Risky Bulletin: There are now SIM-Farm-as-a-Service providers
In other news: Russians hack the Bundestag President; some randoms accessed Anthropic's coveted Mythos model; Plankey withdraws CISA nomination.

This newsletter is brought to you by Nebulock. You can subscribe to an audio version of this newsletter as a podcast by searching for "Risky Business" in your podcatcher or subscribing via this RSS feed. You can also add the Risky Business newsletter as a Preferred Source to your Google search results by going here.
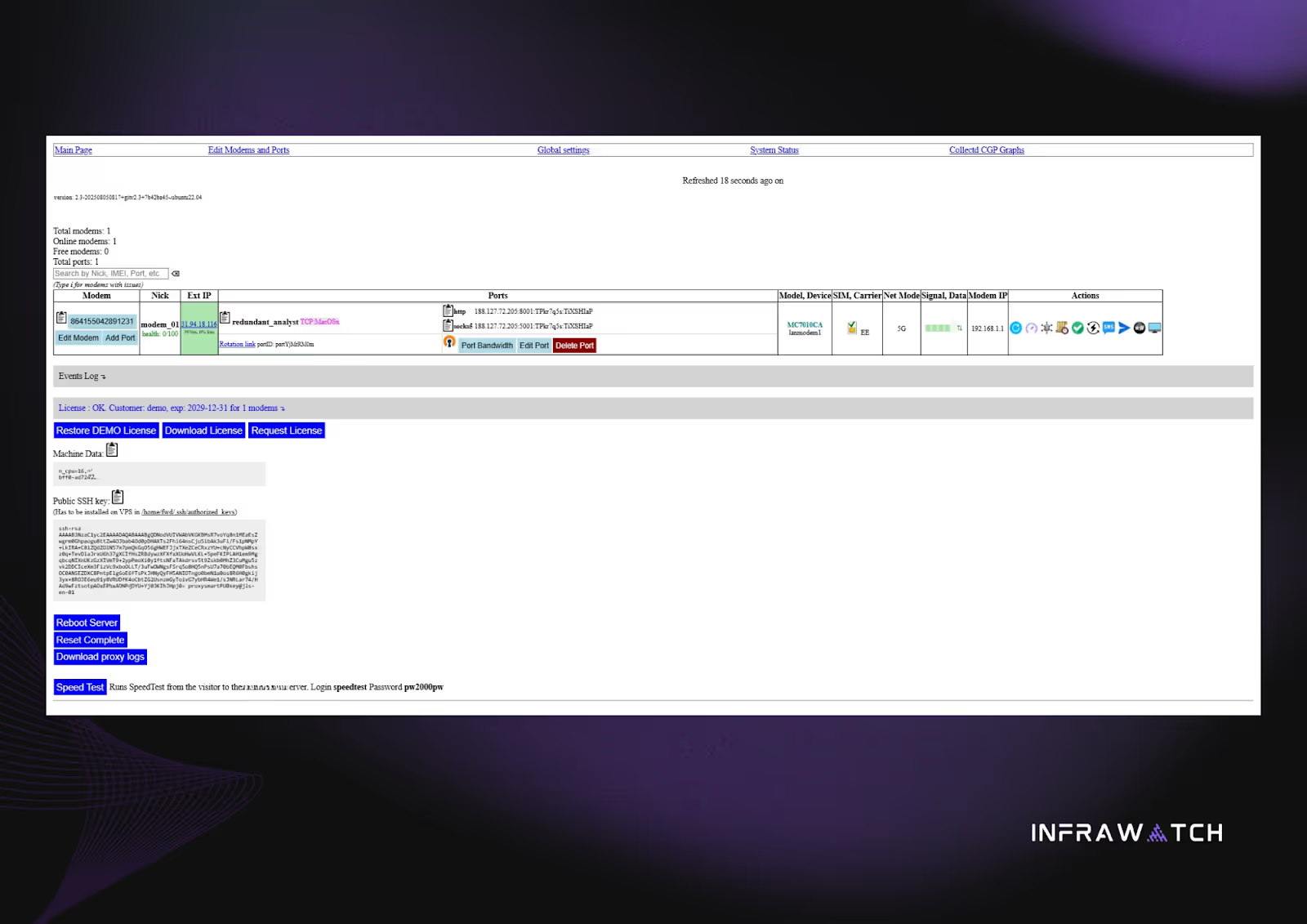
An ugly-looking web panel has been linked to 94 SIM farms located across 17 countries around the globe.
ProxySmart, as the panel is called, is among the first SIM-Farm-as-a-Service providers observed in cybercrime underground circles.
According to security firm Infrawatch, the panel was developed by a group operating out of Belarus, a group the company describes as "individuals with long-running involvement in SIM farm and mobile proxy operations."
Infrawatch says the panel leaves noticeable clues online that can be used to trace SIM farms and possibly take down and disrupt their operations.
ProxySmart appears to have built a considerable clientele that relies for it to manage an assortment of nefarious services ranging from residential proxy botnets to social media bot farms and censorship evasion services.
Some of these clients are shadowy figures in the hacking underground while others are legitimate companies with real corporate identities.
Infrawatch describes the ProxySmart service as a full "turnkey solution" that "lowers the technical barrier" for entering the mobile proxy and social media bot landscape.
As a product, ProxySmart comes with documentation, technical support, an API, an Android app, and a web panel.
The Android app is installed on smartphones that are part of the SIM farm, while the API allows admins to interact with 4G and 5G modem dongles, if SIM farm operators want to go that route.
Everything is controlled from the web panel, where operators can enroll new devices and automate operations, such as sending and receiving SMS messages, performing actions on the screen, or automating network requests.
The panel also comes with anti-fingerprinting tools allowing operators to disguise their SIMs as anything they want, from smartphones to desktop OSes.
The emergence of such a service comes at a time when residential proxy botnets are becoming widespread and a common occurrence in all sorts of cybercrime operations.
Proxy meshes, which started as an APT-only feature about half a decade ago, are now broadly used even by lower tier actors to mask the origin of their attacks and traffic to their command-and-control servers.
If the market for malicious proxies is growing, then the market for SIM farms and IoT botnets will grow as well. While law enforcement have cracked down quite heavily on some IoT botnets in recent years, with SmartProxy on the market, it may soon be time to shift some of that focus towards identifying SIM farms as well.
Risky Business Podcasts
The main Risky Business podcast is now on YouTube with video versions of our recent episodes. Below is our latest weekly show with Pat, The Grugq, and James at the helm!
Breaches, hacks, and security incidents
Randoms accessed Anthropic's Mythos on launch day: A group of AI hobbyists have gained access to Anthropic's private Mythos cybersecurity agent. The group gained access to Mythos on launch day. They used a contractor's leaked credentials and guessed Mythos operating endpoints. Anthropic said the intruders didn't run malicious prompts and seem to have only "played around." [Bloomberg // The Guardian]
The only surprise is that it wasn’t a War Thunder forum
— Jan Jęcz (@jeczjan.eurosky.social) 2026-04-21T22:03:38.660Z
Bundestag President hacked via Signal: Russian cyber spies have compromised the Signal account of Julia Klöckner, the president of the German Bundestag. The hackers spied on a sensitive group that also included the head of the German government, Chancellor Friedrich Merz. The hack didn't extend to Merz's account. Germany's cybersecurity agency said earlier this year that Russia was on a hacking spree that targeted Signal and WhatsApp accounts. [Der Spiegel]
Hackers steal Sri Lanka's money: Hackers have stolen $2.5 million from The Sri Lanka Ministry of Finance. Officials said the funds had been diverted during a foreign debt repayment. The payment was initially scheduled to repay debts to Australia. Sri Lanka has asked Australian law enforcement to help investigate the hack. [ABC]
Volo crypto-heist: Hackers have stolen $3.5 million worth of crypto-assets from the Volo DeFi platform. The hackers allegedly used an exploit against three very specific vaults. Volo said it will absorb the loss and continue operations as normal.
Rituals Cosmetics data breach: Dutch cosmetics company Rituals has fallen victim to a security breach. Unidentified hackers have stolen the personal data of the company's customers across Europe. No password or payment information was compromised. [Metro Nieuws // TechCrunch]
UK Biobank breach: The personal information of half a million people who volunteered their medical data to the UK Biobank was offered for sale on the Alibaba marketplace. [Belfast Telegraph]
New KICS supply chain attack: Hackers have compromised the KICS vulnerability scanner for the second time in a month. The intruders released malicious versions of the KICS Docker image, GitHub Action, and VS Code extensions. Cybersecurity firm Checkmarx, which manages the scanner, has confirmed the incident on Wednesday. The KICS scanner was also compromised in the same way at the end of March. The Bitwarden CLI package is the first major confirmed victim of this incident.
New Mastodon DDoS attack: A new DDoS attack has hit Mastodon's biggest instance, Mastodon Social, on Thursday, two days after a similar incident.
Mysterious downtime during missile strikes: Networking equipment installed at the Isfahan nuclear site malfunctioned ahead of US and Israeli missile strikes. Iranian officials reported issues with devices from Cisco, Fortinet, Juniper, and MikroTik. Officials are still searching for the cause of the malfunctions but noted that the country was disconnected from the global internet at the time of the attacks. [Entekhab] [h/t NG]
New telecom surveillance attacks: Security researchers have spotted two sophisticated telecom surveillance campaigns that sought to track the location of high-profile individuals. The first campaign exploited the SS7 protocol while the second used SMS messages containing hidden SIM card commands. CitizenLab says the campaigns were the work of professional surveillance vendors. The attackers allegedly abused 4G infrastructure in Israel, the UK, and the Channel Islands for their attacks. [CitizenLab]
NEW @citizenlab.ca report We uncover two sophisticated telecom surveillance campaigns. The findings expose how surveillance vendors exploit the global telecom ecosystem to conduct covert location tracking operations that can persist undetected for years. citizenlab.ca/research/unc...
— Ron Deibert (@rondeibert.bsky.social) 2026-04-23T13:37:31.506Z
General tech and privacy
Australia launches investigation into gaming companies: Australia's eSafety Commission has launched an inquiry and has asked the big four of online gaming—Roblox, Minecraft, Fortnite and Steam—what are they doing to stop grooming and radicalization on their platforms.
Meta installs spyware on employee's systems: Meta is installing spyware on the systems of US employees to capture mouse movements, clicks, and keystrokes. Meta says the data will be used to train its AI models and not for employee reviews. The company has laid off more than 8,000 workers and plans to replace them with AI models. The captured data will be used to train the models in areas where AI is deficient, such as clicking on menus and typing in input fields. [Reuters]
Meta will begin keystroke logging US employees at work -- complete with mouse movements and periodic screenshots -- to train better AI agents. This comes after Boz posted about a future in which AI will "primarily do the work" at meta. It's a new era for tech labor. www.reuters.com/sustainabili...
— Jeff Horwitz (@jeffhorwitz.bsky.social) 2026-04-21T16:41:59.323Z
GitHub CLI now collects telemetry: GitHub has notified users that the GitHub CLI now collects anonymous usage telemetry by default and that they should disable the feature if they do not want to share such information.
GitHub unreachable in Kazakhstan: Kazakhstan government officials have denied that they are blocking access to GitHub after developers reported issues accessing the platform this week. [TengriNews.kz]
NCSC announces SilentGlass: The UK cybersecurity agency has designed and will start selling its first ever commercial product. The device, named SilentGlass, will sit between monitors and PCs or laptops and help block malicious connections. The device will be manufactured by Goldilock Labs and Sony UK and will be available for HDMI and Display Port connections.

Government, politics, and policy
Russia revokes almost 2,000 telco licenses: Russia's telecommunications watchdog has revoked almost 2,000 telecom licenses. The Roskomnadzor says the offending telcos have failed to provide necessary registration and operational information. Most of the affected operators are small neighborhood providers in Moscow and other Russian cities. Russian lawmakers are also working on passing newer and tougher rules to prevent the operators from regaining their licenses. [Cableman.ru]
Plankey withdraws CISA nomination: Sean Plankey has asked the White House to withdraw his nomination for the role of CISA Director. The official was initially nominated for the job in March last year but failed to get Congress approval. Several senators, from both parties, placed holds on his nomination for a variety of reasons. He was re-nominated again this year but to no success. Plankey also retired from the Coast Guard last month where he served in cyber roles before his nomination. [Politico]
Two privacy bills arrive in Congress: Republican lawmakers have introduced two privacy bills in Congress this week. The two bills are designed to preempt a patchwork of state privacy laws across the US and unite regulation under one set of nationwide rules. The Secure Data Act introduces privacy regulations for the tech and IT sector, while the GUARD Financial Data Act introduces new rules for banks and financial institutions. Consumer privacy groups have already called the bills "a significant step back for privacy" meant to replace "stronger state and local laws." [CNBC // IAPP]
CyberCom carried out 8k operations: US Cyber Command carried out more than 8,000 cyber operations last year. New Cyber Command leader Gen. Josh Rudd expects this year's operations to surpass that number. The Trump administration has repeatedly flaunted Cyber Command's involvement in recent conflicts in Iran and Venezuela. [NextGov]
100+ countries have spyware: More than 100 countries have bought spyware and other hacking technologies. Speaking at the CYBERUK conference in Glasgow, Richard Horne, the CEO of the UK's cybersecurity agency, says the barrier for states to acquire hacking the technology. Horne warned UK companies that together with the rise of spyware and AI, they are "failing to grasp the reality of today’s world." [Politico Europe]
Sponsor section
In this Risky Business sponsor interview, Catalin Cimpanu talks with Sydney Marrone, Head of Threat Hunting at Nebulock, about hunting shadow AI agents on corporate networks.
Arrests, cybercrime, and threat intel
HexDex arrested: French authorities have arrested a 21-year-old hacker who was behind a prodigious hacking campaign last year. A 21-year-old man, going online as HexDex, was detained on Monday in the Vendée province, in Western France. He is accused of hacking French organizations, including 15 sports federations, a weapons manufacturer, an e-campus platform, and even a police training platform. [Le Parisien]
Scam compound charges: The US Department of Justice has charged two Chinese nationals for their role in a major cryptocurrency investment fraud operation. Jiang Wen Jie and Huang Xingshan allegedly ran the Shunda scam compound in Myanmar (Burma). They were also planning to open a second one in Cambodia after Burmese authorities seized the first in November of last year. Both suspects were arrested on immigration charges by Thai law enforcement earlier this year. The FBI also seized $700 million worth of cryptocurrency tied to money laundering operations, a Telegram channel used to recruit workers for the compounds, and 503 scam domains.

US sanctions Cambodian senator for scam compounds: The US Treasury has sanctioned a Cambodian senator behind a network of cyber scam compounds. Kok An and his family allegedly ran scam compounds out of retrofitted casinos and office parks in Cambodia and Thailand's border regions. The scam centers were raided by authorities in both countries at the end of last year. Kok has been on the run since the raids. Besides him, the US also imposed sanctions on 28 individuals and companies linked to the official. [The Record]
Namastex npm attack: Hackers have deployed malware in the npm packages of AI company Namastex. According to Socket Security, the malware looks identical to the one managed by the TeamPCP group and used in recent supply chain attacks. In the meantime, JFrog and Step Security say they spotted TeamPCP spreading malware again on PyPI.
"Guarantee" Telegram marketplaces: The Recorded Future threat intel team has an interesting report out on what they call "guarantee Telegram marketplaces," a term to describe a rising trend of Telegram channels where threat actors sell various fraud and scam-related services to the operators of regular scam ops or the more industrialized cyber scam compounds. The new king of this market seems to be a platform named Dabai Guarantee.
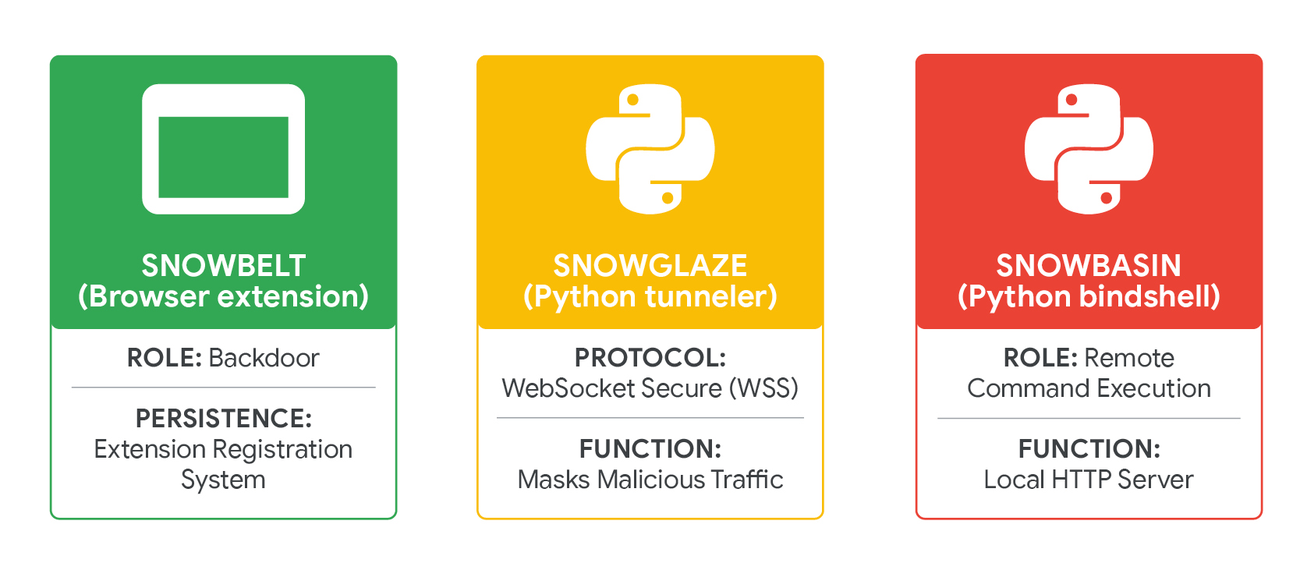
UNC6692 profile: Google's Mandiant division has identified a new threat actor—which is tracking as UNC6692—that is engaged in sophisticated social engineering campaigns impersonating IT helpdesk employees in order to convince victims to hop on a Teams chat, access phishing pages, or install malware on their systems. The group's main tools are the SNOW malware family, which includes a malicious browser extension, a Python tunneler, and a reverse shell.
Nova interview: Threat intelligence analyst Marco A. De Felice has published an interview with the operators of the Nova ransomware group.
Hidden prompt injections in the wild: Forcepoint has spotted hidden AI prompts inside the source code of at least ten websites, just waiting to be scanned by clueless AI agents.
Malicious Chrome extension: DomainTools has spotted a malicious Chrome extension posing as the official Google Authenticator app that was made available on the official Web Store.
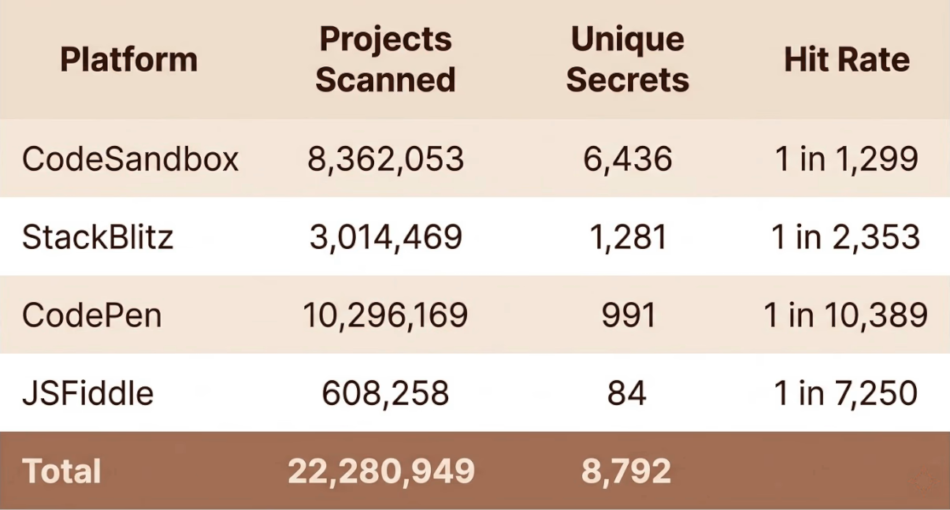
CDE exposure: Almost 8,800 tokens and secrets have been leaked online through web-based development environments, also known as CDEs (cloud development environments). The tokens were found across 22 million public code snippets and projects hosted on platforms such as CodePen, CodeSandbox, JSFiddle, and StackBlitz. The most impactful finding was a token belonging to a GitHub employee that allowed write access to the GitHub platform itself. [Truffle Security]
Malware technical reports
ZionSiphon is AI-generated: ICS security firm Dragos has concluded that the newly discovered ZionSiphon malware, designed to attack Israel's water management sector, was generated using AI coding tools and is non-functional.
Mirai botnet goes after old D-Links: A new Mirai DDoS botnet is going after old EoL D-Link routers using an exploit for a bug tracked as CVE-2025-29635. Attacks against older TP-Link and ZTE vulnerabilities were also observed.
ValleyRAT: Breakglass has spotted new campaigns spreading ValleyRAT, a remote access trojan developed and used by China-based threat group SilverFox.
OLUOMO phishing kit: Censys's Andrew Northern looks at OLUOMO, a new AitM-capable phishing kit the company has spotted in the wild.
Bedep DGA: Gen Digital has published an interesting historical report on the decade-old Bedep ad fraud botnet that was active in 2014 and 2015. The report looks at the botnet's DGA, which used the euro foreign exchange reference rates published by the European Central Bank as part of its randomizing algorithm.
Devil NFC MaaS: A cybercrime platform named Devil NFC is providing ready-made access to Android banking trojans that can relay and steal NFC transaction data and PINs in real time to help criminal groups hijack transactions or empty bank accounts at ATMs.
#BREAKING #ESETresearch uncovered an active NGate Android malware campaign targeting Spanish speaking users, combining fake app distribution, NFC relay abuse, PIN harvesting, and a shared Devil NFC MaaS backend. The operation is tied to the Devil NFC infrastructure used in Spain since Jan 2026 1/10
— ESET Research (@esetresearch.bsky.social) 2026-04-23T12:21:14.857Z
Sponsor section
Agentic AI platform Nebulock pitches its product in one of our recent Snakeoilers episodes.
APTs, cyber-espionage, and info-ops
Sandworm (APT-C-13): In a recent report, Qihoo 360 looks at how Russian APT group Sandworm is using SSH and Tor nested tunnels to double-encrypt traffic between victims and their C2 servers.
Geo Likho: A new APT group named Geo Likho has targeted the Russian aviation industry and shipping companies.
Kimsuky: Breakglass has spotted over 60 new domains linked to North Korean APT group Kimsuky.
HexagonalRodent: A North Korean APT group is making "significant use" of generative AI technologies in a campaign targeting developers in the Web3 ecosystem. The group has set up several companies to target developers with fake job offers. Developers would get infected with malware during the application process when they have to go through a skills assessment test. The group has stolen as much as $12 million worth of cryptocurrency from private wallets in just three months. Security firm Expel tracks the group under the name of HexagonalRodent.
I spent nearly 4 months investigating the inner workings of a North Korean state-sponsored hacking group. Here's what I learned: 🧵 - The group used generative AI tools to aid in almost every part of their operation. - They exfiltrated 26,584 cryptocurrency wallets from 2,726 victim systems. 1/3
— Marcus Hutchins (@malwaretech.com) 2026-04-22T19:43:07.655Z
Harvester's GoGra Linux backdoor: The Harvester APT group has developed a new, highly-evasive, Linux version of its older GoGra backdoor.
UAT-4356 never left Cisco ASA firewalls: A Chinese cyber-espionage operation found a way to remain on Cisco ASA firewalls even after two waves of patches released in 2024 and 2025. Cisco says the UAT-4356 deployed a new backdoor named FIRESTARTER that exploited a "previously unknown persistence mechanism" to survive the patching process. The new backdoor was found by CISA and is linked to a Cisco ASA firewall hacking campaign initially tracked as ArcaneDoor. Cisco has told customers this week to reimage and upgrade devices to a new firmware release.
GopherWhisper: ESET says a new Chinese APT group it tracks as GopherWhisper is targeting Mongolian government organizations with an assortment of new malware strains.
Chinese proxy botnets: Sixteen cybersecurity agencies have published a joint advisory on China's use of proxy botnets to disguise its espionage activity. The botnets are made up of regular day devices, such as home routers, security cameras, video recorders, and other types of IoT devices. The advisory specifically warns about the concept of "IOC extinction," where an indicator of compromise, such as an IP address, is only used a few times before it's discarded, making tracking and prevention very difficult.

Vulnerabilities, security research, and bug bounty
Nextcloud stops bug bounty program due to AI flood: German office suite maker Nextcloud has shut down its bug bounty program following an increase in low-effort AI-generated reports. The program was taken offline on Wednesday in a sudden decision. Co-founder Jos Poortvliet said his staff was spending twenty to thirty times more time on reports than before, and most were complete nonsense. [Tweakers]
Qihoo has a Mythos-scale rival: Chinese tech giant Qihoo 360 has developed its own cybersecurity AI model that can rival Anthropic's Mython agent. Qihoo's new agent has allegedly found more than 1,000 vulnerabilities, including in products like Microsoft Office and OpenClaw. The company says the new agent is now a core component of its vulnerability discovery operations. [Bloomberg]
Claude Opus generates bad code: According to several security experts, Anthropic's Claude Opus assistant is producing low quality and insecure source code, which is something that everyone has been warning about for years now but the AI tech bros still went ahead and created the faulty product anyway. Insert "you had one job meme." [Forbes]
LMDeploy exploitation: Threat actors began exploiting an AI server platform 12 hours after a patch was made available. Attacks are targeting LMDeploy, a popular toolkit for compressing and serving LLMs. Tracked as CVE-2026-33626, the exploited vulnerability is a server-side request forgery (SSRF) that allows attackers to access server endpoints without authentication. [Sysdig]
Apple patches notification retention bug: Apple has released a security update to patch a bug that allowed notifications from a deleted app to remain in a device's log. The iOS patch addresses a specific bug used by the FBI this year to extract old Signal messages from a suspect's device even after they deleted the app. Copies of the old private messages were stored in an iPhone database of past notifications that wasn't cleared properly.
Oracle CPU: The quarterly Oracle security updates are out, with patches for 481 vulnerabilities. Tenable has a breakdown of the fixes.
ASP.NET out-of-band security update: Microsoft has released an out-of-band security update to patch an ASP.NET elevation of privilege bug tracked as CVE-2026-40372.
Spinnaker RCEs: ZeroPath has found two RCEs in Spinnaker, a multi-cloud continuous delivery platform widely used in the enterprise sector.
Pack2TheRoot vulnerability: Security updates have been released for PackageKit, a cross-distro package manager for Linux distributions. The patch fixes a privilege escalation bug that can allow unprivileged users to obtain root access on the underlying OS. The vulnerability, codenamed Pack2TheRoot, has been tested and confirmed on distros such as Ubuntu, Debian, Fedora, and RockyLinux.
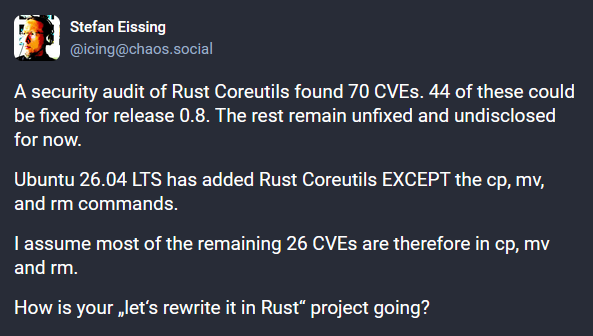
Rust-coreutils security audit: Canonical is releasing more than 40 security patches for the Ubuntu operating system. The patches are all in the Rust-coreutils library. The library is a rewrite in Rust of the GNU Core Utilities, the Linux component that supports basic file, shell and text manipulation utilities. The security flaws were found in a security audit last year and more patches are expected later this year. [Phoronix]
Infosec industry
Threat/trend reports: Cisco Talos, Curator, Datadog, Internet Watch Foundation, NZ NCSC, Positive Technologies, and Red Canary have recently published reports and summaries covering various threats and infosec industry trends.
Cyber-insurers looking at capping AI-related payouts: At least two cyber-insurance providers are considering capping payouts for AI-related security incidents. The caps would apply to attacks known as LLMjacking. These are incidents similar to cryptocurrency mining, but where hackers take over AI servers and cause increased costs for the hacked company. According to the Financial Times, payments caps are being discussed at QBE and Beazley, as low as 5% of the total losses.
CYBERUK 2026: Talks and live streams from the UK NCSC's CYBERUK 2026 security conference, which took place this week, are available on YouTube.
Risky Business podcasts
In this edition of Seriously Risky Business, Tom Uren and James Wilson talk about the French criminal investigation into bias and illegal content on X. Elon Musk and former X CEO Linda Yaccarino didn't appear for voluntary interviews scheduled this week, but refusing meetings won't make X's problems go away.
In this edition of Between Two Nerds, Tom Uren and The Grugq take a deep dive into how a single hacker used OpenAI and Anthropic's tools to help hack nine Mexican government organisations in quick time.




