Risky Biz News: Two ransomware gang websites go puff!
In other news: Mandiant reveals secret Citrix zero-day; DPRK hackers target JetBrains TeamCity servers; and Five Eyes warn of increasing Chinese espionage.
This newsletter is brought to you by application allow-listing software maker Airlock Digital. You can subscribe to an audio version of this newsletter as a podcast by searching for "Risky Business News" in your podcatcher or subscribing via this RSS feed. On Apple Podcasts:
Two ransomware gangs have had their dark web server infrastructure disrupted this week in two extremely different circumstances, with hacktivists wiping the servers of the Trigona gang and law enforcement seizing RagnarLocker's infrastructure a day later.
The first to fall was Trigona, a ransomware operation that began operations in June of last year.
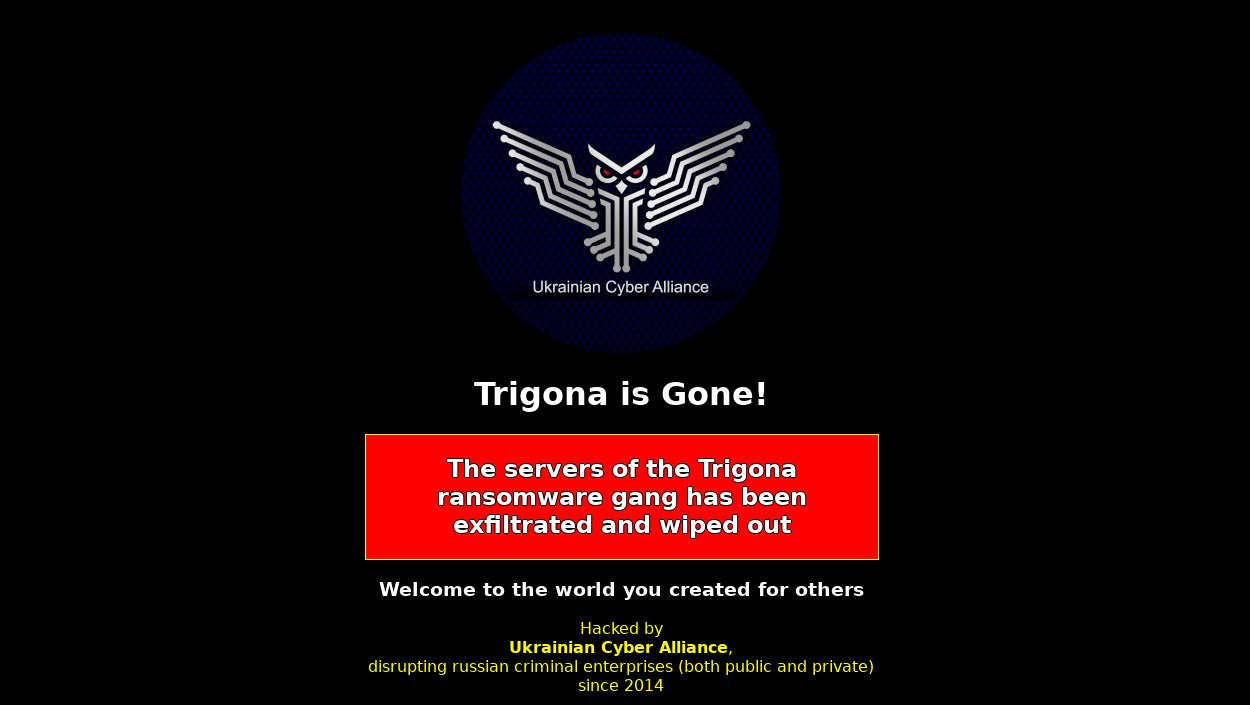
In Facebook and Twitter posts, a group of pro-Ukrainian hacktivists named the Ukrainian Cyber Alliance said they hacked the backend servers supporting Trigona's operations.
The apparent intrusion began last week when one of the group's members breached Trigona's Atlassian Confluence server—go figure!
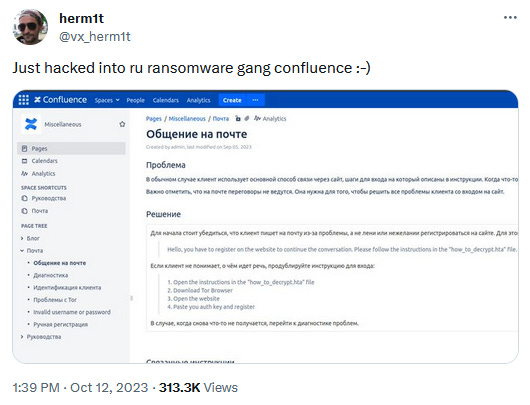
Once inside, the group says it made copies of Trigona's victim data, and then wiped their infrastructure clean. This included ten servers hosting the Trigona dark web leak site, RaaS backend, source code, internal chat rooms, and even Trigona's cryptocurrency wallets.
The Ukrainian Cyber Alliance didn't say how much money the wallets were holding, but they told The Record that they plan to share some of the Trigona data with security researchers.
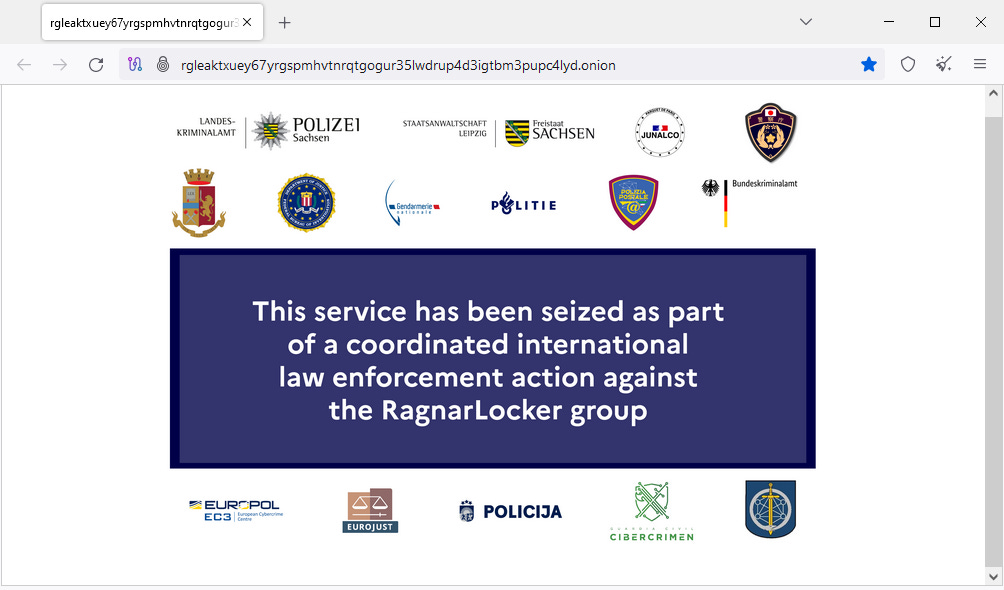
One day after Trigona's demise, the website for the RagnarLocker gang also went down, with a takedown message listing the logos of the FBI, Europol, and more than a dozen European law enforcement agencies.
Contacted by TechCrunch, Europol confirmed the takedown but said they plan to reveal more details on Friday—a few hours after this newsletter goes live.
While we might not have all the details of this takedown in this edition, the action is extremely significant. The RagnarLocker group was one of the oldest ransomware gangs that were still active. Launched in early 2020, most ransomware groups that launched around that time have long succumbed to in-fighting, rebrands, and law enforcement takedowns.
Even if RagnarLocker was not one of the most active ransomware groups today, it is still good news seeing it bite the dust regardless!
Breaches, hacks, and security incidents
CIA Twitter channel hack: A security researcher has exploited a Twitter bug to hijack a link shared by the CIA on its official account and redirect users seeking to access the CIA's Telegram informant channel with a link to his own.
Hamas hijacks accounts of kidnapped victims: Hamas operators have used the smartphones of kidnapped Israelis to hijack their online accounts and spread propaganda and threats of violence. [Additional coverage in the New York Times/non-paywall]
Real Sociedad cyberattack: Spanish football club Real Sociedad are dealing with a cyberattack that has impacted some of its servers and databases.
certSIGN cyberattack: certSIGN, an official provider of e-signatures for the Romanian government and the private sector, has suffered a ransomware attack. The company restored service after a day.
23andMe leak: The hacker behind the 23andMe data breach has published online the personal information of 4.1 million of the site's users. The data is mostly for UK and German users. Known as Golem, the hacker previously leaked the data of 1 million Ashkenazi Jews. 23andMe confirmed the breach at the start of the month but downplayed its severity. [Additional coverage in TechCrunch]
Casio ClassPad breach: Japanese electronics giant Casio says that hackers breached its ClassPad educational platform and stole the personal data of registered users. The company confirmed the breach after hackers began advertising the ClassPad data on an underground hacking forum in September. Casio says the hacker stole the data of more than 91,000 customers across 149 countries.
CloudChat hack: A threat actor has compromised the website of the CloudChat instant messaging platform and modified the company's Windows installer to deliver malware. It's unclear for how long the backdoored installer was live, but security firm Sophos says it spotted the incident in August and notified the vendor. While it has not received a reply, Sophos says the app's website appears to have now been secured.
BigWhale crypto-heist: The BigWhale DeFi platform has lost $1.5 million worth of crypto-assets after one of its private keys leaked online. The company has promised to refund investors up to "the last cent."
Everscale crypto-heist: The Everscale cryptocurrency project has halted operations after a large number of its tokens were mysteriously stolen. The token's value dropped by 20%. The value of the theft remains unknown. [Additional coverage in Crypto News]
General tech and privacy
Twitter to charge new users: Twitter is moving forward with its plan to charge new users to post on the site. The company is currently running an experiment in New Zealand and the Philippines to see how the new system works and has plans to expand it globally. Twitter says it's taking this step as a way to fight bots. The site has been flooded with bots after Musk's takeover, going from the 300 million MAU it had for half a decade to more than 550 million MAU this year.
Hidden Brave VPN service: The Brave browser was caught installing a hidden VPN service on Windows systems, even if the browser user is not a customer of the company's VPN+firewall offering. [Additional coverage in gHacks]
Microsoft log retention: Starting with October 2023, the log retention period on Microsoft Purview accounts is now 180 days—instead of 90—for both standard and premium customers. Microsoft announced this change back in July after its systems were breached by Chinese hackers, and the lack of proper logs hindered IR investigations.
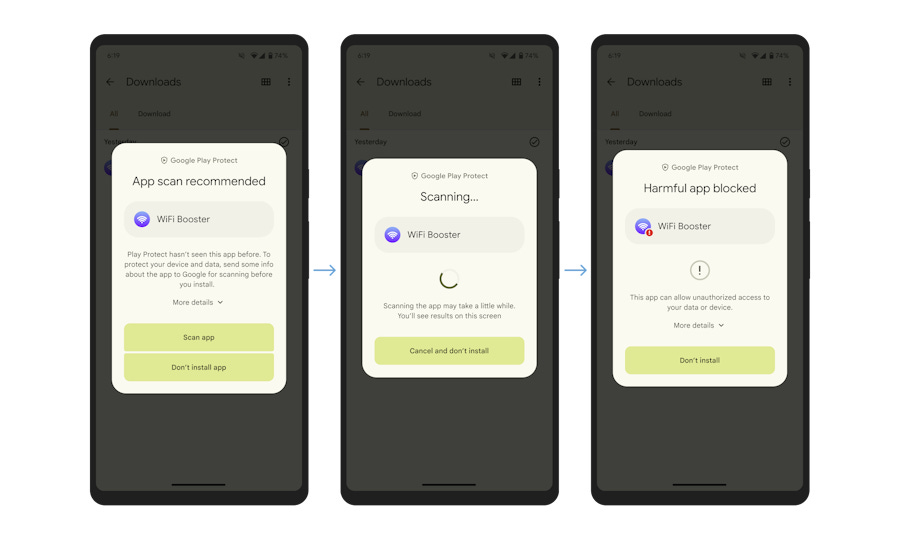
Google Play Protect update: Google has updated the Play Protect security feature on Android phones to perform real-time scans of suspicious apps.
"Google Play Protect will now recommend a real-time app scan when installing apps that have never been scanned before to help detect emerging threats. Scanning will extract important signals from the app and send them to the Play Protect backend infrastructure for a code-level evaluation. Once the real-time analysis is complete, users will get a result letting them know if the app looks safe to install or if the scan determined the app is potentially harmful."
Government, politics, and policy
Mandatory cyber insurance in Russia: The Russian government is considering introducing a new law that would require mandatory cyber insurance for all public and private companies. Discussions on the law began in June but have been moving slowly. The primary cause is the lack of cyber insurance providers across Russia. [Additional coverage in Kommersant]
Russia builds more internet walls: The Kremlin is working on a law to block access to online games unless they store servers inside Russia. The move comes after several pro-Ukraine and anti-Russian protests were included in some online games, such as Roblox and CounterStrike. [Additional coverage in RBC]
Western companies in Russia: RecordedFuture looks at the dilemma facing Western companies that still have assets in Russia.
"Russia is aware of the corporate dilemma, where Western companies must decide whether to stay in Russia and risk potential targeting or leave and face asset loss but gain Western praise."
Phishing guidance: CISA, the NSA, and the FBI have published a report with guidance on how to stop the latest phishing techniques.
Five Eyes warn of Chinese IP theft: The heads of the Five Eyes intelligence-sharing alliance held their first-ever joint press conference to warn that China is engaging in a concerted campaign to steal cutting‐edge intellectual property from democratic countries. Officials from Australia, Canada, New Zealand, the UK, and the US say the campaign ranges from online hacks to classic human intelligence operations where spies approach targets to spy on their behalf. UK officials say that only in their country alone, spies have approached more than 20,000 people to spy on behalf of China. FBI Director Christopher Wray says China is primarily interested in technologies such as AI, robotics, biotech, and quantum computing.

Sponsor section
In this Risky Business News sponsor interview, Catalin Cimpanu talks with Airlock Digital founders Daniel Schell and David Cottingham about the recent Microsoft Digital Defense Report and the problem of properly securing PowerShell.
Cybercrime and threat intel
E-Root admin arrested: US authorities have indicted a Moldovan national on crimes related to running E-Root, an online marketplace that sold access to hacked computers. Sandu Diaconu was detained in the UK in May 2021 and extradited and arraigned in a US court this week. Diaconu ran E-Root for years until the end of 2020, when the FBI seized the site. Officials say E-Root sold access to more than 350,000 computers across the world, with access being provided via RDP and SSH.

Tech CEO sentenced for IP address theft: US authorities have sentenced the CEO of Micfo LLC to five years in prison for defrauding the American Registry of Internet Numbers (ARIN). Amir Golestan, 40, of Charleston, pleaded guilty to tricking ARIN into granting his company more than 750,000 IPv4 addresses that he later sold on the black market for $3 million in profit. [Additional coverage in KrebsOnSecurity]
US seizes DPRK websites: The US government has seized 17 websites used by North Korean IT workers to disguise their identity and get hired by US companies. The group used the websites to pose as US-based software development companies in order to evade sanctions and pick up outsourcing contracts. The Justice Department says it also seized bank accounts holding $1.5 million in illicit funds generated by the group. Officials say that thousands of North Korean IT workers have been sent to live abroad, and they generate millions in US dollars every year for the regime, money that is used to fund North Korea's weapons program. The FBI has issued updated guidance on how to spot and report DPRK IT workers. [Additional coverage in TheDailyBeast]
Indian government cracks down on tech support scammers: The Indian government raided call centers in 76 locations across the country that engaged in tech support and cryptocurrency scams. Officials detained suspects and seized equipment and bank accounts across 11 Indian states. Named Operation Chakra-II, India's Central Bureau of Investigation received help from Microsoft and Amazon, whose services and customers were often targeted by the scammers.
Notepad++ and KeePass malvertising campaign: Malicious Google Ads promoting malware-infested versions of the Notepad++ editor and the KeePass password manager have been running rampant on the Google search engine for months.
Failed ransomware attack: Sophos looks at a failed ransomware attack with a LockBit knock-off on a company's network, via their Adobe ColdFusion server.
Default password research: Security firm Outpost24 has found that more than 1.8 million leaked admin accounts had been using insecure and easy-to-guess passwords. The most common password was "admin," which researchers found used for more than 40,000 admin accounts. Other common passwords such as "123456," "root," and "Password" also made the Top 20.
Office file formats: Intezer looks at all the different Microsoft Office file formats and how to deal with them during IR engagements.
Web malware evolution: Sucuri researchers explain how threat actors have evolved from using JS and PHP files to store malicious code to using non-executable file formats like LOG and TXT. The technique allows threat actors to avoid having their code spotted by security scanners but also load the content of the LOG or TXT files inside JS and PHP files at runtime without detection.
LATAM threat landscape: As part of its talk at the VirusBulletin conference, ESET researchers have analyzed the threat landscape of Latin America, and the various cybercrime groups active in the region.

Malware technical reports
Qubitstrike: A threat actor named Qubitstrike is targeting internet-connected Jupyter Notebooks hosted in Google and AWS cloud infrastructure. The campaign targets Jupyter Notebooks with weak credentials. Once inside, the group deploys a rootkit, extracts cloud credentials from the compromised host, and moves to other cloud systems in order to mass-deploy a cryptominer. Cado Security researchers believe the threat actor may be based in Tunisia.
Munchkin: Palo Alto Networks has a report on Munchkin, a tool used by the BlackCat (AlphV) ransomware gang to move laterally across breached victim networks and push its file encryptor to as many machines as possible.
Sponsor Demo
Airlock Digital CEO David Cottingham shows Patrick Gray how Airlock's execution control and allowlisting solution works.
APTs and cyber-espionage
More WinRAR abuse: In our Monday (Oct 16) edition, we covered how several APT groups (APT28, Konni, DarkPink) were abusing a recently patched WinRAR zero-day (CVE-2023-38831) as part of their operations. Since then, Google TAG has also published a report highlighting the same thing. Besides APT28 (FROZENLAKE), Google says it also saw Russia's Sandworm (FROZENBARENTS) and Chinese group named APT40 (ISLANDDREAMS) also abusing the vulnerability.
Crambus: Iranian cyber-espionage group Crambus (APT34, OilRig, MuddyWatter) has breached the network of a Middle Eastern government for eight months between February and September 2023. According to Broadcom's Symantec division, the group backdoored and exfiltrated data from 12 computers. They also installed a PowerShell backdoor named PowerExchange on the government's Exchange email server in order to intercept communications in real time.
Hamas-Iran overlap: Recorded Future analysts have found server infrastructure overlaps between apps linked to the Hamas terrorist organization, Palestinian cyber-espionage group TAG-63 (AridViper), and Iran's Quds Force.
DPRK's TeamCity exploitation: Two North Korean hacking groups named Diamond Sleet and Onyx Sleet are exploiting a vulnerability in JetBrains TeamCity CI/CD servers to gain access and deploy backdoors and remote access trojans across enterprise networks. Tracked as CVE-2023-42793, the vulnerability was patched in late September, and attacks began at the start of October after proof-of-concept code was published online. Several ransomware groups have been spotted leveraging the vulnerability for initial access. Roughly 1,200 TeamCity servers are currently reachable online.
DPRK uses AI for malware: Deputy National Security Advisor Anne Neuberger says that North Korea is experimenting with using AI to write malicious code and find new systems to exploit. Other nation-state actors are also using AI, but Neuberger did not provide any other details. The exact quote is below. [Additional coverage in VentureBeat]
"So we have observed some North Korean and other nation-state and criminal actors try to use AI models to help accelerate writing malicious software and finding systems to exploit."
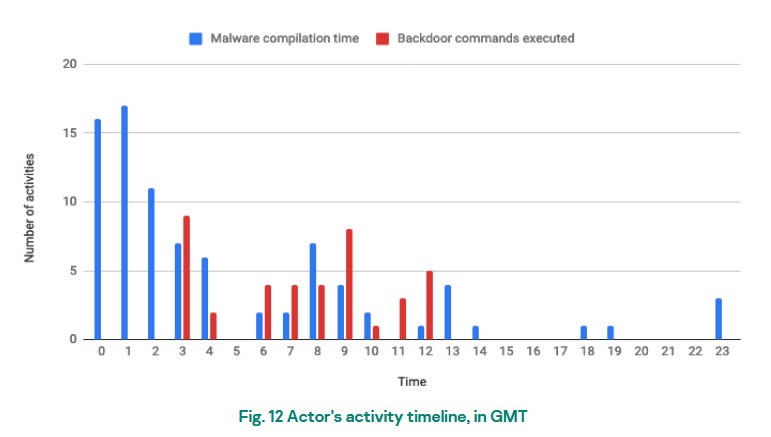
MATA campaign: Cyber-spies have targeted oil companies and defense contractors across Eastern Europe in what looks to be a suspected North Korean operation. The attacks took place between August 2022 and May 2023 and used an updated version of the powerful MATA malware framework. Discovered by Kaspersky, the company says the framework included both Windows and Linux malware, stealers, EDR bypassing tools, and even a USB worm to collect data from air-gapped networks. Kaspersky researchers have not formally attributed the attacks but noted the MATA code contains similarities to malware previously used by North Korean and Five Eyes APT groups. An analysis of malware compilation times seems to point the finger at a group based in Korean, Chinese, and Vietnamese time zones. While Kaspersky did not name the group, it appears this is what PT Security has previously named Dark River.
Vulnerabilities, security research, and bug bounty
Secret Citrix zero-day: Google's Mandiant division says that a recently patched Citrix vulnerability has been exploited in the wild since the end of August. Tracked as CVE-2023-4966, the vulnerability impacts ADC and NetScaler devices and was patched on October 10. Mandiant says the zero-day can allow attacks to hijack existing user sessions and bypass authentication requirements. The company is now warning owners of Citrix ADC and NetScaler devices to install the recent patch and invalidate all existing user sessions to prevent threat actors from abusing old sessions.
More info on the Adobe Reader zero-day: North Korean hackers have exploited an Adobe Reader zero-day (CVE-2023-26369) in a social engineering campaign that targeted security researchers this year. The Adobe Reader zero-day is the unnamed zero-day that Google mentioned in a blog post in September. North Korean hackers have been targeting security researchers for the past two years in an attempt to steal exploits and research on unpublished vulnerabilities. The recent campaign stood out because, besides GitHub and Twitter, North Korea also contacted security researchers active on the Mastodon network. Besides the recent Adobe Reader zero-day, in the past, North Korean hackers also used an Internet Explorer zero-day to compromise the PCs of security researchers.
Synology NAS bugs: Claroty researchers have discovered that Synology NAS devices are using a weak RNG algorithm that can allow threat actors to reconstruct the admin account password and take over the device. Tracked as CVE-2023-2729, the issue was fixed in June.
Oracle CPU: The quarterly Oracle security updates are out, with patches for 387 vulnerabilities.
Caliptra security audit: NCC Group has conducted a security audit of Caliptra, a firmware solution for implementing Root of Trust on datacenter-class SoCs. The security audit was contracted by Microsoft and found 26 vulnerabilities, all fixed now.
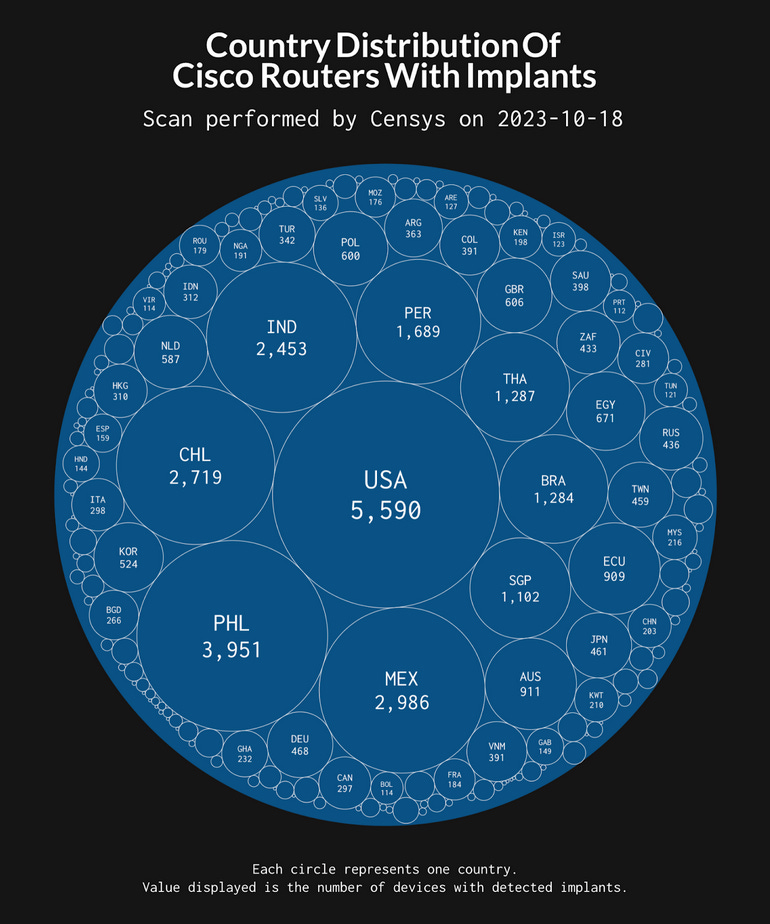
Cisco IOS XE carnage: The number of backdoored Cisco routers and switches via the recent IOS XE zero-day (CVE-2023-20198) has now almost reached 42,000. More in this GreyNoise analysis.
Infosec industry
New tool—Security Insights Specification: The Open Source Security Foundation (OpenSSF) has released the final version of the Security Insights Specification, a specification that provides a mechanism for projects to report information about their security in a machine-processable way.
Risky Business Podcasts
In this edition of Between Two Nerds, Tom Uren and The Grugq discuss how changing circumstances change the risk/reward balance and change whether effects operations are worthwhile.




