Risky Bulletin: Google patches Android remote takeover bug
In other news: Palo Alto Networks discloses a firewall zero-day; Ivanti also patches one; leak exposes Russia's spy and hacker school.

This newsletter is brought to you by PortSwigger. You can subscribe to an audio version of this newsletter as a podcast by searching for "Risky Business" in your podcatcher or subscribing via this RSS feed. You can also add the Risky Business newsletter as a Preferred Source to your Google search results by going here.
This month's Android security updates carry an important patch for a critical vulnerability that can grant attackers remote access to an Android smartphone or smart device.
Tracked as CVE-2026-0073, the bug allows attackers to bypass authentication in the Android remote debugging service ADB.
Successful exploitation opens a remote shell on a device where the ADB service was enabled. ADB is disabled by default in the standard Android OS release, but may be enabled and left exposed by accident by some OEM (device makers) during factory testing, which has happened a lot over the past years.
The issue impacts all devices running Android 11 or later, which is every Android version released since September 2020.
The bug was discovered by BARGHEST, a UK non-profit that does security research to help protect human rights defenders and journalists across Asia against mobile hacking and surveillance.
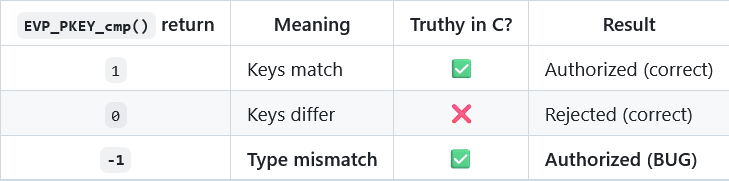
BARGHEST described the issue as a "logic error" in the ADB authentication process.
When a user connects via ADB, they need to present a public key to be compared to a private key stored on the device.
Researchers found that if the key types don't match, for example the private one is RSA and the public one is Ed25519, the ADB service would return an error but still open the remote Android shell for the user trying to authenticate.
The bug only works if the ADB service was used at least once, so there's an initial private key on the Android ADB host to compare it with.
Exploitation works in private networks and over the internet.
Over the past decade, there've been countless botnets that grew to massive sizes by exploiting Android devices with ADB ports left exposed over the internet. Most of them targeted ADB ports left exposed without a password and this bug will likely lead to a surge in attacks from the same botnets targeting devices that were previously considered secure.
This bug is also likely to be integrated into targeted attacks and Android device unlocking toolkits used by law enforcement.
"The exploit does not provide kernel code execution, root, or direct compromise of hardware-backed secrets by itself. The demonstrated primitive is remote code execution as the Android 'shell' user in SELinux context 'u:r:shell:s0'. That is still a serious compromise: the attacker has reached the operating system’s debugging interface, not an ordinary application sandbox, an important contextual stage for Android security."
Patching is highly recommended, and a fix has been released this week with Android's May monthly security bulletin.
Risky Business Podcasts
The main Risky Business podcast is now on YouTube with video versions of our recent episodes. Below is our latest weekly show with Pat, Adam, and James at the helm!
Breaches, hacks, and security incidents
Chime sued over DDoS: Some Chime Financial customers have filed a class-action lawsuit against the company for a DDoS attack it fended off last month from a hacktivist group named The 313 Team.
Schemata leak: A DOD contractor has leaked US service member records and sensitive military training documents. The leak took place via an API exposed online without authentication. According to security firm Strix, AI virtual training platform Schemata took 150 days to secure the leaky API. [CyberScoop]
AI company Braintrust discloses hack: AI startup Braintrust has told customers to replace API keys following a security incident. The company says hackers gained access to its AWS infrastructure and may have accessed their API key database. Braintrust provides AI observability tools so companies can monitor and understand how their AI models work and respond. The company's customers include the likes of Cloudflare, Vercel, Stripe, and other tech giants. [TechCrunch]
Ekubo crypto-heist: Hackers have stolen $1.4 million worth of crypto assets from the Ekubo Protocol.
DAEMON Tools supply-chain attack: AVB Disc Soft has released new clean versions of DAEMON Tools. The company's site was compromised for almost a month and hackers included hidden backdoors in the software.
Five water treatment stations hacked in Poland: Five water treatment facilities were hacked last year across Poland. Attackers gained access to industrial control systems in some facilities. Poland's intelligence service did not attribute the attacks to any group or foreign state. [ABW // The Record]
Pegasus investigation reopened in Barcelona: The Catalan high court has reopened an investigation into the use of the Pegasus spyware against members of Catalan NGO Omnium Cultural. The case was closed by a lower court in February. [Diari de Catalunya] [h/t Sophie in't Veld]
General tech and privacy
Rights groups unite against age checks: Nineteen of the world's biggest privacy rights groups and privacy tech companies have signed a joint statement asking the UK government to reconsider its mandatory age checking rules. Some of the signatories include Mozilla, the Tor Project, the EFF, and Big Brother Watch.
Chrome 148: Google has released version 148 of its Chrome browser. See here for security patches and webdev-related changes. The biggest change in this release is support for lazy loading audio and video elements.
ProtonMail adds PQC support: Proton has added post-quantum cryptography (PQC) protections to its email service, ProtonMail.
Meta revamps backup fleet: Meta has rolled out new cloud infrastructure to handle Messenger and WhatsApp's end-to-end encrypted backups.
German domains go down in massive outage: All German .de domains went down on Tuesday due to a DNSSEC disruption at the country's domain registrar. [Cloudflare]
Government, politics, and policy
US includes offensive cyber in counterterrorism strategy: The US government will use offensive cyber operations as part of its counterterrorism response. The new provision was included in the White House's new Counterterrorism Strategy published this week. The document listed Islamit terrorists, drug cartels, transnational gangs, and "anti-fascists" as potential targets. It did not list extreme right groups as one, though. [NextGov // US Counterterrorism Strategy , PDF]
US hasn't forgotten about CISA 2015: The Trump administration is preparing a long-term reauthorization of the Cybersecurity Information Sharing Act of 2015. The act allows the private sector to share cyber intelligence with the government without legal liabilities. It temporarily expired last year for a few months for the first time since it was approved and later extended until September this year. National Cyber Director Sean Cairncross says he expects Congress to do the right thing. [NextGov]
EU working to exclude US firms from EU clouds: EU officials are preparing new regulations that would exclude US tech giants from EU clouds. The EU Cloud and AI Development Act is one of the several packages the EU is preparing to ensure its tech sovereignty. EU officials say they're seeing "very effective lobbying" from US companies claiming that moving away from their services would be too expensive. The new regulation is scheduled for debate at the end of May. [Politico Europe // Politico Europe]
Sponsor section
In this Risky Business sponsor interview, James Wilson talks with James Kettle and Daf Stuttard from PortSwigger about the incredible research James will unveil at Black Hat US this July, and how that research will be productised into Burp Suite.
Arrests, cybercrime, and threat intel
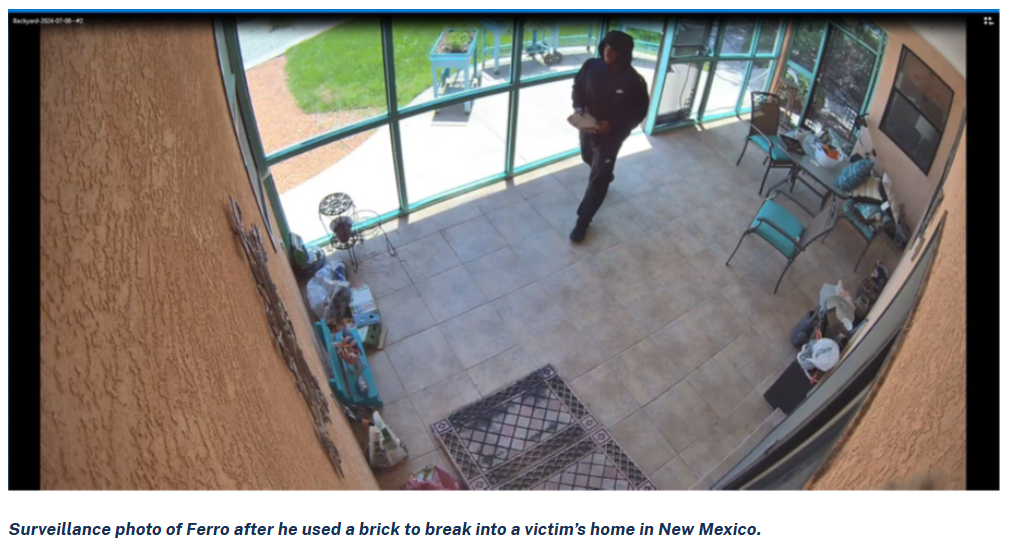
GothFerrari sentenced to prison: A California man was sentenced to 6.5 years in prison for stealing cryptocurrency wallets. Marlon Ferro worked as the hired muscle of a group of cryptocurrency hackers. When phishing and social engineering attempts failed to hack a victim, Ferro would be sent to break into a target's home and steal their crypto-wallets. The entire group made more than $250 million.
Two more DPRK laptop farmers sentenced to prison: The US has sentenced two more Americans to prison for running laptop farms for North Korean remote IT workers. Matthew Issac Knoot, of Nashville, Tennessee, and Erick Ntekereze Prince, of New York, were both sentenced to 18 months in prison. The two ran two separate laptop farms that allowed North Koreans to pose as Americans and obtain employment at US companies. The workers made more than $1.2 million in salaries from their employment.
Swatter arrested in Hungary: Hungarian police have arrested a 20-year-old suspect for swatting attacks against US individuals. The suspect was a member of a Discord group that streamed their swatting to members of the community. Other members of the same community were also arrested at the start of the year.
Phone numbers in scam emails: Phone numbers used in scam emails often cluster around a threat actor, allowing for easy tracking of some activity. [Cisco Talos]
macOS ClickFix campaign: Microsoft looks at a ClickFix campaign targeting macOS users with payloads such as Macsync, Shub Stealer, and AMOS. [Microsoft]
Malicious NuGet packages: A cluster of five malicious NuGet packages impersonating popular Chinese .NET libraries is deploying infostealers on dev machines. [Socket Security]
"The stealer targets saved credentials across 12 browsers, 8 desktop cryptocurrency wallets, 5 browser wallet extensions and exfiltrates to a newly-registered C2 domain. Across all versions, the five packages have accumulated approximately 65,000 downloads, putting tens of thousands of developer workstations and CI/CD build servers in scope of credential and crypto wallet theft. All five packages remain available on NuGet at the time of writing."
New PCPJack group: A new hacking group is breaking into cloud servers previously breached by the TeamPCP group and replacing their malware with their own tools. The hack-and-replace campaign has been going on since last month. The attackers are replacing TeamPCP backdoors and with their own credential stealers and self-spreading worms. SentinelOne tracks this group as PCPJack. [SentinelOne]
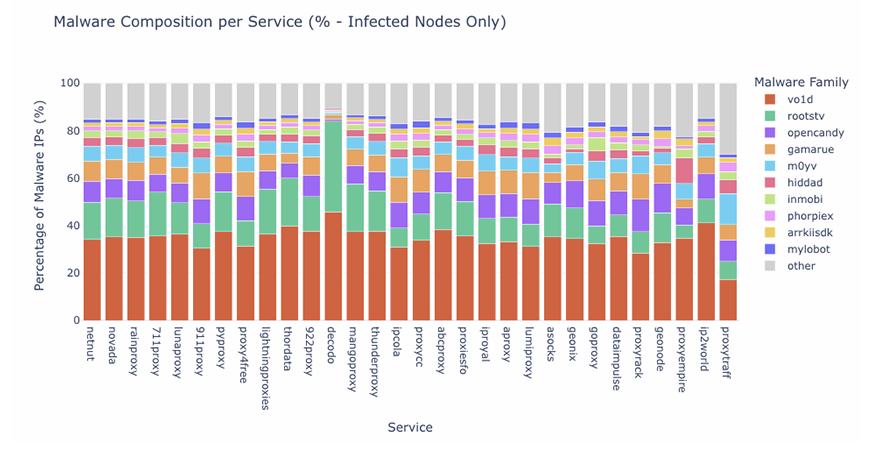
Residential proxy ecosystem: One in five IP addresses listed in residential proxy networks are also communicating with malware command-and-control servers, suggesting the owners of those devices have an active malware infection. [Bitsight]
CallPhantom campaign: Google has removed 28 apps from the official Android Play Store for defrauding users. The apps promised access to the call records, SMS data, and WhatsApp call history of any phone number but charged users and returned randomly-generated data. They were downloaded more than 7.3 million times, primarily from India and the Asia‑Pacific region. [ESET]
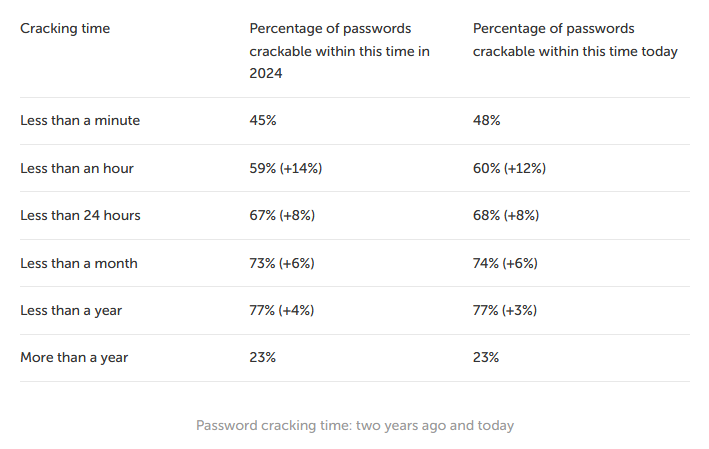
Most MD5 hashes can be cracked under an hour: Almost 60% of MD5 hashes can be cracked in under an hour with an NVIDIA RTX 5090 graphics card, and a whopping 48% can be cracked under a minute. [Kaspersky]
Malware technical reports
TCLBANKER: Elastic's security team has published an analysis of TCLBANKER, a new banking trojan targeting the Brazilian market via WhatsApp and Outlook spam. Elastic says the banker is an update of the older MAVERICK/SORVEPOTEL family.
Salat Stealer: DarkAtlas looks at Salat Stealer, a Go-based remote access trojan also known as WEB_RAT.
Sponsor section
Join Burp AI developers, Dan and Pete, as they walk us through the new agentic AI functionality in Burp Suite Professional's Repeater.
APTs, cyber-espionage, and info-ops
Contagious Interview update: North Korean hackers are using a new method to hide malware in GitHub repositories. Malicious loaders are hidden inside Git hooks, which are shell scripts that execute automatically when users interact with a repo. The new technique has been used in a North Korean campaign that targets developers with fake job offers. Individuals who clone a GitHub "code assignment" will end up infecting themselves with malware. [OpenSourceMalware]
"The OpenSourceMalware team has spotted a fresh twist in the DPRK's Contagious Interview / TaskJacker playbook: the operators have pivoted away from stuffing their stage-2 loader into .vscode/tasks.json, package.json postinstall scripts, or fake .woff2 font files, and are now hiding it inside Git hooks. The candidate clones the "coding assessment" repo, and the loader fires before the commit object is even written."
OceanLotus is on PyPI: Vietnamese APT group OceanLotus has been seen distributing the ZiChatBot malware via malicious PyPI packages. [Kaspersky]
BO Team's ZeronetKit: Ukrainian hacking group BO Team left a Git repository exposed online and leaked the source code of its ZeronetKit backdoor. The leak also exposed a Linux version of the malware, something researchers didn't see before. [Kaspersky]
Operation Silent Rotor: A spear-phishing campaign has targeted UAV companies in Russia and Central Asia with malicious documents right before a major UAV conference last month. [Seqrite]
Iran-Russia cyber love: Although Moscow has denied helping Iranian hackers, the evidence suggests there is a lot of cooperation between the two states. [Margin Research]
MuddyWater deploys Chaos ransomware: And speaking of that evidence, here's the MuddyWater Iranian APT deploying the Chaos ransomware, advertised on Russian hacker forums, in some of its intrusions. [Rapid7]
Leak exposes Russia's APT school: A major Moscow university has been exposed as a primary training center for Russia's military hacking units. Students at a special department at the Bauman State Technical University in Moscow are thought to hack, spread disinformation, and sabotage operations. A leak of more than 2,000 internal documents has traced former students to multiple GRU cyber units. The leak includes curricula, contracts, photos from classes, and lists of students and teachers from 2022 to 2024. The Bauman Technical University was founded in 1830 and is generally considered Russia's MIT equivalent. [Delfi // Der Spiegel // FrontStory.pl // Le Monde // The Guardian // The Insider // VSquare]
US aligns with Russia on Canadian info-op: Disinformation groups from Russia and the US have aligned to push separatist narratives in Canada's Alberta region. Russian groups like Storm-1516 and the Pravda network and the MAGA influencer ecosystem are heavily pushing the topic in the hopes of destabilizing Canada's political landscape. The influence operation began after President Trump touted plans to annex Canada and members of the US Republican party visited Alberta to prop up the movement this year. [DisinfoWatch // CBC]
Vulnerabilities, security research, and bug bounty
Security updates: Apache Camel, Axis, Chrome, Cisco, Eclipse, Firefox, Ivanti, Juniper, Moodle, Palo Alto Networks, Samsung, Zyxel.
PAN discloses firewall zero-day: A "state sponsored" hacking group is exploiting a zero-day in Palo Alto Networks firewalls. The zero-day, tracked as CVE-2026-0300, is in the devices' web login interface and no authentication is required. It allows threat actors to run malicious code on the firewalls with root privileges. Affected devices include firewalls from the PA and VM series. Palo Alto Networks has told customers to restrict logins to internal IP addresses until a patch is available.
Ivanti patches an EPMM zero-day: Ivanti has released security updates to patch an actively exploited zero-day in its EPMM mobile management platform. The zero-day is connected to two zero-days the company patched in January but have continued to be exploited. The vulnerability requires attackers to be authenticated on an admin account and was most likely used to maintain persistence after the January patches. The zero-day is one of five vulnerabilities Ivanti patched on Thursday.
Edge stores passwords in cleartext: The Microsoft Edge browser loads and stores all stored passwords in cleartext in its memory, from where it can be easily dumped by any user on the system. [SANS ISC]
New vm2 sandbox escape: There's another major sandbox escape in vm2, the virtual machine technology that ships with Node.js.
SFMC vulnerabilities: Salesforce rolled out an extensive security overhaul of its Marketing Cloud platform to address a suite of vulnerabilities. The bugs could have allowed attackers to leak contacts and sent emails from any of the company's tenants. The issue was reported in early January and patched after eight days. To mitigate the bugs Salesforce rolled out a new encryption scheme for all customers and expired all individual links for emails sent before January 23. [Searchlight Cyber]
"We reported these findings to SFMC and they took action to remediate these issues. Salesforce deployed AES-GCM encryption across the platform, expired all links created prior to January 23, 2026 at 21:00 UTC, and disabled double evaluation of email subject line AMPscript."
Mozilla's Mythos use: For all the curious infosec AI people, Mozilla has published a blog detailing its work with Anthropic's Mythos AI model and how it was used to find and patch 271 vulnerabilities this year.
Infosec industry
Acquisition news: Cisco will acquire Astrix Security, a provider of security services for AI agents.
New tool—FlowCarp: Security firm Netresec has released FlowCarp, a command line tool that identifies the application layer protocol in network traffic without relying on port numbers, static signatures or code that tries to parse the application layer.
New tool—Decipher: JHU professor Matthew Green has released Decipher, an AI-enabled application for cracking ciphers.
New tool—Spinel: Ruby creator Yukihiro Matsumoto has open-sourced Spinel, a tool to compile Ruby code into standalone native executables. It supports the three main desktop OSes, Linux, macOS, and Windows.
Threat/trend reports: Cisco Talos, Comparitech, Kaspersky, Microsoft, Pixm, Prove, and Zoho have recently published reports and summaries covering various threats and infosec industry trends.
Risky Business podcasts
In this edition of Seriously Risky Business, Tom Uren and James Wilson talk about the sudden drive to put regulation around the releases of new AI models because of their cyber security implications. A standardised approach is desirable, but clamping down too hard won't achieve as much as might be hoped. Experts with older or even open models can get just as far as novices with the latest models.




