Risky Bulletin: Russian man investigated for extorting Conti ransomware group
In other news: Google takes down Chinese espionage operation; Mexican government hacked using Claude; new Cisco zero-day secretly exploited for three years.

This newsletter is brought to you by Socket, a developer-first security platform that prevents vulnerable and malicious open-source dependencies from infiltrating software supply chains. You can subscribe to an audio version of this newsletter as a podcast by searching for "Risky Business" in your podcatcher or subscribing via this RSS feed.
Russian authorities have arrested a Moscow resident for posing as an FSB intelligence officer to extort and demand payments from members of the Conti ransomware group.
Ruslan Satuchin was detained in October of last year and has remained in custody after authorities extended his arrest warrant in December.
According to Russian news outlet RBC, the suspect contacted a Conti member in September of 2022, claiming he could prevent the FSB from investigating them for a bribe.
While the report doesn't mention how Satuchin identified the Conti members, his alleged extortion campaign began six months after an unnamed Ukrainian IT specialist hacked the group and released internal chats on the internet, shortly after Russia's invasion of Ukraine.
Within weeks of the dump, several threat intel specialists linked some Conti members to their real world identities, with many members being based in Russia.
RBC reported that Satuchin is pleading not guilty and had known of the investigation against him before his arrest, but refused to flee the country. A Moscow court denied his request for release on house arrest in December, with prosecutors claiming he might try to intimidate Conti members to withdraw their accusations.
The Conti gang has been operational and launching attacks for more than a decade now. It initially launched under the name Ryuk, and later became Conti. After its 2022 leak, the group's members have been linked to a bunch of smaller ransomware operations, such as BlackSuit, Royal, and Chaos.
Conti is believed to have hacked hundreds of organizations across the world and made an estimated $150 million from their ransomware attacks.
Even if the US State Department has rewards for up to $10 million for information on Conti members for their past attacks, Russian media kept calling them "patriotic hackers" in all their reports this week, just because they never attacked Russian companies. Nice moral compass you got there, Russia!
Satuchin faces up to ten years in prison if found guilty.
[h/t Oleg Shakirov, A.C.]
Risky Business Podcasts
The main Risky Business podcast is now on YouTube with video versions of our recent episodes. Below is our latest weekly show with Pat and Adam at the helm!
Breaches, hacks, and security incidents
Mexican government hacked using Claude: A hacker has stolen more than 150 gigabytes of data from multiple Mexican government agencies. The attacker allegedly used Claude to assemble scripts to gain access to government networks. According to Bloomberg, he breached and stole data from Mexico's tax authority, national electoral institute, and several state water utilities. The stolen data covers 195 million taxpayer and voter records, government employee credentials, and civil registry files.
UFP cyberattack: Medical device manufacturer UFP Technologies has likely been hit by a ransomware attack. The company told investors it deployed its backups after attackers stole and destroyed some of its data. No ransomware group has yet taken credit for the attack. [The Record]
ManoMano hack: Spanish home improvement and DIY retail chain is notifying customers of a security breach.
Canada Tire breach: Hackers have leaked the personal details of 38 million customers of Canadian retailer Canadian Tire. The data was stolen in a hack last October. Stolen data included names, phone numbers, and physical addresses.
Olympique de Marseille cyberattack: Hackers have breached the online store of French football club Olympique de Marseille and are now selling the data online. The club confirmed the incident this week.
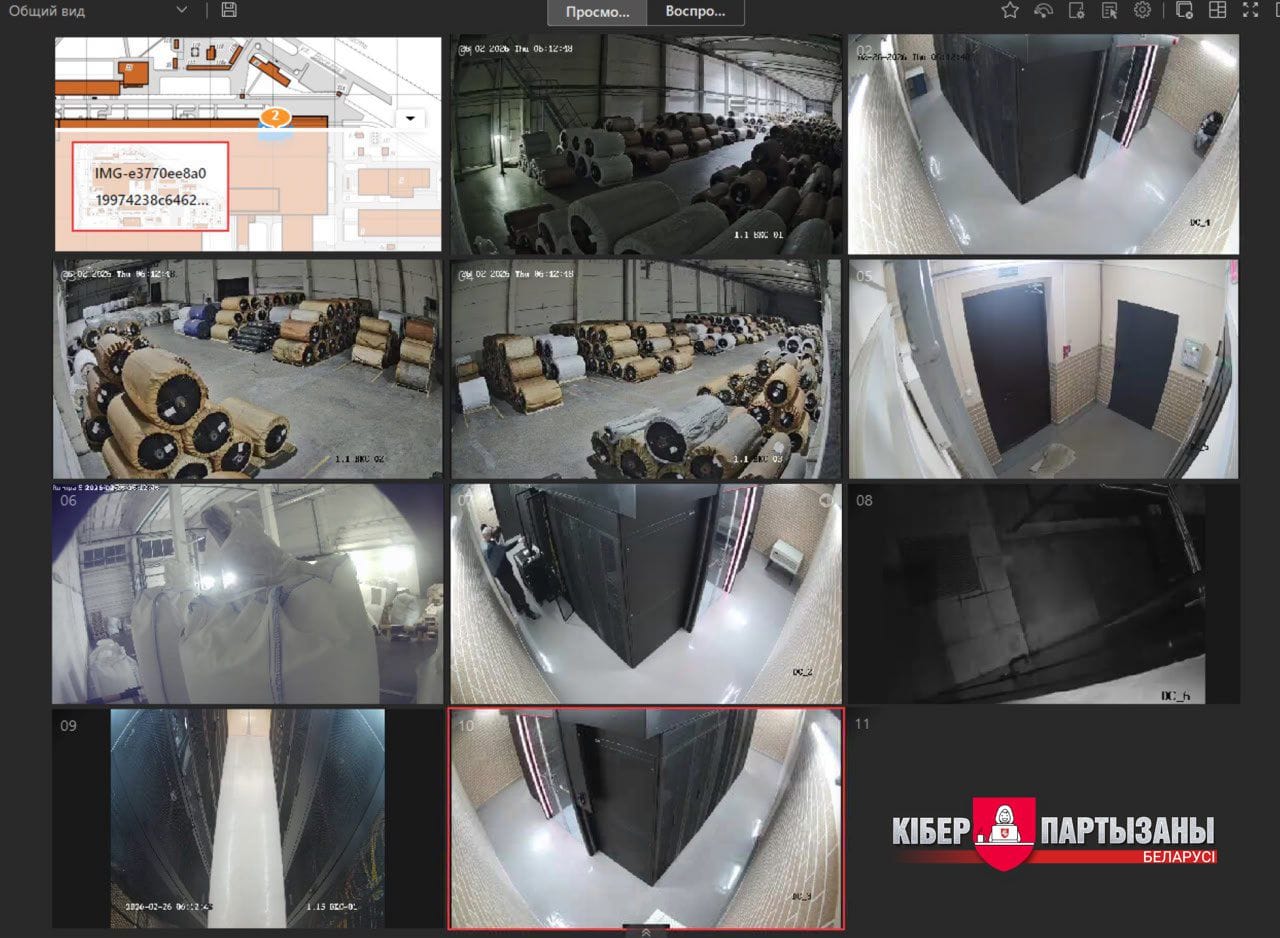
Khimvolokno cyberattack: Belarusian hacktivist group the Cyber Partisans claim to have hacked Belarusian industrial giant Khimvolokno. The company is Russia's largest supplier of nylon threads used for military helmets and body armor. The Cyber Partisans say they hacked Khimvolokno on the fourth year anniversary of Russia's invasion of Ukraine. They claim to have gained full admin access within a day and destroyed crucial servers and more than 1,000 workstations.
General tech and privacy
Apple age requirements: Apple has published details on how it plans to deal with all the age verification requirements around the globe and the US. It will be a mixture of age categories and parental controls.
FTC urges age verification: The FTC has urged online platforms to adopt age verification technologies, promising not to bring COPPA enforcement cases if they don't use age check data for something else except age checks.
New York sues Valve over loot boxes: The state of New York has sued Valve for using a loot box mechanism in its games—Counter-Strike 2, Team Fortress 2, and Dota 2.
Mountain View cancels Flock contract: After disabling its Flock license plate readers at the start of the month, the city of Mountain View in California, the home of the US tech sector, has canceled the contract altogether. The city says the company allowed out-of-state agencies to access the cameras and its data without permission. [NBC Bay Area]
Meta AI floods police forces: Meta's stupid AI is generating false CSAM reports and flooding police departments across the US, according to the US Internet Crimes Against Children (ICAC) taskforce. [The Guardian]
Google to revamp Search in the EU: To avoid a massive fine in the EU, Google will soon roll out changes to its search engine on the continent that will also show results from rival services, and not just its own. This will cover search results for hotels, flights, or restaurants, where Google was previously prioritizing its own apps and services so it could rack up the commissions. [Reuters]
1Password increases prices: Password manager 1Password is about to lose a ton of users after it increased prices by quite a considerable amount this week. [TidBITS]
Government, politics, and policy
Anthropic responds to "War Department" pressure: The AI company has posted a statement from CEO Dario Amodei, rejecting Pete Hegseth's demands that it unshackle it model's safeguards for the US military. Amodei said its technology is not reliable enough to be used for fully autonomous weapons. It is also standing firm on its rule that Anthropic’s model cannot be used for mass surveillance of Americans. The company said it "will work to enable a smooth transition to another provider" if the Department chooses to "offboard" it.
US tells diplomats to fight foreign data sovereignty laws: The US State Department has told diplomats to lobby against laws designed to prevent American tech companies from handling foreigners' data. US officials argue data sovereignty and data localization laws will hinder the US AI sector. Since taking office last year, the Trump administration has repeatedly focused on fighting data privacy and protection laws. [Reuters]
Russia's VPN ban reaches 469: The Roskomnadzor's VPN ban count has now reached 469 apps and services, as of this month. [Ria Novosti]
Full Telegram block expected in April: The Russian government is allegedly planning to block all Telegram traffic starting in April this year. The country's internet watchdog has been slowly blocking Telegram features and throttling traffic since August of last year. Currently, Roskomnadzor is throttling Telegram traffic at 55%. Authorities also launched a criminal probe of Telegram founder and CEO Pavel Durov this week. He is accused of facilitating terrorist activity on the platform. [RBC]
UK NCSC reports better patching numbers: The UK's cybersecurity agency says vulnerabilities are being fixed six times faster after it launched a vulnerability monitoring service last January. Bugs and misconfigurations are now being patched in eight days, down from the previous average of almost two months. The NCSC Vulnerability Monitoring Service works by continuously scanning the networks of more than 6,000 UK public sector bodies. It currently processes and resolves around 400 issues each month.
The Netherlands approves Solvinity sale: The Dutch government's market authority has approved the sale of cloud provider Solvinity to American company Kyndryl, meaning the government's cloud networks now run on the infrastructure of a US company. Major political figures have pressured the government not to approve the sale due to data sovereignty concerns.
Sponsor section
In this Risky Business sponsor interview, Casey Ellis and Feross Aboukhadijeh discuss how AI is affecting open source, chat about a few attacks the company has seen in the wild and introduce Socket’s answer to the smouldering trashfire: Socket Firewall.
Arrests, cybercrime, and threat intel
Four sentenced in Predatorgate scandal: Four individuals have been sentenced to prison in the Predatorgate scandal in Greece. Three executives from Intellexa and one from Krikel have been collectively sentenced to 126 years and eight months in prison. They will have to serve at least eight years of the sentences, pending an appeal. Intellexa founder Tal Dillian is one of those sentenced. No Greek government official was on trial, even if they paid and deployed the Predator spyware against journalists and political opponents. [eKathimerini // Politico Europe]
“The court rejected any mitigating circumstances to the four defendants, and imposed a combined prison sentence of 126 years and eight months, eight of which will have to be served. The prosecutor recommend the full service of the sentence but the court suspended it pending appeal.”
— Vas Panagiotopoulos (@vaspanagiotopoulos.com) 2026-02-26T11:31:27.124Z
Vastaamo hacker disappears: Finnish hacker Aleksanteri Kivimäki has lost an appeal and will have to go back to prison after the court increased his original sentence. His lawyer says he has left the country and his whereabouts are currently unknown. Kivimäki was sentenced to six years and three months for hacking the Vastaamo psychotherapy centre in 2020 and extorting patients. He was released from prison last year following an appeal. The Helsinki Appeals Court has now rejected his case and even increased his sentence to six years and eleven months. Kivimäki's lawyer says his client plans to return to Finland and serve the rest of his sentence. [Yle]
SLH starts recruiting women: The Scattered Lapsus$ Hunters (SLH) hacking group is recruiting women to carry out vishing attacks against the help desks of large companies. According to Dataminr, the goal to use female voices is to bypass security training received by help desk staff. The group is known to have male members. Female recruits are being promised $500 to $1,000 upfront.
Fin crime still prevalent: A study of 54,000 security incidents found that 71% of incidents were financially motivated crimes, with ransomware being the most common type of intrusion. The study also found that in most cases, the victims failed to maintain their IT infrastructure. This included weak passwords, unpatched servers, and incomplete logging and monitoring.
Data extortion claims increased: Cyber insurance claims to cover data theft and extortion attacks have overshadowed ransomware for the first time last year. Data theft-only attacks accounted for 57% of all extortion insurance claims last year, according to numbers released by cyber insurance provider Resilience.
This doesn't surprise me. Orgs have greatly matured their recovery operations to the point that they'll wipe and restore rather than pay for a decryption key. The attackers are going where the money is.
— Jesse Harris (@elforesto.coolestfamilyever.com) 2026-02-26T15:55:41.933Z
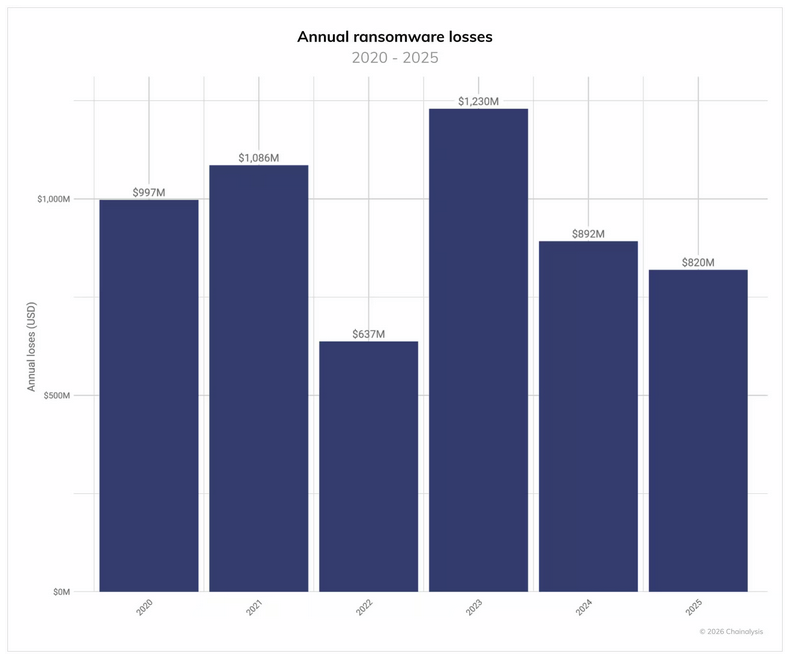
Ransomware payments stagnate: The total ransomware payments last year stagnated even if the number of attacks increased. According to blockchain analysis firm Chainalysis, ransomware gangs made $820 million in 2025, about the same amount they made the year before. Chainalysis joins a larger list of threat intel companies spotting a decline in the number of victims who pay attackers.
CrashFix variant abuses promise bombs: Secure Annex has found two malicious Chrome extensions that used JavaScript promise bombs to crash browsers and then show malicious instructions to fix the issue that actually infected users with malware.
Malicious NuGet package steals Stripe API tokens: ReversingLabs has found a malicious NuGet package that posed as a Stripe payment utility but stole its users API tokens.
Malicious npm package: Tenable has discovered a malicious npm package (ambar-src) that was downloaded more than 50,000 times in just a few days.
ARPA abuse: Phishing groups are abusing .arpa domains for their operations, a TLD that's not supposed to host anything except IP-address-to-domain maps.
WebDAV campaign: Cofense has spotted a phishing campaign abusing LNK shortcut files and WebDAV to download malicious files on targets' systems.
"Campaigns seen using this tactic tend to use complex chains of multiple different script payloads and legitimate files to deliver remote access trojans (RATs) that are hosted on different WebDAV servers."
OCRFix campaign: Cyjax has discovered a ClickFix campaign that used websites impersonating the Tesseract OCR tool as a springboard for its attacks.
GTFire campaign: Group-IB is tracking a phishing campaign using Google Firebase to host the phishing pages and Google Translate to disguise the malicious URLs and bypass email and web security filters.
Post-RAMP takedown evolution: Rapid7 looks at several new hacking forums that are popping up online after the law enforcement takedown of RAMP. Possible successors include the likes of T1erOne and DragonForce's Rehub.
D-Shortiez leak and skullduggery: A security firm has gained access to a malvertising test platform and used the information to help ad companies block more than 59 million malicious ads last year. Confiant says the test platform was operated by D-Shortiez, a malvertising group active since 2022. The platform allowed security researchers to get an early preview of upcoming campaigns, data they shared with the ad tech industry.
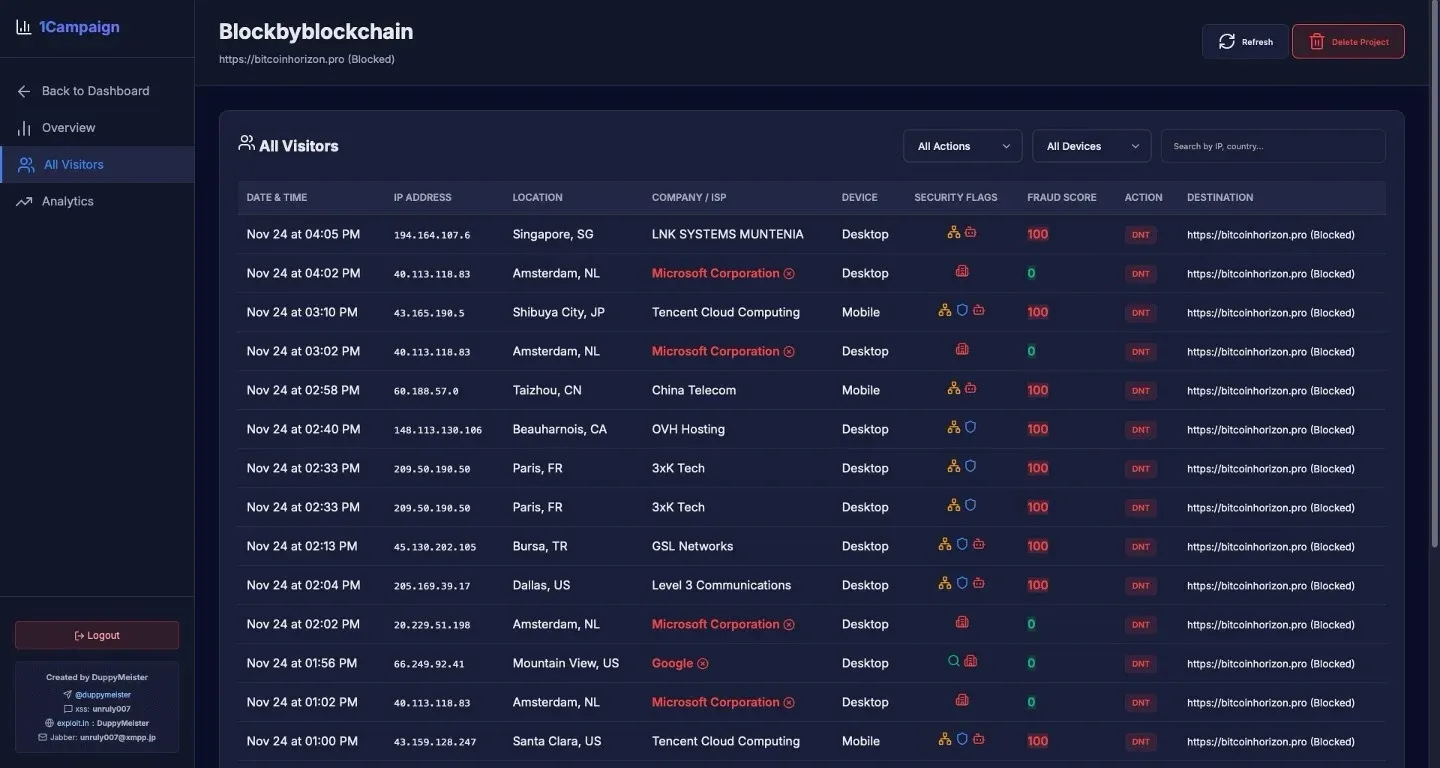
1Campaign profile: Varonis has published a profile on 1Campaign, a new service to help threat actors bypass Google's new ads screening feature and run malvertising campaigns through Google Ads.
"At its core, 1Campaign is a cloaker. Cloaking is a technique where malicious actors show different content to different visitors. Security researchers, ad platform reviewers, and automated scanners see a harmless "white page," while real victims see the actual phishing or scam content."
Malware technical reports
C77L ransomware: Russian security firm F6 has discovered a new RaaS named C77L that appears to be operated out of Iran. The RaaS has been active since March of last year and has been used in attacks against at least 40 Russian and Belarussian organizations. The initial entry point appears to be unsecured VPN and RDP endpoints.
Dohdoor: Cisco Talos has identified a new backdoor named Dohdoor that has been distributed in the wild since December and has primarily targeted the US education and health care sectors. Talos believes this might be North Korean malware.
ComSuon: Gen Digital researchers have discovered a new infostealer named ComSuon.
DarkCloud: Flashpoint looks at DarkCloud, a commercially available infostealer first seen in 2022 and written in Visual Basic 6.0.
Agent Tesla: The Agent Tesla infostealer is still active, despite being abandoned for a few years now. Fortinet looks at one of the recent campaigns distributing it.
ResidentBat: Censys has identified 10 command and control servers used for ResidentBat, an Android spyware implant used by the Belarusian KGB.
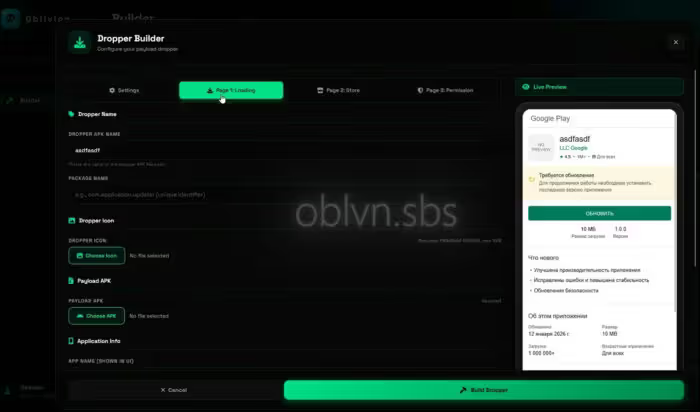
Oblivion: Certo researchers have spotted a new Android RAT named Oblivion that is being sold on underground hacking forums.
Sponsor section
In this Soap Box edition of the Risky Business podcast Patrick Gray chats with Socket founder Feross Aboukhadijeh about how to measure the reachability of vulnerabilities in applications. It's great to know there's a CVE in a library you're using, but it's even better if you can say whether or not that vulnerability actually impacts your application.
APTs, cyber-espionage, and info-ops
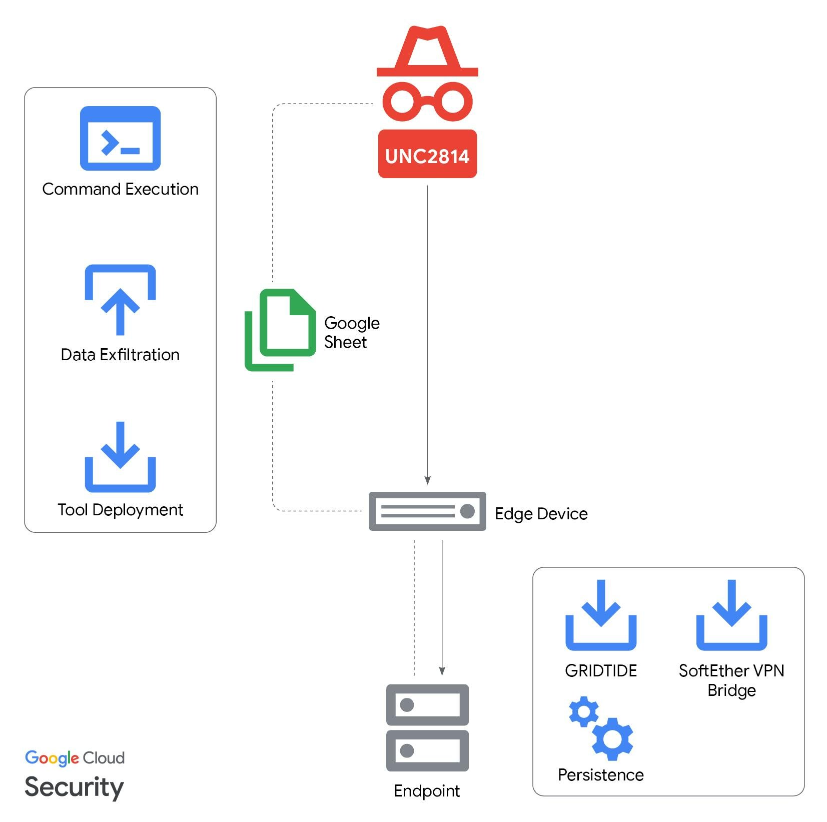
Google disrupts UNC2814: Google has taken down infrastructure used by a Chinese cyber-espionage group in attacks targeting telecoms and governments over the past three years. The company has disabled Google Cloud servers and Google Sheets accounts used for the command and control backend of a new backdoor named GRIDTIDE. Google says the malware is the work of a group it tracks as UNC2814.
Contagious Interview: Abstract Security is tracking a Contagious Interview campaign that uses boobytrapped VSCode and Cursor IDE projects to infect jobseekers with malware. This campaign has been taking place for half a decade now and is the work of North Korean hackers, seeking access to developer environments from where they could pivot to more networks.
Info-ops come to Threads: Meta's new Threads micro-blogging platform and Twitter rival has been flooded with pro-PRC propaganda bots, according to a new report.
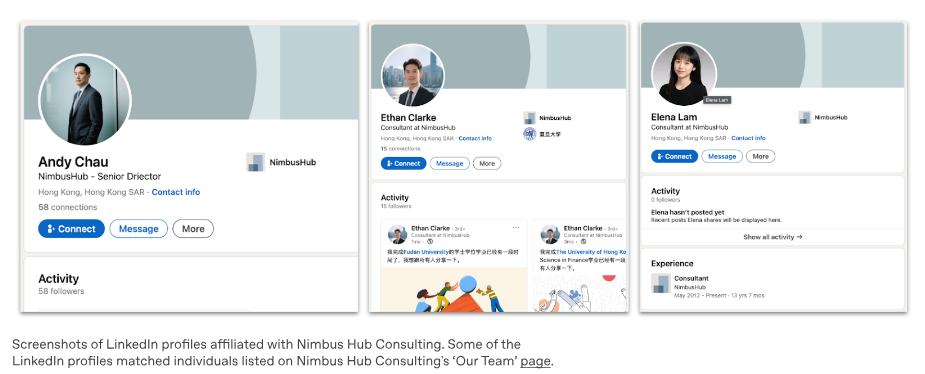
OpenAI disrupts new info-ops: OpenAI has taken down ChatGPT accounts linked to a possible Chinese intelligence operation. The accounts wrote emails and performed reconnaissance of their targets. They used a fake corporate identity but their queries were focused on geopolitical topics. OpenAI also took down clusters running online scams, Russian influence operations across Africa, and a Chinese info-op targeting Japan's prime minister.
Vulnerabilities, security research, and bug bounty
New Cisco zero-day: Cisco has released firmware patches to fix an actively exploited zero-day in Catalyst SD-WAN devices. Attackers are exploiting a vulnerability (CVE-2026-20127) in the peering authentication system to gain access to the device with admin privileges. It has a CVSS severity rating of 10/10. Attacks with the zero-day were discovered by the Australian Signals Directorate. Cisco's security team traced back the attacks to 2023 and linked them ot a group it tracks as UAT-8616. An older 2022 bug in the same devices was also exploited as part of the attacks.
FreePBX exploitation: More than 900 FreePBX telephony servers have been infected with the EncystPHP webshell. Almost half of the infected servers are located in the US. The attacks are exploiting a vulnerability (CVE-2025-64328) patched in November that lets attacks inject commands in the server's administrative interface.
Zyxel patches: Taiwanese hardware vendor has released patches for seven vulnerabilities in its routers and wireless extenders. Some of the patches cover some serious bugs such as an unauth command injection tracked as CVE-2025-13942.
Other important security patches: Grafana, Juniper, Trend Micro.
SolarWinds WHD RCE: WatchTowr Labs has published a write-up on a two-vuln exploit chain composed of an auth bypass and deserialization issue that can be used for RCE attacks on SolarWinds Web Help Desk servers. This was patched at the end of January. The two bugs are tracked as CVE-2025-40552 and CVE-2025-40553.
1% of 2025's vulnerabilities were exploited: Only 422 of security flaws discovered last year were exploited in the wild. The number represents almost 1% of all vulnerabilities disclosed last year. Network edge devices accounted for a third of all products exploited last year. According to VulnCheck, those that got exploited were abused shortly after disclosure, by multiple threat actors, and caused sprawling damage before companies could patch.
Researcher accidentally hacks 7,000 smart vacuums: DJI has patched a security flaw in its backend that could have allowed attackers to take over all its Romo smart vacuums. Security researcher Sammy Azdoufal says DJI servers returned data for any device just by providing a device serial number. DJI shared the data on any device without any authentication or authorization. Azdoufal says he was able to map the locations of more than 7,000 Romo smart vacuums and 3,000 DJI portable power stations that shared the same server. [The Verge]
Internet scans were indirectly flooding Let's Encrypt: The Let's Encrypt free certificate authority has stopped issuing certificates for very long domain names. The project blamed the issue on some misconfigured servers. Random internet scans hitting the servers would cause them to request new certificates and flood Let's Encrypt servers. These new certificate requests would usually appear with very long domain names and DNS labels.
New AirSnitch attack: Academics have developed a new attack that breaks the encryption that separates WiFi clients. The new AirSnitch attack exploits how the routers work at the first two layers of the OSI layer, rather than attacking their software. It was successfully tested against routers from major vendors like Netgear, D-Link, Ubiquiti, and Cisco. It also works against devices running open-source firmware like DD-WRT and OpenWrt. [ArsTechnica]
We found that Wi-Fi client isolation can often be bypassed. This allows an attacker who can connect to a network, either as a malicious insider or by connecting to a co-located open network, to attack others. NDSS'26 paper: www.ndss-symposium.org/wp-content/u... GitHub: github.com/vanhoefm/air...
— Mathy Vanhoef (@vanhoefm.bsky.social) 2026-02-26T18:32:21.867Z
Infosec industry
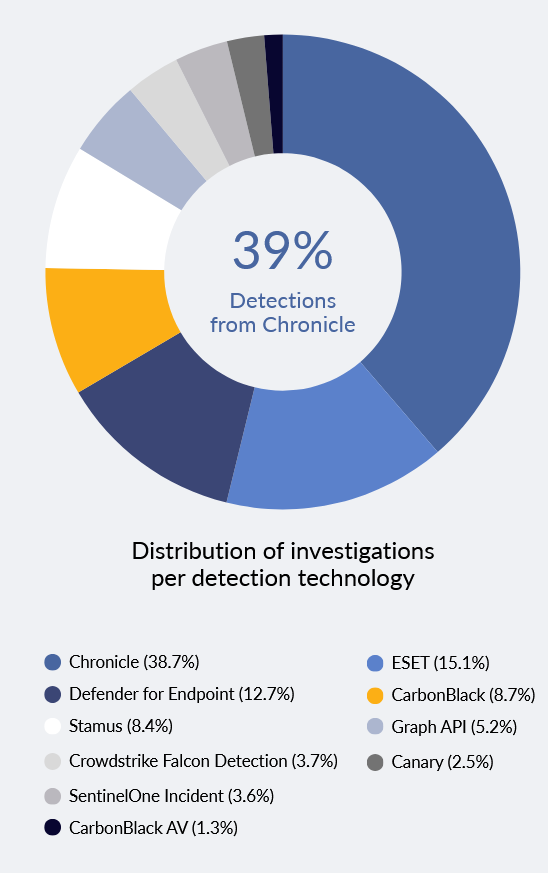
Threat/trend reports: Chainalysis, DarkTrace, Exabeam, Expel, Experian, Hunt & Hackett, IBM X-Force, LevelBlue, NCC Group, NewsGuard, Pew Research, ReliaQuest, Resilience, and VulnCheck have recently published reports and summaries covering various threats and infosec industry trends.
New tool—Systing: Josef Bacik has released Systing, an eBPF-based tracing tool.
New tool—AutoPiff: Security researcher Ahmad Abdillah has published AutoPiff, an analysis engine for detecting vulnerability fixes in Windows kernel driver patches.
DefCamp 2025 videos: Talks from the DefCamp 2025 security conference, which took place in Bucharest at the end of November, are now available on YouTube.
Risky Business podcasts
In this edition of Seriously Risky Business, Tom Uren and Amberleigh Jack talk about the argy bargy between the Pentagon and AI company Anthropic. US Defense Secretary Pete Hegseth is demanding that all safeguards are lifted from Claude, while Anthropic CEO Dario Amodei is insisting on protections against mass surveillance of Americans and use in lethal autonomous weapons.
In this edition of Between Two Nerds, Tom Uren and The Grugq talk about how 'professional' Five Eyes cyber espionage agencies like NSA will use AI. These agencies place a premium on stealth and won't yolo AI.




