Risky Bulletin: Meta disrupts Mexican cartels
In other news: Instagram will disable support for E2EE DMs; new Chinese APT targets militaries across SE Asia; supply chain attack at AppsFlyer.

This newsletter is brought to you by Sublime Security. You can subscribe to an audio version of this newsletter as a podcast by searching for "Risky Business" in your podcatcher or subscribing via this RSS feed.
Meta's security team has suspended thousands of accounts last year that were tied to Mexican and other Latin American drug cartels.
The Facebook and Instagram accounts were used to recruit youth for drug trafficking and drug dealing, to advertise drugs, and to organize violence and extortion operations.
Meta says it used AI to detect the coded language typically used by cartels and also to identify photos of drugs posted on its platforms. Human reviewers also confirmed the findings before accounts were removed.
Most of the suspended accounts and groups were active in Mexico, but some were also located in the US.
A specific category of accounts appear to have been set up mainly for recruitment purposes. These accounts glorified their own criminal activities and lifestyle in the hopes of recruiting vulnerable youth to join their ranks.
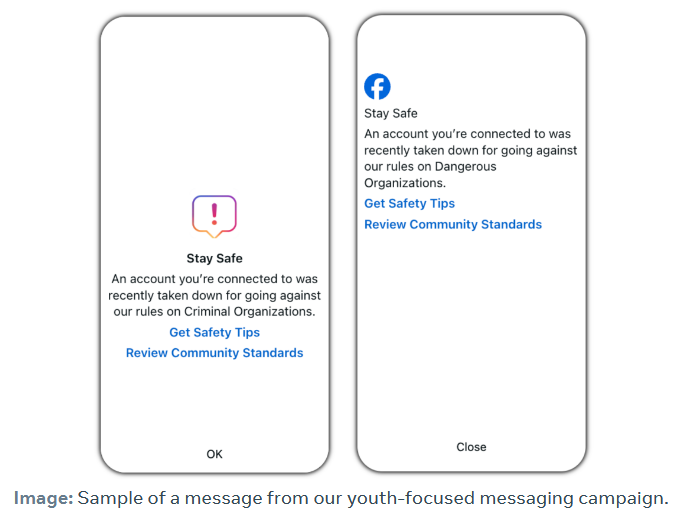
To combat these groups, Meta says it prompted youth in Mexico last year with a special message when they interact with the accounts, which later led to "a demonstrable increase in account deactivation and unfriending behavior." This alert was expanded towards the end of last year to other cartel hotbeds like Brazil, Colombia, and Haiti.
Other groups and accounts used Facebook and Instagram for day-to-day operations. They posted photos of their product, they recruited dealers and mules, or posted threats and extortions.
Some of these accounts appeared to have been connected to the trafficking into the US of drugs such as fentanyl, cocaine, and crystal meth. Other accounts were also linked to ATM fraud.
The cartel takedown effort was included in Meta's H1 2026 Adversarial Threat Report [PDF], where it was overshadowed by two other operations. In the first, Meta took down Iranian accounts involved in influence operations against the US, all while the US is bombing Iran.
The second was a major crackdown against cyber scam compounds, with Meta playing an active role in the arrest of one group in Thailand and the company taking down almost 11 million accounts linked to cyber scam operations last year.
Risky Business Podcasts
We launched a new podcast series called Risky Business Features. In this episode James Wilson takes a (ridiculously) deep dive into the Coruna exploit kit.
Breaches, hacks, and security incidents
Former BND official falls for Signal phishing: A former high-ranking official in Germany's intelligence service BND and NATO fell victim to a Signal spearphishing attack. Arndt Freytag von Loringhoven told reporters he was the target of an attack that demanded his Signal PIN code, which he supplied. According to Der Spiegel, other high-ranking German politicians fell for the same attack, while other intelligence officials were also targeted. Dutch intelligence agencies said last week that Russian state-sponsored hackers were behind a global campaign to hack Signal and WhatsApp accounts.
Leak of Swedish e-government code: A threat actor has leaked the source code of Sweden's e-government portal. The hacker, named ByteToBreach, claims to have stolen the code from a government IT contractor. The company is the Swedish branch of global IT giant CGI Group. It confirmed a breach last Thursday. The hacker published the code to prove they stole the data of millions of Swedish citizens, along with electronic signing documents. [Dark Web Informer // Threat Landscape // Aftonbladet]
Free parking in Perm: A DDoS attack has crashed the public parking meters in the city of Perm, Russia. Authorities have allowed drivers to park for free until the system is recovered.
Starbucks employee breach: A hacker stole the details of almost 900 Starbucks employees.
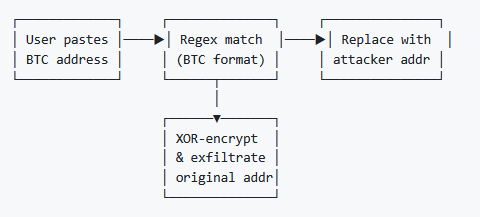
AppsFlyer supply chain attack: A threat actor has compromised the AppsFlyer analytics service to deliver a cryptocurrency address hijacker. The code was deployed in the company's mobile and web-based SDK. The malware waited for copy-paste operations, intercepted cryptocurrency addresses, and replaced them with one controlled by attackers. The hijacker targeted Bitcoin, Ethereum, Solana, Ripple, and TRON currencies. [Profero]
General tech and privacy
Instagram to disable encrypted DMs: Instagram will disable support for end-to-end encrypted private messages on May 6. The social network has advised users to download any sensitive media from those chats before support is disabled. Instagram didn't give a reason for its decision. Earlier this month, TikTok said it would not support encrypted DMs because it couldn't scan messages for abusive content.
Adobe settles hidden fees case: Adobe has agreed to pay a $75 million fine to settle a DOJ investigation for hiding a hidden termination fee for US customers. The company will also provide free services worth the same amount to all affected customers.
Activision goes after CoD leakers: Game studio Activision has sent cease and desist letters to dozens of Call of Duty leakers, threatening lawsuits if they continue to leak content from its upcoming Call of Duty Modern Warfare 4 game. All of them have published public tweets that they will comply with the Activision request.[1, 2, 3, 4, 5] [Dexerto]
Chrome comes to Linux Arm: Google will launch a Chrome version for Arm64 Linux devices in the second quarter of the year. Chrome has been on macOS Arm since 2020 and Windows Arm since 2024.
EU alternative for Office: Office EU, an European company, has launched Office.eu, an EU-based alternative to Microsoft Office and Google Workspace, built on open-source technology and running on European server infrastructure.
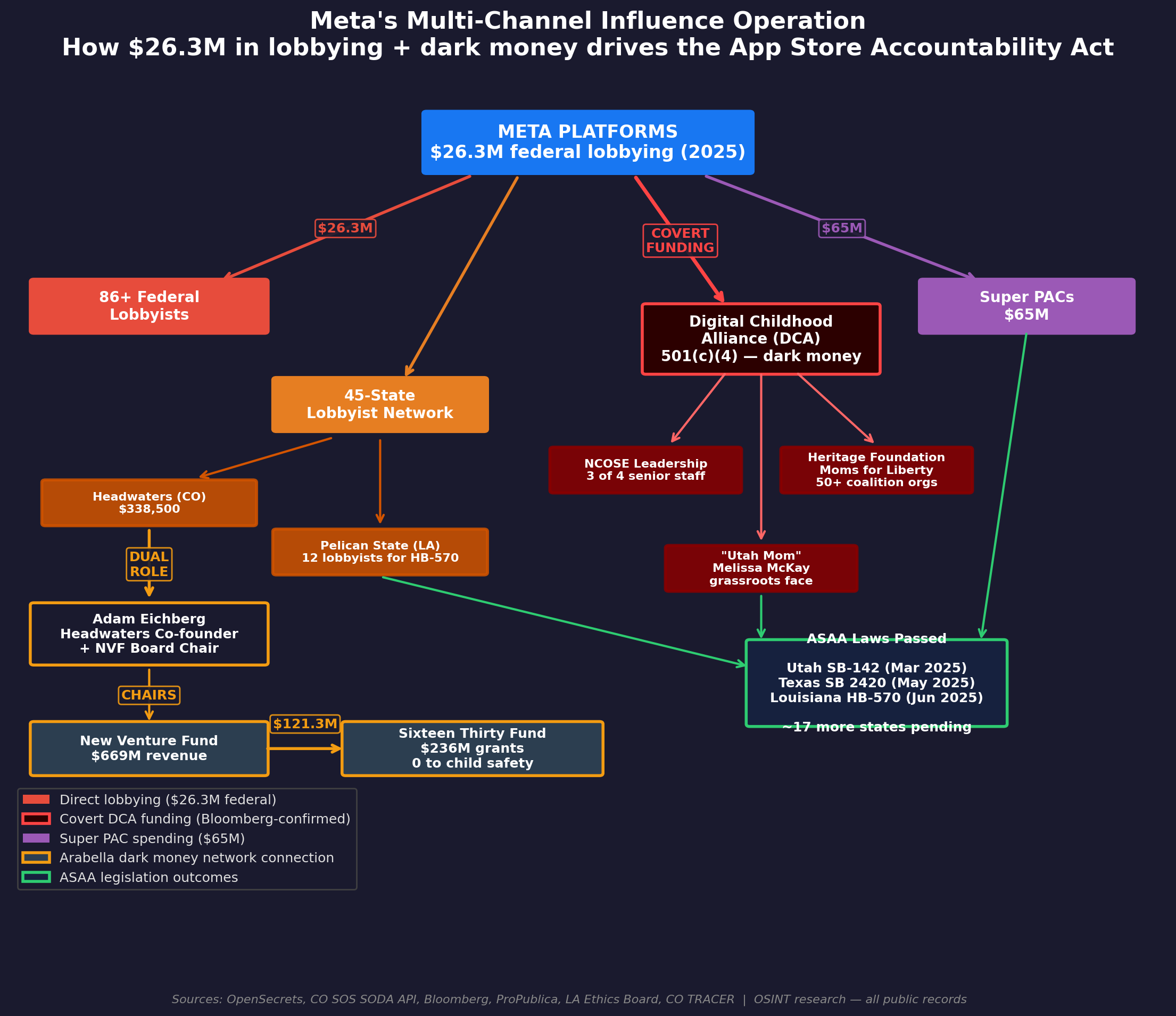
Meta linked to age-verification legal push: After a California law wants Linux to perform age-verification checks on all local user accounts, the Linux community got super pissed off about it and traced all the lobby efforts to push age verification laws across the globe to Meta, which was later joined by a bunch of other social networks. These lobby efforts are focused on moving age-verification checks from the social network's side to app stores and operating systems—hence why other social networks joined Meta's attempts.
Government, politics, and policy
UK pushes tech platforms for better age checks: The UK government is pushing tech companies to implement better age checks on their platforms. The UK's privacy and communications watchdogs want companies to crack down on weak age verification methods that let kids declare an adult age without proof. The ICO sent letters to TikTok, Snapchat, Facebook, Instagram, YouTube, and X. Ofcom also asked Roblox to review and toughen its age check system.
FISA searches increase: The number of FBI FISA searches grew by a third last year, according to US officials. The FBI performed almost 7,400 searches for American citizens' data against an NSA database of internet traffic. Despite the spike, the number is minuscule compared to the almost 3 million FBI FISA searches reported in 2021. [The Record]
FBI searches of U.S. person data collected using FISA 702 authority rose some 35% in 2025, according to an FBI letter to Congress that was obtained by Nextgov/FCW. Confirming earlier coverage from @martinmatishak.bsky.social -> www.nextgov.com/cybersecurit...
— David DiMolfetta (@ddimolfetta.bsky.social) 2026-03-12T22:23:09.505Z
Intellexa-v-Athens spat: After the founder of spyware vendor Intellexa was sentenced to 126 years in prison, Tal Dilian told the media his company sells exclusively to governments, hinting that the Greek government was responsible for hacks of its opposition party and not him and his employees. We love drama! [OCCRP]
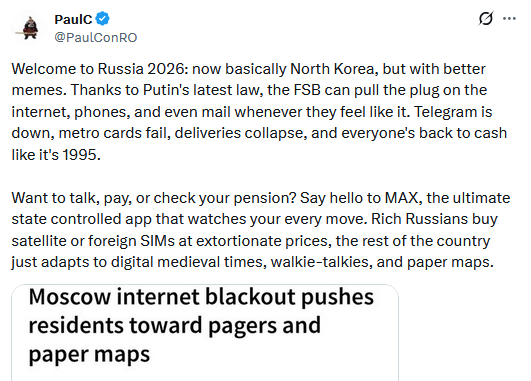
Moscow enters its second week without mobile internet: Moscow residents have entered their second week without mobile internet. Mobile internet access has been cut off since March 6 without any explanation. The outage began two weeks after the FSB got the power to cut internet access anywhere at will in the country. Russian news outlets are reporting that some mobile operators are restoring internet access but are only allowing access to a small number of government-approved sites. [Kommersant // Forbes Russia]
Sponsor section
In this Risky Business sponsor interview, Catalin Cimpanu talks with Alex Orleans, Head of Threat Intelligence at Sublime Security, about the increase in email attacks leveraging Zoom invites and other video conferencing tools.
Arrests, cybercrime, and threat intel
New Interpol crackdown: Interpol has detained 94 individuals in a global operation against cybercrime organizations. The suspects were involved in phishing, ransomware, and online scam operations. The crackdown also seized 33,000 phishing sites and 45,000 IP addresses used to host malicious sites. The arrests were part of Interpol's Operation Synergia III.
British man charged with "cybercrimes": A British man has been charged under cybercrime laws in Dubai for publishing videos of Iranian missile strikes on social media. Local laws prohibit the publishing of content related to national security or that may cause panic. The suspect was identified as a 60-year-old British tourist. He faces at least two years in prison and a fine of up to $54,000. [CNN]
Grandmother put in jail after AI mistake: A Tennessee grandmother spent six months in jail after a police AI system misidentified her in a bank fraud case. Angela Lipps says she was put in jail even if she never traveled to North Dakota, where the crime was committed. She was charged solely based on a facial recognition match, even if the person in the video didn't look close to her age of 60. [Grand Forks Herald]
Scam software broker goes on trial: The trial of an Israeli citizen whose company created software for cyber scam operations has begun in Germany. [OCCRP]
Inside a Cambodian scam compound: Bloomberg published a deep dive into a Cambodian scam compound named O Smach that apparently had studios for video calls with victims decked out to look like police stations from China, India, and Indonesia. This included everything from uniforms, insignia, documents, and so on. This is not unique to this particular compound, as I've seen reports on this exact same thing in other compounds too.
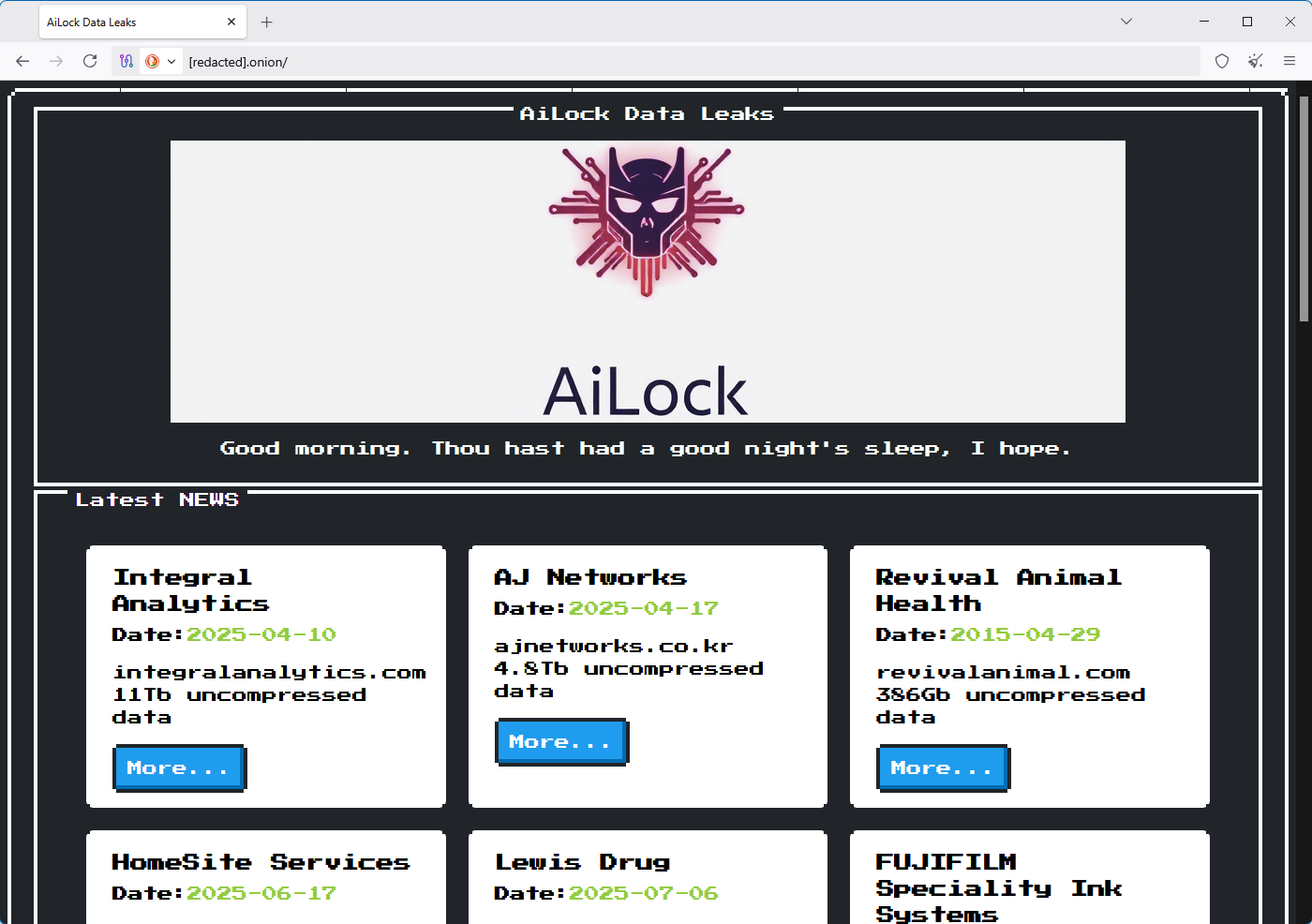
New AiLock ransomware group: A new ransomware group started leaking victims this month. Named AiLock, the group claims to have already breached at least 12 companies. One of them is apparently England's field/grass hockey federation.
New SilverFox TTPs: Knownsec has published a report with new techniques used by SilverFox, the fin threat actor targeting Chinese users.
FBI looking at Steam malware: The FBI is looking for information from victims about Steam malware. The Bureau asked victims who downloaded malicious games from Steam to contact its agents. The number of malicious games uploaded on Steam has grown in recent years, with most being infected with infostealer.
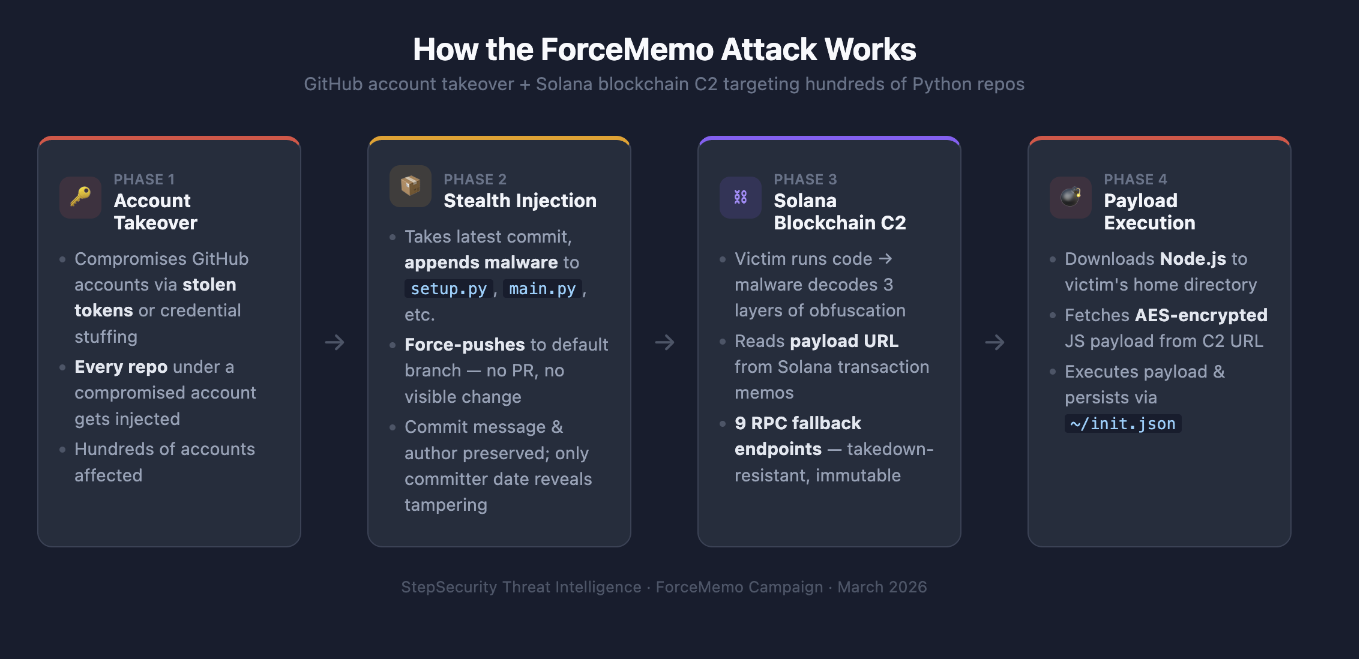
ForcedMemo campaign hits GitHub: A threat actor has breached hundreds of GitHub accounts to inject malicious code in Python projects. The malicious code appears to be a crypto-wallet stealer. The hacks have been taking place since March 8. Step Security says the attackers are using Github credentials previously stolen by the GlassWorm self-replicating worm that hit the VSCode ecosystem last year. The campaign's infrastructure also uses old GlassWorm infrastructure.
BQTlock goes free: The operators of the BQTlock ransomware platform said they will provide access to their encrypter for free for anyone who targets Israeli organizations.
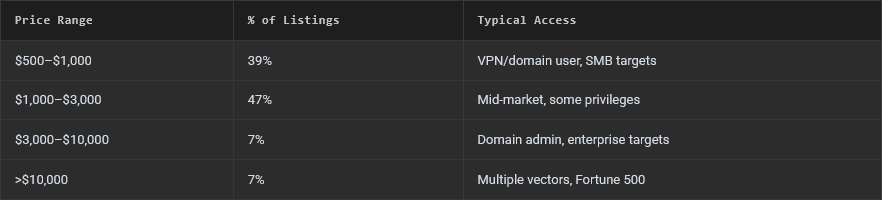
IAB market is now very affordable: The initial access broker market saw a dramatic shift toward affordability last year. The vast majority of hacked networks had prices of under $3,000, according to Abstract Security. Valid accounts without MFA was the most common initial access vector.
Malware technical reports
Phexia Stealer: A German security engineer has spotted a campaign targeting macOS users with the Phexia Stealer.
ACRStealer: G DATA team looks at a new version of the ACRStealer.
MIMICRAT: Stormshield looks at a new C++-based RAT named MIMICRAT that is being delivered via ClickFix campaigns. This was also spotted by Elastic a while back.
GlassWorm returns again: Socket has spotted the GlassWorm self-replicating worm inside 72 new OpenVSX extensions since the end of January, confirming that the malware that appeared last year is still going strong despite efforts to limit its reach by Eclipse Foundation admins. Codeberg has also spotted the same group too.
Slopoly: IBM's X-Force says a threat actor tracked as Hive0163 has used an AI-generated backdoor named Slopoly during ransomware attacks this year.
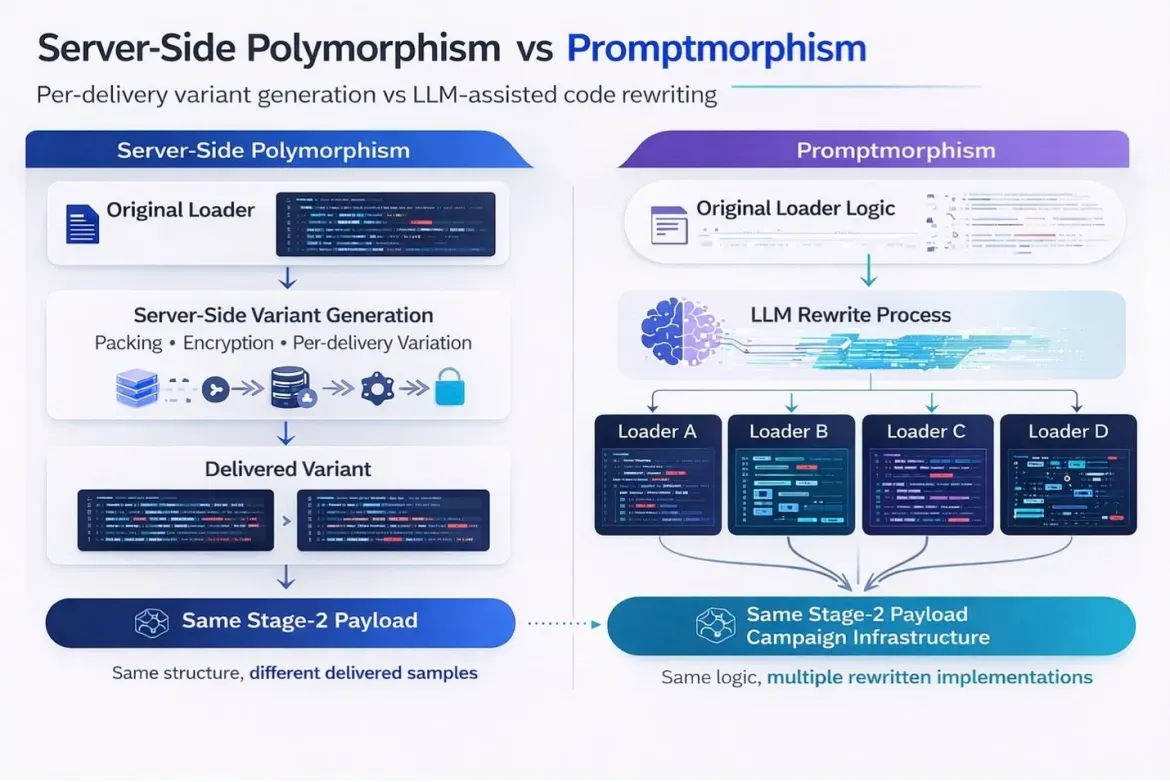
Promptmorphism: Gen Digital researchers describe promptmorphism, a new twist on polymorphism, where threat actors use AI tools to rapidly generate new versions of their malware.
Sponsor section
In this sponsored product demo, Sublime Security co-founder and CEO Josh Kamdjou joins Risky Business podcast host Patrick Gray to show off the company's email security platform, including its latest agentic AI bells and whistles.
APTs, cyber-espionage, and info-ops
CL-STA-1087 goes after foreign militaries: A suspected Chinese APT group has targeted Southeast Asian military organizations since 2020. The attacks focused on very specific intelligence collection. Targeted information included military capabilities, organizational structures, and collaborations with Western armed forces. Palo Alto Networks tracks the group as CL-STA-1087.
Chinese APT targets Gulf states: As it was expected, Zscaler saw a Chinese APT start targeting Gulf states as the conflict in the region intensifies.
Operation CamelClone: Seqrite published on Friday a report on Operation CamelClone, an APT campaign targeting a wide spectrum of countries using Middle East-specific themes.

FAMOUS CHOLLIMA's PylangGhost RAT: Kieran Miyamoto (KMSec) has spotted new malicious packages uploaded on npm by DPRK APT Famous Chollima. These ones were laced with one of their known RATs, known as PylangGhost.
DRILLAPP backdoor: Lab52 has discovered a new backdoor named DRILLAPP that was used in attacks against Ukrainian organizations. The backdoor is written in JavaScript, is run inside a headless Edge browser instance, and might be the work of a Russian APT group named Laundry Bear.
Hydra Saiga (Yorotrooper, ShadowSilk, Silent Lynx): A suspected Kazakhstani APT group is targeting organizations in the water infrastructure of neighboring countries. Espionage campaigns have targeted hydroelectric power plants in Kyrgyzstan, and the water ministries of Tajikistan and Uzbekistan. The campaign took place between September 2024 and March 2025. A year later, Kazakhstan announced a severe drought and water shortages after water levels dropped in the Syr Darya river, which flows through all four countries.
This is a long, very detailed analysis of a malware campaign by a Kazakhstan-aligned threat actor. But the most important bit, that says a lot about the world today, is the campaign's focus on critical water infrastructure www.vmray.com/hydra-saiga-...
— Martijn Grooten (@martijngrooten.bsky.social) 2026-03-13T11:46:37.997Z
Vulnerabilities, security research, and bug bounty
Chrome patches a zero-day, one remains unfixed: Google has released a security update to patch an actively exploited zero-day in the Chrome browser. The company's initial patch notes also included mentions of a second zero-day, although this was later removed. A fix for this second bug is still under development and is expected later this week.
Windows OOB update: Windows released an out-of-band security update on Friday for Windows 11 enterprise systems to fix an issue with the Hotpatch feature.
CrackArmor vulnerability: Nine vulnerabilities in the AppArmor Linux kernel security module can allow attackers to bypass kernel protections, escalate to root, and break container isolation. Codenamed CrackArmor, the bugs impact all AppArmor versions released since 2017. The app is a very popular kernel security module used with Ubuntu, Debian, SUSE, Kubernetes, and many other popular Linux-based products.
"This 'CrackArmor' advisory exposes a confused-deputy flaw allowing unprivileged users to manipulate security profiles via pseudo-files, bypass user-namespace restrictions, and execute arbitrary code within the kernel. These flaws facilitate local privilege escalation to root through complex interactions with tools like Sudo and Postfix, alongside denial-of-service attacks via stack exhaustion and Kernel Address Space Layout Randomization (KASLR) bypasses via out-of-bounds reads."
RegPwn vulnerability: MDSec has published a write-up on RegPwn (CVE-2026-24291), an elevation of privilege in Windows 10 and 11 that Microsoft patched this month in the Accessibility Infrastructure (ATBroker.exe) service. This seems to have been reported by both MDSec and Google Project Zero.
LnkMeMaybe vulnerability: TrustedSec has published a write-up on LnkMeMaybe (CVE-2026-25185), a vulnerability that can allow threat actors to spoof LNK files to link to unwanted items.
Veeam security update: Backup software company Veeam has released a security update to patch five vulnerabilities in its products. Three of them have CVSS scores of 9.9/10, so this should be a priority for most users.
Another MAX complaint: Here's another report that Russia's national messenger MAX might be a secret government backdoor and enables broad surveillance. There's been quite a few of those lately.
BitChat cache poisoning: BARGHEST tested Jack Dorsey's BitChat app and found a cache poisoning attack that could be used by "an adversary to inject unauthenticated messages into the mesh and have them redistributed during synchronization, enabling dos, spam, spoofed messages, or degradation of reliable message delivery" across the app's mesh network feature.
Most MCPs are insecure: A scan of 1,800 MCP servers found security issues in 66% (1196) of server instances.
AI agents suck at authorization: An audit of 30 AI agents found that 28 agents use unscoped API keys that they store in env files, meaning they can usually access everything and fail to protect those keys. Nothing is surprising about this report. Nothing about AI agents seems to have been designed with security in mind these days.
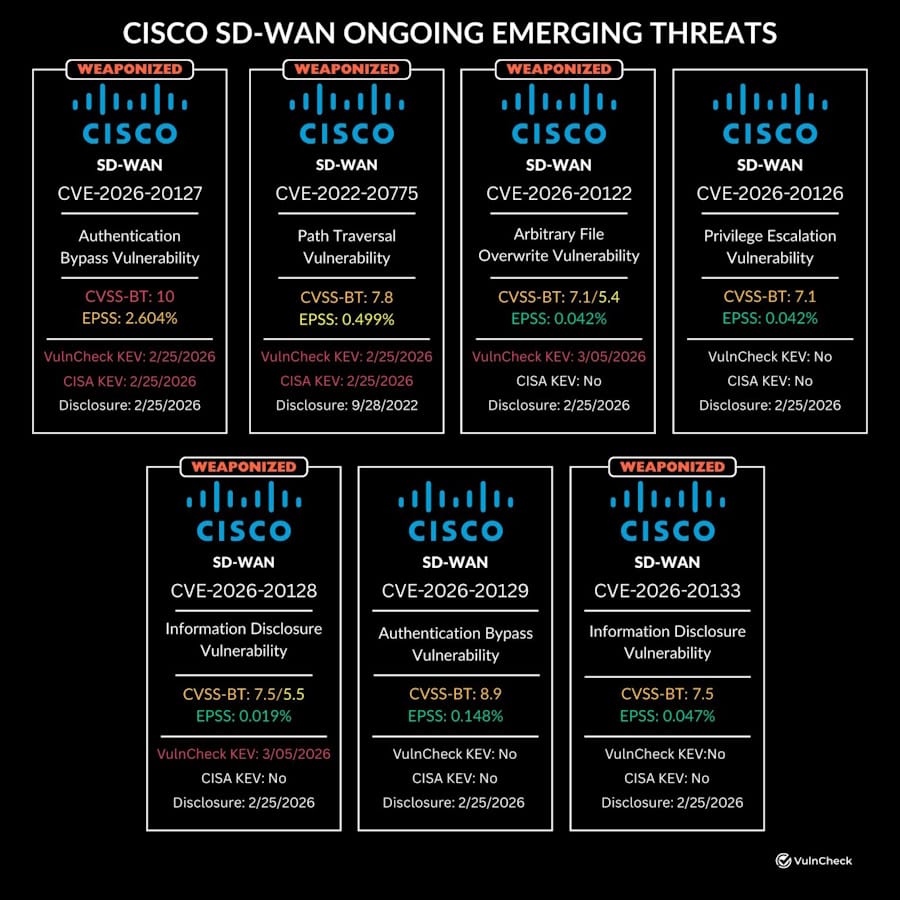
Additional Cisco SD-WAN exploitation: Security firm VulnCheck looks at the recent exploitation activity around Cisco's SD-WAN platform. Attacks have targeted three recent vulnerabilities, but VulnCheck says it expects a fourth bug (CVE-2026-20133) to come under attack pretty soon as well. [h/t Patrick Garrity]
Infosec industry
Threat/trend reports: Abstract Security, Grantex, Intruder, Mondoo, and Valimail have recently published reports and summaries covering various threats and infosec industry trends.
New tool—Pius: Security firm Praetorian has released Pius, an asset discovery tool with 23 plugins to discover a company's IP ranges, domains, subdomains, and more.
New tool—Betterleaks: Aikido Security has open-sourced Betterleaks, a secrets scanner built for speed and configurability.
New tool—IRFlow Timeline: Palo Alto Networks' Renzon C. has open-sourced IRFlow Timeline, a high-performance native macOS application for DFIR timeline analysis.
New tool—Elfina: Offensive security researcher ISSAC has released Elfina, a multi-architecture ELF loader written in Rust that is supporting x86 and x86-64 binaries.
RE//verse 2026 videos: Talks from the RE//verse 2026 security conference, which took place at the start of the month, are available on YouTube.
Risky Business podcasts
In this edition of Seriously Risky Business, Tom Uren and Amberleigh Jack talk about the newly released Trump Cyber Strategy for America. The ideas in it are fine and occasionally even game-changing, but many of its goals have been undercut by the administration's actions to date.
In this edition of Between Two Nerds, Tom Uren and The Grugq talk about why an internet shutdown won't stop US cyber operations in Iran.




