Risky Bulletin: The Intellexa CEO is pissed!!!
In other news: Google launches threat disruption unit; German police visit companies in the dead of night about software bugs; FTC bans all foreign-made routers.

This newsletter is brought to you by Authentik. You can subscribe to an audio version of this newsletter as a podcast by searching for "Risky Business" in your podcatcher or subscribing via this RSS feed.
The CEO of a major spyware vendor says he is being scapegoated by the Greek government and is willing to testify and spill the beans on their illegal surveillance operations.
Intellexa CEO Tal Dillian is pissed out of his mind after a Greek court sentenced him, his wife, and two executives to more than 126 years in prison last month on generic charges of "violating the confidentiality of telephone communications."
The sentence is related to a major Greek political scandal known in Greece as Predatorgate, which this newsletter first covered back in December 2024.
The scandal first came to light in 2022 after a member of the Greek opposition said the EU cybersecurity staff found spyware on his work device. One report at a time, Greek media slowly uncovered a sprawling surveillance operation that deployed spyware on the phones of major political figures, judges, prosecutors, journalists, and business people.
Reporting in Greek media exposed the hacks as an operation carried out by the country's intelligence service, the EYP, at the orders of the ruling government.
A Parliamentary inquiry into the surveillance found that the government purchased the Predator spyware from spyware maker Intellexa, but the commission investigating the abuses had its members replaced and powers stripped.
The government coverup continued when the Supreme Court stripped the case from initial prosecutors, ignored witness testimonies, and then went as far as clearing the ruling government and EYP officials of any wrongdoing.
Instead, a criminal investigation was allowed to continue into Intellexa itself that focused on the fact that Intellexa lacked the proper authorization to sell its software and that its tool broke telco confidentiality, which only authorities are allowed.
The case and the ruling were odd to begin with. Even the biggest Intellexa haters out there were in agreement that the trial and the sentence made zero sense, as it was the government that purchased and used the software and not Dillian and his staff acting rogue.
In an emailed statement to Greek news outlet Inside Story, Dillian had confirmed what almost everyone had known already from news reports, and that his company sold its Predator spyware to government-only customers, and in this case to the Greek government and the EYP.
Even if the text is in Greek and has been machine translated through different engines, the accusations were the same. Dillian says he is being set up to take the fall.
He went as far as to call the government and EYP of engaging in a "conspiratorial criminal act" to send him and his staff to prison in order to cover their abuses of power. He says Intellexa only provides the surveillance system and the customers carry out the surveillance, and they have no say in selecting the targets.
Dillian says he plans to appeal the sentence and he'll be willing to testify again in the courts and even in front of UN commissions.
"I remained silent during the trial, but I will not be a scapegoat. I will present my case before national, regional, and international institutions, including requesting the intervention of the UN Special Rapporteur on judicial independence."
If #Intellexa boss Tal Dilian is willing to testify about the abuse of, and illicit exports of spyware, many capitals in Europe and the Berlaymont have reasons to be very, VERY worried.
— Sophie in't Veld (@sophieintveld.bsky.social) 2026-03-24T18:58:15.231Z
Is this the first ever case of a spyware maker publicly criticizing their own customers? I’m struggling to think of one.
— Lorenzo Franceschi-Bicchierai (@lorenzofb.bsky.social) 2026-03-24T19:00:37.237Z
New Tal Dilian statement on #PredatorGate points even more clearly to the 🇬🇷authorities: “I believe it is a crime for private individuals to interfere communications. But it is even more serious crime to organize a conspiracy crime to send innocent people to jail to cover up political authorities.“
— Vas Panagiotopoulos (@vaspanagiotopoulos.com) 2026-03-24T18:45:53.138Z
Risky Business Podcasts
We recently also launched a new podcast series called Risky Business Features. In this episode, James Wilson and Brad Arkin discuss the attack that devastated medtech company Stryker. It turns out the attackers used Microsoft's Intune to wipe the company’s devices, but what else could they have weaponised?
Breaches, hacks, and security incidents
Breach at the Dutch Ministry of Finance: Hackers have breached the internal servers of the Dutch Ministry of Finance. The breach took place last week. The incident impacted employee work but public web portals were unaffected.
Hackers breach South Korea's top lender: Hackers have stolen sensitive customer data from South Korea's largest private lender. NRL Capital Lend discovered the incident last week. Stolen information includes customer names, addresses, ID details, as well as loan details and credit scores. The company believes the hack originated from an employee account after they installed malware on their personal PC. [ChosunBiz]
Crunchyroll breach: A hacker has breached anime streaming platform Crunchyroll and stolen customer data from its ticketing platform. The breach took place last week. The data of around 6.8 million users is believed to have been stolen. Crunchyroll has more than 17 million registered users. [The Record]
CrunchyRoll has been compromised. An unknown Threat Actor bribed a third-party helpdesk contractor who intentionally detonated malware in CrunchyRoll's computer network. Over 100GB of customer data was stolen. Information and photos via @IntCyberDigest
— vx-underground (automated mirror) (@vxundergroundre.bsky.social) 2026-03-23T00:54:35.886Z
Liberty breach in SA: South African life insurance provider Liberty has disclosed a security breach.
Mazda data breach: Mazda says hackers stole information on employees and business partners from a warehouse management system in a breach last December. [Mazda, PDF]
HackerOne breach: HackerOne employees have been impacted by a recent breach at employee benefits and retirement funds management platform Navia.
InfiniteCampus breach: A threat actor has compromised the Salesforce account of student management platform InfiniteCampus. The ShinyHunters group took credit for the breach and threatened to leak the company's data this week.
Resolv crypto-heist: Hackers have stolen $25 million worth of crypto assets from the Resolv crypto project. The attackers exploited the platform, minted extra tokens, and cashed out. The attack allegedly happened at full speed, with the hackers expecting to be discovered. [CoinTelegraph]
Woundtech incident: A hacker apparently spent a lot of effort redacting user data before they leaked it, even giving the hacked company the chance to redact it themselves. Mobile wound treatment provider Woundtech did not take them up on the offer. [DataBreaches.net]
University of Warsaw ransomware attack: ESET said it stopped an attack with the Interlock ransomware against the University of Warsaw before attackers could encrypt systems.
Checkmarx vulnerability scanner hacked: Hackers have compromised KICS, an open-source vulnerability scanner managed by security firm Checkmarx. Hackers added malware to steal credentials to the KICS GitHub action and two of its VS Code extensions. The incident was the work of TeamPCP, a hacking group known for hacking cloud infrastructure. The group also hacked Trivy last week, another open-source vulnerability scanner managed by Aqua Security. [CStromblad // Step Security // Wiz]
Trivy supply chain attack expands: In the meantime, TeamPCP also expanded its Trivy hack to Acqua Security's entire GitHub repo, compromising its private GitHub projects and Docker images. [Socket Security // Open Source Malware]
General tech and privacy
Reddit prepares new account verification methods: Reddit is considering using FaceID, TouchID, and other passkey technology to verify user accounts. CEO Steve Huffman says the goal is to ensure that a real human is behind an account. Huffman's comments come as the platform is dealing with a flood of AI-generated content. A study last year found that almost 15% of Reddit posts were AI-generated. [PCMag]
The rise of GEO: China's search engines are getting flooded by what experts are calling GEO, or generative engine optimization—the art of poisoning LLMs and the information space so search engines that use AI widgets return fake and manipulated information.
CSAM at record levels: AI-generated CSAM imagery is at an all-time level, according to a new Internet Watch Foundation report.
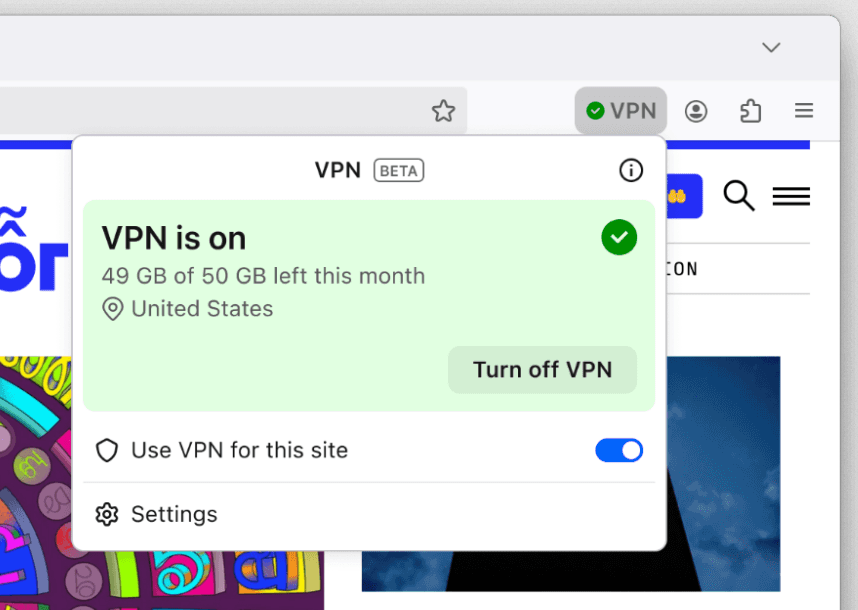
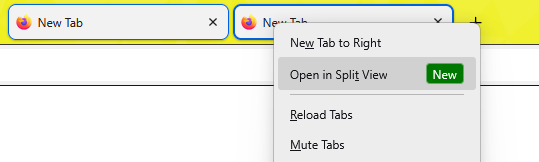
Firefox 149: Mozilla has released Firefox 149. New features and security fixes are included. The biggest feature in this release is the addition of a built-in VPN service and support for Split View tabs.
Government, politics, and policy
China-EU cybersecurity research: Chinese and EU universities have partnered on almost 50 cybersecurity research projects. Some of the partnerships involved Chinese universities known to be part of an elite group named the Seven Sons of National Defense. The US warned that China is using joint research projects to infiltrate and recruit insiders to steal or share sensitive research. Several US professors have been charged and sentenced for lying about their ties to Chinese academia. [Bloomberg]
Russia to block international calls to seniors: Russian phone operators will have to block international calls to customers over the age of 60. The new rules are part of an update to the country's anti-fraud laws. The same rules will also require mobile operators to block the delivery of one-time codes via SMS to children devices. This measure is designed to prevent children from signing up to social media accounts without their parent's approval. [Forbes Russia]
MAX is now mandatory for officials: The Russian government has mandated that all officials use the MAX national messenger app for official communications. [Meduza]
State Department launches new cyber office: The US State Department has established a new cyber office after shutting down the previous one in April last year. The new Bureau of Emerging Threats will investigate the use of cyberattacks, AI, and outer space technology against the United States. The new Bureau will include five major divisions focused on cybersecurity, critical infrastructure, space security, threat assessment, and disruptive technologies. [ABC News]
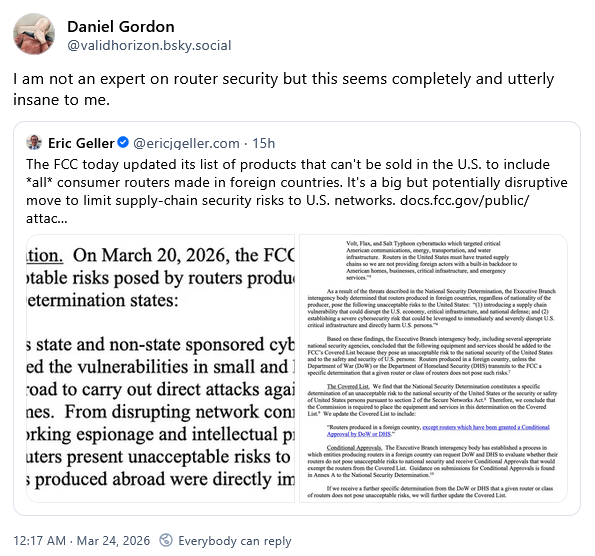
US bans all foreign-made routers: The US Federal Communications Commission has banned the import and sale of all foreign-made internet routers. The ban applies to all countries, and not just a few select Chinese vendors. The agency cited national security concerns over its decision. It claims that foreign made routers introduce a supply chain vulnerability that disrupts the US economy, its critical infrastructure, and national defense.
Sponsor section
In this Risky Business sponsor interview, Casey Ellis chats to Fletcher Heisler, founder and CEO of open source identity provider, Authentik. They chat about Extended Identity Access Management (XIAM), the company’s new acronym that has been seven years in the making.
Arrests, cybercrime, and threat intel
University professor hacked students: An assistant professor at University College Dublin has been accused of hacking more than 140 of his students. He is accused of installing malware in the university campus and offices that collected passwords. The suspect allegedly accessed accounts, stole sensitive data, and harassed victims. He was arraigned in court last week and set to appear again in July. [TheJournal]
Yanluowang ransomware affiliate sentenced to 81 months: A Russian national has been sentenced to 81 months in prison for hacking US companies and selling access to ransomware groups. Aleksei Volkov worked as an initial access broker for the Yanluowang ransomware. He used the name of chubaka-kor on hacking forums. Volkov was arrested in Rome in 2023, a year after Yanluowang disbanded.
Operation Atlantic reaches out to victims: Law enforcement agencies from Canada, the UK, and the US are reaching out to potential victims of crypto-phishing operations. This includes individuals who were targeted in investment scams and crypto fraud known as approval phishing.
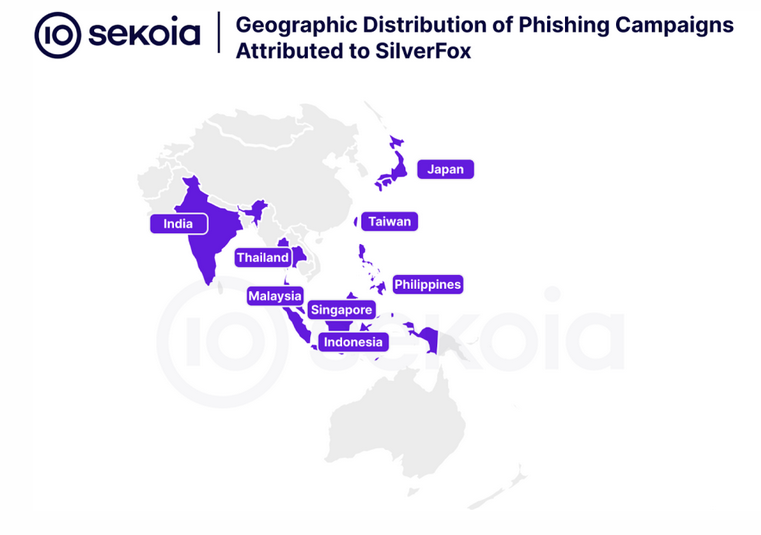
Silver Fox profile: French security firm Sekoia has published a profile on Silver Fox, the financially motivated group that initially targeted Chinese-speaking audiences but has now expanded operations all across Southeast Asia.
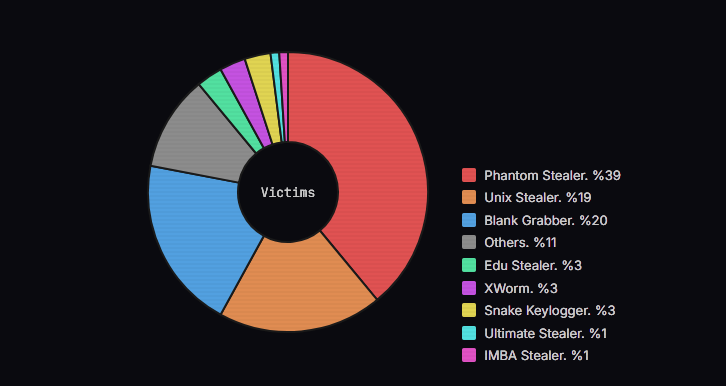
Infostealer market: CTI Monster looks at the most active infostealer operations over the past five months, which includes the likes of Phantom Stealer, Unix Stealer, and Blank Grabber.
More malware on GitHub: In the wake of our last newsletter edition, Netskope found more malware uploaded and disguised as legit GitHub repos.
FAUX#ELEVATE campaign: A threat actor is targeting the French enterprise sector with a phishing campaign designed to deploy crypto-miners and infostealers on compromised networks.
AI agent stealers: Expel found four Chrome extensions that steal user prompts entered in AI agent conversations.
K8s scanning cluster: GreyNoise has published a report on a cluster of malicious servers operating out of Paris that has mass-scanned the internet for vulnerable Kubernetes infrastructure.
"What we’re looking at with AS211590 (Bucklog SARL / FBW Networks SAS) is ,something else entirely – a purpose-built, Kubernetes-orchestrated scanning cluster running from a single /24 in Paris that generated 13 million sessions over 90 days and barely registered the load."
A sea of outdated IIS servers: More than half a million end-of-life IIS servers are connected to the internet. According to the Shadowserver Foundation, almost half of them run versions that are not supported by Microsoft through the Extended Security Updates program and do not receive any kind of support. Most of the servers are running in the US and China.
Over 511 000 End-of-Life Microsoft IIS instances seen in our daily scans, out of those over 227 000 instances that are beyond the official Microsoft Extended Security Updates (ESU) period. We now tag those 'eol-iis' and 'eos-iis' respectively in our Vulnerable HTTP reports.
— The Shadowserver Foundation (@shadowserver.bsky.social) 2026-03-23T09:51:09.040Z
Malware technical reports
EvilTokens PhaaS: A new phishing platform named EvilTokens is behind a campaign that is abusing the Railway.com platform for an active device code phishing operation targeting Microsoft 365 accounts.
Green Blood 2.0: South Korean security firm AhnLab has published a report on the new version of the Green Blood ransomware, a group that launched operations earlier this year.
Pay2Key returns: Pay2Key, a suspected Iranian ransomware and data-wiping group, has returned with new operations. I wonder what happened recently that made them come back. Can anyone tell me?
Novel WebRTC skimmer: Sansec has discovered a novel web skimmer that steals credit card form data from infected e-stores using a hidden WebRTC channel.
Brbbot: A security researcher going by 7amthereaper has published an analysis of Brbbot, a new backdoor spotted in the wild.
CanisterWorm: Step Security looks at CanisterWorm, the self-propagating npm worm that the TeamPCP hacking group has been deploying across the DevOps ecosystem via the compromises of two security scanners—Trivy and KICS. The worm has a secret behavior that wipes systems that have the Farsi language as default and are on Iran's timezone.
Jackskid botnet: Nokia's security team looks at Jackskid, one of the four IoT DDoS botnets taken down by the FBI last week. Per the report, the botnet runs on modified Mirai code and was built to target Android TV set-top boxes. CNCERT tracks this as RCtea.
DarkSword leaks online: The DarkSword iOS hacking framework has been leaked on GitHub last week. The leak is allegedly a recent version and contains read-to-use exploits. The exploits can be placed on websites and inside apps to hack iPhones and iPads running on older versions of iOS. Apple has told users to update to the latest iOS 18 and iOS 26 versions to avoid getting hacked. Mass-exploitation of iOS devices is expected because of the leak. [TechCrunch]
You really gotta watch this space. I might be wrong, but feels like we're watching a wave starting to crest. Could see mass takeover of old/unpatched iPhones in a way we've never seen before.
— Kevin Collier (@kevincollier.bsky.social) 2026-03-23T21:42:16.767Z
Sponsor section
Authentik is an open-source identity provider that is also offered with paid enterprise features. In this demo, CEO Fletcher Heisler and CTO Jens Langhammer walk Risky Business host Patrick Gray through an overview and a demo of the technology.
APTs, cyber-espionage, and info-ops
Nasir Security: Resecurity says an Iranian threat actor going by Nasir Security is hacking energy organizations across the Middle East, more specifically supply chain vendors involved in engineering, safety, and construction of energy facilities. The group also runs a leak site with overinflated, fake, or misleading claims.
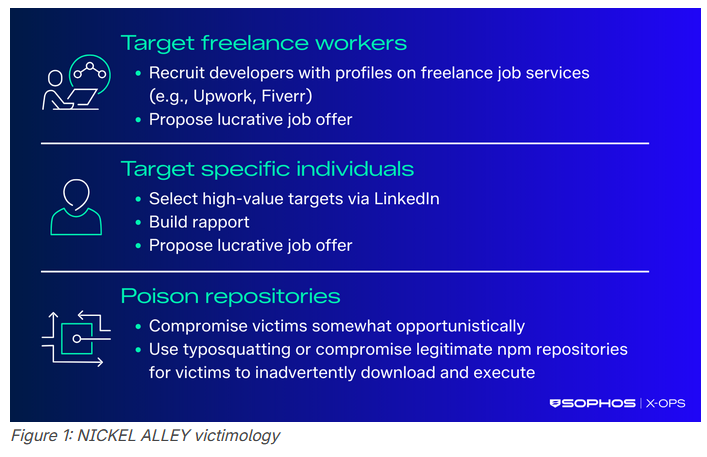
NICKEL ALLEY: It's Sophos' turn to look at Contagious Interview campaigns, with the company investigating a group it tracks as NICKEL ALLEY.
APT-C-13 (Sandworm): Qihoo's security team looks at a series of attacks attributed to Russia's Sandworm espionage group where they leveraged registry keys to enable secret RDP backdoor connections to compromised environments.
Russian info-ops in Hungarian elections: Russian disinformation group Matryoshka is running a massive TikTok influence operation targeting Hungary's upcoming Parliamentary election. The campaign is nigh identical in tactics with Russian groups used in campaigns targeting the election cycles of Romania, Moldova, Czechia, Poland, Germany, and France over the past two years.Some smaller campaigns are also active on Twitter and Telegram, and some are incredibly dumb.
"Other fake news reports on X and Telegram by Matryoshka claimed that Zelensky sent an “HIV squad” of Ukrainian women to infect Hungarian men, that Ukrainians have threatened the friends of Orbán’s children and grandchildren with physical harm, and that Ukrainians are posting videos of themselves burning the Hungarian flag on TikTok."
IRGC info-op hits BlueSky: Academics at Clemson have published a report on an Iranian info-op active on Twitter, BlueSky, and Instagram. While Russian groups have been active on BlueSky before, this is the first time I remember seeing the IRGC active there.
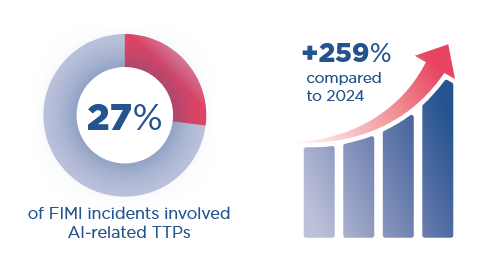
AI adoption grows among info-op groups: A quarter of online influence operations last year involved the use of AI tools, according to a report from the EU diplomatic service. The use of AI-generated text, and manipulated audio and video is now a routine practice after threat actors experimented with the technology in previous years. The EU cited lowered costs, the broad availability and scalability of AI tools. Despite the expansion, EU officials also noted that much of the AI-generated material was low-quality and easy to spot.
Vulnerabilities, security research, and bug bounty
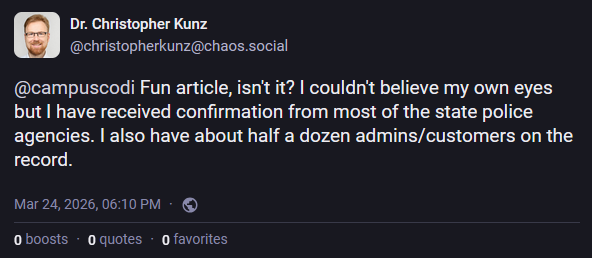
German police visits companies in the dead of night about vulnerabilities: German police visited companies in person over the weekend to warn them about software vulnerabilities in their networks. Some of the visits took place in the dead of night, at 3AM. The visits targeted companies known to run Windchill and FlexPLM software. Unpatched vulnerabilities were disclosed in both products last week. [Heise Online]
KACE bug exploited in the wild: Threat actors are hacking Quest KACE endpoint management systems to breach corporate networks. The attacks began earlier this month and are exploiting a bug patched last May. Tracked as CVE-2025-32975, the vulnerability is an authentication bypass in the server's SSO component. Attacks involved lateral movement, credentials harvesting, and access to backup systems.
Citrix security update: Citrix has released a security update this week to patch two vulnerabilities, including a critical memory bug.
GCP RCE: Google has fixed a remote code execution in its cloud platform that could have allowed attackers to abuse the Looker service to run malicious commands on its underlying servers when malicious customers deleted Git repositories. [Flatt Security]
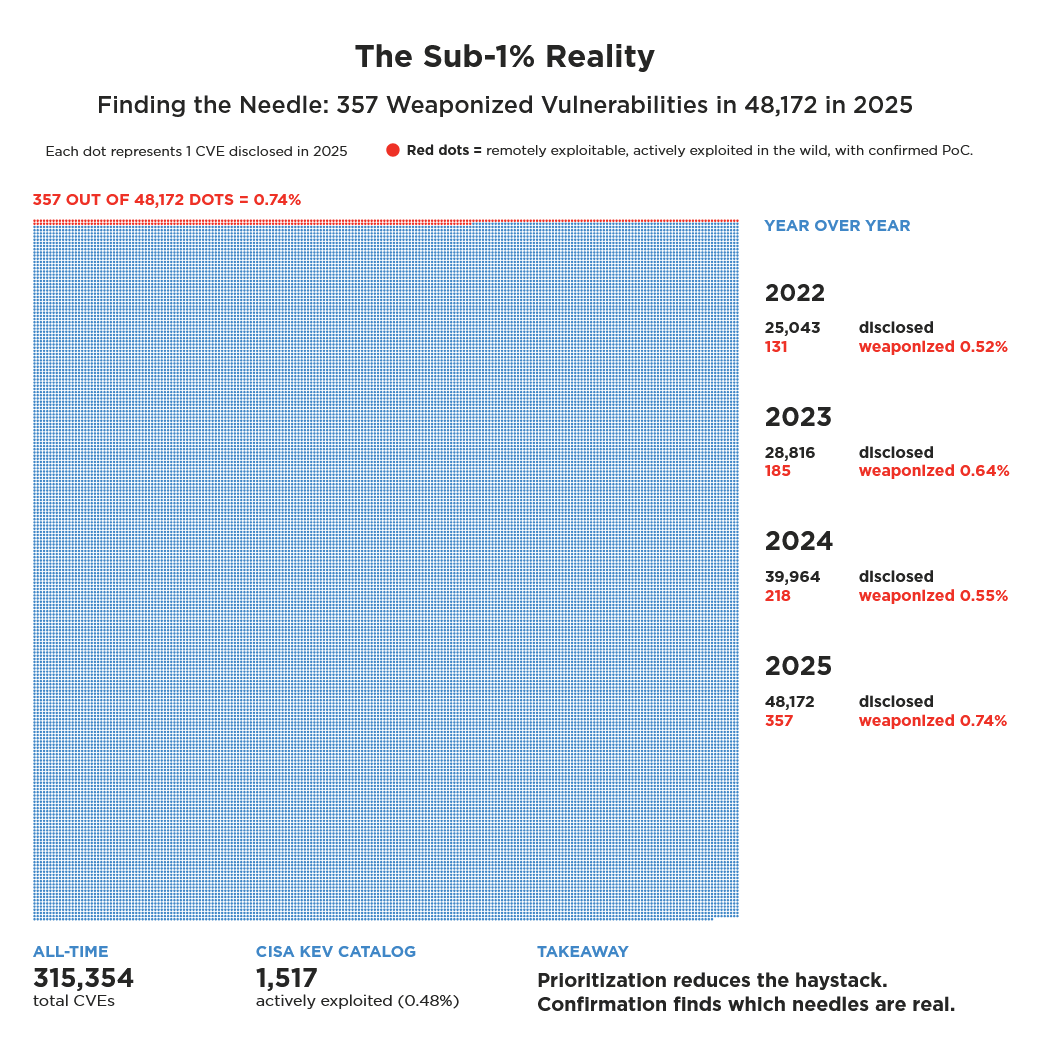
Less than 1% of vulnerabilities were exploited last year: According to a new Qualys report, only 0.74% (357) of the 48,000+ vulnerabilities disclosed last year were exploited in the wild.
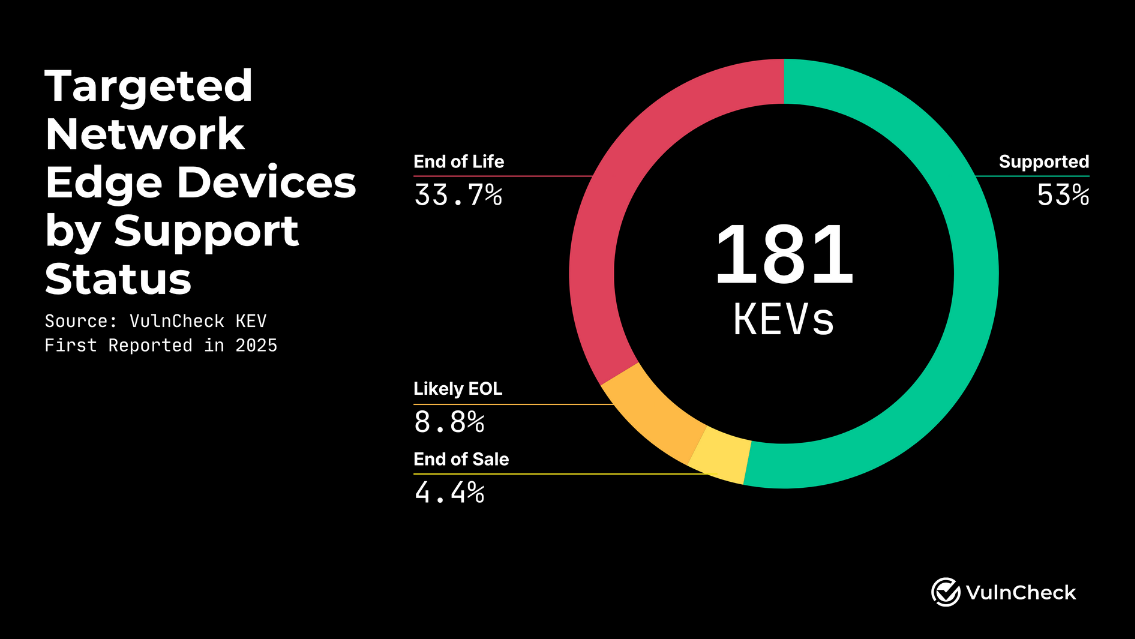
Edge devices were most targeted last year: Threat actors exploited 181 different vulnerabilities in edge devices last year, with over 42% of exploits targeting EOL device versions, per a new VulnCheck report.
Infosec industry
Threat/trend reports: ArmorCode, Cisco Talos, the EU EEAS, Google Mandiant, Qualys [PDF], Sophos, Veracode, and VulnCheck have recently published reports and summaries covering various threats and infosec industry trends.
Google launches threat disruption unit: Google has launched a new cyber unit that will be tasked with disrupting threat actor operations. The new team was announced at this year's RSA security conference. Google says the team will use legal actions and court orders to take down threat actor infrastructure. The takedown operations won't be limited to Google's own infrastructure and the team plans to work with industry partners. [NextGov]
New tool—OpenClaw Security Platform: Security firm Zenity has released OpenClaw Security Platform, a security layer for OpenClaw AI agent installations.
ROCon APAC 2025 videos: Talks from the Risk Operations Conference APAC 2025 security conference, which took place last October, are now available on YouTube.
Risky Business podcasts
In this edition of Between Two Nerds, Tom Uren and The Grugq discuss how Google just keeps on finding iOS exploit kits. Is iPhone security busted? And why are Russian state hackers after crypto?




