Risky Bulletin: Iranian password sprays came first, then came the missiles
In other news: Encryption-breaking quantum computers expected within a decade; major npm package Axios got hacked; Flint24 hackers sentenced to prison in Russia.

This newsletter is brought to you by Knocknoc. You can subscribe to an audio version of this newsletter as a podcast by searching for "Risky Business" in your podcatcher or subscribing via this RSS feed. You can also add the Risky Business newsletter as a Preferred Source to your Google search results by going here.
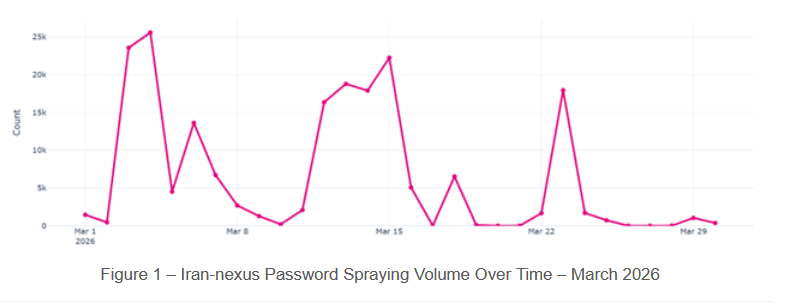
A suspected Iranian APT group has conducted a wide-ranging password spray attack against the Microsoft 365 accounts of governments and private sector organizations across the Middle East.
While password spraying campaigns are a dime a dozen, this one stood out to Check Point researchers because it targeted Israeli and UAE municipalities that were hit by Iranian drone and missile strikes.
"The activity primarily targeted municipalities, which play a critical role in responding to missile-related physical damage. Also, we observe some correlation between the targets of this campaign to cities that were targeted by missile attacks from Iran during March. This suggests the campaign was likely intended to support kinetic operations and Bombing Damage Assessment (BDA) efforts."
The campaign started in early March, just as Iran began mustering its comeback after initial US and Israeli strikes that killed Iranian leader Ali Khamenei and tens of high-ranking government, military, and intelligence officials in late February.
As Iran gathered its hacking crews and gave them new instructions, password spraying activity started being observed by Check Point.
Most of the targets included Israeli organizations. Orgs in the UAE, Saudi Arabia, and Europe were also targeted, but to a much lesser degree.
Activity took place in three waves across March and the password spraying is still ongoing.
Besides municipal government bodies, which are the ones who collect information on strikes and respond to attacks through emergency services, the password spraying campaign also targeted private sector entities connected to the war, such as those in the satellite, aviation, energy, and maritime sectors.
The campaign appears to be a pretty obvious intelligence gathering operation, and a typical one in recent years, with Russia and Ukraine carrying out similar intel-gathering hacking campaigns to assess the damages of their strikes as well.
While no attribution is 100% accurate, Check says the password spraying activity appears to be the work of a group tracked as Gray Sandstorm, an Iranian APT that has used password spraying as an initial access vector since 2021.
Risky Business Podcasts
The main Risky Business podcast is now on YouTube with video versions of our recent episodes. Below is our latest weekly show with Pat and Adam at the helm!
Breaches, hacks, and security incidents
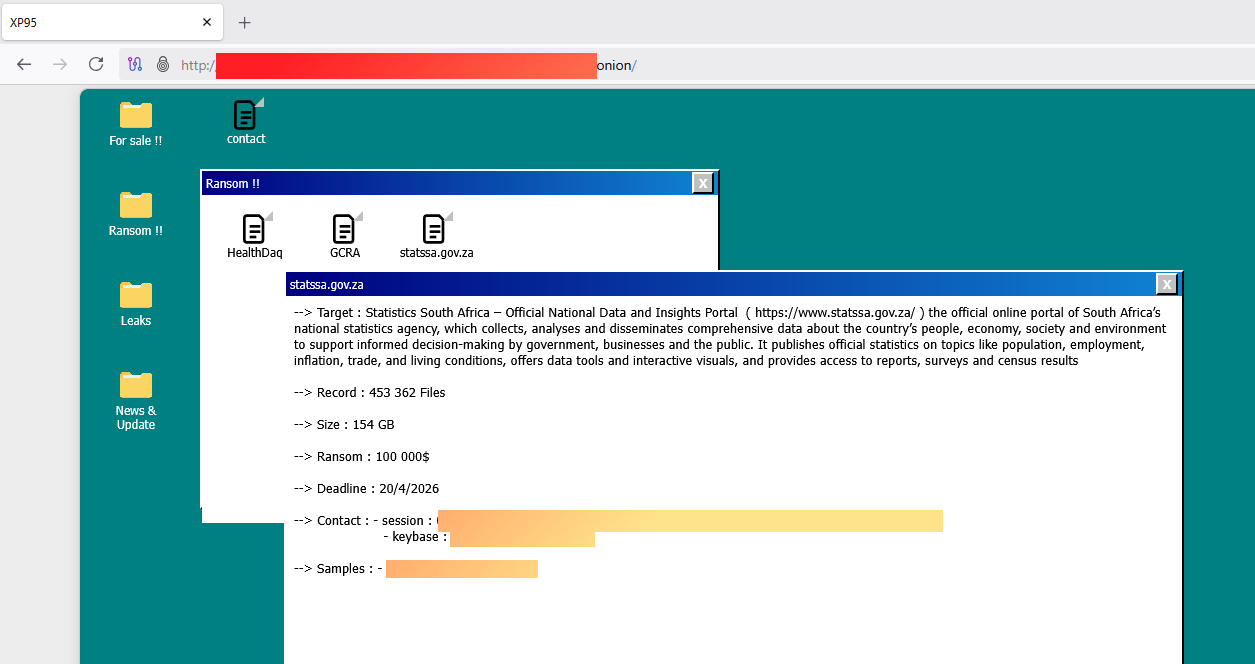
Statistics South Africa ransomware attack: South Africa's government statistics agency is being extorted by a ransomware group. Hackers are asking for $100,000 to not leak the agency's data. The attack has been claimed by XP95, a group that started operations in March. [MyBroadband]
Claude source code leaks via npm: The source code of Anthropic's Claude AI coding agent has leaked online. The source leaked via a map file in the company's npm account. This is the second time Claude Code's source leaks online via an npm map file after a similar incident in February of last year. [NDTV]
Claude Code's source was apparently leaked via a source map inclusion in NPM? Oh NPM, you're the gift that keeps on giving. Here's a link to what appears to be the source: github.com/abubakars... Honestly, kinda silly it wasn't open source already.
— Taggart (@taggart-tech.com) 2026-03-31T13:20:41.000Z
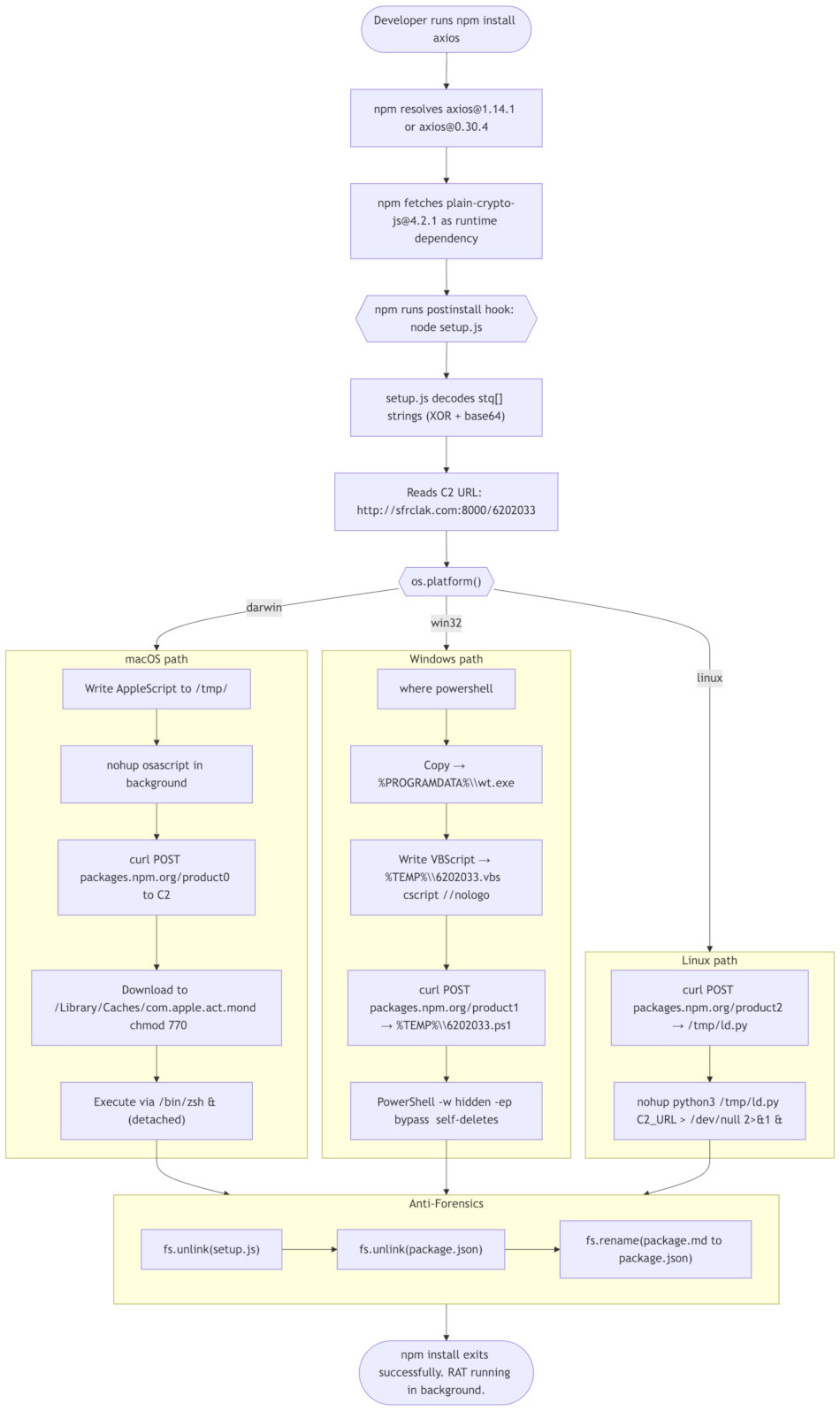
Popular npm package hacked: One of the most popular npm packages has been hacked to deploy a remote access trojan on systems that run it. Attackers broke into the GitHub and npm accounts of the Axios package and locked out its admin on Monday. Malicious versions were live for just over three hours on the npm portal. Because Axios has over 100 million weekly downloads, even a short window likely resulted in thousands of compromised projects downstream. Google linked the attack to a North Korean hacking group tracked as UNC1069. [Aikido Security // DataDog // Derp // Elastic // Huntress // Koi Security // OpenSourceMalware // SafeDep // Semgrep // Snyk // Socket Security // Step Security // Wiz]
General tech and privacy
ECH is RFC 9849: The IETF has codified last month the TLS 1.3 Encrypted Client Hello (ECH) component as an official IETF standard, as RFC 9849.
C++26 is done: The ISO C++ committee has completed work on the C++26 specification of the C++ programming language. This will be the biggest overhaul to C++ since the 2011 specification.
New Aliro standard: A new communications standard will allow users to pass identity checks and enter secure buildings using their smartphones and smart wearable devices. The new Aliro standard was released by the Connectivity Standards Alliance earlier this year and has the backing of major vendors like Apple, Google, and Samsung. The standard is expected to be integrated in future home alarm systems, building management software, and other access control systems.
Android developer verification rolls out: Google has started verifying Android developer accounts this week. Any company or individual who wants their app listed on the Play Store must verify their account by providing a government ID or business registration data. A new menu item has been added to the Play Store dashboard to speed up the process. Students and hobbyist developers can skip this verification process but their app's install count will be severely limited.
Google Workspace ransomware protection: Google's Drive/Workspace ransomware protection feature has left beta and is now production ready.
Telegram warns against third-party clients: Telegram is showing security alerts to users who connect through third-party client apps. The company says third-party apps can log user personal details, record chats, and are susceptible to MitM attacks. [Durov Code]
DMCA abused for Google SERP censorship: The Press Gazette and a Search Engine Land follow-up article into a company that abuses AI articles to manipulate SEO have been removed from Google search results using fake DMCA complaints. I wonder who filed them. Such a big mystery! [PressGazette]
Australia to investigate five tech platforms: Australia's online safety commission is investigating five tech platforms over failures to comply with its new social media minimum age requirement. The investigation targets Facebook, Instagram, Snapchat, TikTok, and YouTube. Observed failures include allowing kids to re-establish their age until they pass the check, not providing a way to report accounts as underage, and still allowing children under 16 to create accounts even if they failed the age check.
Major GDPR fine in Italy: Italy's data protection agency has fined the country's largest bank €31.8 million. The agency says an Intesa Sanpaolo employee improperly accessed the data of more than 3,500 customers. Some of the affected customers were public figures like celebrities and politicians. This is Italy's second-largest GDPR fine and its fourth against Intesa. The largest was against energy provider Enel, which was fined €79.1 million in February 2024.
OkCupid settles FTC investigation: OkCupid has quietly settled an FTC investigation after it was caught sharing the personal data and images of millions of its users with third-parties. It's a slap on the wrist settlement.
Government, politics, and policy
Russia's war on VPNs intensifies: The Russian government has ordered local digital platforms to block VPN users from accessing their sites. Letters have been sent this week to Russian banks, online marketplaces, and IT companies. Officials promised to include sites that block VPN users on a whitelist of sites allowed during mobile internet blackouts. Some platforms plan to introduce extra fees for users connecting to their services via VPN. Apple also pulled more VPN apps from its Russian App Store. [Kommersant // Forbes Russia // TechRadar]
Russian cracks down on Apple ID: Starting April 1, Russians will not be able to refill their Apple ID balance using their mobile accounts. [RBC]
Russia's internet blockade extends to third city: After Moscow and Sankt Petersburg, Russia's internet blocking and whitelist-based access system has now extended to a third city—Rostov-on-Don. [Durov Code]
Iran to start targeting US tech giants: Iran will start targeting the infrastructure of American tech companies across the Middle East starting April 1. The Islamic Revolutionary Guard Corps published a list of 18 companies they accuse of helping Israeli and American military operations. Seventeen of the 18 are US companies. The biggest names on the list include Google, Apple, Microsoft, and NVIDIA. Previous Iranian strikes have hit Amazon and Microsoft data centers in the region, causing prolonged outages. [The Hill]
South Korea launches ransomware task force: The South Korean government has launched a task force to help companies investigate and recover from ransomware attacks. The task force will operate under KISA, the country's cybersecurity agency. KISA says ransomware attacks increased by 40% last year, compared to 2024.
Gottumukkala polygraph investigation dropped: CISA has dropped an investigation into seven staffers who arranged a polygraph test of former CISA acting director Madhu Gottumukkala. The agency began investigating the seven last year after Gottumukkala failed the test. The official claimed the test was unsanctioned and that he was tricked into taking it. Later reporting by Politico found that Gottumukkala pushed for the test in order to access sensitive documents. [Politico]
Confirming @jsaks.bsky.social www.politico.com/news/2026/03... that DHS has closed its investigation into the former acting CISA director's failed polygraph. 5 of the 7 employees under investigation have been reinstated, while the other 2 had already resigned, per a person familiar with the matter.
— Eric Geller (@ericjgeller.com) 2026-03-28T15:01:20.672Z
Sponsor section
In this Risky Business sponsor interview, James Wilson chats with Adam Pointon, CEO of Knocknoc, about how AI is making old school security controls and paradigms like deny-by-default cool again.
Arrests, cybercrime, and threat intel
US charges Uranium Finance hacker: The US Justice Department has charged a 36-year-old Maryland man with hacking the Uranium Finance cryptocurrency platform. Jonathan Spalleta allegedly stole $53 million from the platform across two hacks in April 2021. Authorities seized $31 million of the stolen funds in February of last year after spending years tracking the funds. Spalleta allegedly used the rest to acquire antique Roman coins, rare Pokemon and Magic: The Gathering cards, and other rare paraphernalia.
US charges ten "market makers": The US has charged ten individuals involved in a scheme to promote and artificially inflate cryptocurrency prices. The suspects include executives and employees from four companies—Gotbit, Vortex, Antier, and Contrarian. The companies provided services known as "market makers." They used wash trading to inflate trading volumes and prices to allow their customers to pump-and-dump cryptocurrency tokens. The FBI caught the four after creating and running its own cryptocurrency token.
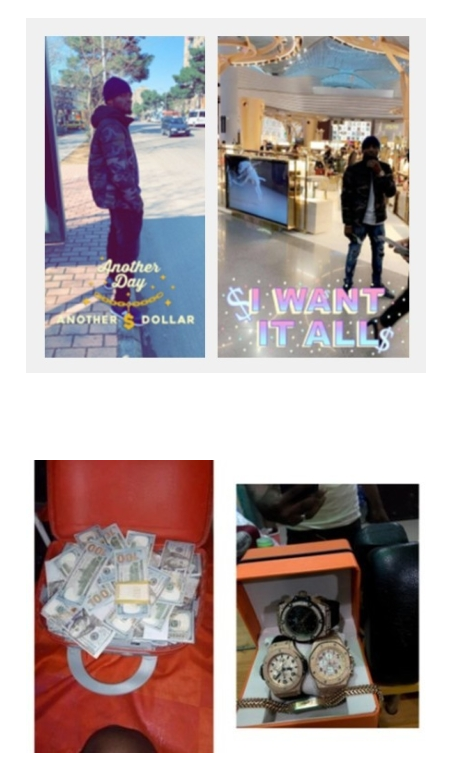
Nigerian fraudster sentenced: The US has sentenced a Nigerian national to 15 years in prison for online scams that stole more than $1.5 million from Americans. Inmate Owolabi managed a fraud group that ran classic Nigerian Prince scams. The prosecution used Owolabi's social media posts flaunting his stolen wealth to request a harsh prison sentence.
Flint24 hackers sentenced to prison: Russian authorities have sentenced 26 members of the Flint24 hacking group to prison sentences. Suspects received sentences ranging from five to 15 years in a penal colony. The Flint24 group operated tens of underground carding shops. Authorities dismantled the group in 2020 after they were caught selling the data of Russian citizens. [TASS]
Encryption-breaking quantum computers expected within 10 years: Quantum computers capable of breaking current encryption are expected within the next ten years, or 15 years max. Quantum experts cited substantial progress in quantum computing research and recent implementations. The accelerated timeline of breaking classic encryption issued by the Global Risk Institute is what also prompted Google to accelerate its transition to quantum-resistant encryption last month. The company has set out to secure all its products against quantum computer attacks by 2029. The French, UK, and US governments have also recently urged companies to adopt technologies to harden their encryption against quantum computer attacks.
New Intellexa company: Czech journalists claim to have identified another local company part of the Intellexa umbrella—Czech Sigi Consulting. The company's CEO was Juval Rabin, the son of former Israeli PM Yitzhak Rabin.
FBI warns of Chinese mobile apps: In a PSA this week, the FBI has warned Americans against using foreign-developed mobile apps, and especially Chinese ones.
IAB prices skyrocket: Rapid7 says prices for initial access sales have "increased dramatically" last year, with some forums, like DarkForums and RAMP, becoming the go-to places for most sales.
Tax phishing season is here: Proofpoint looks at multiple threat actor clusters currently engaged in tax-related phishing ops, ahead of the closing of this year's tax season.
Australians lost $1.5b to scams: Australians lost $1.5 billion (AUD$2.18 billion) to online scams last year. Almost a third of the sum was lost to investment-related scams. According to the National Anti-Scam Center, 2022 was the worst year on record, when Australians lost $2.1 billion (AUD$3.1 billion) to scams.
REF1695 cryptominer campaign: Elastic's security team looks at an e-crime group (REF1695) that has been spreading cryptominers and RATs through fake installers since 2023.
WhatsApp phishing campaign: Microsoft's threat intel team has detected a WhatsApp phishing campaign delivering VBS scripts and backdoors on victim systems.
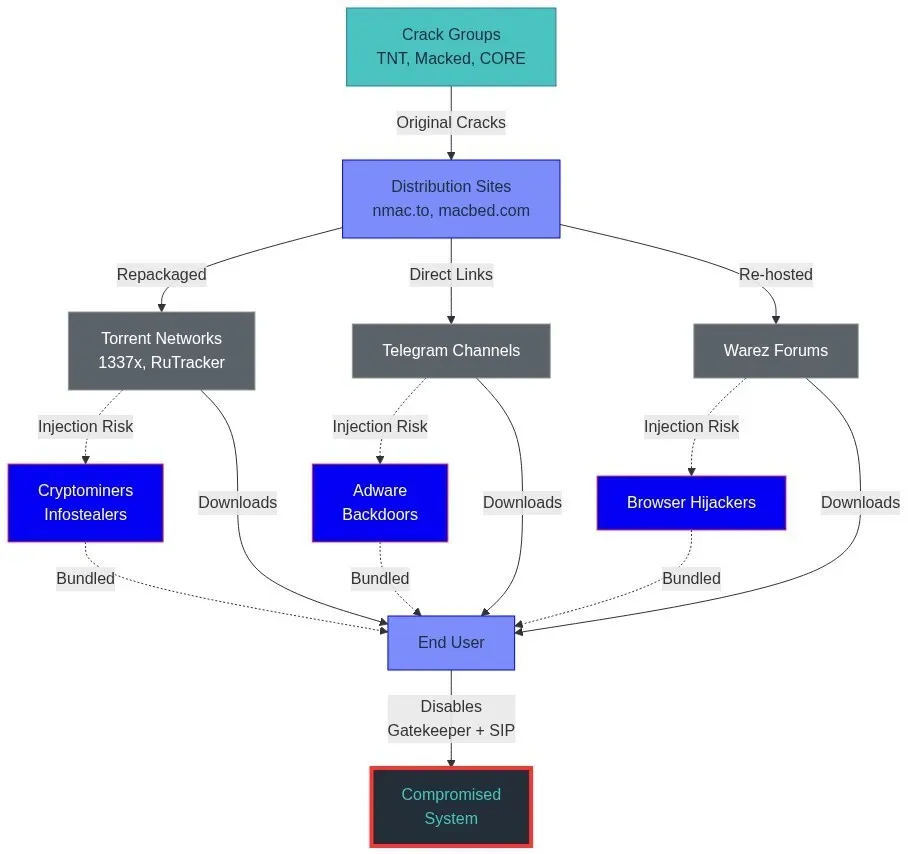
Cracked macOS software campaign: Windows are used to the dangers of running software cracks on their systems, but macOS users are still unaware of how dangerous this can be. Gen Digital has recently spotted threat actors using macOS software cracks to deploy an assortment of malware strains, such as cryptominers, infostealers, backdoors, and adware.
Malware technical reports
FvncBot targets Poland again: CERT Poland has analyzed new samples of the FvncBot Android banking trojan, seen in a campaign targeting Polish users. The malware was first spotted at the end of last year by Intel471.
RoadK1ll: A recent Blackpoint report looks at RoadK1ll, an implant used by threat actors to maintain persistence and move laterally on hacked networks.
DeepLoad: There's a new malware loader named DeepLoad in town! The devs used AI for some of the code and are currently using ClickFix to distribute it.
CrySome RAT: CyFirma has spotted a new C# RAT named CrySome being used in the wild.
"A defining characteristic of CrySome is its ability to survive system resets by leveraging recovery partition abuse and offline registry modification, allowing execution to be re-established even after a factory reset. This is coupled with multi-layered persistence mechanisms including scheduled tasks, Windows services with recovery policies, watchdog processes, redundant binary placement, and registry-based execution triggers."
Phantom Stealer: Group-IB looks at a new infostealer named Phantom Stealer that is being distributed in campaigns targeting Russian and English-speaking audiences.
Venom Stealer: BlackFog published a report on Venom Stealer, an infostealer that uses a looped credential harvesting system that continuously steals new passwords and cookies from an infected host as the user keeps using their browser, instead of dumping passwords once at infection time, like most stealers do.
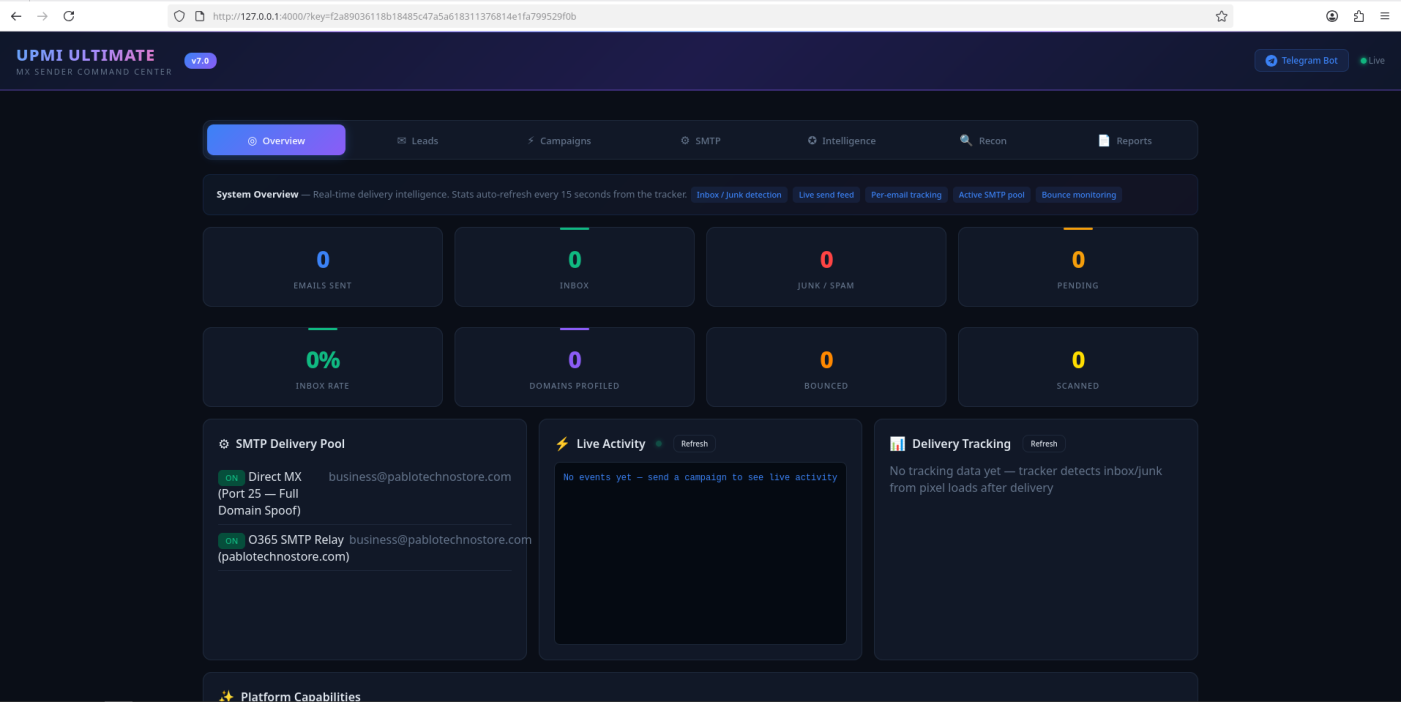
UPMI Ultimate PhaaS: A cybercrime group has leaked the source code of their phishing platform via a misconfigured web server. According to Ctrl-Alt-Intel, the UPMI Ultimate platform can carry out AitM attacks and collect authentication cookies. It was generated with AI and appears to be the work of a group named Team Unlimited. It also contains a backdoor system that secretly collects all credentials harvested by its customers.
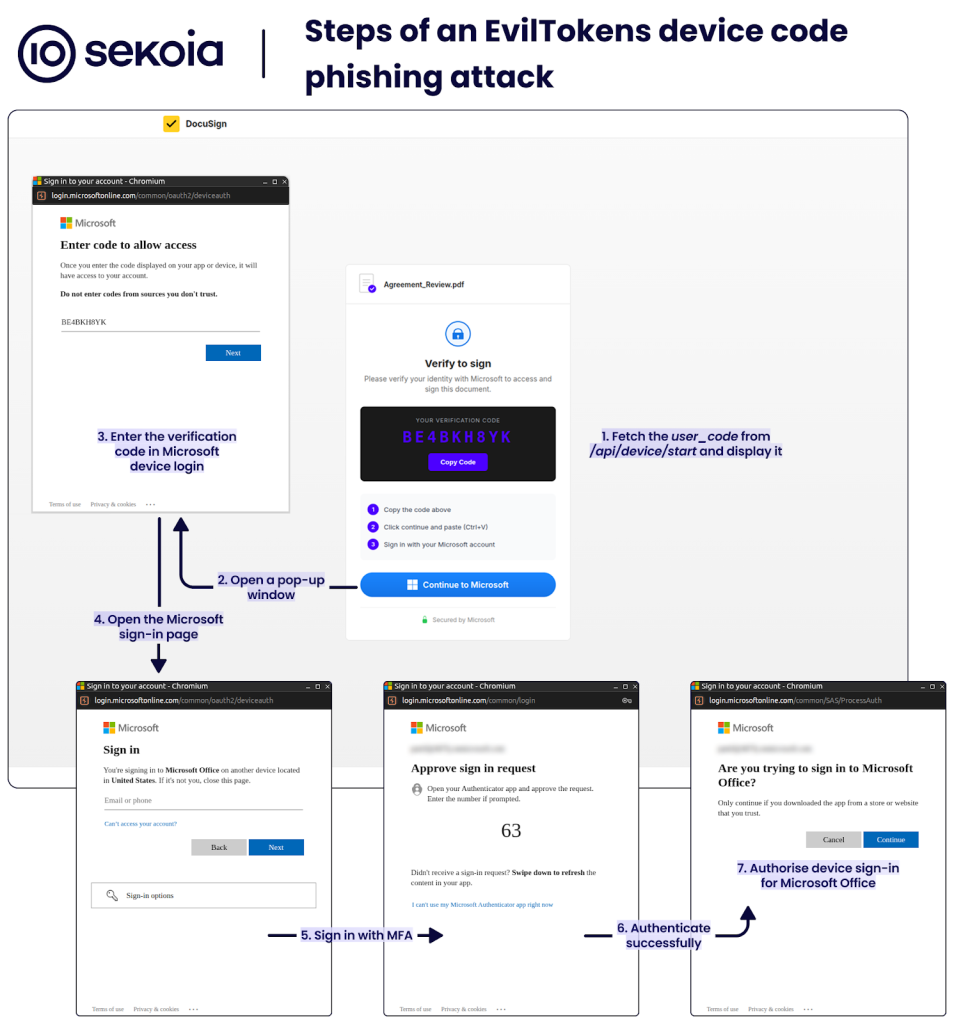
EvilTokens PhaaS: A newly launched phishing platform can allow threat actors to automate device code phishing campaigns targeting Microsoft accounts. The new EvilTokens platform launched in February and has been used in live attacks throughout March. Device code phishing is a rather new technique that tricks users into granting attackers access to an account without compromising their credentials. The technique abuses a legitimate feature designed to allow users to connect to their Microsoft account from a smart device like a smart TV or IoT device. EvilTokens helps attackers trick users into requesting device code and then handing it over.
Sponsor section
In this product demo, Knocknoc CEO Adam Pointon walks Patrick Gray through the Knocknoc secure access platform. Knocknoc is a platform that restricts network and service availability to authenticated users via existing network security equipment. Users don't need to install an agent. It also has an identity-aware proxy component that supports web applications and RDP.
APTs, cyber-espionage, and info-ops
Contagious Interview: A group of North Korean hackers engaged in Contagious Interview campaigns left one of their web consoles exposed on the internet.
"This is the second time this week that I've found the web console for a live threat campaign. This is happening more frequently for a few reasons: first, DPRK threat actors are managing a lot of infrastructure assets, and sometimes they probably just forget. Iterating through all the GitHub, Vercel, Npoint and other infrastructure is a lot of stuff to manage. But what's even worse, I think, is that these threat actors just don't care. A few years ago, they would never have left one of these consoles exposed,but now, they don't care about cleaning up after themselves. They have so many more, that even if this gets taken down, they have other services to replace it."
APTs adopt MAX: According to a Russian threat intelligence group, some APT groups are using the government's MAX instant messenger to contact their targets. [h/t Oleg Shakirov]
APTs target Russian law enforcement: At least three APT groups have mounted campaigns against Russian law enforcement agencies this year. The campaigns leveraged email and social media phishing. They used lures such as Starlink registration apps and UAV drone flying tutorials to infect targets with various strains of malware. Russian security firm BI.ZONE has linked attacks to groups like Paper Werewolf (GOFFEE), Versatile Werewolf (HeartlessSoul), and the previously unknown Eagle Werewolf.
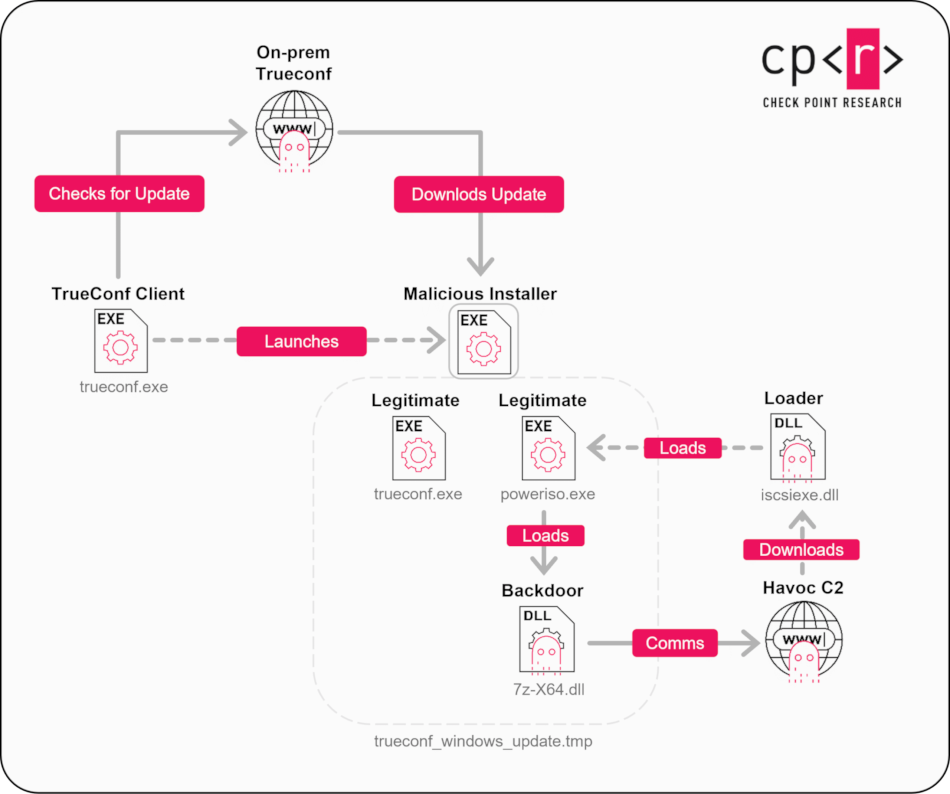
APT leverages TrueConf zero-day: A suspected APT group is exploiting a zero-day in the TrueConf video conferencing server. Attacks have targeted the on-premises servers of several governments across Southeast Asia. Tracked as CVE-2026-3502, the zero-day allows attackers with control over the central TrueConf server to push malicious updates to connected clients. Check Points says the APT has a Chinese nexus.
Vulnerabilities, security research, and bug bounty
Mass PolyShell attack wave: Magento online stores are being targeted using a recently patched vulnerability known as PolyShell. According to Sansec, attacks have entered the mass-exploitation phase, with hundreds of stores being hacked every hour. The vulnerability was disclosed in mid-March. It allows unauthenticated remote attackers to upload web shells on unpatched stores.
Fortinet exploitation: Hackers are exploiting an SQL injection vulnerability in Fortinet EMS servers. Attacks targeting the bug began last week. The vulnerability allows unauthenticated attackers to take over the EMS server's web interface using malcrafted HTTP packets. Tracked as CVE-2026-21643, it was patched back in February. A technical analysis of the bug was published earlier this month.
LangChain vulns: Cyera researchers have published a write-up on three vulnerabilities in the LangChain and LangGraph AI toolkits. The bugs include a path traversal, a serialization injection, and an SQL injection.
OpenAI Codex bug: BeyondTrust's security team has discovered a command injection vulnerability in OpenAI's Codex cloud environment that could have allowed attackers to steal GitHub OAuth tokens from customers. This is now patched.
RSR RE: Khanh of Calif Security has reverse-engineered Apple's Rapid Security Responses (RSR), the macOS and iOS update system that delivers emergency security patches to users without the need to restart their devices.
InsomniacUnwinding technique: Security researcher Lorenzo Meacci introduces InsomniacUnwinding, a new technique to hide and sleep malicious code, even from EDR solutions that continuously scan the memory for malicious code.
Infosec industry
Threat/trend reports: The ACCC, the Global Risk Institute, Radware, Rapid7, and Sophos have recently published reports and summaries covering various threats and infosec industry trends.
Kaspersky reports record revenue: Russian security firm Kaspersky has reported a record revenue of $836 million last year. The company reported revenue increases in Russia and former Soviet states. Kaspersky was ousted from the US market in 2024 and has closed most offices across the EU after Russia's invasion of Ukraine.
New tool—PQC-LEO: Cryptologist Callum Turino has open-sourced PQC-LEO, a tool to benchmark and evaluate the feasibility of integrating Post-Quantum Cryptography (PQC) algorithms into production environments and products.
New tool—QuicFuscate: Christopher Schulze has released QuicFuscate, an anti-censorship QUIC/HTTP/3 VPN protocol.
New tool—InfraGuard: Whispergate has released InfraGuard, a redirection proxy and manager to protect C2 infrastructure.
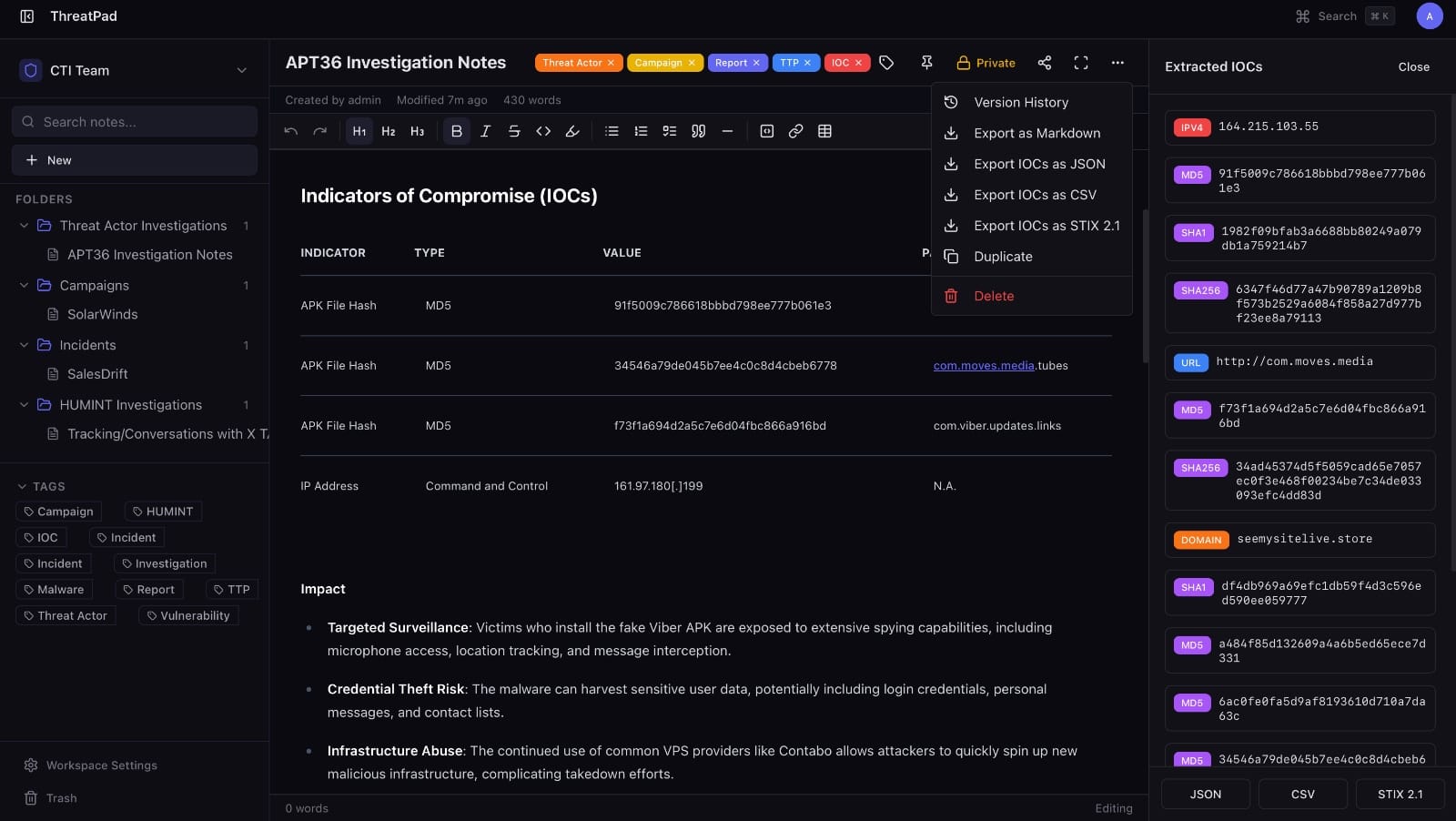
New tool—ThreatPad: CloudSEK's Bhavik Malhotra has released ThreatPad, a collaborative, real-time note-taking platform for CTI and SOC teams.
MCTTP 2025 videos: Talks from the Munich Cyber Tactics, Techniques & Procedures 2025 security conference, which took place last September, are now available on YouTube.
BSides Seattle 2026 videos: Talks from the BSides Seattle 2026 security conference, which took place last month, are available on YouTube.
Risky Business podcasts
In this edition of Between Two Nerds, Tom Uren and The Grugq talk about hacking and scams. While hacking is disappearing as a threat for most people, it is a new golden age for scammers. Even Tom has been scammed!
We recently launched a new podcast series called Risky Business Features. In this episode, James Wilson is "joined" by one of his OpenClaw AI agents for a chat about whether or not an LLM can understand, modify or even create a sophisticated nation-state grade iOS exploit kit.




