Why China's Latest APT Campaign is Legitimately Worrying
PLUS: A Tale of Two Spywares
Your weekly dose of Seriously Risky Business news is written by Tom Uren, edited by Patrick Gray with help from Catalin Cimpanu. It's supported by the Cyber Initiative at the Hewlett Foundation and this week's edition is brought to you by Nucleus Security.
Why China's Latest APT Campaign is Legitimately Worrying

Reports that a state-sponsored PRC cyber actor could be pursuing capabilities to disrupt US critical infrastructure are causing a stir.
This eye-catching nugget is contained within a Microsoft report about a group it calls Volt Typhoon. Microsoft thinks, with "moderate confidence", that Volt Typhoon's campaign is "pursuing development of capabilities that could disrupt critical communications infrastructure between the United States and Asia region during future crises".
The statement actually feels a bit out of place in the report as it doesn't contain any evidence that backs up the assessment. The report says that Volt Typhoon "typically focuses on espionage and information gathering", although it has "targeted critical infrastructure organisations in Guam and elsewhere in the United States". Microsoft says that in this campaign, affected organisations "span the communications, manufacturing, utility, transportation, construction, maritime, government, information technology, and education sectors".
Microsoft isn’t alone in this assessment. Matt Olney, Cisco's director of threat intelligence, told Reuters that the networking vendor had also encountered the group during a critical infrastructure incident, and concluded that the best explanation for the adversary’s activities was preparation for disruption. Per Reuters:
The hackers were hunting for documentation showing how the facility worked, Olney said, and they did not appear to be after money. He would not provide details but said "it's the kind of critical infrastructure that would definitely be targeted in a conflict."
"We definitely had alarm bells going off," he said.
Likewise, John Hultquist, Mandiant's head of threat intelligence, told Wired that in Mandiant's experience with the group "there's not a clear connection to intellectual property or policy information that we expect from an espionage operation". This raises concerns that the purpose of some of these campaigns may be to prepare for potentially destructive operations.
The group has popped up in some worrying places. The US Navy is confirmed to have been impacted in this campaign and Volt Typhoon had been quite active in Guam-based networks. Guam is key to the US's military presence in the Pacific, but it is also a telecommunications hub with nearly a dozen submarine cables landing there. Telco operations on Guam could be targeted to enable further access for espionage purposes, but would also make a superb target for disruption.
Microsoft's report didn't arrive in isolation. The Five Eyes cyber security authorities also issued a joint advisory detailing Volt Typhoon's activity. The statement doesn't mention potentially disruptive operations, but NSA official Rob Joyce told CNN the agency is on board with Microsoft's call.
"We assess this is prepositioning against critical infrastructure — more broadly than just [potentially] interrupting communications," Joyce said, adding: "We do agree with the Microsoft assessment."
This, more than anything, makes us think that there are genuine reasons to be concerned and that Microsoft is saying what some in the US government are already thinking.
The IC and private industry arrive at these assessments via different routes, too. Companies like Microsoft and Mandiant draw inferences from looking at a threat actor's actions, but agencies like NSA have other tools at their disposal that can divine an adversary's intent. They are spy agencies and it's their job to figure these things out.
Other countries, including Russia, North Korea, and Iran have conducted destructive cyber operations. So of course it makes sense for the PRC to do its homework and see if disruptive cyber operations might be useful in the event of a possible conflict. But why now?
There are a couple of different possibilities here. The best case scenario is this is just-in-case positioning — get the access in case you need it later. The worst case scenario is this is a calculated step towards a military action in the Taiwan Strait.
As with any coordinated disclosure there is a fair bit of signalling involved here. One message, to the PRC, is "you've been busted". Another, to critical infrastructure operators is that "stakes are high, up your game".
They'll need to. Volt Typhoon's tradecraft is best described as "contemporary". It uses a variety of different techniques that hinder detection including using valid credentials, abusing legitimate tools already present in the host environment (aka living off the land) and proxying network traffic via compromised small and home office routers. Its operators rarely use malware and cover their tracks by clearing logs.
Thankfully, it seems like it’s early days for Volt Typhoon and "hunting for documentation" is at least a few steps away from "Cyber Pearl Harbour".
A Tale of Two Spywares
NSO Group is under new ownership that places Omri Lavrie, one of NSO's co-founders, in control, according to The Wall Street Journal. Per the journal:
The company’s lenders believe that NSO has valuable intellectual property and should continue operating rather than shut down and liquidate, even though its finances are in turmoil, people familiar with their thinking said. They have agreed not to call NSO in default for failing to pay debts to them since the 2021 blacklist and have extended millions of dollars to help pay NSO’s expenses since then, the people said.
NSO probably does have valuable intellectual property, but in our view its value as an ongoing concern is diminished somewhat by the Biden administration doing whatever it can to make sure the company dies in a ditch.
In contrast to NSO Group, Paragon Solutions, another Israeli spyware manufacturer, has made sure to stay in the US government's good books. The Financial Times reports on these efforts:
American approval, even if indirect, has been at the heart of Paragon’s strategy. The company sought a list of allied nations that the US wouldn’t object to seeing deploy [Paragon's product] Graphite. People with knowledge of the matter suggested 35 countries are on that list, though the exact nations involved could not be determined. Most were in the EU and some in Asia, the people said.
“Everything they did was with the strategy that at the end of the day, the US should see them as the good guys,” said one person familiar with the decisions.
One of Paragon's first steps in this regard was to engage a DC-based consultancy, WestExec Advisors, which at the time included Antony Blinken and Avril Haines, who are now Secretary of State and Director of National Intelligence respectively. WestExec told The Financial Times it advised Paragon "on its strategic approach to the US and European markets, as well as the formulation of its industry-leading ethical commitments".
This approach has some opportunity costs. Apparently Paragon declined to sell to the Saudi government in the wake of NSO's involvement in the targeting of Jamal Khashoggi, The Washington Post correspondent who was murdered by the Saudi government. Despite that, staying on the right side of the US is paying off — Paragon still has a business and even has the US Drug Enforcement Agency as a client.
This is what success against mercenary spyware looks like. The goal is not the eradication of spyware from the global market. The goal is to limit the sale of spyware to countries the US government trusts with these capabilities.
Listen to Patrick Gray and Tom Uren discuss this edition of the newsletter in the Seriously Risky Business podcast:
Three Reasons to be Cheerful this Week:
- PyPi to enforce 2FA: The Python Software Foundation will require all accounts that maintain a python library must have two-factor authentication turned on by the end of the year. The foundation is also working to purge its server logs of IP addresses, replacing them instead with IP address hashes. [more on Risky Business News]
- Malicious domains hosted by Freenom decline: The number of phishing websites hosted on top-level domains managed by domain registrar Freenom has declined significantly. Freenom was responsible for over half of all country code top level domains reported for phishing, but this has now declined to under 15%. This follows a lawsuit from Meta in which it complained that Freenom was providing free domain name registration services even after receiving evidence that customers were using sites for phishing or other malicious purposes.
- Legit hacking in space: The US Government's ISS National Laboratory is launching Moonlighter, a small hacking sandbox satellite to enable "real-time cyber security testing in orbit". We're not exactly sure how it is better than an Earth-based testbed, but it is surely way cooler.
Sponsor Section
In this Risky Business News sponsor interview, Catalin Cimpanu talks with Patrick Garrity, VP of Marketing and security researcher at Nucleus Security, on how the company has been tapping into CISA's KEV database for insights on vulnerability management and prioritisation.
And in this product demo Nucleus Security's COO Scott Kuffer shows Risky Business podcast host Patrick Gray their vulnerability management platform. It ingests scan outputs from a number of vulnerability identification tools, normalizes that information, and then allows vulnerability management teams to do things like assign responsibility for certain types of bugs to the correct people.
Shorts
Show Me the Money
Chinese hackers targeted the Kenyan government after the country started having difficulty repaying loans made to it under China's Belt and Road Initiative. Sources told Reuters that the hacks were aimed, at least in part, at gaining information on the debt owed to Beijing. Of course as the PRC's interests become more global so do its intelligence collection requirements.
Iran Pivots from Wipers to Ransomware
An Iranian group, Agrius, has deployed new ransomware called Moneybird that is written in C++. The group, also known as Black Shadow, is reportedly tied to the Iranian Ministry of Intelligence and Security and has over time evolved from launching destructive attacks masquerading as ransomware to actually deploying real ransomware. The group's main targets are, of course, Israeli organisations.
Getting paid to cause mayhem is nice, getting paid twice is even nicer.
So Many Phish In the Sea
Group-IB reports 3,677 unique phishing kits were used in the wild last year, up 25% from the previous year. Many kits use techniques to avoid detection by security firms and most use an email account or Telegram channel to receive phished credentials.
The Fluffy and Friendly ICS Malware
Mandiant has found malware designed to cause electric power disruption and thinks it may have been written to use for Russian red team exercises simulating power disruption attacks. Mandiant thinks that even this possibility is worrying as it suggests that "the barriers to entry are lowering" for malware that disrupts industrial control systems.
Risky Biz Talks
You can find the audio edition of this newsletter and other fine podcasts and interviews in the Risky Biz News feed (RSS, iTunes or Spotify).
In our last "Between Two Nerds" discussion Tom Uren and The Grugq look at how criminals — and spies — try to protect themselves from state adversaries.
From Risky Biz News:
Iranian hacktivists breach president's office, leak sensitive files: An Iranian hacktivist group calling itself "Uprising 'til Overthrow" has breached the Iranian President's Office and leaked a large collection of classified documents.
According to a press release posted on the website of exiled opposition party MEK, the group claims to have taken control of more than 120 servers and over 1,300 computers from the network of the President's Office.
The group claims to have had full control over the entire network, to the point they were able to decrypt classified material and encrypted communications from the past several years. [more at Risky Business News]
Void Rabisu and RomCom's evolution: A financially motivated threat actor known as Void Rabisu (Tropical Scorpius) has significantly changed its mode of operation since October 2022. The group is known for operating the Cuba ransomware and the RomCom backdoor, which it offers under a malware-as-a-service model. Trend Micro says that since October 2022, the RomCom has been used in a series of geopolitically motivated attacks linked to the Ukrainian conflict. The security firm says it has seen RomCom in campaigns targeting the Ukrainian government and military, but also organisations outside Ukraine that were linked to the conflict. This includes a local government that provides help to Ukrainian refugees, a parliament member of a European country, a European defence company, and various IT service providers in Europe and the US. Trend Micro's report confirms similar findings by BlackBerry's security team, which assessed the cybercrime group was now working for the Russian government.
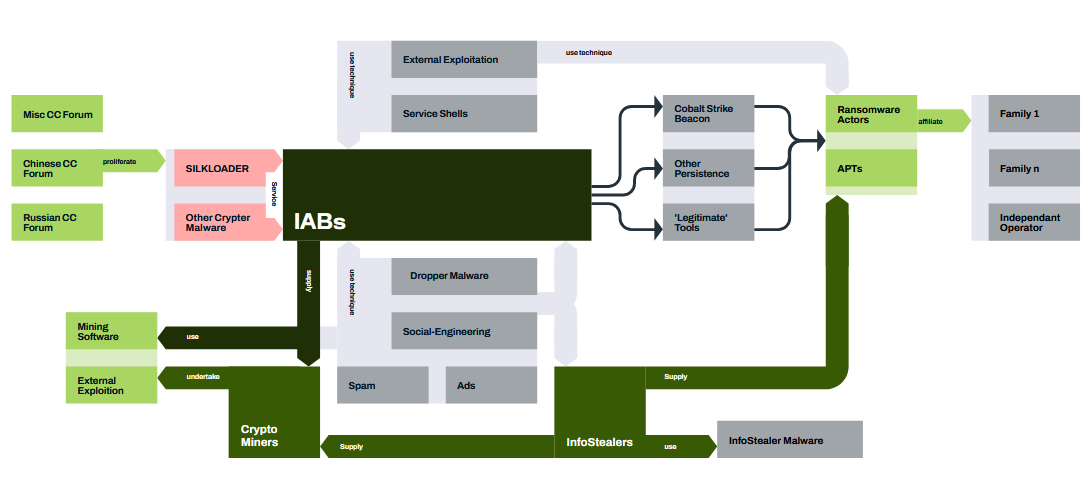
Professionalisation of cybercrime: Back in April, Trend Micro published a report on the professionalisation and specialisation of the cybercrime landscape. On the heels of that report, WithSecure has a deeper dive into the topic, showing how the underground cybercrime ecosystem has slowly adapted to provide highly specialised services, an evolution from the old 2010s when each cybercrime ecosystem was trying to provide all-out offerings. Now, you have groups dedicated to crafting exploits, gangs specialised in initial access, people specialised in expanding that initial access, ransomware gangs, MaaS platforms, money mule services, and so on. Many of these services are then offered to one another, with groups supporting each other's operations.