The Lawful Access Debate Becomes the Child Safety Debate
PLUS: What the Crypto Winter means for Lazarus
Your weekly dose of Seriously Risky Business news is written by Tom Uren, edited by Patrick Gray with help from Catalin Cimpanu. It's supported by the Cyber Initiative at the Hewlett Foundation and founding corporate sponsor Proofpoint.
This is the last edition of the year and we will be back in mid-January. The podcast version of this newsletter and Between Two Nerds with The Grugq will also have a break.
Last week Apple announced a number of new security improvements, including the ability for users to opt-in to End-to-End (E2E) encryption for iCloud backups. Law enforcement is, predictably, upset about this. These new features certainly have the potential to reignite the debate around lawful access to devices and user data. However, we think legislation and regulations that hone in on child safety are a more likely response to increasingly law enforcement-resistant tech ecosystems.
The most significant improvement—what Apple has dubbed "Advanced Data Protection for iCloud"—rolls out E2E encryption for most data that can be backed up to iCloud. This will be an opt-in feature and will roll out initially to US users before the end of the year and globally in early 2023. iCloud Contacts, Mail, and Calendar won't be E2E encrypted because of "the need to interoperate with the global email, contacts, and calendar systems".
Apple also announced other security improvements will be available in early 2023, including alerts when new devices are added to iMessage conversations and allowing security keys to secure Apple IDs. (more on Risky Business News). These security improvements aren't at all groundbreaking but are significant given Apple's prominence as a consumer device vendor and given its positioning as a privacy-first technology giant.
The company has also confirmed its since mothballed plans for on-device scanning for Child Sexual Abuse Material (CSAM), which were announced last year, are officially dead:
We have further decided to not move forward with our previously proposed CSAM detection tool for iCloud Photos. Children can be protected without companies combing through personal data, and we will continue working with governments, child advocates, and other companies to help protect young people, preserve their right to privacy, and make the internet a safer place for children and for us all.
However, Apple still plans to introduce other safety features that will pop up warnings for children who send or receive photos that contain nudity, for example.
The on-device CSAM-scanning technology was intended to tip off authorities if previously identified child exploitation material was found in a shared iCloud library. At the time, this new on-device scanning didn't really seem necessary because iCloud wasn't E2E encrypted. Apple could have scanned for CSAM server-side, the process typically used at companies that handle user-generated content. Given E2E encrypted iCloud backups, however, on-device scanning absolutely makes sense as a kind of compensating control.
The situation now, however, is that E2E backup encryption is being rolled out without increased protections against the spread of CSAM.
Current US legislation doesn't require companies to actively search for CSAM, but they have to report it to the National Center for Missing and Exploited Children if they find it. There is an international trend, however, towards legislation that forces companies to be more proactive when it comes to CSAM and online harms.
Australia's Online Safety Bill 2021, for example, requires that companies meet Basic Online Safety Expectations which are essentially set by Ministerial decree and so can be amended easily. These expectations don't currently require scanning for CSAM but instead require that "reasonable steps" be taken to minimise a variety of online harms that include child sexual exploitation material and behaviours such as grooming.
Draft UK, US, and EU legislation has similar intent. The language varies, but providers are required to do more to combat CSAM. Provisions that require scanning of E2E encrypted services when other mitigations are proven inadequate are explicitly spelled out. In one sense, scanning of E2E encrypted communications is being used as a stick, and lawmakers are effectively saying "find something that works against CSAM or else".
Although this is all draft legislation, we think stricter regulation is inevitable. It's justified, too, when we consider that companies could and should be doing more already.
Countering CSAM without putting E2E encrypted messaging at risk is achievable. Many approaches to this are captured in this report examining Meta's expansion of E2E messaging from a human rights perspective. Many of the suggestions have some sort of privacy impact — using metadata and behavioural analysis to identify problematic behaviour, for example — but we think that more action is justified here if it can mitigate risks to children.
Apple is well placed to weather all this. It has rolled out E2E encryption for iCloud backups but has its on-device scanning technology waiting in the wings if legislation requires it to implement some sort of CSAM scanning.
Aside from the implications around CSAM, Apple's announcement went down like a lead balloon at the FBI. It told The Washington Post it was "deeply concerned with the threat end-to-end and user-only-access encryption pose[s]". It continued:
This hinders our ability to protect the American people from criminal acts ranging from cyber-attacks and violence against children to drug trafficking, organized crime and terrorism. In this age of cybersecurity and demands for 'security by design', the FBI and law enforcement partners need 'lawful access by design'.
We don't see the FBI getting much traction here. The policy debate has shifted to child protection as a priority and the public is now well aware that law enforcement agencies have other options to access phones covertly.
But beyond upsetting domestic law enforcement agencies, there is an international angle here too.
Apple keeps its China-based user's iCloud data locally in the PRC, including encryption keys, in a data centre run by a state-owned mobile operator. Apparently, this was the price of doing business in China.
Surprisingly, Apple's software chief Craig Federighi told The Wall Street Journal he expected that E2E encrypted iCloud backups would be rolled out to Chinese users, saying "We believe so, we want to roll out across the world". When asked about the Chinese government's view, however, Federighi happily declared "They've not told me!"
We are not entirely convinced that it will happen, but there is an argument to be made that iCloud data localisation was just as much about preventing US spying rather than enabling domestic surveillance. In the wake of recent protests against strict Covid policies, for example, The New York Times reports facial recognition and phone tracking technology were used to identify protestors. And given the country's internet-based censorship and tracking, it simply has a lot of alternative ways to get information about individuals of interest. In other words, access to iCloud data may be a nice-to-have rather than a must-have for the PRC.
In the meantime, all eyes will be on western lawmakers who must decide whether to reignite the lawful access debate or settle for regulations designed to suppress the worst types of crimes against children.
Where Does North Korea Go as The Crypto Bubble Bursts
The US Department of Justice is reportedly considering charging executives of Binance, the world's largest cryptocurrency exchange, with various criminal charges, including for money laundering and sanctions violations. This comes after the recent collapse of the FTX cryptocurrency exchange and this week's arrest and indictment of its founder and former CEO Sam Bankman-Fried.
Before it imploded, FTX was once the world's third-largest cryptocurrency exchange. It was not a well-run enterprise. In addition to non-existent risk controls and generally chaotic management, there appears to have been some serious fraud happening there, and even the fraud was amateurish and chaotic. John Ray III, the new CEO of FTX appointed to clean up the bankruptcy, told the US House Financial Services Committee that as opposed to the sophisticated financial crimes committed at Enron in the 1990s, FTX's management engaged in "really just old fashioned embezzlement".
"This is just taking money from customers and using it for your own purpose. Not sophisticated at all," Ray continued.
We wonder what effects a "crypto winter" might have on cybercrime. Over the last year some of the most sophisticated hacks have involved North Korean groups just stealing cryptocurrency. Blockchain analysis company Chainalysis estimated in September that North Korea-linked groups had stolen about USD$1bn of cryptocurrency from DeFi protocols. These virtual dollars have been easy pickings for the North Koreans, but we wonder if the opportunities to steal cryptocurrency will be fewer and also less lucrative.
North Korea has been quite agnostic about how it has stolen money and in addition to cryptocurrency theft has also over time tried ATM cash-outs schemes, ransomware and also stolen from traditional banks by manipulating interbank SWIFT messages.
Stealing USD$1bn in funny money to fund North Korea's nuclear program is bad, but all the other schemes it has tried over the years are worse in that they cause more collateral damage, like undermining confidence in the global financial system.
Anyway, this is just our way of saying the average bank and credit union CISO might have to deal with a particularly nasty threat actor returning to their risk register in 2023. Good times!
Evaluating Our Ransomware Predictions
At the beginning of this year, we laid out a best and worst case for ransomware:
The best case: combined international efforts tamp down ransomware while defences improve ever so slowly. Worst case: ransomware escalates into a crisis as crews in multiple untouchable jurisdictions get involved.
We aren't at either extreme, but it seems we've reached some sort of equilibrium where ransomware crews avoid causing the most serious impacts (e.g. Colonial Pipeline), but are happy to cause very serious disruption within a (slightly) smaller blast radius.
In just the last couple of weeks we've seen attacks against Rackspace's hosted Microsoft Exchange environment, ransomware at the California Department of Finance, the Belgium city of Antwerp's IT systems, and ransomware at a New Zealand MSP affecting several government departments. Attacks against hospitals and healthcare generally have remained a constant theme in 2022.
Governments are stepping up to the plate and promising more robust responses: Australia announced a standing offensive cyber disruption operation and we expect others to follow. 2023 may be the year we find out if these new, offensive approaches actually pay dividends. Let's see.
Three Reasons to be Cheerful this Week:
- Google launches OSV-Scanner: OSV-Scanner is a free tool that helps developers understand whether projects include dependencies that contain vulnerabilities.
- When doxxing a cybercrime group pays off: An anonymous Twitter account doxxed members of the URSNIF malware operation, apparently in a plain old extortion attempt. The account outed three of URSNIF's members before being paid off. "I just made more money in a single week than I have made in years. Pay workers right and they won't have a reason to leak s***", the account tweeted. More on Risky Business News.
- Chrome now has passkeys support: Google has added support for passkeys to its Chrome web browser through an update released last week. Passkeys are an industry standard that allows users to log into apps or websites without entering a password and using a cryptographic token instead.
Sponsor Section
Seriously Risky Business is supported by the Hewlett Foundation's Cyber Initiative and corporate sponsor Proofpoint.
What your users don’t know about #cyberthreats can hurt them—and your org. This e-book explores real-world #cyberattack examples and five major categories that began with—or hinged on—compromising users.
— Proofpoint (@proofpoint) 7:55 PM ∙ Dec 7, 2022
Download at: ow.ly/49Tp50LWWy2
#phishing #ransomware #M356 #cloud
Okta and Passwordless Authentication
Risky Business publishes sponsored product demos to YouTube. They're a great way for you to save the time and hassle of trying to actually get useful information out of security vendors. You can subscribe to our product demo page on YouTube here.
In our latest demo, Brett Winterford and Harish Chakravarthy demonstrate to host Patrick Grey how Okta can be used for passwordless authentication. These phishing resistant authentication flows — even if they are not rolled out to all users — can also be used as a high-quality signal of phishing attempts that can be used to trigger automated follow-on actions.
Shorts
ChatGPT the new Phishing Hotness
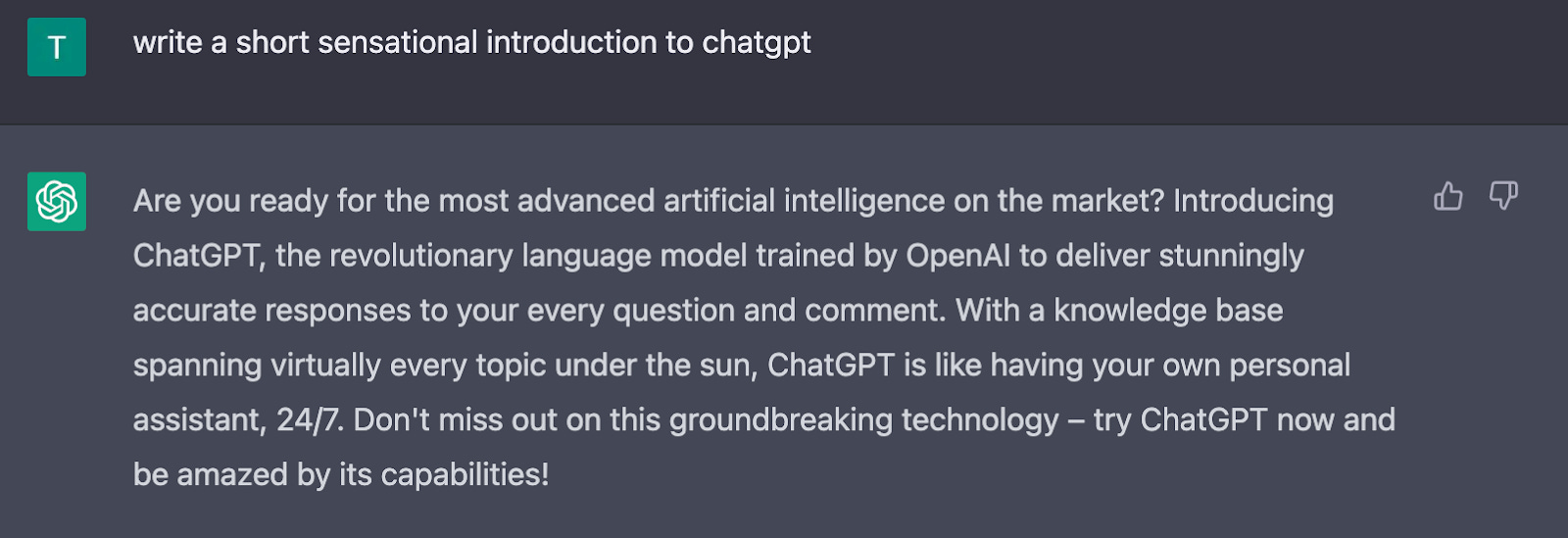
People are already examining how ChatGPT, which describes itself as "the most advanced artificial intelligence on the market" and claims to "deliver stunningly accurate responses to your every question and comment" can be used maliciously.
ChatGPT is incredibly limited, but good enough at some things to create a misleading impression of greatness.
— Sam Altman (@sama) 12:11 AM ∙ Dec 11, 2022
it's a mistake to be relying on it for anything important right now. it’s a preview of progress; we have lots of work to do on robustness and truthfulness.
Researchers have already examined how it can be used to write both better phishing emails that could lead to more successful phishing per delivered email, for example. Or it could lead to more varied phishing emails that are harder for companies to block en masse.
Sherrod DeGrippo, VP of Threat Research at Proofpoint, told Seriously Risky Business that she thinks the technology will eventually be used maliciously.
"The BEC and fraud actors, primarily based in Morocco and Nigeria are likely to find ways to use these to automate confidence and trust building in their victims".
Despite that, however, she doesn't see ChatGPT as a "huge evolution in tooling".
"Most of what could be done, they’re already doing," she continued. "Further, we have found that threat actors are relatively slow to adopt new technology at scale because they simply don’t need it. They’ll do what works until it stops working."
Of course it's already possible to detect ChatGPT-generated text, but we're guessing the amount of compute required to do that at scale would be substantial.
Disclosure: Proofpoint is a corporate sponsor of this newsletter.
Japan On Board with Disrupting Hackers
The Japanese government is planning to introduce laws to allow it to launch cyber operations to disrupt attackers when a potential risk is identified. This appears to be just one part of the Japanese government rethinking the country's pacifist approach to self-defence. The Washington Post reported this week that Japan will buy Tomahawk cruise missiles, describing it as a "stunning break with a long tradition of eschewing offensive weapons".
In isolation we think this change makes sense, but in the context of a more robust approach to defence it is a no-brainer. In a modern military offensive cyber operations should be one of the tools available. More at The Record.
When Extortion for Insider Trading is Good News
A Krebs on Security article explains that the latest innovation in ransomware is to frame executives by planting emails that implicate them in insider trading. We think it is good news that groups are being forced to try different extortion schemes. Alex Holden, founder of cyber security firm Hold Security, told Krebs that the group in question gets access to victim organisations "but nobody wants to pay them".
When Asking Nicely Is Easier Than Hacking
Instead of having to pilfer intelligence, North Korean spies are simply asking nicely. By posing as researchers or academics, the Thallium or Kimsuky group engages with political and foreign affairs experts to gather intelligence. Reuters writes "in some cases, the attackers have commissioned papers, and analysts had provided full reports or manuscript reviews before realising" they were being duped.
SBOM Meets the Too Hard Basket, For Now
FedScoop reports that an amendment to force some contract holders to provide a software bills of materials (SBOM) has been omitted from the National Defense Authorization Act. While SBOMs would help when it comes to remediating problems such as Log4Shell it's such a long-term project that we can't help but think that current bandwidth might be better spent elsewhere anyway.
Risky Biz Talks
In addition to a podcast version of this newsletter (last edition here), the Risky Biz News feed (RSS, iTunes or Spotify) also publishes interviews.
In our last "Between Two Nerds" discussion Tom Uren and The Grugq find that for most countries use of cyber capabilities makes sense. Except for the US. They are in a different position and the development of cyberspace as a domain of strategic competition is a net loss for them.
From Risky Biz News:
New spyware vendor: Politico Europe has a profile on Altrnativ, a French company that allegedly sells spyware and surveillance tools to at least six African countries. The most interesting part of the piece is that one of the Altrnativ founders is the former CEO of Qwant, a privacy-first search engine that at one time was the default search provider of the Brave browser. That's quite the career turn.
Citrix and Fortinet patch zero-days exploited in APT and ransomware campaigns: Citrix and Fortinet, two of today's largest providers of enterprise networking equipment, have released security updates to patch two zero-day vulnerabilities that were exploited in the wild against their devices.
The Fortinet zero-day (CVE-2022-42475) is an unauthenticated RCE that impacts the FortiOS operating system that runs on the company's SSL-VPN devices. According to reports, the vulnerability was being exploited to gain access to corporate networks and then deploy ransomware. This zero-day was first spotted exploited in the wild by French security firm Olympe last week, and Fortinet deserves some credit for patching it over the weekend in just three days.
Similarly, the Citrix zero-day (CVE-2022-27518) is also an unauthenticated RCE as well. It impacts the company's ADC and Gateway devices, and the exploitation was spotted by none other than the US National Security Agency. (more on Risky Business News)
Twitter’s failed attempt to block bot farms: After Elon Musk, Twitter's controversial CEO, bragged on social media that he had a surprise for all the bot farms, Twitter managed to spectacularly shoot itself in the foot on Monday when the company blocked entire IP address blocks for around 30 mobile carriers across Asia. According to Platformer, this included the primary telecom providers in India and Russia, as well as the second-largest telecom in Indonesia. However, the block was short-lived, as Twitter had to revert its decision a few hours later after telcos and users complained all over Asia about not being able to access the service—go figure! The social network also officially dissolved its Trust and Safety Board as well on Monday, as, let's face it, it was getting in the way of Musk's attempts to influence US politics at this point.



