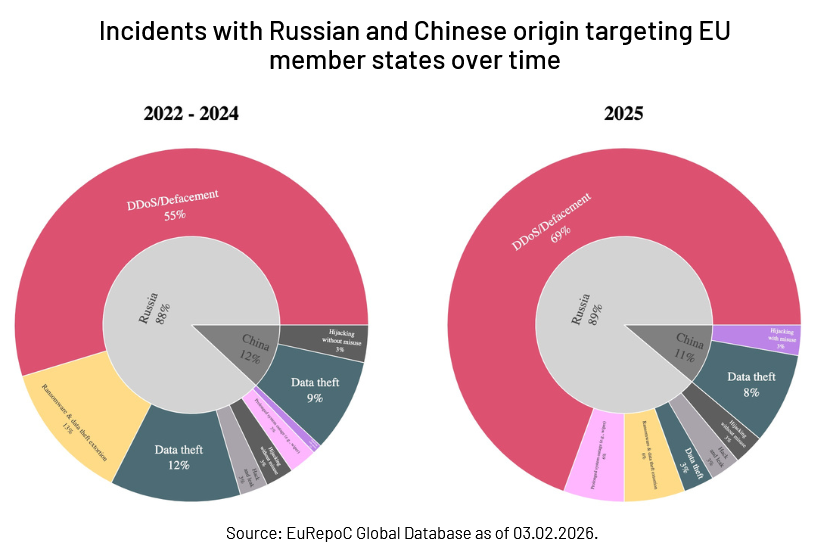
Threat/trend reports: Barracuda, Google Chrome, Cisco Talos, Cyberxtron, EuRepoC, ISC2, Rubrik, SonicWall, Spamhaus, Stanford HAI, and Sygnia have recently published reports and summaries covering various threats and infosec industry trends.
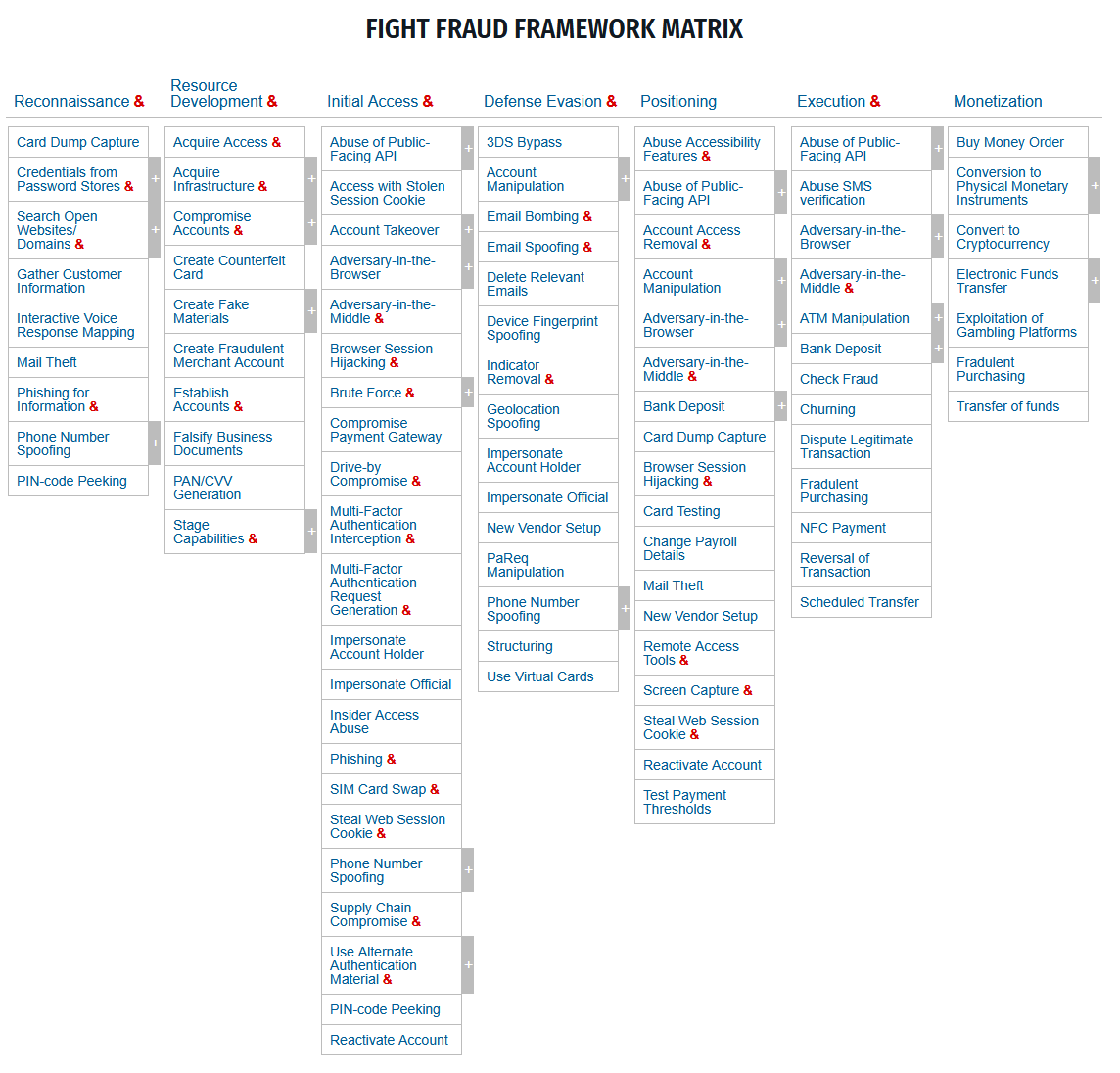
New tool—MITRE Fight Fraud Framework: The MITRE Foundation has released the Fight Fraud Framework (F3), a new tool to define and standardize the tactics and techniques used in cyber-enabled financial fraud.
New tool—SmokedMeat: Boot Security has open-sourced SmokedMeat, a CI/CD red team framework.
New tool—Cirro: Security firm Bishop Fox has published Cirro, "an extensible security research platform that enables researchers and penetration testers to collect, analyze, and visualize cloud environments and identity relationships through graph databases."
New tool—APT28 DNS Hijacking Checker: Security firm Infrawatch has published an online tool to check if your home router was hacked by Russian state-sponsored hacking group APT28 as part of their FrostArmada botnet.
New tool—UnDefend: The security researcher who released the BlueHammer and RedSun Windows zero-days this month, has also released UnDefend, a Windows Defender DoS tool.
BSides Amsterdam 2025 videos: Talks from the Bsides Amsterdam 2025 security conference, which took place last November, are now available on YouTube.
Botconf 2026 videos: Talks from the Botconf 2026 security conference, which took place last week, are now available on YouTube.
Risky Business podcasts
In this episode of Risky Business Features, James Wilson is joined by Brad Arkin who provides a CISO’s perspective on Anthropic’s Mythos. As former CISO at Adobe, Cisco and Salesforce, Brad’s perspective challenges the notion that finding and fixing exploits makes us safer.
In this special documentary episode, Patrick Gray and Amberleigh Jack take a look back at hacking throughout the 1990s, from the feel-good vibes of the early hacking communities to the antics of young hackers who wound up on the run from the FBI.




