Risky Bulletin: Russia starts criminal probe of Telegram founder Pavel Durov
In other news: Teenagers are behind the Ttareungyi hack; Anthropic accuses three Chinese AI companies of distillation attacks; US Treasury sanctions Russian exploit broker.

This newsletter is brought to you by Socket, a developer-first security platform that prevents vulnerable and malicious open-source dependencies from infiltrating software supply chains. You can subscribe to an audio version of this newsletter as a podcast by searching for "Risky Business" in your podcatcher or subscribing via this RSS feed.
Russian authorities have launched a criminal investigation of Telegram founder and CEO Pavel Durov. He is allegedly charged with promoting and facilitating terrorist activity on the Telegram platform by failing to respond to law enforcement takedown requests.
The criminal probe was revealed in a long piece published on Tuesday by the official newspaper of the Russian government, the Rossiyskaya Gazeta.
Russian officials have accused Durov of choosing a "path of violence and permissiveness" by not cooperating with its law enforcement agencies.
They say Telegram has ignored more than 153,000 requests to remove illegal content sent by the Roskomnadzor and other agencies. Over 33,000 of them were allegedly related to sabotage, terrorism and extremist activity.
Officials claim the platform is teeming with Ukrainian intelligence operatives, who buy leaked or hacked data on Telegram shops to enhance their operations and recruit or extort Russians into acts against the state.
Ukrainian intelligence has allegedly tracked the relatives of military personnel, their travel routes, and daily routines. The FSB claims it received more than 700 reports of threats made via Telegram against Russian military family members.
The FSB also claims it discovered and prevented 475 terrorist attacks being planned on the platform, including 61 attacks on schools.
The publication says Durov and Telegram shared the phone numbers and IP addresses of Russian citizens with foreign governments, data that was allegedly used to launch attacks on civilian targets in Russia. Is it true? Highly unlikely. But the newspaper also called Durov a man "under foreign influence" and accused him of sacrificing the safety of Russian citizens for to Western interests.
It feels like every aspect of Russian life now is viewed by the authorities through the lens of the war, whether something is good or bad or legal or illegal is all based on that calculus.
— ⸻realhackhistory.org (@bsky.realhackhistory.org) 2026-02-24T08:51:51.293Z
Russia has been slowly turning on its most successful tech entrepreneur since last year, a crackdown that just happened to coincide with the launch of MAX, a state-controlled messenger and all-in-one app.
Since MAX's rollout, Russia began blocking Telegram voice and video calls since August, and began throttling the main Telegram instant messenger earlier this month, with the Roskomnadzor allegedly forcing a traffic degradation of around 55%.
Shortly after the most recent block came into place, Durov took several days, but eventually put out a statement denouncing Russia's decision to block his app. Rossiyskaya Gazeta hints that those "provocative statements" didn't go well with Russian officials, and he was called out in their hit piece.
Durov called the government's decision as a restriction of its citizens' freedom, but the government's newspaper says "the measures taken are not an attack on freedom, as Western puppeteers are trying to imagine" but Russia's legitimate right to protect its citizens and digital sovereignty (ahh, that word again).
They go as far as to put Durov in the same category as Mikhail Khodorkovsky, Alexei Navalny, and his Anti-Corruption Foundation and that together with the rest, they have "the blood of Donbass children on their hands." [major eye roll]
Sure, Russia wants to block Telegram, and they have legitimate reasons to do so, but we could have done with the over-dramatization here. This paragraph would have probably been enough to justify the ban without all the "think of the children" misplaced rhetoric.
"In conditions of total hybrid warfare, they become strategic weapons. Ignoring laws, refusing dialogue and actually aiding criminals puts Telegram outside the legal framework of Russia."
In fact, this is the same reason Durov was arrested in France in August 2025, when French authorities had enough of Telegram skirting law enforcement requests and detained the CEO on criminal charges. Months later, Durov and Telegram folded like an accordion and started moderating the platform, which had indeed become a safe haven for all sorts of criminal activity.
But in fairness, this crackdown might also be driven by the Kremlin's desire to push Telegram's massive Russian userbase to its MAX messenger, who is still around the 3-6 million active users mark, depending on different sources. A full Telegram block would without a doubt raise MAX adoption rates.
There are few things that Russian & Ukrainian security services agree on. But both detest Telegram basically for the same reason: it's being used by the adversary Russia considers blocking Telegram & Ukraine is not there yet RU rg.ru/2026/02/24/t... UA interfax.com.ua/news/general...
— Oleg Shakirov (@shakirov2036.bsky.social) 2026-02-24T07:17:44.837Z
It seems Durov's public efforts to shame Western police agencies for meddling in Telegram's affairs have not earned him a pass from Russian officials. My snark aside, it's sad to witness the death of another RuNet blogosphere. Shades of LiveJournal's demise flash before my eyes...
— Kevin Rothrock (@kevinrothrock.me) 2026-02-24T06:40:22.057Z
Risky Business Podcasts
The main Risky Business podcast is now on YouTube with video versions of our recent episodes. Below is our latest weekly show with Pat and Adam at the helm!
Breaches, hacks, and security incidents
Teenagers are behind the Ttareungyi hack: South Korean police have arrested two high-school students for hacking the Seoul public bike sharing service. The two allegedly breached Ttareungyi's servers and stole the data of 4.62 million users. The hack took place in June 2024 but was only discovered this year. The two suspects met on Telegram and learned about cybersecurity while they executed the hack. [The Chosun Daily] [h/t Cha Minseok]
Marquis sues Sonicwall over breach: US fintech company Marquis has sued firewall maker SonicWall over a security breach last December. Marquis claims SonicWall failed to secure its cloud servers where firewall configs were backed up. Hackers stole firewall config files from SonicWall's servers, which they later used to breach Marquis. SonicWall confirmed the breach of its cloud service last September and blamed the incident on a state-sponsored threat actor. [TechCrunch]
UAE says it blocked mega attack: In a press release over the weekend, the UAE's cybersecurity agency says it blocked a major cyberattack that targeted its critical infrastructure sectors, including attempts to deploy ransomware. It's a pretty generic statement, and it's quite unclear what happened. [GulfNews]
Odido hack linked to ShinyHunters: The ShinyHunters hacking group has taken credit for the hack of Dutch ISP Odido. The hackers issued the company a final warning this week to pay a ransom demand or they will leak customer data. Odido previously confirmed hackers stole the data of 6.2 million customers. [Tweakers]
Odido breach compensation: Also in Odido news, the company is giving customers affected by its data breach an F-Secure voucher to use the antivirus for free for two years. This is genuinely a more expensive payout than the $5-$10 Americans typically get for their breaches.
Air Côte d’Ivoire ransomware attack: The Ivory Coast's flag carrier Air Côte d'Ivoire had confirmed a ransomware attack that crippled its IT systems earlier this month. [The Record]
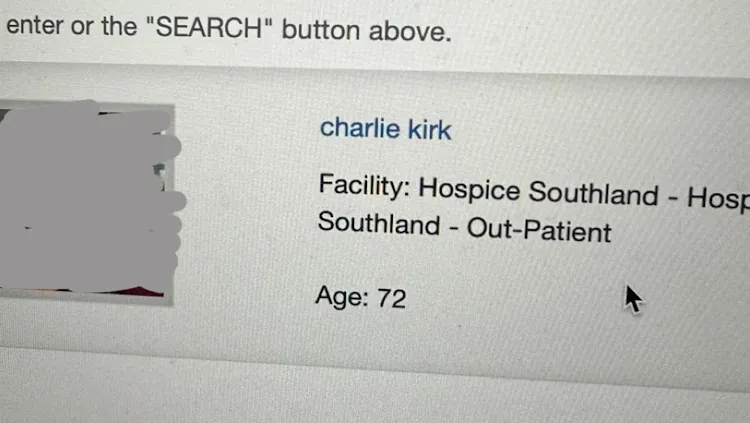
MediMap hacked and defaced: Hackers have gained access to MediMap, a New Zealand healthcare app used in disability and hospice care. The app took down its website on Sunday after discovering the hack. The intruders allegedly renamed some patients to Charlie Kirk and changed their status to deceased. [RNZ // Stuff] [h/t DataBreaches.net]
IoTeX crypto-heist: Hackers have stolen $4.4 million worth of crypto-assets from the IoTeX platform. The attackers stole the funds after compromising a private key for one of the platform's integrations. The company has offered to let the hackers keep 10% as a bug bounty if they return the rest of the funds. [CoinDesk]
YieldBlox crypto-heist: A threat actor has exploited the YieldBlox lending platform to steal $10 million worth of crypto-assets. The hackers manipulated prices on the Stellar blockchain integration to extract higher assets than they put in. According to the platform, the hackers increased token prices by 100 on tokens that didn't have any activity before their attack. [Protos]
WLFI discloses attempted attack: Hackers have allegedly breached Twitter accounts of several cofounders at the Trump family's World Liberty Financial crypto fund to spread rumors about the USD1 token. The organization called the incident a coordinated attack that also involved "paid influencers." [Decrypt]
Step Finance shuts down after last month's hack: Step Finance has ceased operations after losing $30 million in a hack at the end of last month. The company says it failed to secure new funds or an acquisition following the security breach. Two other platforms owned by the same company, SolanaFloor, and Remora Markets, are also shutting down.

General tech and privacy
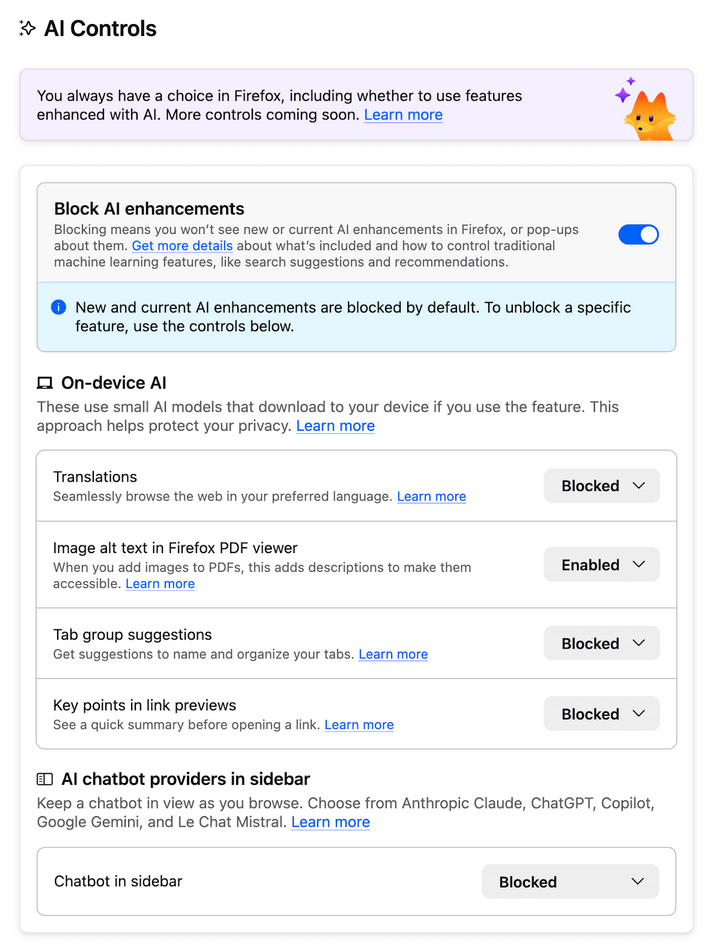
Firefox 148: Mozilla has released Firefox 148. New features and security fixes are included. The biggest feature in this release is the browser's new controls for controlling the AI component. The browser also ships with the Sanitizer API, which allows for easier HTML data manipulation without exposing users to XSS attacks.
DPAs warn about genAI deepfake threat: Data protection agencies from 61 countries and regions have issued a joint statement warning about the huge risks that come from genAI tools and their ability to create unconsensual and realistic images and videos.
News Release: OIPC BC joins international data protection authorities in statement on privacy risks of AI-generated imagery Read the full news release: www.oipc.bc.ca/documents/ne... Read the international Joint Statement: www.oipc.bc.ca/media/17985/...
— Office of the Information and Privacy Commissioner for BC (@oipcbc.bsky.social) 2026-02-23T21:34:27.781Z
Tech colonoscopy: A privacy expert has gone through the process of verifying on LinkedIn, a process that extracted every little piece of personal information about them, from passport photos to real names and real ID numbers. The culprit—a US-based and Thiel-backed startup named Persona, which is also the age verification provider at Discord and is getting broadly adopted by a bunch of other services too. The good news is that after the massive backlash over Persona's shady data handling and a user exodus to rival platforms, Discord has now dropped Persona.
Annoying Romanian ISPs are annoying: A public petition has been filed in Romania against the country's internet service providers that, contrary to EU legislation, are locking users out of their routers and not allowing them to inspect the firmware, see what processes are running on them, or even if they are up to date.
UK fines porn company: The UK's communications watchdog has fined porn company 8579 LLC £1.35 million ($1.8 million) for failing to roll out age checks for British visitors.
UK fines Reddit: The UK's privacy watchdog has fined Reddit £14.47 million ($19.56 million) for collecting the data of children under the age of 13.
Anthropic accuses three rivals of stealing: Anthropic has accused three Chinese AI companies of scraping its Claude model in a so-called AI distillation attack. DeepSeek, Moonshot AI, and MiniMax allegedly set up more than 24,000 Claude accounts. The companies used the accounts to run millions of queries and train their models on Claude's output.
The *audacity* it takes the big model trainers to complain that somebody else scraped their work and is capturing value from it without permission. The sheer chutzpah. The staggering lack of self-awareness. It's gobsmacking.
— Laurie Voss (@seldo.com) 2026-02-23T21:49:12.855Z
Government, politics, and policy
German court rejects Pegasus defamation lawsuit: A German court has dismissed a lawsuit filed by the government of Morocco against newspaper ZEIT for an article exposing its use of the Pegasus spyware. [ZEIT]
Montana has a cyber warfare officer: The US state of Montana has appointed its first cyber warfare officer as part of the state's National Guard. [KTVH]
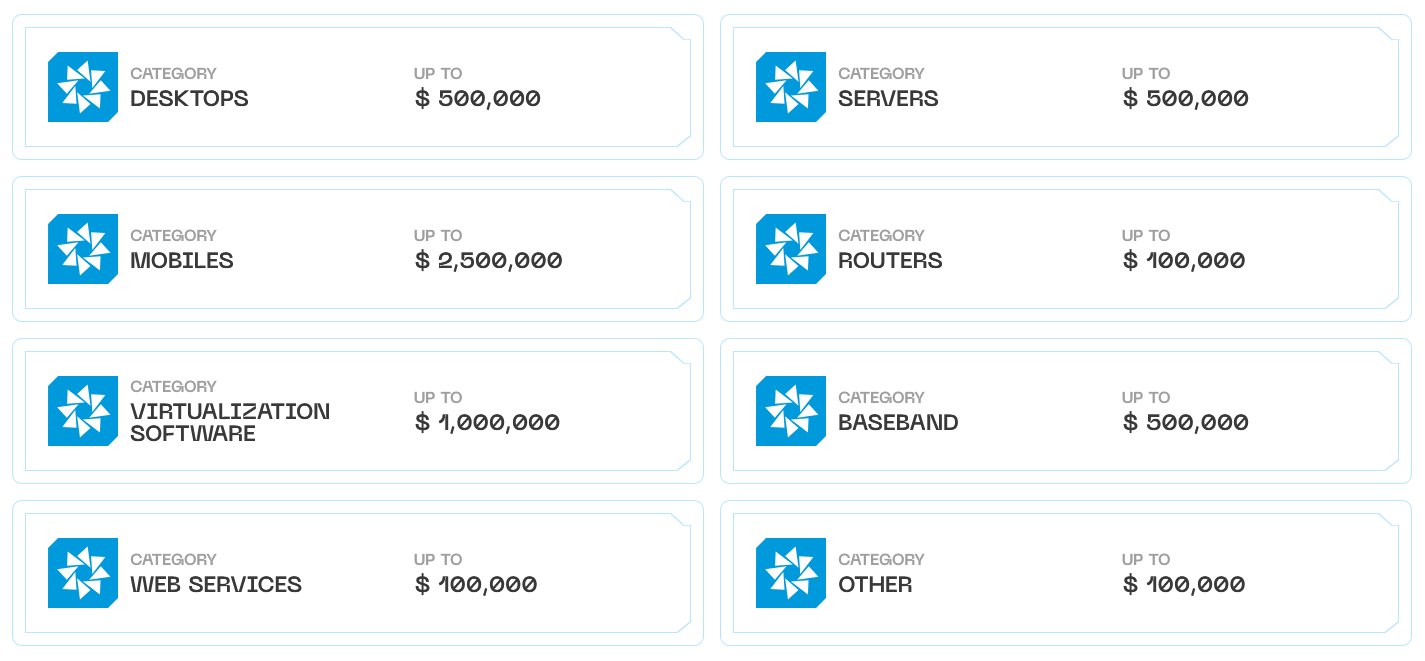
US Treasury sanctions Russian exploit broker: The US Treasury has sanctioned individuals and entities associated with Russian exploit broker Operation Zero. The company is a known supplier of exploits and zero-days for the Russian government. Operation Zero is also the company that acquired exploits stolen from L3Harris Trenchant by one of its former executives. Sanctions were levied against Operation Zero's parent company, an UAE affiliate, Operation Zero CEO Sergey Zelenyuk, his assistant, and two business partners. The Treasury says the two are members of the Trickbot malware group and they also run their own exploit brokerage company in the UAE and Uzbekistan. This company was also sanctioned.
Sponsor section
In this Risky Business sponsor interview, Casey Ellis and Feross Aboukhadijeh discuss how AI is affecting open source, chat about a few attacks the company has seen in the wild and introduce Socket’s answer to the smouldering trashfire: Socket Firewall.
Arrests, cybercrime, and threat intel
Trenchant exec sentenced to 87 months: The L3 Harris executive who sold his employer’s exploits to a Russian broker has been sentenced to 87 months in prison. Australian Peter Williams pleaded guilty to theft of trade secrets last year. He was sentenced on Tuesday. A hearing to decide whether Williams will need to pay restitution to Trenchant is scheduled for May. His former employer is seeking $35 million. [CyberScoop]
Anonymous Fénix members arrested in Spain: Spanish authorities have arrested four members of the Anonymous Fénix hacktivist group. Two leaders were arrested in May of last year and another two last week. The four were charged with launching DDoS attacks against government sites, political parties, and public institutions.

Malicious NuGet packages: Four malicious .NET packages have been available on the official NuGet repository for more than a year and a half. The packages work together to deploy a proxy on a developer system, then steal ASP.NET identity data, and backdoor any locally developed apps. According to Socket Security, the packages were downloaded more than 4,500 times.
Diesel Vortex profile: A Russian-Armenian threat actor is behind a new phishing platform specifically designed to target the freight and logistics sector. The attacker has stolen more than 1,600 credentials from companies across the US and EU using the new Global Profit phishing kit. Security researchers at Ctrl-Alt-Intel and Have I Been Squatted have found overlaps between the phishing kit's infrastructure and several logistics companies in Armenia.
Maritime sector sees spike in cyberattacks: South Korean maritime security firm Cytur says cyberattacks targeting the sector have doubled over the past year, and have also increased in sophistication as well. The spike has been driven by the broad adoption of ship satellite comms, and some hacks are regularly going from the main IT network to OT systems such as ballast water control and engine monitoring. [Ship Management International]
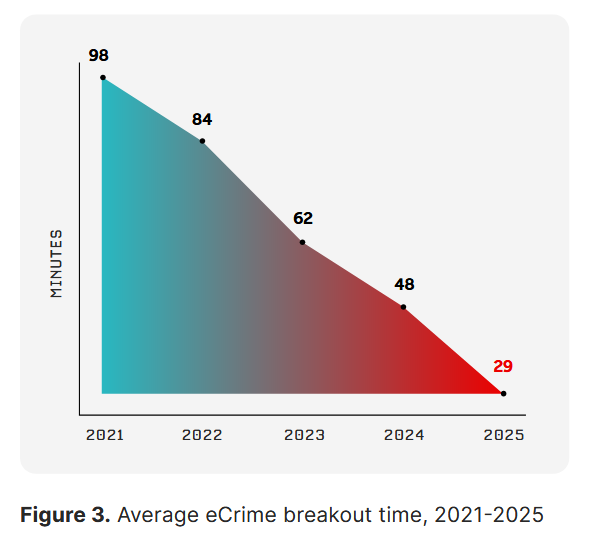
Breakout time down to 29 minutes: Cybercrime groups are moving laterally and compromising entire networks about 29 minutes after the initial breach. Breakout times have hit an all-time low last year, down from 98 minutes recorded in 2021. CrowdStrike says the fastest breakout time last year was 27 seconds. Some of the high tier groups also achieved times of just a few minutes.
Malware technical reports
ActiveMQ to Lockbit: A new DFIR Report looks at how threat actors exploited an Apache ActiveMQ vulnerability from 2023 to drop the LockBit ransomware.
"Despite being evicted after the initial intrusion, they successfully breached the same server on a second occasion 18 days later."
Vshell: Censys has published a pretty in-depth analysis of Vshell, a post-exploitation toolkit from the Chinese market that has been spotted in several recent Chinese APT campaigns.
Moonrise RAT: ANY.RUN has documented a rather stealthy new RAT named Moonrise.
Tycoon 2FA: Point Wild has a breakdown of Tycoon 2FA, today's most active and advanced phishing kit.
Sponsor section
In this Soap Box edition of the Risky Business podcast Patrick Gray chats with Socket founder Feross Aboukhadijeh about how to measure the reachability of vulnerabilities in applications. It's great to know there's a CVE in a library you're using, but it's even better if you can say whether or not that vulnerability actually impacts your application.
APTs, cyber-espionage, and info-ops
Lazarus has joined the Medusa RaaS: North Korean hackers have signed up for the Medusa Ransomware-as-a-Service and are using its tools to attack US healthcare organizations. This is the third ransomware Lazarus operators have used in attacks against US hospitals. They also previously used the Maui and Play ransomware families.
More Contagious Interview stuff: There's been a flood of reports on malicious files used by North Korean hackers to target job seekers. These files are disguised as interview tests but are laced with malware. Once an applicant opens and runs the files, they get infected. The hackers then use the access to the applicant's computer to target their current or future employers. The latest report on this campaign comes from Microsoft and covers Next.js projects shared with individuals looking for developer jobs.
White Lock ransomware linked to Iran: Check Point has linked the WhiteLock ransomware to Iranian state-sponsored groups Void Manticore (Handala Hack) and Cotton Sandstorm.
MuddyWater APT chronology: South Korean security firm Genians has published a chronology of spear-phishing campaigns conducted by the Iranian MuddyWater APT over the past half-decade.
Russian cyberattacks used for missile strikes in Ukraine: Ukraine says data stolen in Russian cyberattacks on its energy grid are increasingly being used to guide missile strikes. According to Ukraine's cybersecurity agency, attackers have stopped trying to wipe power grids. Instead, they appear more focused on mapping facilities, tracking repair crews, and seeing how fast facilities recover after a strike. [The Record]
APT28 behind recent MSHTML zero-day: Russian state-sponsored hackers are exploiting a Microsoft browser zero-day in attacks in the wild. Akamai has linked the attacks to APT28, a cyber unit of Russia's military intelligence services. Tracked as CVE-2026-21513, the zero-day can allow attackers to bypass several browser security boundaries and run malicious code outside its sandbox. Microsoft patched the bug earlier this month.
"This payload involves a specially crafted Windows Shortcut (.lnk) that embeds an HTML file immediately after the standard LNK structure. The exploit leverages nested iframes and multiple DOM contexts to manipulate trust boundaries. This technique allows the attacker to bypass Mark of the Web (MotW) and Internet Explorer Enhanced Security Configuration (IE ESC), effectively downgrading the security context before triggering the vulnerable navigation flow. Ultimately, this allows attacker-controlled content to reach a code path that invokes ShellExecuteExW, leading to execution outside of the browser sandbox."
Mercenary Akula (UAC-0050): BlueVoyant's security team looks at a targeted social engineering campaign against European financial institutions involved in supporting Ukraine. BlueVoyant linked the campaign to Mercenary Akula, a group also known as UAC-0050 and the DaVinci Group. Per BlueVoyant, the group has ties to Russian law enforcement, is primarily financially motivated, but has also conducted cyber espionage and psychological operations.
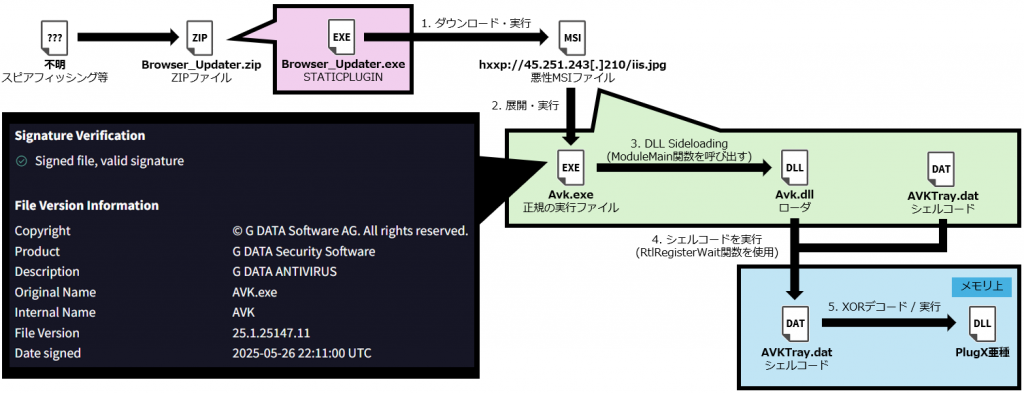
New UNC6384 activity: The security team of Japanese telco IIJ has spotted new activity from Chinese APT group UNC6384. The attacks follow a known modus operandi of using the STATICPLUGIN downloader to deliver updated versions of PlugX.
Vulnerabilities, security research, and bug bounty
A tale as old as time: Cloud software engineer Yannick Dixken tells us how he got legal threats after he reported a vulnerability in the online portal of a diving and sports insurer last year.
FIDO security: A Google security audit found that the FIDO Alliance's support for generic JSON in the Hybrid protocol "doesn't compromise the security of FIDO Hybrid flows."
Vulnerabilities in mental health apps: Security researchers at Oversecured say they found vulnerabilities in mental health apps, including some in AI-based apps. The company is not disclosing the names of the apps since many issues are still unpatched.
DoE patches bug: The US Department of Energy has patched a vulnerability in its critical minerals portal that allowed remote attackers to register accounts on the platform. [NextGov]
Akamai patches HTTP request smuggling bug: American CDN provider Akamai patched an HTTP request smuggling vulnerability in its platform (CVE-2026-26365).
Infosec industry
Threat/trend reports: Check Point, CrowdStrike, Cytur, GreyNoise, HP Wolf Security, Intrinsec, N-able, Sophos, and Upstream Security have recently published reports and summaries covering various threats and infosec industry trends.
New tool—Claude Code Security: Anthropic launched last week Claude Code Security, a Claude AI feature to scan codebases for vulnerabilities and suggest fixes.
New tool—Azul: The ASD has released Azul, an open‑source malware analysis tool designed for large-scale malware analysis.
Hackfest videos: Talks from the Hackfest 2025 security conference, which took place in October, are available on YouTube.
Risky Business podcasts
In this edition of Between Two Nerds, Tom Uren and The Grugq talk about how 'professional' Five Eyes cyber espionage agencies like NSA will use AI. These agencies place a premium on stealth and won't yolo AI.
In this edition of Seriously Risky Business, Tom Uren and Amberleigh Jack talk about a groundswell of calls from officials that European countries need to build cyber capabilities to strike back against adversaries. They also talk about 'distillation attacks' the way that AI developers can steal the secret sauce of advanced models just by asking questions.




