Risky Bulletin: LLMs can deanonymize internet users based on their past comments
In other news: CISA has a new acting director; breach at the French Health Ministry; Google takes down ad fraud botnet.

This newsletter is brought to you by Okta. You can subscribe to an audio version of this newsletter as a podcast by searching for "Risky Business" in your podcatcher or subscribing via this RSS feed.
A team of academics has developed large language models (LLMs) that can deanonymize internet users based on past comments or other digital clues they have left behind.
The new method works even if targets use different pseudonyms across multiple platforms. It can link real identities to hidden accounts and online activity, and vice versa.
The LLMs basically work by analyzing past activity and creating user profiles. Once enough data points are available, connections can be made between similar profiles based on shared vocabulary and other clues revealed online, such as locations, hobbies, age, and so on.
Limited tests achieved a 99% precision rate when analyzing and linking Hacker News accounts to LinkedIn profiles.
"Our results show that the practical obscurity protecting pseudonymous users online no longer holds and that threat models for online privacy need to be reconsidered."
The research team says using their LLMs outperforms classical research methods where digital footprints are examined by hand by a human operator. This enables fully automated deanonymization attacks that can work on all sorts of unstructured data at scale, while also reducing the cost of intelligence gathering work.
"Our findings have significant implications for online privacy. The average online user has long operated under an implicit threat model where they have assumed pseudonymity provides adequate protection because targeted deanonymization would require extensive effort. LLMs invalidate this assumption."
Privacy online is fundamentally at odds with intelligence getting cheaper. Anonymity on the internet has always relied on practical obscurity. We publish in hopes that people can adapt to LLMs changing this. Paper: arxiv.org/abs/2602.16800
— Daniel Paleka (@dpaleka.bsky.social) 2026-02-20T17:03:40.405496Z
And right on schedule: there goes pseudonymity on the Internet. arxiv.org/abs/2602.16800
— Matthew Green (@matthewdgreen.bsky.social) 2026-02-25T00:37:23.501Z
This was inevitable. Something everyone should be aware of. arxiv.org/abs/2602.16800
— Elliot (@1t2ls.bsky.social) 2026-02-25T17:36:10.300Z
Risky Business Podcasts
The main Risky Business podcast is now on YouTube with video versions of our recent episodes. Below is our latest weekly show with Pat and Adam at the helm!
Breaches, hacks, and security incidents
Department of Peace hacks the DHS: Hackers have breached the US Department of Homeland Security and have leaked details on ICE contracts. The data was hacked from DHS' Office of Industry Partnership. It contains details on ICE contracts with more than 6,000 companies. The files were leaked by a group calling themselves the Department of Peace.
Breach at the French Health Ministry: Hackers have stolen the personal data of 15 million French citizens from the country's Health Ministry. The incident took place last year and impacted even some top political figures. The stolen data includes patient records, doctor notes, home addresses, and phone numbers. [France24]
Dutch DJI hacked via Ivanti device: Hackers breached the Dutch Justice Department (DJI) using a recent zero-day in Ivanti's EPMM platform. According to Dutch media, the attackers went undetected for five months before the breach was discovered. The same zero-day was also used to hack the Dutch Data Protection Agency and the European Commission. Multiple Dutch government agencies are also investigating hacks, according to a letter to the Dutch Parliament. [Argos] [h/t DataBreaches.net]
Coupang income falls after breach: South Korean retailer Coupang reported a 97% drop in operating income in the fourth quarter as the company is still dealing with the aftermath of a major security breach. Operating income fell to $8 million from $312 million a year before. It also reported a net loss of $26 million, compared to $156 million in profit a year earlier. [Nikkei]
Roskomnadzor DDoS attack: Russia's internet watchdog fell victim to a DDoS attack on Friday. [United24 // Vedomosti]
"Largest cyberattack in history" claims: A report in Israeli media claims the government carried out the "largest cyberattack in history" during the country's recent joint attack with the US against Iran. The report claims the incident took down secure communication systems, news sites, and critical infrastructure. Some of the claims appear to have been confirmed by Iranian news outlets. [The Jerusalem Post]

Hacked prayer app spreads resistance message: Unidentified hackers took control of an Iranian prayer app during a joint US-Israeli attack to broadcast messages urging the Iranian military to lay down their weapons. They also urged recipients to join the resistance against the current Iranian regime. The messages were sent over an app named BadeSaba Calendar. The Iranian government quickly shut down all Internet access in the country shortly after the attack began. [WIRED]
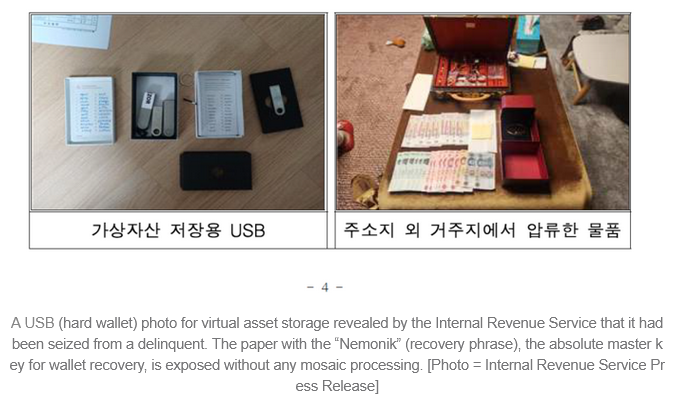
Hacker steals $4.8m after South Korean IRS blunder: A hacker has stolen $4.8 million worth of cryptocurrency from a wallet seized by South Korean authorities. The attacker found the wallet's private key in photos posted online by the South Korean Tax Authority. The seized wallet belonged to one of 124 individuals the agency was investigating for cyber crimes and tax evasion. [Naver News // ForkLog] [h/t Cha Minseok]
General tech and privacy
CT enabled by default in Android: Google will enable Certificate Transparency by default for all apps in Android 17. Apps will have to use certificates that have been recorded in public logs or they will not run on the Android 17 devices. Android's next version is set to be released later this year, in June-July.
Encrypted RCS testing underway: Apple and Google are testing sending encrypted RCS messages between each other's devices. [9to5Google] [h/t TheLemur056]
IETF PLANTS group: The Internet Engineering Task Force has established a new working group to develop new technologies to support quantum-resistant digital certificates. The new PKI, Logs, And Tree Signatures group, or PLANTS, is already working together with Google on an evolution of HTTPS certificates. The new technology is named Merkle Tree Certificates (MTCs), a new form of the old X.509 certificates that integrates public logging into the certificate.
Ubuntu gets password feedback: Ubuntu 26.04 is adding password feedback to sudo. This is a major shift for the Linux distro, which will now show asterisks as the user types in their sudo password. Previously, Ubuntu did not provide any feedback to avoid nearby attackers from determining the length of a user's password. [OMG! Ubuntu] [h/t Marius Voinea]
Amazon Wishlist doxing risk: Amazon is changing how its Wishlists work and is introducing several ways through which a user's home address could be exposed to other users during the wishlist gifting process. [The Daily Dot]
HBO's password sharing crackdown expands: The HBO Max service will start blocking users from sharing their password this year. The policy already existed in the US but is now expanding globally. Users who want to share their password with an out-of-household user will have to pay up an additional $7.99/month. [The Wrap]
Smart TVs are turning into crawler proxies: Several smart TV makers are deploying a new SDK that lets users see fewer ads but also converts their TV into a node into a global proxy network for content scraping. [The Verge]
California's impossible law: PCMag pointed out in a recent article that an upcoming California law will require all operating systems to verify the age of their users at account setup. While the law appears to have been set up specifically for mobile users, it apparently also applies to classic operating systems like Linux. This will be impossible to enforce when creating local accounts.
Instagram to notify parents after dangerous searches: Meta will notify parent accounts when teens start searching Instagram for terms related to suicide or self-harm. The company is rolling out the new notifications after it has seen regulatory and class-action lawsuits over the dangers of social media on kids' mental health. Meta says it's also working on a similar notification that will alert parents when their children are asking similar questions to its AI assistants.

Government, politics, and policy
CISA gets a new acting director: The US Department of Homeland Security has named Nick Anderson as new CISA acting director. He replaces Madhu Gottumukkala, who was transferred to a new role inside the DHS. Gottumukkala has been recently criticized by Congress for firing a third of CISA staff and weakening its ability to defend federal agencies. [ABC News]
Wyden blocks Rudd nomination: Sen. Ron Wyden has pledged to block a vote to confirm Lt. Gen. Joshua Rudd as the next head of US Cyber Command and the National Security Agency. According to The Record, Sen. Wyden cited Gen. Rudd's lack of background in cyber operations and signals intelligence. The US has been without a Cyber Command and NSA lead for 10 months, since President Trump fired Air Force Gen. Timothy Haugh last April.
OpenAI joins Anthropic in DOW scuffle: OpenAI CEO Sam Altman has sided with his rival Anthropic in its dispute with the Pentagon. Altman says he shares the same red lines with Anthropic about not using AI tools for mass surveillance and lethal autonomous weapons. Anthropic told the Pentagon on Friday it will not disable those protections and will work with the agency to transition to a new provider. More than 200 Google and OpenAI employees also signed an open letter showing their support for Anthropic's stance.
Best most detailed technical explanation I’ve seen so far on the Anthropic-Hegseth dispute over military AI use - based on a source granted anonymity
— Frank Bajak (@fbajak.bsky.social) 2026-03-01T17:39:43.834Z
Even one other company speaking up like this makes it harder for the Pentagon to make good on its insane threats. Would love for Google to join the party today.
— Casey Newton (@caseynewton.bsky.social) 2026-02-27T16:35:46.954Z
Claude hit #2 on Apple's US App Store, hours after the DOD designated Anthropic a supply chain risk; it bounced between #20 and #50 for much of February (Jordan Novet/CNBC) Main Link | Techmeme Permalink
— Techmeme (@techmeme.com) 2026-02-28T17:56:00.863Z
AI comments flood pollution board to prevent new rules: Southern California air board rejected new anti-pollution rules after it received tens of thousands of angry emails that appear to have been generated with AI. [Phys]
Albania lifts TikTok ban: Social media company TikTok has returned to Albania after a year-long ban expired last week. The Albanian government banned the app last year after the death of a teenage boy. A 14-year-old was stabbed by another teenager after they clashed online. TikTok says it has now tightened security and safety measures around online bullying. [Reuters]
Chat Control still on the plate: Even if member states voted down the Chat Control legislation last year, negotiations are still taking place on a new version. This time around, member states are looking for a "voluntary" scheme around the scanning of private messages as a way to ease tensions and have the law passed. However, as EDRi points out, all of this is in limbo for now.
Apple devices approved for classified NATO networks: Apple iPhones and iPads have been approved to handle classified information in NATO networks. The devices were approved following an audit by the German government. They are the first consumer-grade devices to be approved for NATO use without additional special software.
India blocks Supabase: The Indian government has blocked access to database and developer platform Supabase. Officials have not disclosed a reason for the sudden block. The company has told customers to use private DNS or VPN servers to get around the block. [The Meridiem]
Sponsor section
In this sponsored interview Casey Ellis chats to Harish Peri, SVP and general manager for AI security at Okta, a cloud-based identity and access management company. The pair chat about the fact that AI is forcing enterprises to relearn the basics around identity security, and how Okta for AI Agents can help.
Arrests, cybercrime, and threat intel
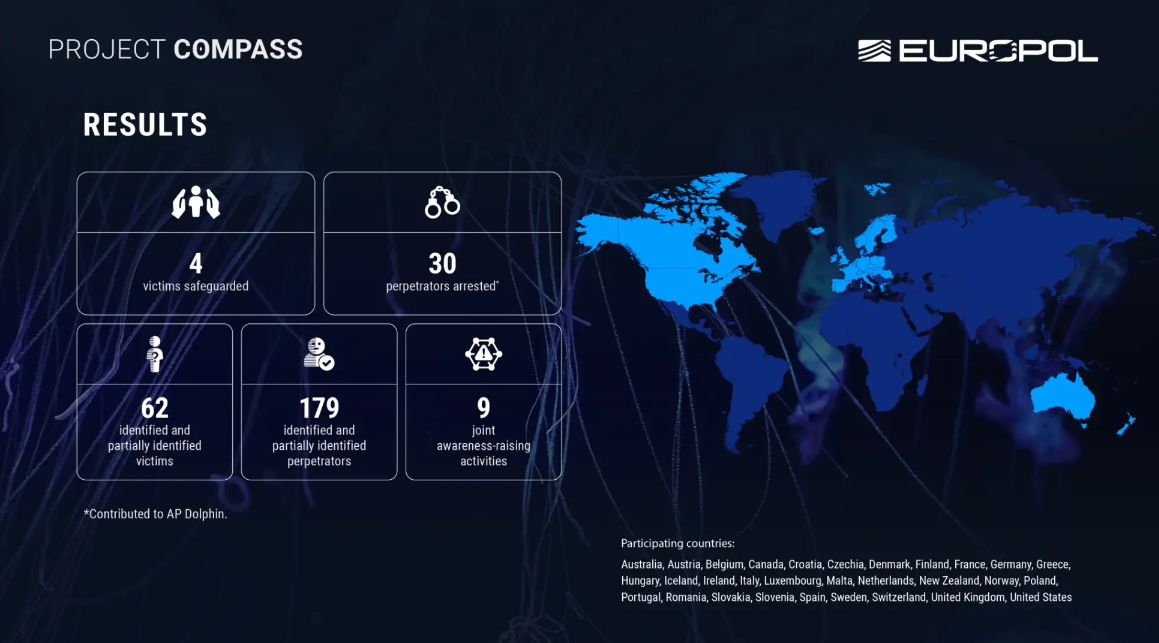
The Com arrests across Europe: A coordinated law enforcement operation has detained 30 individuals connected to an underground online community known as The Com. An additional 179 members were also identified as part of the investigation. The Com has been operating for several years and has been linked to online doxxing, harassment, threats of violence, extortion, sexual exploitation, and cybercrime. It's a really lovely place! </s>
Call center scammer sentenced in Germany: A German court has sentenced the operator of a call center scam network to seven and a half years in prison. Mikheil Biniashvili ran the Milton Group call center network out of Albania between 2017 and 2019. The call centers tricked victims into investing their funds into platforms controlled by Biniashvili and his accomplices. The operation made tens of millions of euros from victims. He also sold the call center's scamming software to other threat actors. [OCCRP]
More scammers arrested in Cambodia: Cambodian authorities have arrested 21 individuals linked to cyber scam operations. Most of the suspects were Chinese nationals. [Kampuchea Thmey] [h/t CyberScamMonitor]
US seizes scam funds: The US DOJ seized $61 million worth of Tether from crypto-wallets linked to cyber scam operations.
OnlyFake admin indicted: The US has charged an Ukrainian national with running a portal that sold fake identification documents. Yurii Nazarenko made more than $1.2 million from running the OnlyFake portal. Nazarenko has already pled guilty and faces up to 15 years in prison.
Kimwolf botnet linked to Canadian man: Cybersecurity reporter Brian Krebs tracked down the admin of the Kimwolf DDoS botnet to a 23-year-old from Ottawa, Canada. Jacob Butler is allegedly the hacker named Dort, who created and is managing the botnet. Butler told Krebs he has not used the Dort persona since 2021 and claims someone is impersonating him.
Meta sues malicious advertisers: Meta filed lawsuits last week against malicious advertisers in Brazil, China, and Vietnam. Some of the advertisers were engaged in celeb-bait schemes and used cloaking techniques to avoid Meta's ad review processes.
FUNNULL is back: QiAnXin has discovered new infrastructure for FUNNULL, a Philippines-based CDN sanctioned last year by the US Treasury for supporting cyber scam operations.
Malware distributed through PiviGames: G DATA has found several cases of malware being distributed through PiviGames, a Spanish portal hosting pirated PC games.
Internet Archive abuse: There's nothing sacred in this world anymore, which is why the Internet Archive is being abused for malware campaigns now.
Malicious Go module deploys backdoor: Socket has found a malicious Go library on GitHub that poses as a popular cryptography package but steals user passwords and deploys the Rekoobe backdoor on infected hosts.
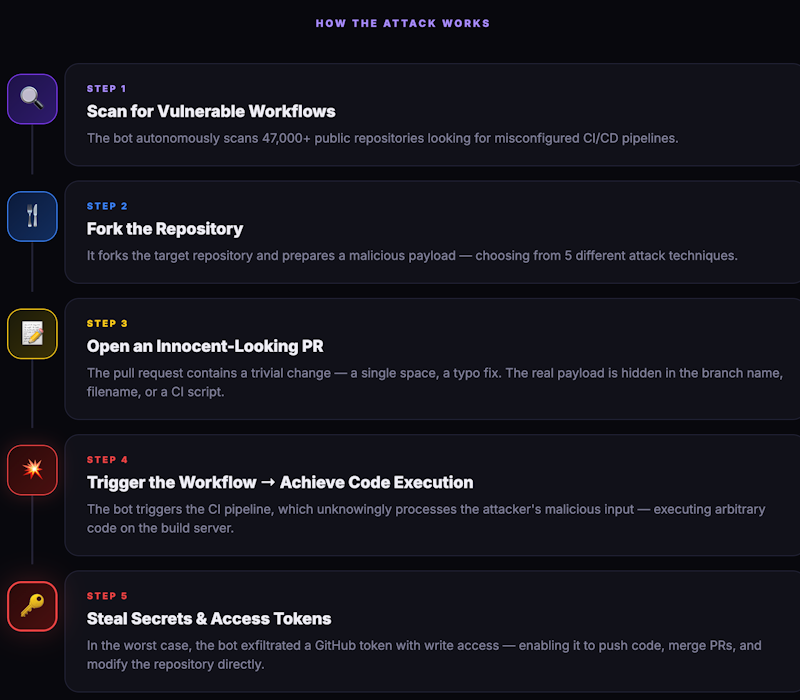
Automated bot attack targets GitHub repos: An automated GitHub bot has scanned and exploited major open-source projects in an attempt to extract their GitHub tokens. The attacking bot scanned GitHub for projects with misconfigured CI/CD pipelines, cloned their repos, and submitted a pull request with malicious payloads in branch or file names. According to Step Security, the bot successfully compromised at least four major projects, including from Microsoft and DataDog.
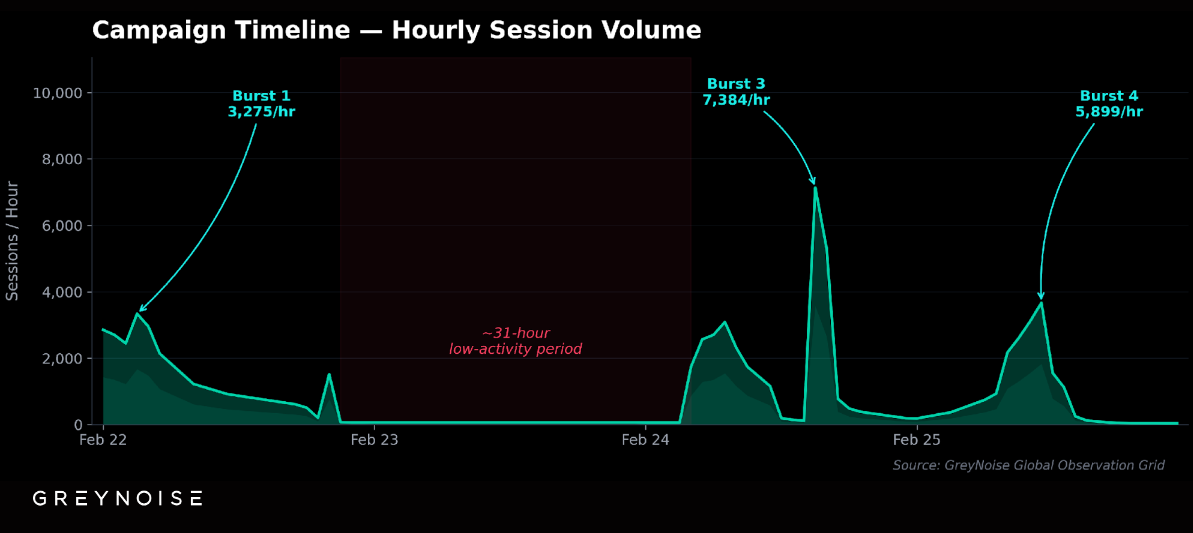
SonicWall scanning flare-up: Security firm GreyNoise has detected a spike in scans for SonicWall devices that originated from the infrastructure of a known proxy provider. The campaign started on February 22 and looked for exposed SonicWall SSL VPNs. GreyNoise says there were little to no exploitation attempts and that the threat actor was likely looking to map out a possible attack surface.
Malware technical reports
Genisys ad fraud botnet: Google has removed 115 Android apps from the Play Store for engaging in a complex ad fraud operation. The apps opened websites inside hidden browser windows to generate ad display revenue for their creators. The IAS Threat Lab identified more than 500 websites that were generated using AI tools and used to serve the ads. The company tracks this botnet as Genisys.
Zerobot: Akamai says a Mirai-based IoT botnet named Zerobot is now exploiting vulnerabilities in the n8n AI toolkit and the Tenda routers.
Aeternum C2: Qrator Labs has spotted a new malware loader botnet named Aeternum C2 that hosts its C&C servers on the public Polygon blockchain.
ClickFix to Termite ransomware: The Deception Pro team has spotted a ClickFix campaign leading to a hands-on-keyboard attack that deployed the Termite ransomware. The company linked the attack to a group known as Velvet Tempest (DEV-0504).
MawaStealer: A malware researcher going by Shavit has published an analysis of campaigns pushing the new MawaStealer.
AMOS campaign: Neil Lofland looks at a ClickFix campaign targeting macOS users with the AMOS infostealer.
Moonrise RAT: Evalian looks at a new Windows RAT named Moonrise. See a similar report from ANY.RUN here.
1Phish kit: The Datadog team looks at 1Phish, a new phishing kit that was first spotted in September in campaigns targeting 1Password users. Datadog reports that the kit has slowly evolved since being spotted the first time.
"The combination of anti-analysis controls, staged credential harvesting, and MFA support demonstrates that 1Password users are being targeted with an operationally mature phishing kit, not isolated phishing pages."
RESURGE web shell: CISA has updated an old malware report on the RESURGE web shell to add new information about its use in recent attacks on Ivanti Secure Connect devices.
Sponsor section
Okta's Brent Arrington and a panel of OIE experts showcase how Cross App Access secures AI Agent access across applications.
APTs, cyber-espionage, and info-ops
More PlugX sightings: After a similar report from Japanese telco IIJ, Lab52 has spotted its own research on recent PlugX sightings in the wild.
Shift in Storm-1516 campaigns: As the US has stopped supporting Ukraine militarily, Russian disinformation campaigns are now targeting its European allies, specifically focusing on France and Germany, its main backers.
More Contagious Interview payloads: Contagious Interview, the DPRK campaign targeting job seekers with boobytrapped payloads, is the gift that keeps on giving. The latest payloads include malicious VS Code extensions dropping known North Korean malware such as Beavertail, InvisibleFerret, and OtterCookie.
FAMOUS CHOLLIMA on npm: Kieran Miyamoto, a threat intel analyst at the London Stock Exchange Group, has identified 17 malicious npm packages operated by North Korean hacking group FAMOUS CHOLLIMA. Socket Security also saw the same cluster, but tracked an additional nine packages, bringing the total to 26.
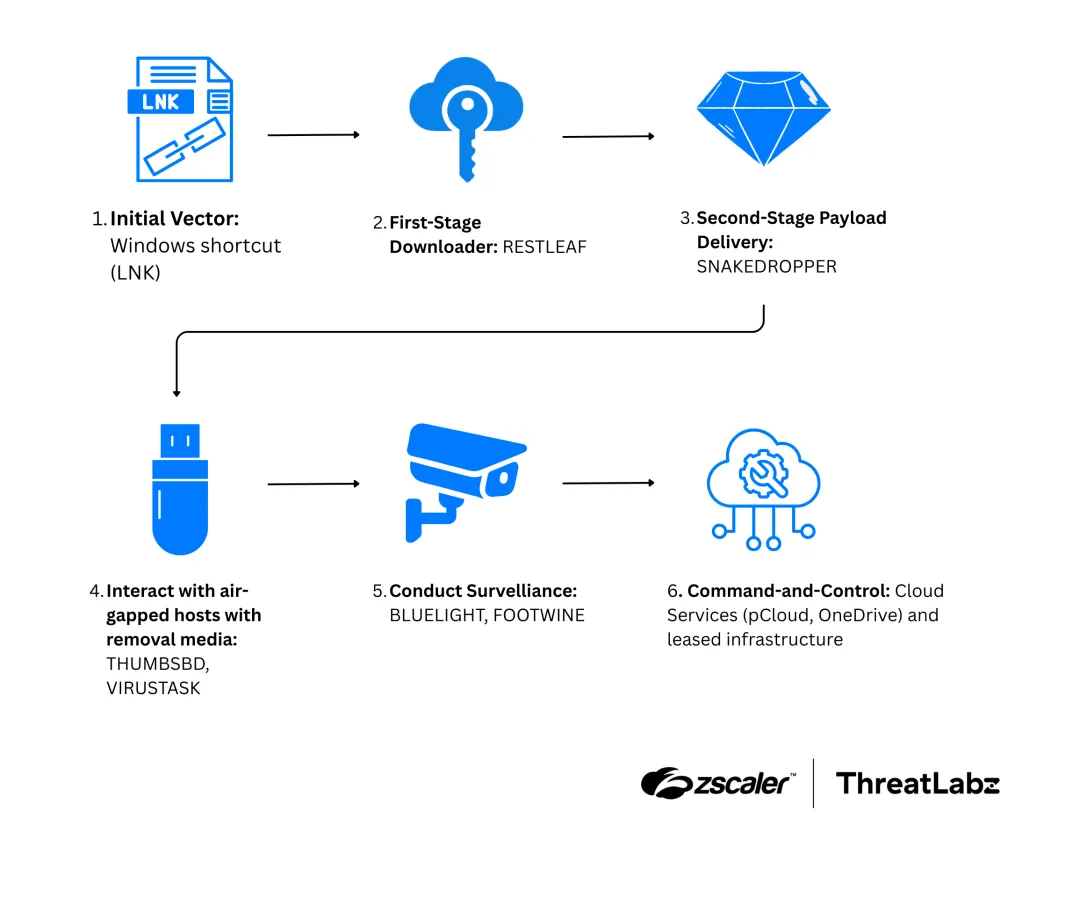
APT37 adds air-gap jumping capabilities: North Korean state-sponsored hackers have developed and are using new malware capable of jumping air-gapped networks. Two new malware families named THUMBSBD and VIRUSTASK have been spotted in recent APT37 (ScarCruft, Ruby Sleet, Velvet Chollima) operations. Both are designed to replace files on removable drives and use them to carry data and commands to and from secure networks.
Vulnerabilities, security research, and bug bounty
Unfixed Matrix crypto bugs: A security researcher has disclosed seven cryptographic bugs in the Matrix secure messenger. The bugs impact Vodozemac, the project's Rust crypto library used by the project. The researcher disclosed the bugs a week after reporting them after the Matrix project declined to patch them. The project argued there was "no practical security impact" on its code.
Unfixed Node.js bug: Martino Spagnuolo has discovered a new Unicode truncation/smuggling and HTTP request splitting attack against Node.js, as a variation of an older 2018 vulnerability. The Node.js project said this doesn't fit its current threat model and declined to patch it.
RCEs in Unitree robots: Security researchers Olivier Laflamme and Ruikai Peng have discovered two vulnerabilities that can be exploited for remote code execution attacks against Unitree robots. One vulnerability exploits an MQTT-like service called DDS (Data Distribution Service) while the second targets the robot's local database. Both attacks can be triggered by pressing a button on the robot's controller. Unitree patched both issues last month.
Misconfig in Mendix apps: The Mendix low-code platform is exposing user data in default setups due to broad permissions. According to DIVD, anonymous and newly registered users have access to raw data sources. This allows attackers with access to low-privileged accounts to easily scrape applications without needing elevated access.
Twitch app leak: Twitch is shipping server-side SDK keys with its iOS app instead of client-side tokens, which is exposing its production and internal features and roadmap. [Buchodi's Threat Intel]
Windows Tasks EoP: MDSec has published a write-up on CVE-2026-20941, an elevation of privilege in the Windows Tasks service that Microsoft patched in January.
3k Google API keys leaked online: Almost 3,000 Google API keys are exposed on the internet and ripe for abuse. According to Truffle Security, the keys allowed apps to connect to Google Maps and Firebase databases. The keys are now much more sensitive as they also allow access to a user's Gemini AI assistant and all the data in a user's account.
Log4j calls out AI sloppers: The Apache Log4j project says it's getting flooded with low-quality vulnerability reports written using AI that are clogging its developers. Some changes will come to the triage process, but it's unclear what for now.
OpenClaw vulnerability: Oasis Security has found a new vulnerability in the OpenClaw local AI agent framework. The vulnerability allows any website to silently take full control of a developer's AI agent. No plugins, extensions, or user interaction are required.
Infosec industry
Threat/trend reports: DataTribe, the Dutch NCSC, IDC, Positive Technologies, and Rostelecom have recently published reports and summaries covering various threats and infosec industry trends.
New tool—mquire: Security firm Trail of Bits has released mquire, a Linux memory forensics tool that works without any external dependencies.
New tool—Nerva: Security firm Praetorian has open-sourced Nerva, a CLI tool that identifies what services are running on open network ports.
"It fingerprints 120+ protocols across TCP, UDP, and SCTP, averaging 4x faster than nmap -sV with 99% detection accuracy. Written in Go as a single binary, Nerva helps security teams rapidly move from port discovery to service identification."
New tool—ICS Phishing Toolkit: Sublime Security open-sourced the ICS Phishing Toolkit, a security add-on for email security platforms to remove malicious ICS calendar invites from a user's work calendar.
New tool—LiteBox: Microsoft launched LiteBox, a Rust-based library for creating cross-OS sandboxes.
New tool—SBOM Tools: Binarly's Alex Matrosov has launched SBOM Tools, a platform to compare and analyze SBOM files to understand software supply chain risks.
New tool—GoLinHound: RantaSec has released GoLinHound, a BloodHound collector written in Go that discovers Linux and SSH attack paths.
New tool—MacNoise: A security engineer named 0xv1n has released MacNoise, a macOS system telemetry generation framework.
New tool—LOLGlobs: The same oxv1n also released a project named LOLGlobs. The project tracks glob-based tools that can be abused for wildcard-based command obfuscation. The project is similar to other initiatives that track benign tools that can be abused for attacks on Windows (LOLBAS, LOLDrivers, and LOFLCAB), Linux (GTFOBins), macOS (LOOBins), CI/CD pipelines (LOTP), ESXi VMs (LOLESXi), RMM software (LOLRMM), tunneling technologies (LOLTunnels), and JavaScript gadgets (GMSGadget).
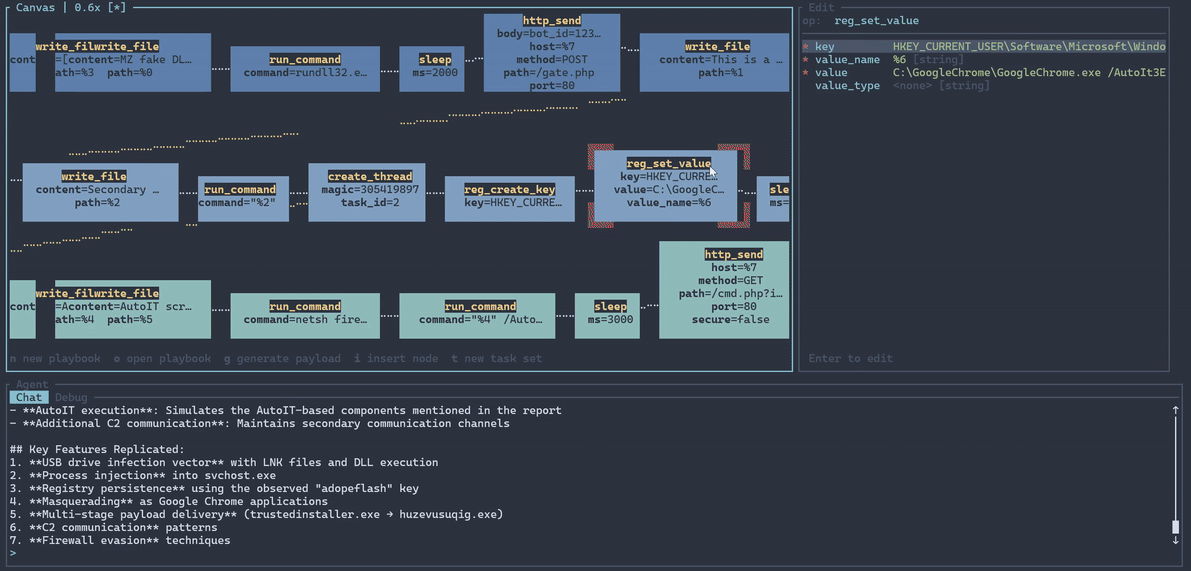
New tool—SynthAPT: Security researcher Weston Walker (ACE Responder) has released SynthAPT, a playbook-based adversary simulation framework for replicating complex attack paths.
Risky Business podcasts
In this edition of Seriously Risky Business, Tom Uren and Amberleigh Jack talk about the argy bargy between the Pentagon and AI company Anthropic. US Defense Secretary Pete Hegseth is demanding that all safeguards are lifted from Claude, while Anthropic CEO Dario Amodei is insisting on protections against mass surveillance of Americans and use in lethal autonomous weapons.
In this edition of Between Two Nerds, Tom Uren and The Grugq talk about how 'professional' Five Eyes cyber espionage agencies like NSA will use AI. These agencies place a premium on stealth and won't yolo AI.




