Risky Biz News: Google wants to reduce lifespan of TLS certificates from one year to just 90 days
In other news: Authorities take down ChipMixer service used by ransomware gangs; Magniber ransomware starts targeting Europe; US charges two suspects for DEA portal hack.
This newsletter is brought to you by Airlock Digital, Proofpoint, runZero, and Thinkst Canary. You can subscribe to an audio version of this newsletter as a podcast by searching for "Risky Business News" in your podcatcher or subscribing via this RSS feed.
Google has announced plans to reduce the maximum lifespan of a TLS certificate from the current value of 398 days to only 90 in a move that is going to send shockwaves across several IT industries.
There is currently no official date for when this new policy is going to come into effect.
Google says it plans to make a future proposal on this topic at the CA/Browser Forum, an informal group made up of browser vendors and Certificate Authorities (CAs), the companies that issue TLS certificates.
This would mark the fourth time that the maximum lifespan of a TLS certificate would be changed after TLS certs went from 5-year validity periods to three, two, and then one.
Every policy change has been riddled with endless discussions on why a change would be detrimental to both CAs and their customers.
Tim Callan, Chief Experience Officer at certificate authority Sectigo, believes Google is "deliberately telegraphing" the industry about its plan in order to avoid the public brouhaha we had in previous years.
Google appears to have found the right tone, with the company advocating that reducing certificate lifespans "encourages automation" and moves the CA industry away from "baroque, time-consuming, and error-prone issuance processes" that have failed to detect abuse.
Google specifically mentions that CAs automating their TLS cert issuance procedures will "allow for faster adoption of emerging security capabilities and best practices."
From industry reactions, both Sectigo and GlobalSign appear to have embraced a migration to automated certificate lifecycle management (CLM) procedures.
Either that or they know that Google can enforce the change in Chrome at any time and without a vote in the CA/Browser Forum, and CAs will have to start issuing 90-day certs or lose customers.
This exact scenario happened in 2020 when Apple unilaterally decided to support one-year TLS certs, and everyone else had to follow its lead—Google, Mozilla, and then the (grumbling) CAs.
Breaches and hacks
Rubrik hack: Cloud security firm Rubrik confirms that it is one of the companies that got hacked using the GoAnywhere zero-day (CVE-2023-0669) last month. The company says the intruders only gained access to a non-production IT testing environment and that "there was no lateral movement to other environments." Nevertheless, Rubrik has confirmed the threat actors managed to steal some of its data from the non-production environment, data from its sales department, including data on customers and partner companies.
Poolz crypto-heist: The Poolz cryptocurrency platform lost $665,000 worth of assets after an attacker exploited a bug in one of its blockchain contracts.
ICS incidents: Kaspersky's ICS team has a summary of the cybersecurity incidents that impacted the industrial sector in H2 2022. This includes breaches at Swiss dairy giant Cremo, Luxembourg-based energy provider Encevo, German semiconductor manufacturer Semikron, and others.
General tech and privacy
Docker to remove free tier: Virtualization platform Docker plans to remove free Organization accounts from Docker Hub, the company's Docker images repository. The move is expected to impact and effectively boot most open-source projects off the platform unless they pay $420/year. Tutorials are currently being shared online on how to move Docker images from Organization accounts back to free personal accounts.
Epic Games fined $245 million: The US FTC has fined Epic Games, the company behind the Fortnite game, $245 million for using dark patterns to trick players into making unwanted purchases. The FTC says the practice was specifically vile since it allowed children to rack up unauthorized charges without any parental oversight.
Government, politics, and policy
Federal agency breach: CISA says that multiple threat actors, including an APT group, exploited a 2019 vulnerability to gain access to a federal agency's IIS web server. CISA says the attacks took place from November 2022 through early January 2023. The exploited vulnerability is tracked as CVE-2019-18935 and was previously widely exploited for at least two years before the CISA report this week. The vulnerability resides in the UI component of the Progress Telerik framework, a tool commonly used for building user interfaces for ASP.NET applications. In the past, the same bug has been widely used in cryptomining campaigns and for building various botnets.
New SEC cybersecurity rules: The US Securities and Exchange Commission has proposed new cybersecurity rules for operators on the US securities market, such as broker-dealers, clearing agencies, and national securities exchanges. The new rules require that financial companies report cybersecurity breaches to the SEC within 48 hours of detection. The new rules mandate that financial entities establish "reasonably designed" policies to address cybersecurity risks in their environments and run cybersecurity audits every year to test their defenses. The new rules will enter a 60-day public comment period before they are updated or adopted as is.
Audit of Chinese drones: A group of US senators has formally asked CISA to conduct a cybersecurity analysis of drones manufactured by "Chinese military company" DJI. The senators believe the Chinese government could use DJI drones to map US critical infrastructure, information they could use to enable better-targeting efforts in the event of a conflict.
Dutch police pilot program: Dutch police is running a pilot program and looking to recruit "cyber volunteers" to help agents investigate or prevent cyber crimes. Dutch police have had a "volunteer program" for 75 years. Through a pilot in the Veluwe Vallei Noord region, Dutch officials are now looking to expand its volunteer program to also cover cybersecurity-related cases, such as bank helpdesk fraud, phishing, ransomware, friend-in-emergency fraud, or sextortion.
Ukraine to legalize IT Army: The Ukrainian government is working on a law that would legalize the activity of its so-called "national hacktivist group," the IT Army of Ukraine. The new law would draft the IT Army into the ranks of the Ukrainian army. The move comes after cybersecurity and international politics experts have warned that members of the IT Army would be liable for criminal prosecution for some of their actions, since they were not formally sanctioned by the Ukrainian government as part of its official war-time defense operations. [Additional coverage in Newsweek]
Risky Business Demo
In this Risky Business demo, Tines CEO and co-founder Eoin Hinchy demonstrates the Tines no-code automation platform to host Patrick Gray.
Cybercrime and threat intel
ChipMixer: US and European law enforcement authorities have taken down ChipMixer, a dark web-based cryptocurrency mixing service. Officials say the portal launched in 2017 and has helped criminal groups launder more than $3 billion worth of assets. As part of the operation, officials took control of servers in Germany, seized Bitcoin worth €44 million, and charged the service's owner, Minh Quốc Nguyễn, a 49-year-old man from Hanoi, Vietnam. Below are some of the funds ChipMixer processed through the years, per the US DOJ:
- $17 million in bitcoin for criminals connected to approximately 37 ransomware strains, including Sodinokibi, Mamba and Suncrypt;
- Over $700 million in bitcoin associated with wallets designated as stolen funds, including those related to heists by North Korean cyber actors from Axie Infinity's Ronin Bridge and Harmony's Horizon Bridge in 2022 and 2020, respectively;
- More than $200 million in bitcoin associated either directly or through intermediaries with darknet markets, including more than $60 million in bitcoin processed on behalf of customers of Hydra Market, the largest and longest-running darknet market in the world until its April 2022 shutdown by US and German law enforcement;
- More than $35 million in bitcoin associated either directly or through intermediaries with "fraud shops," which are used by criminals to buy and sell stolen credit cards, hacked account credentials and data stolen through network intrusions; and
- Bitcoin used by the Russian General Staff Main Intelligence Directorate (GRU), 85th Main Special Service Center, military unit 26165 (aka APT 28) to purchase infrastructure for the Drovorub malware, which was first disclosed in a joint cybersecurity advisory released by the FBI and National Security Agency in August 2020.
ViLE members charged: The US government has charged two members of the ViLE hacking crew that broke in May 2022 into a law enforcement portal operated by the US Drug Enforcement Administration (DEA). US officials say that Sagar Steven Singh, who went online as Weep, and Nicholas Ceraolo, known as Convict, used the stolen passwords of US and foreign police officers to access the portal. The duo collected personal data and extorted victims for money, threatening to release their personal information on the internet. In addition, US officials say Singh and Ceraolo also used the portal to file fake emergency requests with US tech companies in order to deanonymize online accounts and identify future extortion victims. According to KrebsOnSecurity, doxes would typically be posted on Doxbin, a doxing site where both suspects were allegedly staff members. US authorities arrested Singh this week while Ceraolo remains at large.
NFT hackers on the hook: A Florida judge has ruled in favor of a plaintiff who had their NFTs stolen by hackers in December 2021. The judge ruled that the unidentified hackers must pay the plaintiff $971,291 worth of USDT (Tether), plus interest, for the NFT assets they stole. The case marks the first instance where a judge issues a default judgement against NFT hackers, giving victims the means to recover stolen funds once the hackers are identified. [Read more in Decrypt]
New cryptomining operation: Security firm Crowdstrike has discovered a novel cryptojacking operation that mines the new Dero cryptocurrency token on infected hosts instead of Monero, the preferred token of most crypto-mining botnets. Crowdstrike says this new operation has been active since February this year. So far, the gang has had success gaining access to Kubernetes clusters that have anonymous access enabled on their API and listening on non-standard ports.
TeamTNT campaign: Cado Security has an update on the new tooling used by the TeamTNT cryptomining gang.
Black Skills: Flashpoint reports that Russian hacktivist group Killnet is trying to establish a new entity called "Black Skills," which they are advertising as a "private military hacking company." While it's unclear what this means, Flashpoint believes Killnet may be trying to establish itself as a "corporate identity."
"According to our intelligence, the new group will be organized and structured, with subgroups taking care of payroll, public relations and technical support, pen testing, as well as data collection, analysis, information operations and hits against priority targets."
New npm malware: Thirty-six new malicious npm packages spotted. Check out GitHub's security advisory portal for details.
KEV update: CISA has updated [1, 2] its KEV database with four new vulnerabilities that are currently being actively exploited. Three are zero-days patched during this week's Patch Tuesday, while the fourth is a Fortinet zero-day the company patched last week.
- CVE-2023-26360 - Adobe ColdFusion Improper Access Control Vulnerability
- CVE-2023-23397 - Microsoft Outlook Elevation of Privilege Vulnerability
- CVE-2023-24880 - Microsoft Windows SmartScreen Security Feature Bypass Vulnerability
- CVE-2022-41328 - Fortinet FortiOS Path Traversal Vulnerability
Secureworks 2022 IR report: Secureworks published this week its yearly incident response report for the past year. Secureworks says financially motivated attacks accounted for most of the incidents investigated last year. They accounted for 79% of all incidents, which is lower than in previous years. The company believes this "could potentially be connected to the Russia / Ukraine conflict disturbing cybercrime supply chains." On the other hand, state-sponsored activity increased from 6% in 2021 to 9% of all incidents in 2022.
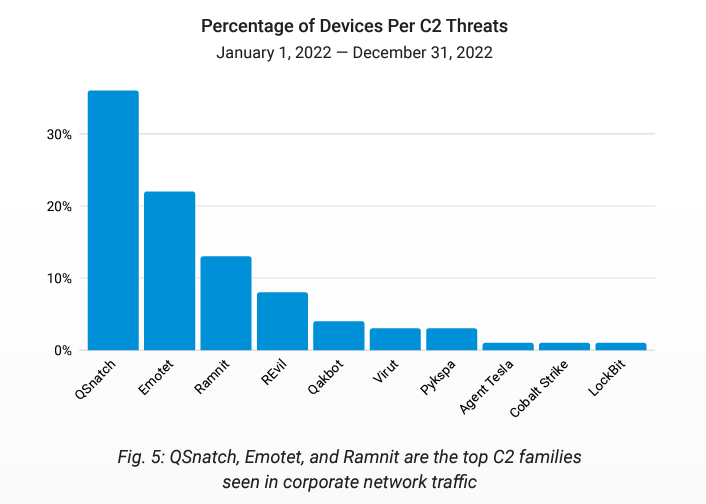
QSnatch still going strong: Akamai has published a report on malicious DNS traffic they saw from corporate networks last year. One of the report's most interesting findings is that more than a third (36%) of malicious DNS traffic the company saw in 2022 was related to QSnatch, a botnet that primarily infects NAS devices. Second was Emotet, followed by Ramnit.
Malware technical reports
LemonDuck: Chinese security firm Antiy has put out a report on the LemonDuck malware.
HinataBot: Akamai researchers have discovered a new Go-based botnet named HinataBot that appears to have been built to launch DDoS attacks. Akamai says HinataBot has been active in the first three months of 2023 and is actively being updated by the authors/operators. Currently, the botnet runs on compromised Huawei HG532 routers, exposed Hadoop YARN servers, and IoT devices using the Realtek SDK.
Magniber comes to Europe: Google's security team says that the threat actor behind the Magniber ransomware has recently changed their mode of operation and is now targeting users across Europe. This is a significant shift in Magniber activities, which have exclusively targeted South Korea since the ransomware was first spotted in 2017. Google says it observed more than 100,000 file downloads carrying Magniber payloads since the start of the year, and more than 80% of these were in Europe. This recent Magniber campaign also stands out because the gang also discovered and abused a Windows zero-day (CVE-2022-44698) to bypass Mark-of-the-Web protections and run their payloads.
BianLian ransomware: Cybersecurity firm Redacted says that the BianLian gang has changed tactics ever since Avast released a decrypter for their ransomware strain at the start of the year. The gang is still active, but since it cannot use its ransomware anymore, it is only engaging in data theft and then extorting companies for payments by threatening to release sensitive files online. One of the tactics employed by the gang is to study local laws in the victim's jurisdiction and tailor their threats accordingly.
"In several instances, BianLian made reference to legal and regulatory issues a victim would face were it to become public that the Organization had suffered a breach. The group has also gone so far as to include specific references to the subsections of several laws and statutes. While the applicability of the laws (to the victim and their data) referenced by BianLian would need to be assessed by the courts, at first glance, the laws referenced by the actors did in fact correspond to the jurisdiction where the victim was located. This attention to detail shows that the criminal gang is taking the extra time to tailor threats to their victims to maximize the pressure to pay the ransom."
Trigona ransomware: PAN's Unit42 has a report out on a new ransomware strain named Trigona that has been making the rounds since October of last year. Also covered by Fortinet earlier this year here.
LockBit 3.0: CISA and the FBI have published a joint malware report on the new version of the LockBit ransomware, also known as LockBit 3.0 or LockBit Black.
SilkLoader: WithSecure has identified a new malware strain they are calling SilkLoader that is currently being used by Chinese and Russian cybercrime groups. The malware leverages side-loading through the VLC media player to install Cobalt Strike beacons on infected hosts. WithSecure says it has seen SilkLoader in "several human-operated intrusions that resembled precursors to ransomware deployments."
HookSpoofer: Uptycs threat research team has discovered a new infostealer with keylogging and clipper capabilities named HookSpoofer. The stealer is coded in C# and based on an open-source program named Stormkitty.
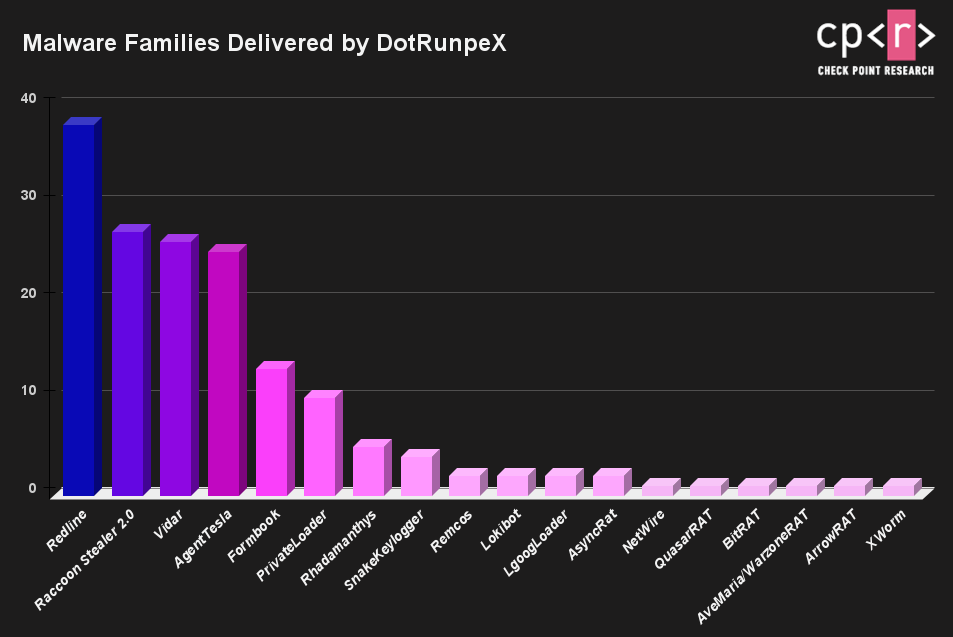
DotRunpeX: Check Point has a breakdown of a new .NET loader that is currently being deployed in the wild. The new loader is named DotRunpeX, and according to the company, it is typically dropped as a second-stage payload on already infected systems as an intermediary stage that can allow cybercrime gangs to deploy a more powerful third-stage payload. DotRunpeX has been seen in the wild since at least October last year and has been used to drop a wide assortment of infostealers and RATs.
Sponsor Section
Airlock Digital is one of this newsletter's four main supporters and this week's featured sponsor. Earlier this year, in May, Airlock Digital CEO David Cottingham held a product demo with Patrick Gray, the host of the main Risky Business podcast, showing how Airlock's allow-listing product works.
APTs and cyber-espionage
Kimsuky: South Korean security firm AhnLab has a 44-page English report on the 2022 activities of the Kimsuky APT. The report focuses on the group's tooling and sheds some light on its new FlowerPower killchains.
Reaper (APT37): Security firm Sekoia says it was able to gain access to two command and control servers operated by Reaper (APT37), a North Korean APT group, and get a gleam of the group's tools, including its use of a phishing kit capable of bypassing 2FA. This one supported phishing iCloud, Naver, and Kakao accounts.
Saaiwc: Qihoo 360 published a report on attacks carried out by the Saaiwc (Dark Pink) APT against targets in Indonesia.
APT-C-36 (Blind Eagle): Lab52 published a report on APT-C-36 (Blind Eagle), an APT group they say has "many similarities in terms of tactics, techniques and procedures (TTPs) with the group Hagga/Aggah."
Winter Vivern: SentinelLabs has published a report detailing the activities of an APT group "aligned with global objectives that support the interests of Belarus and Russia's governments." Named Winter Wivern (UAC-0114), attacks by this group have been spotted by CERT-UA and Poland's BCZC cybercrime agency. The group's past operations were previously documented by DomainTools in 2021.
Nobelium: BlackBerry has a report out on Nobelium (APT29) attacks targeting EU governments aiding Ukraine.
Sandworm boss dox: A Wired piece has identified Evgenii Serebriakov as the leader of Sandworm, the most aggressive hacking team of Russia's GRU military spy agency. Wired reports, citing intelligence service sources, that Serebriakov was placed in charge of Sandworm in the spring of 2022 after serving as deputy commander of APT28, another one of the GRU's cyber units. Serebriakov is known to western intelligence as he was charged in 2018 for being directly involved in a botched hacking attack against the Organization for the Prohibition of Chemical Weapons in the Hague, Netherlands.
Iridium: Microsoft has a report [PDF] on Russian cyber activity in Ukraine last year. The report covers mostly Iridium (Sandworm) APT activity and also covers one of its ransomware strains named Sullivan (aka RansomBoggs).
"MSTIC observed at least three variants of this ransomware deployed against one Ukrainian Organization over the course of three to four days, reflecting iterative development and refinement for modular functionality and improved detection evasion. As of December, MSTIC had only observed Sullivan at two Ukrainian organizations with no obvious military or political significance. IRIDIUM's use of ransomware in Poland and the testing and refinement of Sullivan on networks that seem more like cyber test ranges than actual targets suggest the actor is preparing Sullivan, or related malware, for use outside of Ukraine."
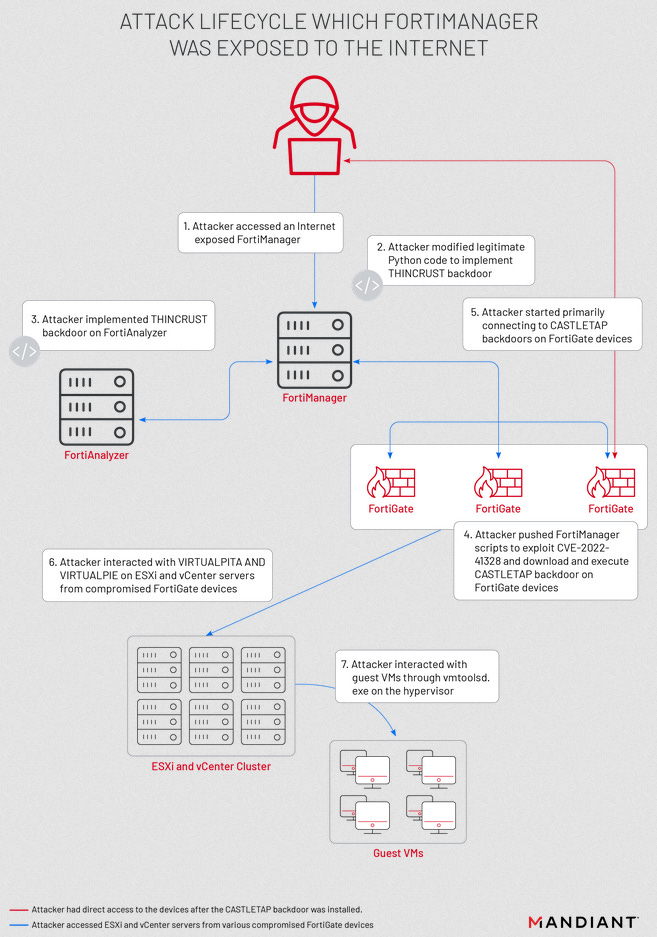
UNC3886 and Fortinet: Google's Mandiant division says that the recent attacks against Fortinet devices using a zero-day tracked as CVE-2022-41328 have been the work of a suspected Chinese cyber-espionage group it tracks as UNC3886. Fortinet confirmed the zero-day attacks last week. In a blog post, the company says the zero-day was exploited by "an advanced actor" in "highly targeted" attacks at governmental or government-related organizations. Mandiant says it saw UNC3886 compromise VMWare ESXi systems last year and observed the group connect to the compromised servers from Fortinet devices on multiple occasions.
Vulnerabilities and bug bounty
Chess.com vulnerability: Security firm Check Point has discovered, reported, and helped fix a vulnerability in the popular Chess.com platform. The vulnerability could have been used to extract successful chess moves to solve online puzzle challenges and win puzzle ratings, and decrease an opponent's time and win games.
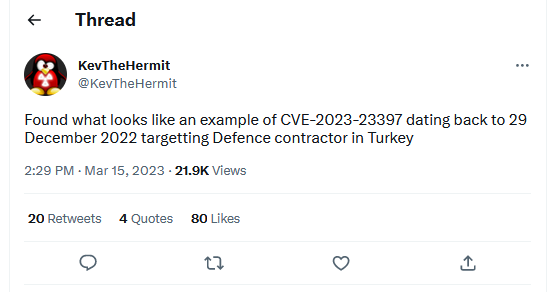
Outlook RCE script: Microsoft has published a PowerShell script to enable owners of Exchange email servers to scan messaging items (mail, calendar, and tasks) to see if item properties contain UNC paths. The presence of such artifacts is a typical sign a threat actor has sent a malicious email to the server and tried to exploit CVE-2023-23397, an Outlook zero-day that Microsoft patched this week. The bug was actively exploited in the wild by a Russian threat actor since last year as part of a cyber-espionage campaign targeting organizations across Europe.
Infosec industry
JSAC2023 review: JPCERT/CC has published summaries and materials from the JSAC2023 security conference the Organization hosted at the end of January.
Acquisition news: Rapid7 has acquired Minerva Labs, an Israeli company that builds anti-evasion and ransomware prevention technology.
New framework: Two of Meta's chief security and disinfo investigators have published a new framework that security teams can use to break down attacks and catch attacks at their earliest stages.
"The kill chain consists of ten links. Each link represents a top-level tactic—a broad approach that threat actors use."





