Risky Bulletin: Shai-Hulud goes open-source
In other news: Dream Market admin charged after major OPSEC failure; France investigates Israeli disinfo firm; Composer rushes to fix GitHub token leak.

This newsletter is brought to you by Knocknoc. You can subscribe to an audio version of this newsletter as a podcast by searching for "Risky Business" in your podcatcher or subscribing via this RSS feed. You can also add the Risky Business newsletter as a Preferred Source to your Google search results by going here.
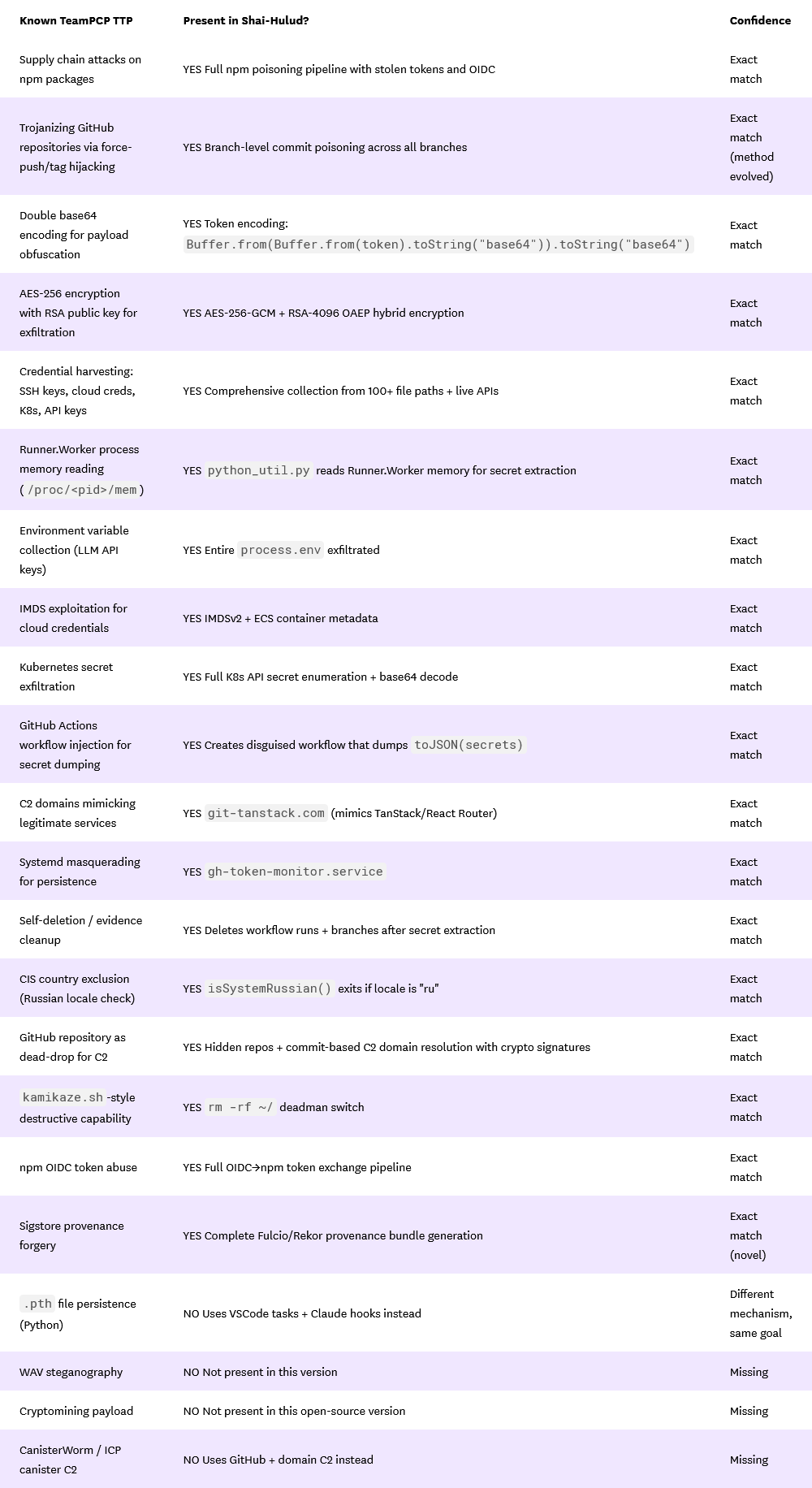
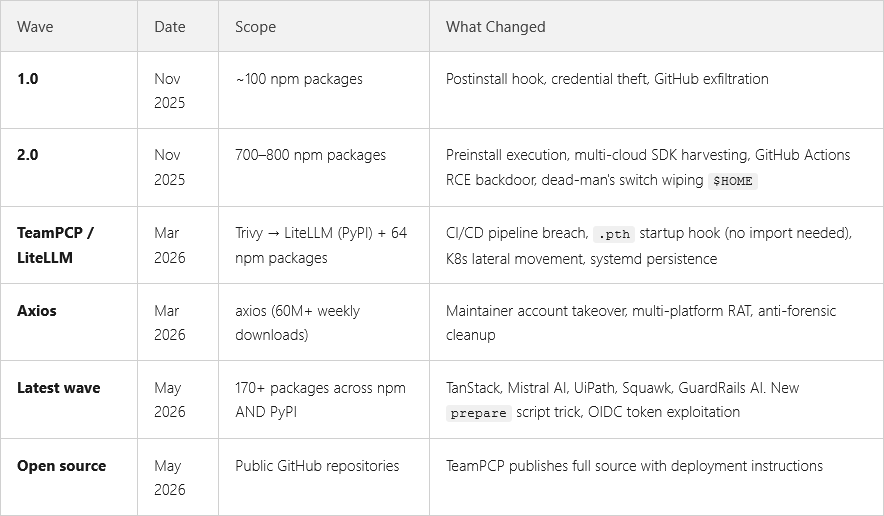
Individuals claiming to be associated with the TeamPCP hacking group have released the source code of the Shai-Hulud worm that has devastated open-source libraries across the npm and PyPI ecosystems.
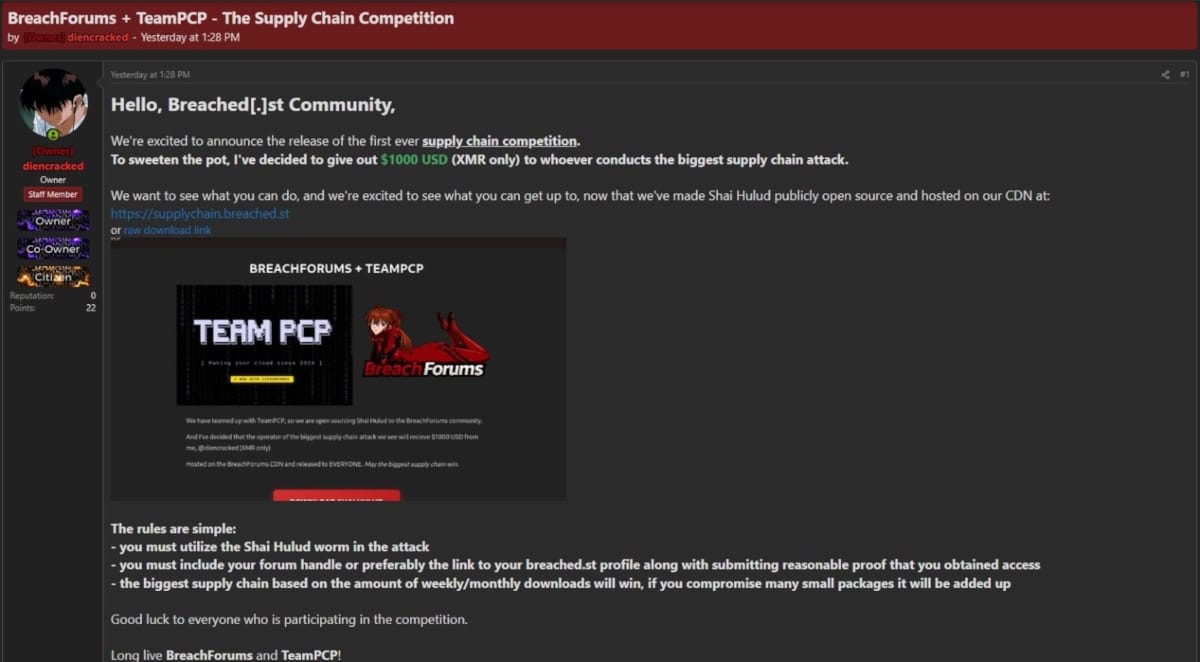
The code was released this week on the Breached[.]st hacking forum.
It was released two days after it was used in a supply chain attack that compromised the TanStack React framework and then spread to almost 400 packages, including libraries at AI company Mistral and business automation giant UiPath.
Although threat actors have a tendency to lie about what they release, the worm's authenticity has already been confirmed as a near exact match by Datadog researchers
It is unclear what prompted the source code release. It's also unclear if the code was, indeed, released by TeamPCP and not by a rival group posing as them.
This doesn't actually matter, though, since the damage has already been done. The code's availability is bound to spawn a wave of attacks against GitHub repositories and the developer ecosystems. Just think of how the release of the Mirai malware code led to an invasion of IoT botnets that is still going on today. Or how the release of the Babuk and LockBit source code caused similar spikes of ransomware activity.
The Mirai code release was intended to help the malware's original creator hide in a storm of similar activity. It could be quite plausible that TeamPCP is also trying to hide in a similar way.
The individual who announced the Shai-Hulud leak encouraged other threat actors to use the worm, even promising a $10,000 reward to whoever carries out the largest supply chain attack in the coming days.
The theory that TeamPCP may be trying to hide its tracks is a legitimate one, but I doubt it will work. The worm was first seen in November and has been tied to at least six supply chain attacks so far.
That's a lot of logs the group has left traces in.
Risky Business Podcasts
The main Risky Business podcast is now on YouTube with video versions of our recent episodes. Below is our latest weekly show with Pat, Adam, and James at the helm!
Breaches, hacks, and security incidents
Transit Finance crypto-heist: Hackers have stolen $1.9 million from the Transit Finance cross-chain aggregator. The hackers exploited a four-year-old legacy smart contract to extract the funds. The platform promised to compensate affected users.
TAC crypto-heist: Hackers have stolen $2.8 million from the TAC cross-chain platform. The incident took place on the same day and also targeted a smart contract that interacts with the TON blockchain. The same type of contract was exploited in the Transit Finance too.
OpenAI impacted by TanStack incident: OpenAI is rotating code-signing certificates after two employees were impacted by the TanStack supply-chain attack this week. The company confirmed malicious activity originating from the two employee devices that matched the Mini Shai-Hulud worm. OpenAI says the intrusion was limited to a small number of repositories and the malware didn't have any access to user data. [OpenAI]
General tech and privacy
Meta adds Incognito Chat to AI: Meta has added an incognito mode for its AI assistant on WhatsApp and its Meta AI app. The company claims that all the incognito conversations are processed inside a secure environment where even its engineers can't see. [Meta]
Debian makes reproducible builds mandatory: The Debian OS project is mandating that all new Debian packages use reproducible builds. All packages that want to be included in the upcoming Debian 14 release must adopt the new coding practice. Reproducible builds can allow developers to verify that a binary has originated from specific source code.
Government, politics, and policy
The Pentagon is very confused: Pentagon officials are deploying Anthropic's Mythos model to find security flaws while they are fighting in court to label the company a supply chain risk. [Reuters]
UK to rewrite key cybercrime laws: The UK government is moving forward with a plan to rewrite the country's main cybercrime law—the Computer Misuse Act of 1990. The new version will include protections for security researchers, something the first version did not include last year. The overhaul will also include a new legal mechanism named Cyber Crime Risk Orders designed to disrupt cybercrime operations—but details are currently scarce. [The Record]
Sponsor section
In this Risky Business sponsor interview, Patrick Gray chats with Knocknoc CEO Adam Pointon about their Greynoise integration.
Arrests, cybercrime, and threat intel
Dream Market admin charged: The US has charged a 49-year-old German national with running the now-defunct Dream dark web marketplace. Owe Martin Andresen was arrested in Germany last week. Dream Market launched in 2013 and was shut down by authorities in 2019. He operated on the site under the name of "Speedstepper" and was the market's top admin. Although other Dream Market admins were detained and sentenced to prison in previous years, he was never identified. Authorities finally tracked him down after he converted some of the Dream market Bitcoin into gold bars and sending them to his home in Germany
Chinese hacker extradited to South Korea: South Korean authorities have extradited a Chinese hacker from Thailand. The suspect was the leader of a group that stole more than $275 million from local celebrities. The group hacked a South Korean telco in 2023 and used the data to gain access to the victims' bank accounts. The group's most famous victim was Jung Kook, a member of K-pop supergroup BTS. [The Chosun Daily]
Teenager convicted: A 16-year-old teenager in the occupied territories of Donetsk has been found guilty by a Russian court of selling hacked accounts on a Telegram channel. Authorities say the hacked accounts were later used to place fraudulent calls to Russian citizens through instant messengers. His sentencing was scheduled for next month.
SIM farm disrupted in St. Petersburg: Russian authorities have dismantled a SIM farm operating in the city of Sankt Petersburg. The farm ran more than 6,000 SIM cards and was primarily used to place scam calls. Russian authorities claim some of the SIM farm's customers included scammers from Ukraine. [Baza]

Scam compounded raided twice in six months: Cambodian authorities have raided a scam compound in the city of Sihanoukville for the second time in six months. More than 400 suspects were detained, but even more fled through the streets. Gun shots were reported by authorities during the breakout. The same scam compound location was also raided in December when 50 suspects were arrested. [JinBianNews] [h/t Cyber Scam Monitor]
As has been standard practice for several years, under pressure, police extracted certain individuals, and left the scam operation to continue operating. After the December raid we continued to hear from people held there against their will. 4/6
— Cyber Scam Monitor (@cyberscammonitor.bsky.social) May 11, 2026 at 2:38 AM
Chaos in Sihanoukville, Shots Fired in Fourth Raid on Jin Yu Men Tang Casino
— Jacob in Cambodia 🇺🇸 🇰🇭 (@jacobincambodia) May 9, 2026
Authorities raided Jin Yu Men Tang Casino in Sihanoukville this evening, the fourth time officers have hit the location. Khmer reporting describes shots fired during the operation. Officers detained… https://t.co/QzIq6KLZRC pic.twitter.com/Lm4UIGawcu
France investigates Israeli disinfo firm: French authorities have launched an investigation into an Israeli company named BlackCore over a disinformation campaign. Officials say the company may be linked to an online campaign that smeared three mayoral candidates of the France Unbowed party. The campaign targeted mayoral candidates for the cities of Marseille, Toulouse, and Roubaix. The far-left party has criticized Israel for its Palestine war. [Reuters]
NATS abused as C2: Threat actors are using the NATS.io messaging service for hosting malware command-and-control infrastructure. [Sysdig]
KongTuke switches to Teams: The KongTuke e-crime group has switched from ClickFix campaigns to carrying out Microsoft Teams phishing and social engineering as the initial entry point into corporate environments. The final payload is their own custom ModeloRAT. [Rapid7 // ReliaQuest]
WaSteal extensions: A cluster of 126 Google Chrome extensions posing as WhatsApp business helpers are stealing their victims' WhatsApp data. The extensions target the Brazilian market and have been installed more than 146,000 times. They work by intercepting WhatsApp content, including messages, cookies, and even audio. [MalExt]
Malicious npm packages go after Claude: A cluster of five npm extensions are backdooring local Claude agents to intercept their prompts. [Safedep]
Node-ipc incident: And speaking of npm malware, an infostealer was active in newly-released versions of the node-ipc library. [Datadog // Semgrep // Step Security // Socket Security]
Tycoon 2FA adopts DCP: The operators of the Tycoon 2FA, the largest PhaaS provider around, has added support for device code phishing. Device code phishing was first seen used in mass-campaigns by APT groups last year. It has since become wildly popular in the e-crime ecosystem, with several phishing providers adding support for it this year. [eSentire // Proofpoint]
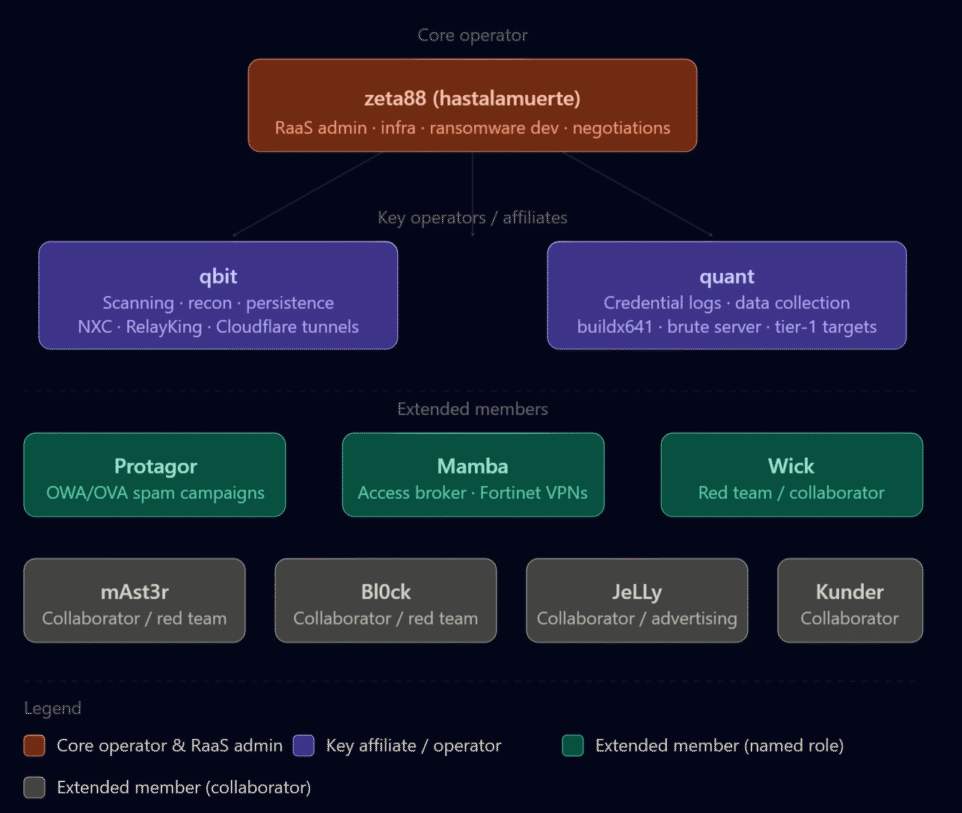
The Gentlemen leak exposes admins and affiliates: Check Point has managed to get its hands on the data that was hacked and leaked from The Gentlemen RaaS. The leak included info on the platform's nine admins and affiliates, internal discussions, info on favorite exploits and tools, and some screenshots of ransom negotiations. Overall, it's not as devastating as the Conti and LockBit leaks, but it still provides an insight into the gang's operations. [Check Point]
Malware technical reports
OrBit returns: A Linux rootkit that hasn't been spotted since 2022 has a new version going around in the wild. [Intezer]
"Nearly four years later, OrBit is still in the wild, and it has not stood still. Hunting across VirusTotal, we pulled more than a dozen samples spanning 2022 through 2026 and walked each one through static and differential analysis. We discovered two parallel lineages: a full-featured “Lineage A” build that tracks closely with the 2022 original, and a lite “Lineage B” fork that drops entire capability domains (PAM, pcap, TCP-port hiding) in exchange for a smaller footprint."
Turla's Kazuar: Microsoft's security team at recent versions of Turla's Kazuar malware family, malware family that's now more than a decade old. [Microsoft]
Sponsor section
In this product demo, Knocknoc CEO Adam Pointon walks Patrick Gray through the Knocknoc secure access platform. Knocknoc is a platform that restricts network and service availability to authenticated users via existing network security equipment. Users don't need to install an agent. It also has an identity-aware proxy component that supports web applications and RDP.
APTs, cyber-espionage, and info-ops
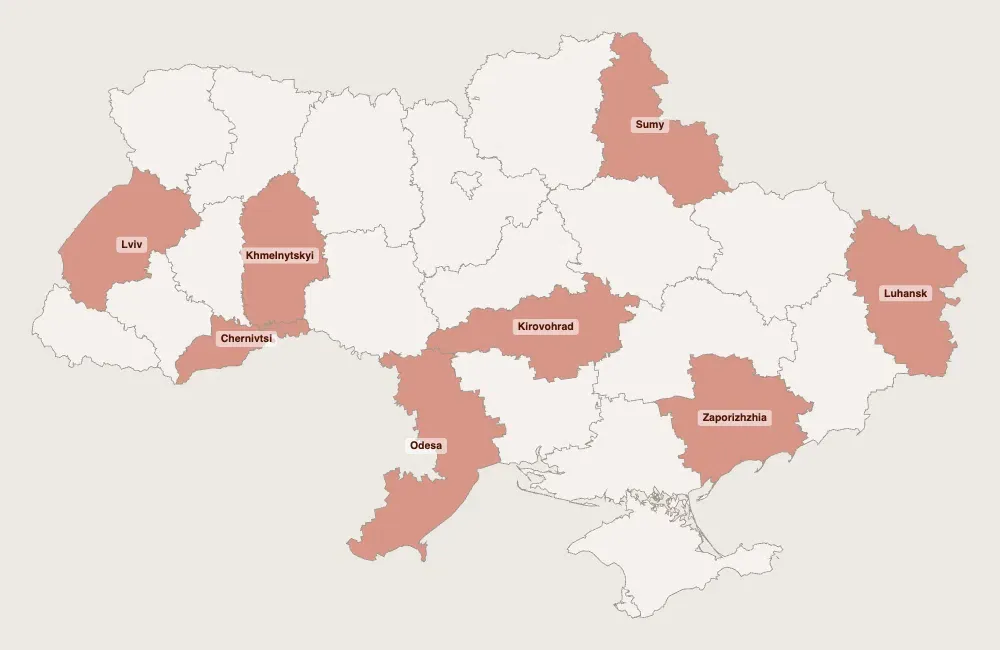
Gammaredon continues WinRAR campaigns: Last year, when a WinRAR zero-day (CVE-2025-8088) was disclosed, the Gammaredon Russian APT group was the first ones to jump on the exploit. Those campaigns are still ongoing, and are exclusively targeting Ukraine. [Harfang Lab]
"Historically, Gamaredon has maintained near exclusive focus on Ukraine since it first appeared in 2013, just months before Russia’s annexation of Crimea. Over a decade later, the targeting remains consistent. Every email in the analyzed dataset targets Ukrainian state institutions or individuals connected to them, spanning the state administration, security, justice and law enforcement sectors in Odesa, Sumy, Kirovohrad, Zaporizhzhia and Khmelnytskyi."
FrostyNeighbor/GhostWriter: And speaking of APTs targeting Ukraine, ESET has also been documenting a FrostyNeighbor campaign. [ESET]
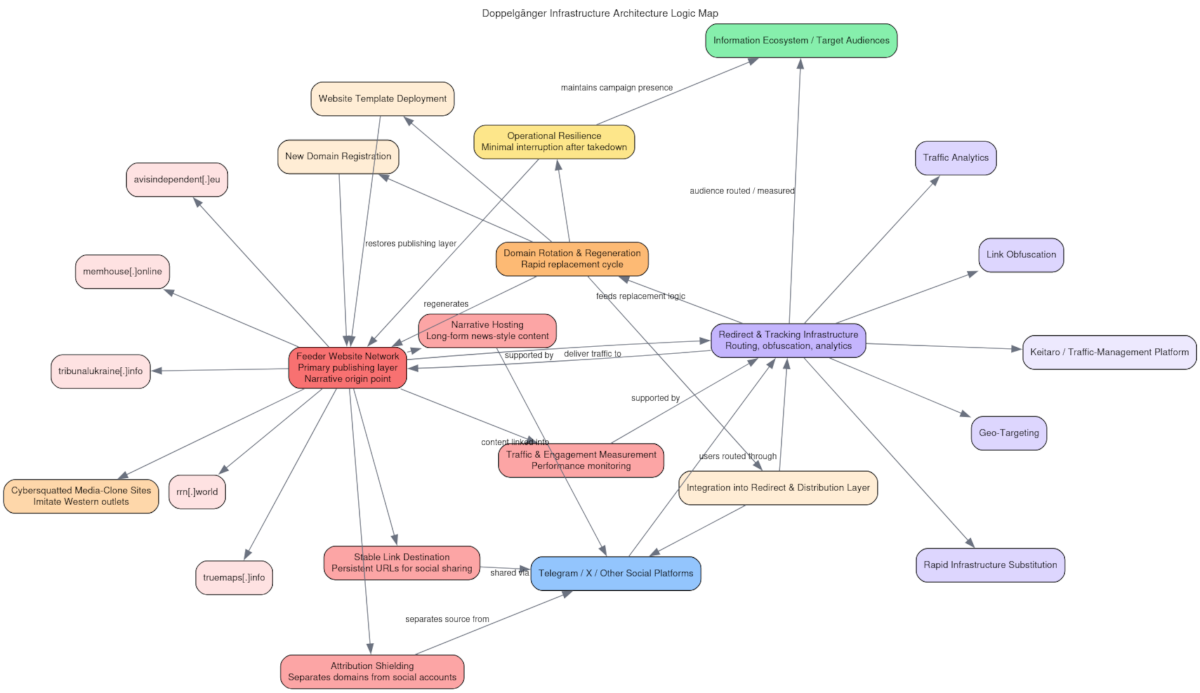
Doppelgänger structure: The DomainTools security team has published one of their typical high-quality write-ups, this time on Doppelgänger (aka Social Design Agency) disinformation campaigns. [DomainTools]
"The operational architecture is designed around a feeder-and-amplifier model. Controlled websites host narrative artifacts such as articles, memes, and commentary. These artifacts are distributed through Telegram channels with large subscriber bases and are subsequently injected into active discussions on X through coordinated reply swarms."
Paper Werewolf's PaperGrabber: Russian security firm BI.ZONE has been tracking a new campaign from APT group Paper Werewolf. For these attacks, the group showcased its sophistication and deployed a new infostealer named PaperGrabber, as well as its own custom-developed Mythic implants. [BI.ZONE]
VELVET CHOLLIMA infostealer campaign: Malware analyst Vlad Pasca has published an analysis of a Velvet Chollima infostealer campaign targeting crypto developers. [Hybrid Analysis]
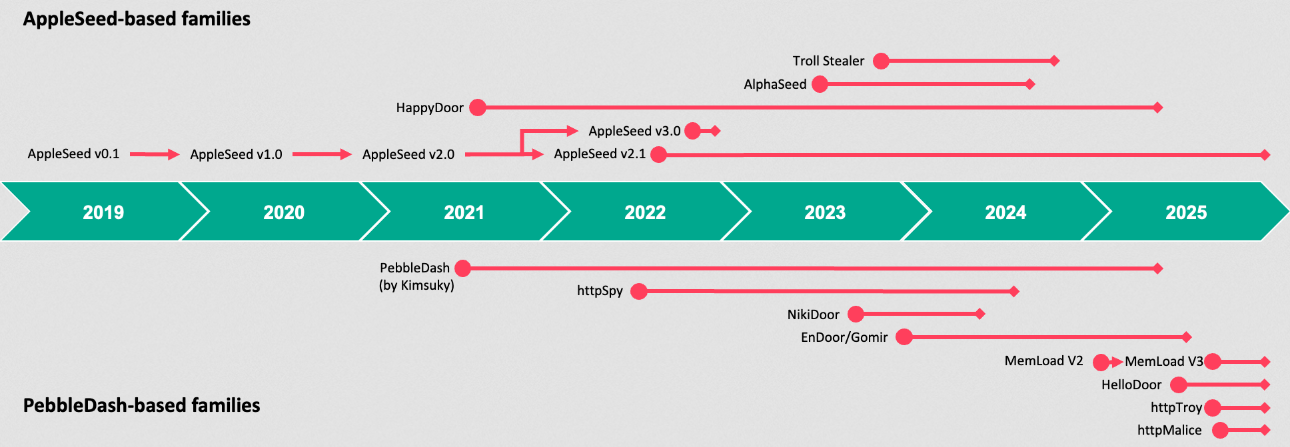
Kimsuky: DPRK APT group Kimsuky has been quite busy developing its PebbleDash malware family over the years. Per Kaspersky, AI may have been used for some of the variations. [Kaspersky]
FamousSparrow targets Azerbaijan's oil and gas industry: A suspected Chinese APT group is targeting Azerbaijan's oil and gas sector. The intrusions appear to be taking place as the country has become one of the EU's main LNG sources. Bitdefender linked the attacks to a group tracked as FamousSparrow, also known as Earth Estries. [Bitdefender]
Vulnerabilities, security research, and bug bounty
Microsoft unveils MDASH: Microsoft has unveiled a new AI model harness for discovering and helping patch software vulnerabilities. MDASH works by aggregating more than 100 specialized AI agents into one singular platform. Sixteen of the 130 vulnerabilities patched in this month's Patch Tuesday were discovered with MDASH.
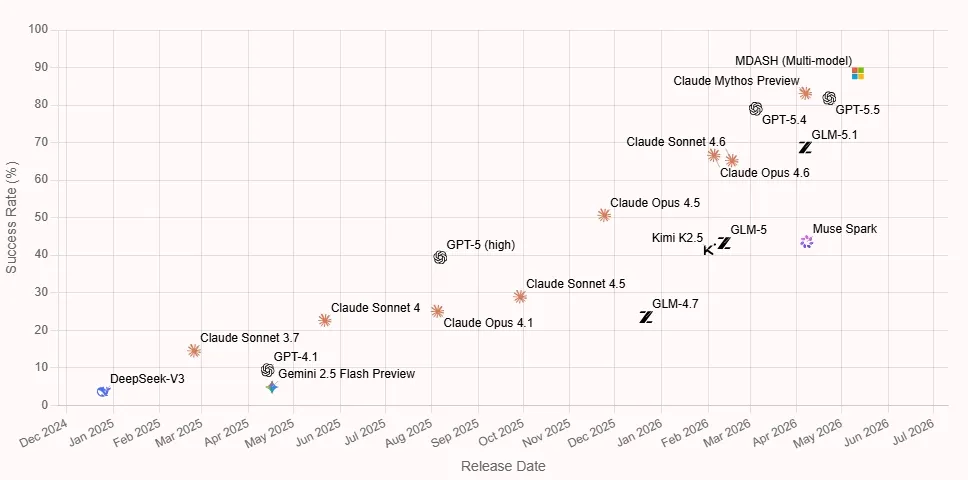
Latest AI frontier models are closing on the cyber horizon: Recent AI cyber models like Anthropic's Mythos and OpenAI's GPT-5.5-Cyber are solving cyber test ranges that previous AI models couldn't crack, and are getting closer to what researchers call the "cyber horizon," when the model will be faster at performing complex cyber tasks than a human. [AISI]
PraisonAI attacks start after 3h: Hackers began exploiting a vulnerability in PraisonAI servers three hours after a patch was released. The attacks targeted a legacy API server that shipped with the main PraisonAI server that was left enabled without any authentication (CVE-2026-44338). The quick move to exploitation was likely the result of a simple PoC. Threat actors have been recently prioritizing vulnerabilities in AI servers, with many solutions coming under attacks as soon as bugs are disclosed. [Sysdig]
Cisco patches a new SD-WAN zero-day: Cisco has released firmware updates to patch an actively exploited zero-day in Catalyst SD-WAN devices. The zero-day allows attackers to become an authenticated peer of the target appliance, and perform privileged operations. Cisco linked the recent attacks to another set of zero-days exploited in February. The same UAT-8616 group is behind this zero-day as well. [Cisco Talos // Rapid7]
FunnelKit exploitation: Hackers are exploiting a vulnerability in a very popular WooCommerce plugin to inject malicious code on online shops and steal credit card data. More than 40,000 WooCommerce stores using the FunnelKit builder are affected. Patches have been released this week. The plugin is typically used to design custom checkout experiences on WordPress-based online stores. [Sansec]
AMD finds priv-esc bug in its CPUs: CPU maker AMD has advised users to install operating system security updates to mitigate a security flaw in its CPUs. The vulnerability was discovered internally. It allows malicious code running on the CPU to break the memory cache isolation and execute at higher privileges. The bug impacts AMD Zen-2 products. This includes the company's Ryzen and EPYC product lines. [AMD security advisory for CVE-2025-54518]
Composer fixes GitHub token leak: Packagist has rolled out an emergency security update to the Composer PHP package manager to fix a bug that leaked GitHub tokens in public GitHub Actions logs. The bug was traced back to GitHub changing the token format, with tokens now including hyphen characters. GitHub paused the rollout of the new format until May 18. PHP developers are advised to install the new Composer update by then to prevent their CI/CD pipelines from leaking the tokens. [Packagist // Sansec // Socket Security]
"If you run Composer in GitHub Actions, you should treat this as urgent. We recommend disabling GitHub Actions on affected organizations or repositories until you have updated to Composer 2.9.8 or 2.2.28."
Fragnesia vulnerability: V12 Security has discovered a variation of the Dirty Frag Linux vulnerability, a local privilege escalation they are calling Fragnesia. [Tenable // Wiz]
MCP server bugs: Akamai researchers have found vulnerabilities within three popular servers that implement the MCP standard—Apache Pinot, Apache Doris, and Alibaba RDS. [Akamai]
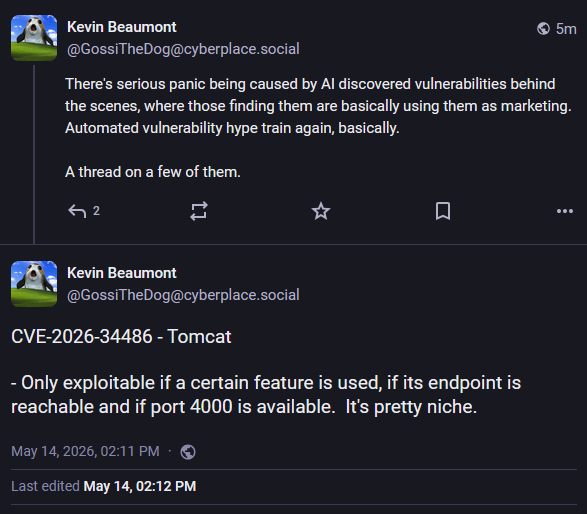
Apache Tomcat RCE: Something I missed last month was this Apache Tomcat unauth RCE bug discovered using an AI source code auditing tool. Get used to these AI-found write-ups. They're everywhere now. It was patched in April, and PoC code was released this week. [Striga]
NGINX Rift vulnerability: F5 has released security updates to fix a major vulnerability in the NGINX web server. Tracked as CVE-2026-42945, the vulnerability is located in the NGINX URL rewrite component and can enable unauthenticated remote code execution attacks. It impacts all server versions released for the past 18 years, since 2008. The bug is also known as NGINX Rift and was discovered by DepthFirst using AI tools. [F5 patches // DepthFirst write-up // POC]
Infosec industry
Threat/trend reports: Beazley Security, Intruder, Sinch, Spur, and Versa Networks have recently published reports and summaries covering various threats and infosec industry trends.
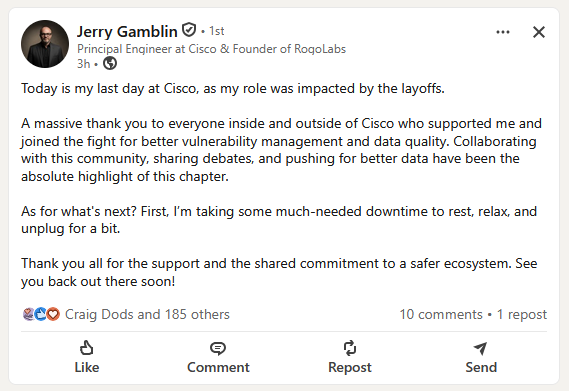
Cisco layoffs: Cisco will lay off 4,000 employees, representing around 5% of the company's global workforce. Cisco CEO Chuck Robbins says the company is currently focused on increasing its spend on AI technologies. The company announced the layoffs on the same day it reported a record revenue of $15.8 billion. [Cisco // TechCrunch]
Acquisition news: Internet infrastructure company Akamai will acquire browser security startup LayerX for $205 million.
New tool—AntiSSRF: Microsoft has open-sourced AntiSSRF, a security-developed, exhaustively-tested secure code library that provides robust URL validation to mitigate the risk of Server-Side Request Forgery (SSRF).
New tool—Vulnerability.Garden: Security researcher Shellsharks has created Vulnerability.Garden, a catalog of named vulnerabilities. So far, we're 25 vulnerabilities away from 1k branded security bugs.
Risky Business podcasts
In this edition of Seriously Risky Business, Tom Uren and James Wilson talk about the argy bargy within the Trump administration about AI regulation. They cover who is fighting, what is at stake and what the real areas of concern are.




