Risky Bulletin: GitHub is starting to have a real malware problem
In other news: Russian intelligence services compromise thousands of Signal accounts; Trivy vulnerability scanner compromised for supply chain attack; FBI takes down Aisuru and Kimwolf botnets.

This newsletter is brought to you by Authentik. You can subscribe to an audio version of this newsletter as a podcast by searching for "Risky Business" in your podcatcher or subscribing via this RSS feed.
GitHub is slowly becoming a very dangerous website as more and more threat actors are starting to use it to host and distribute malware disguised as legitimate software repositories.
What started as an infrequent sighting in early 2024 is now at the center of an increasing number of infosec and malware reports.
The tactic is usually the same. A threat actor would take a legitimate repository, add malware to the files—typically an infostealer or a remote access trojan— and then upload the boobytrapped repo back on GitHub.
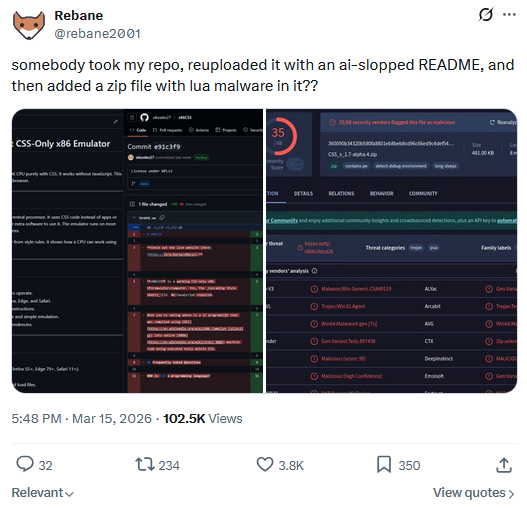
The attacker would then share links online, like social media or forums, or use black-hat SEO or malvertising campaigns to lure users to the malicious GitHub repos.
Attackers were also seen pushing meaningless commits to their repos or using online services that sell GitHub stars and likes to keep the malicious clones at the top of GitHub search page.
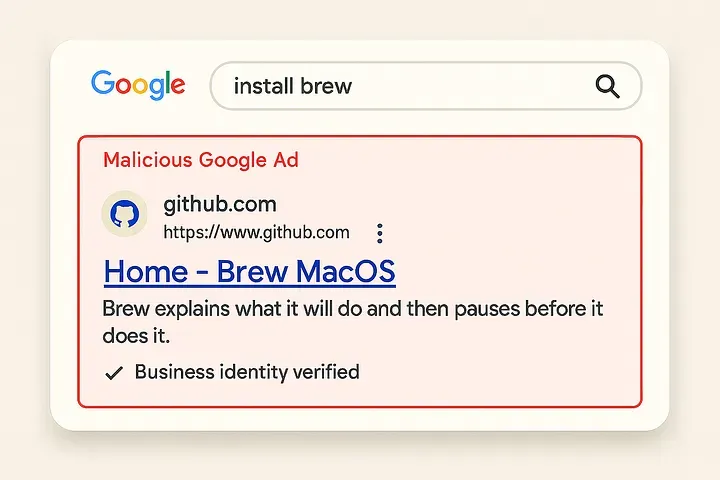
Because of the nature of GitHub, a well-known portal for hosting software releases, users would normally think they landed on the page of an independent software developer and download and run the files without even thinking they might contain malware.
Some of these campaigns abused well-known known software apps, but just as many distributed slightly grey-market tools like gaming cheats and license key cracks.
Clusters discovered over time ranged from hundreds to thousands of repos at a time, with several security vendors arguing that threat actors were using AI to automate campaigns and mass-publish Github repositories.
Here is a list of reports published on these campaigns over the past two years:
- Feb 2024: The report that first spotted this trend, Apiiro saw at the time a campaign of more than 100,000+ malicious GitHub repos using the technique detailed above.
- Feb 2025: A year later, it was Kaspersky's turn to notice the growing number of malware-laced GitHub repos. This one used hundreds of repos targeting gamers.
- Feb 2025: A few days later, Tim Sh published his own finding of a cluster of 1,100+ GitHub repos with gaming mods and gaming cracks containing a version of the Redox Stealer.
- Mar 2025: At this point, even the big dogs like Microsoft started to take notice of this trend.
- Mar 2025: Trend Micro also spotted a campaign using repos for gaming cheats, cracked software, and system tools to distribute SmartLoader, which then dropped LummaStealer.
- Jun 2025: More security vendors are taking notice, and this time was Sophos.
- Jul 2025: A month later, security researcher Dhiraj Mishra uncovered a similar campaign, but this one noticeably different because it was targeting macOS users.
- Jul 2025: It was Prodaft's turn to look at one of these campaigns, spreading what was (at the time) the new CastleLoader.
- Aug 2025: Chinese security firm Microstep also saw this tactic being used to target Chinese developers. This looked to be a smaller, more narrow campaign.
- Sep 2025: LastPass also saw a fake GitHub repo campaign targeting macOS.
- Dec 2025: Kaspersky saw another one of these campaigns that was distributing Webrat.
- Feb 2026: It was DataDog's time to see one of these campaigns, but with a twist. In this one, the threat actors posed as real companies but used ClickFix tricks to fool users into installing infostealers, basically using GitHub as a web page hosting service more than a payload hosting system.
- Feb 2026: Brennan Kenneth Brown saw a rather low-quality campaign that targeted macOS users but some of the repos contained Windows malware. This turned out to be part of a pretty large operation.
- Mar 2026: Huntress saw a different campaign targeting AI aficionados, but instead of payloads, users received modified installation instructions for OpenClaw that deployed malware on their systems.
- Mar 2026: The team at OpenSourceMalware saw a North Korean group appending malware to hundreds of real GitHub npm-related repos in what seemed to be a larger supply-chain attack.
- Mar 2026: Artem Golubin also saw a campaign of 100+ repos, in a report that inspired me to look further into this trend.
- Mar 2026: Acronis found hundreds of GitHub repositories delivering malware to gamers under the guise of "free game cheats." The repos were published across multiple campaigns targeting almost every major online game title.
- Mar 2026: And just as I was writing this, Jamf put out a report on a cluster of malicious repos posing as trading bots, SDKs, and developer utilities.
As can be seen from this timeline, these campaigns have increased in frequency as threat actors have understood how efficient they can be. Just like ClickFix, these campaigns target inattentive users, meaning there's an endless supply of new victims.
Initially, threat actors were also abusing GitHub's trust factor with security tools, but security firms are now taking notice. As Golubin pointed out, about the only one that's not taking notice appears to be GitHub itself.
Just like we saw ClickFix rear its ugly head on the malware landscape and everyone anticipated it would become a major problem going forward, we're also expecting this trend of fake GitHub repos to be a mainstay for the next few years.
But while security firms appear to be doing a good job spotting this, we're also gonna need GitHub's security team to step up. Unfortunately, on a platform designed to copy (fork) a project and create new versions of it (clones), spotting malicious additions to clones of legitimate repos might be quite the engineering problem to fix.
Risky Business Podcasts
The main Risky Business podcast is now on YouTube with video versions of our recent episodes. Below is our latest weekly show with Pat and Adam at the helm!
Breaches, hacks, and security incidents
Trivy supply chain attack: A popular open-source vulnerability scanner was compromised last week in a supply chain attack. Hackers compromised Aqua Security's Trivy tool and used it to deploy malware to downstream users. The malware included a backdoor that harvested credentials and a self-spreading worm impacting the npm ecosystem. A financially motivated hacking group named TeamPCP took credit for the attack. [Aikido Security // Aqua Security // CrowdStrike // GitHub advisory // Socket Security // Step Security // Wiz]
Ransomware shuts down California city: Foster City in California has shut down all public services after a ransomware attack last week. All city services are down, except emergency systems. Officials are considering declaring a state of emergency in order to receive help from state and federal agencies. The city has more than 30,000 residents and is located 20 miles south of US tech hub San Francisco.
LA Metro cyberattack: The Los Angeles Metro system has limited access to its internal system after a cyberattack. It's unclear if this is ransomware, but it likely is. [DysruptionHub]
Navia breach: Almost 2.7 million Americans had their data stolen after a security breach at employee benefits and retirement funds management platform Navia. Social Security numbers and health plan information was included in the stolen data. The breach was traced back to December but no other details were provided. [Navia // Maine OAG // California OAG]
Possible NSCC leak: NetAskari believes a recent hack and leak from China's National Super Computer Center of China (NSCC) might be real.
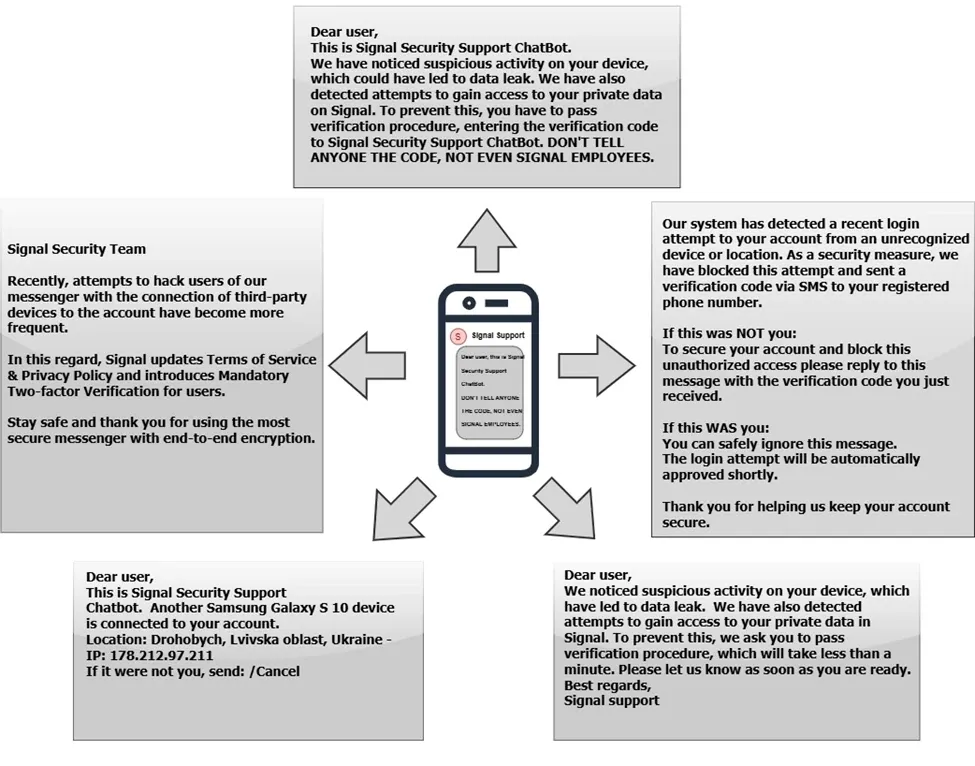
Russian intel compromises thousands of Signal accounts: Thousands of Signal and other secure messaging accounts have been compromised by Russian intelligence services. The campaign targeted government officials, military personnel, and journalists. Attackers posed as support staff and asked victims to share security codes, which they used to link their own devices to the victim's account and intercept communications. The FBI and French authorities issued security alerts last week about the ongoing attacks. Dutch intelligence agencies issued a similar warning earlier this month.
General tech and privacy
Ofcom fines 4chan: The UK's communications watchdog has fined 4chan £450,000 for failing to implement an age verification system. An additional £70,000 for failing to set up its terms of service and failing to assess the risk of its content, according to the UK's new Online Safety Act. 4chan previously sued Ofcom in a US court in August challenging its authority.
GrapheneOS refuses to implement age verification: Privacy-centric mobile OS Graphene has vowed to remain private and not collect any personal user data or implement age verification checks.
GrapheneOS will remain usable by anyone around the world without requiring personal information, identification or an account. GrapheneOS and our services will remain available internationally. If GrapheneOS devices can't be sold in a region due to their regulations, so be it.
— GrapheneOS (@grapheneos.org) 2026-03-20T11:37:59.409Z
Microsoft realizes it screwed up: In a blog post last week, Microsoft acknowledged it ignored customer complaints over Windows 11. The company promised to reduce Copilot integrations, allow for more user customizations in the OS, and cleaner and less buggy updates. After the debacle of its Secure Future Initiative 2.0, I'll believe it when I see it. This company's PR team is an expert at crisis management and empty words.
WordPress adopts AI: Automatting will allow third-party AI agents to help WordPress.com users write and draft content.
Google rewrites SERP headlines: Google is running an experiment where it uses AI to rewrite and replace headlines in search results. According to reports, it's doing a horrible job. [The Verge]
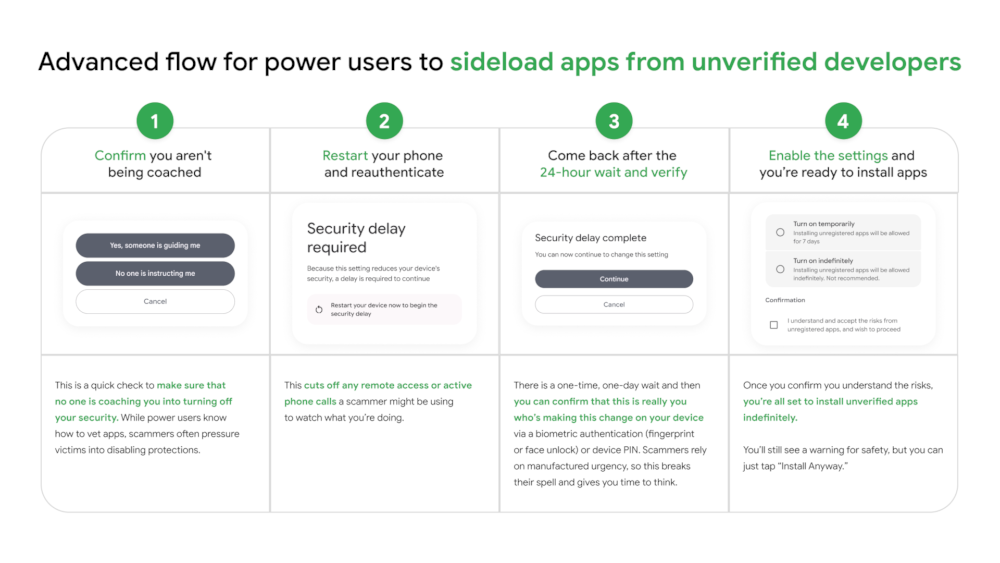
Android to require 24h wait for sideloading apps: Google will require Android users to wait 24 hours before enabling app sideloading on their devices. The requirement will be a one-time waiting period when the sideloading feature is enabled for the first time. The change will go live later this year.
Government, politics, and policy
US AI framework: The White House unveiled a national AI legislative framework that urges Congress to pass AI rules and pre-empt any state laws.
China creates new telecom and cyber fraud alliance: The Chinese government has invited other countries to join a new international alliance to fight telecom and cyber fraud. The new international body will be headquartered in China and launch in September. Beijing says twenty countries have expressed an interest in joining. [CommsRisk]
Iran internet outage not caused by strikes: Iran's internet outage has crossed the three-week mark, making it the largest internet outage in the country's history. The outage is being enforced by the government and is not the result of US and Israeli missile strikes on internet infrastructure. According to multiple reports, Iranian internet backbone networks have been up and maintained upstream connectivity in global BGP tables. [Kentik // Krypt3ia // NCC Group, PDF]
The current, ongoing near total Internet shutdown in Iran, disconnecting Iranians from the global Internet, is now longer than the January 2026 shutdown during nation-wide protests. This makes the current shutdown the longest shutdown IODA has documented in […] [Original post on mastodon.social]
— IODA @ Georgia Tech (@ioda.mastodon.social.ap.brid.gy) 2026-03-19T12:55:31.000Z
Switzerland deploys SCION: Swiss telcos have deployed SCION, a secure alternative to the internet routing protocol BGP. Currently, the system is used in the financial sector. [UBOS]
Russia expands internet blackout to Sankt Petersburg: The Russian government has extended its internet blackout from Moscow to its second-largest city of Sankt Petersburg. All mobile internet is down and experts expect mobile operators to roll out a whitelist of approved sites, just like they did in Moscow.
St. Petersburg just got its mobile internet fully cut. Digital detox, Russian edition.
— WarTranslated (Dmitri) (@wartranslated.bsky.social) 2026-03-22T12:09:56.054Z
Sponsor section
In this Risky Business sponsor interview, Casey Ellis chats to Fletcher Heisler, founder and CEO of open source identity provider, Authentik. They chat about Extended Identity Access Management (XIAM), the company’s new acronym that has been seven years in the making.
Arrests, cybercrime, and threat intel
FBI takes down four botnets: US authorities have seized the command-and-control servers of four IoT botnets involved in large-scale DDoS attacks. Servers for Aisuru, KimWolf, JackSkid, and Mossad were seized on Friday by authorities in the US, Canada, and Germany. The botnets powered DDoS-for-hire services. Some of their attacks reached massive sizes as much as 30 Tbps.
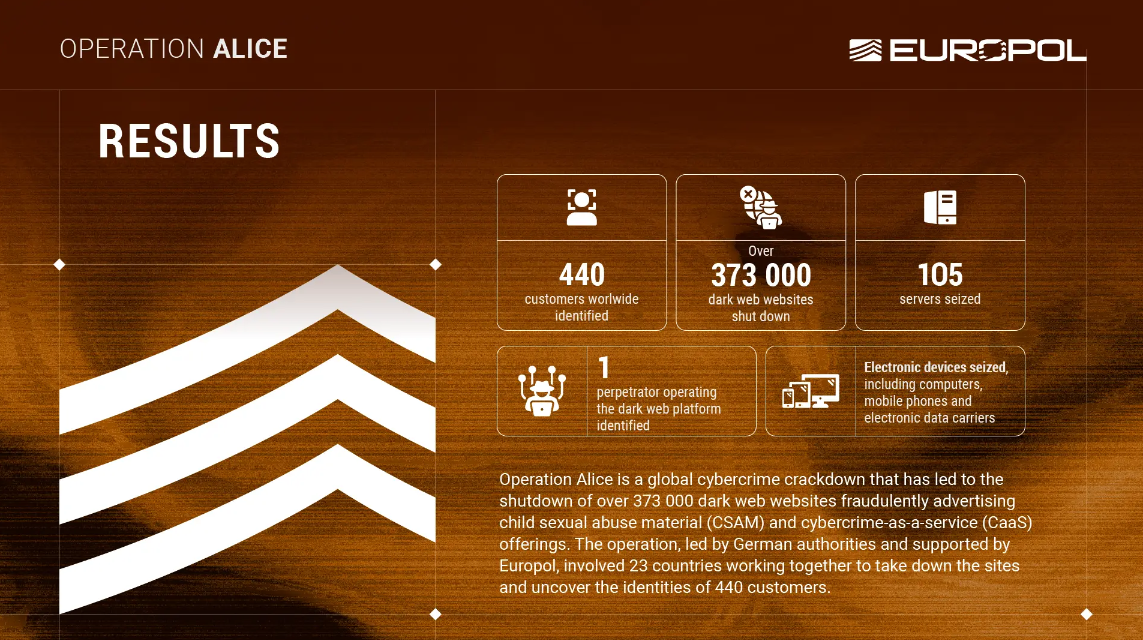
Operation Alice: Europol has seized a network of more than 373,000 dark web portals that promoted child pornography and cybercrime-as-a-service portals. The sites were traced to a 35-year-old Chinese national. The suspect allegedly made €345,000 from selling CSAM material through the sites. An international arrest warrant was issued in his name.
Three sentenced for helping DPRK IT workers: Three Americans were sentenced last week for helping North Korea remote IT workers pose as US-based individuals. The three provided their identities to attackers and hosted laptops at their premises. Alexander Paul Travis of Augusta, Georgia, was sentenced to one year in prison, while two others were ordered to forfeit earnings from the scheme. Travis received a prison sentence because he was a member of the US Army at the time of the scheme.
Extortionist convicted: A jury has convicted a Charlotte man for hacking and extorting a former employer. The incident took place in 2024 after Cameron Curry worked as a contracted IT data analyst for the unnamed company. Curry was found guilty of stealing the firm's data and then threatening to release it unless he was paid a huge $2.5 million ransom.
ClayRAT author detained in Russia: Russian authorities have arrested a student from the city of Krasnodar for developing the ClayRAT Android spyware. The student was detained two months after the malware was first spotted in the wild. The RAT was used in campaigns targeting Russian organizations and was focused on the theft of financial information. [Rostelecom Solar]
Music streamer fraudster pleads guilty: A North Carolina man has pleaded guilty to defrauding music streaming platforms with AI-generated songs. Michael Smith created hundreds of thousands of songs using AI tools, uploaded the songs on popular streaming platforms, and used bot accounts to boost their stats. He made more than $8 million in royalties from platforms like Apple Music, Spotify, and YouTube.
Azure Monitor alert abuse: Threat actors are abusing the Microsoft Azure Monitor service to send phishing emails. Attackers are triggering alerts on their own accounts to send custom alerts to a mailing list that then forwards the mails to victims. Since the emails came from a legit Azure Monitor account they bypass security solutions in targeted networks. So far, the technique has been used for callback phishing campaigns. [BleepingComputer]
Dormant malware activated: Socket has spotted a cluster of dormant VSCode extensions getting activated over the weekend.
Malicious ClawHub skills: According to Raxe, 41.93% of the 238,180 unique OpenClaw skills listed on ClawHub appear to be malicious.
FBI alert on Iranian threat actors: The FBI has published a flash security alert on the use of Telegram as a malware command-and-control system by Iranian threat actors. [FBI Flash Alert PDF]
Tycoon2FA survives takedown: The Tycoon2FA phishing service has restored its server infrastructure after a law enforcement takedown at the start of the month. Phishing activity is now at pre-takedown levels. According to CrowdStrike, the service also didn't bother changing its TTPs.
A “takedown” without an arrest is usually just a pause, episode 833. There’s also an asymmetry in that it often takes skilled personnel from several or even many agencies months to coordinate authorities and effect the technical aspects, whereas 1-2 threat actors set it all up again in days.
— Sig. Ug. (@sigug.bsky.social) 2026-03-22T14:51:33.101Z
Malware technical reports
CECbot DDoS botnet: Security researchers have spotted a new IoT botnet that abuses an HDMI API to support universal remotes to take full control over a smart TV. The new CECbot botnet uses this interface to turn on smart TVs and disable their screens while it silently carries out DDoS attacks. It also uses the devices to port-scan local networks and look for more devices to infect. While CECbot abuses the HDMI interface the initial entry point for infections are still smart TVs running debug ports open on the internet.
Keenadu: Sophos published its own analysis of Keenadu, a backdoor found planted in the firmware of Android tablets by Kaspersky last month.
GSocket backdoor: SANS ISC'd Xavier Mertens looks at a new Linux backdoor built around the GSocket networking utility.
RegPhantom backdoor: Nextron Systems looks at RegPhantom, a stealthy Windows kernel rootkit designed to give attackers code execution in kernel mode.
ICE Cloud: AhnLab has published an analysis of ICE Cloud, a new Go-based cloud vulnerability scanner and brute-force tool.
ClayRAT: Rostelecom's security team published a technical report on ClayRAT, an Android spyware used since last year in attacks against Russian users.
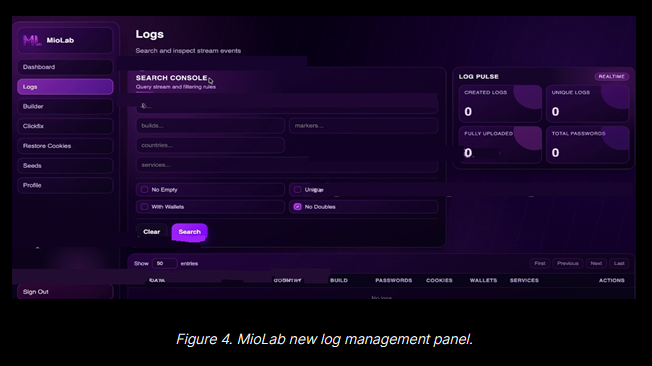
MioLab stealer: LevelBlue looks at MioLab (aka Nova), a new macOS infostealer offered through a MaaS portal.
"MioLab, which is heavily advertised on prominent Russian-speaking underground forums, represents a highly commercialized and professional approach to MacOS malware. Command-and-control (C2) access and API integrations for larger cybercriminal syndicates ("traffers") are part of the MaaS. Distinctively, MioLab places a massive emphasis on cryptocurrency theft, offering an exclusive add-on module specifically engineered to compromise hardware wallets like Ledger and Trezor."
Sponsor section
Authentik is an open-source identity provider that is also offered with paid enterprise features. In this demo, CEO Fletcher Heisler and CTO Jens Langhammer walk Risky Business host Patrick Gray through an overview and a demo of the technology.
APTs, cyber-espionage, and info-ops
Head Mare's PhantomPxPigeon backdoor: The Head Mare APT is targeting Russian orgs with a new backdoor named PhantomPxPigeon.
MuddyWater campaign: Krypt3ia looks at a MuddyWater (Mango Sandstorm) espionage campaign that looks like a strategic pre-positioning and intelligence collection operation. Synaptics also looks at the group's Telegram naming patterns.
Libyan espionage campaign: Broadcom looks at an unattributed espionage campaign that hit a Libyan oil refinery, a telecom organization and a state institution over the past months.
UNK_VaporVibes: A suspected espionage operation is targeting personnel at Pakistani energy firms.
Proofpoint identified a targeted campaign against operations personnel at energy firms linked to projects in Pakistan. The messages were sent on 18 March 2026, and mimicked invitations to the upcoming Pakistan Energy Exhibition & Conference (PEEC). We track the activity as UNK_VaporVibes. 1/8
— ThreatInsight (@threatinsight.proofpoint.com) 2026-03-20T17:14:49.460Z
Vulnerabilities, security research, and bug bounty
Oracle out-of-band security update: Oracle has released an out-of-band security update for its Identity Manager and Web Services Manager products. Tracked as CVE-2026-21992, the vulnerability can be exploited for unauthenticated remote code execution attacks. Oracle's normal quarterly security updates are planned for next month.
Himmelblau vulnerability gives root: A vulnerability in a Linux enterprise app can allow attackers root access over devices. The issue impacts Himmelblau, an interoperability suite to integrate Linux with Entra ID and Intune networks. Attackers with access to a Linux system running the app can abuse a symlink race condition (CVE-2026-31979) in the app to elevate privileges over the entire system. [Akamai]
Gainsight bugs: Rapid7 has found two vulnerabilities in the Gainsight Assist email template plugin that can be used to attack email clients.
QNAP security updates: QNAP has released eleven security updates over the weekend to address issues in multiple software products.
OpenWrt security updates: The OpenWrt open-source router firmware project has released four security updates.
CampusNet vulnerability: The details of 1.1 million German students were exposed online. The leak impacted CampusNet, an IT system used by 22 German universities. Fixes were rolled out within days at most affected entities. [CCC]
Claudy Day vulnerabilities: Oasis Security has found three vulnerabilities in the Claude platform that can be abused for one-click attacks that manipulate prompts and steal user data.
Toxic data flows in MCP servers: A scan of 5,100+ MCP servers found that 555 had toxic data flows, which refers to a combination of agent calls that could be abused for malicious actions.
Langflow exploitation starts within a day: Threat actors began exploiting a recent vulnerability in Langflow AI servers as soon as a patch was available. Tracked as CVE-2026-33017, the vulnerability allows threat actors to run malicious code via the Langflow API without needing to authenticate. Cloud security firm Sysdig spotted attacks 20 hours after the patch was released, giving companies almost no time to install fixes.
More n8n exploited bugs: While CISA added one n8n bug to its KEV database, VulnCheck says two other bugs are also being exploited in the wild and should also be on the list.
KEV update: CISA has updated its KEV database with five vulnerabilities that are currently exploited in the wild.
- CVE-2025-31277 Apple Multiple Products Buffer Overflow Vulnerability
- CVE-2025-32432 Craft CMS Code Injection Vulnerability
- CVE-2025-43510 Apple Multiple Products Improper Locking Vulnerability
- CVE-2025-43520 Apple Multiple Products Classic Buffer Overflow Vulnerability
- CVE-2025-54068 Laravel Livewire Code Injection Vulnerability
Infosec industry
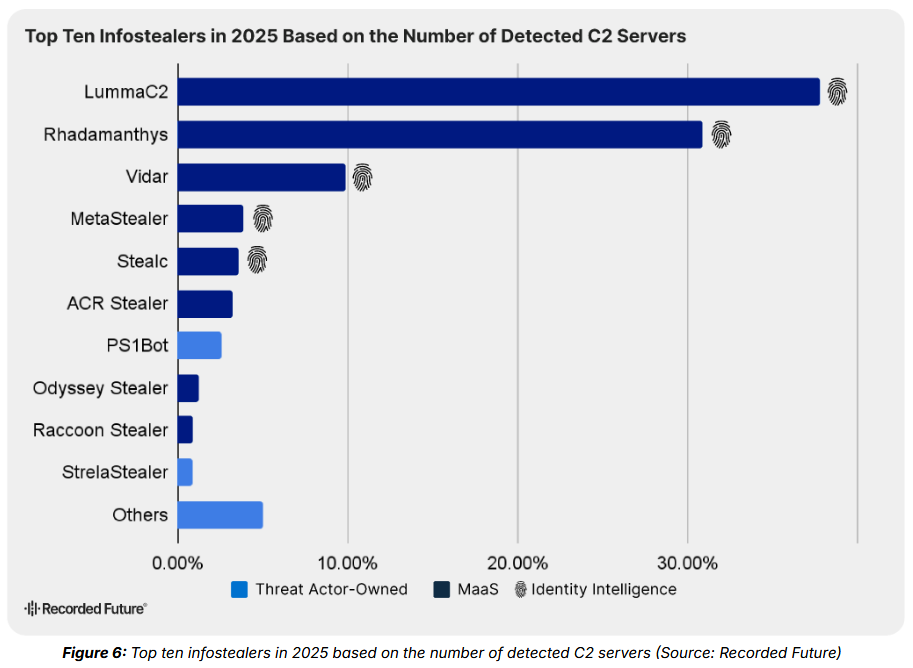
Threat/trend reports: AgentSeal, Ernst & Young, Recorded Future, and Red Canary have recently published reports and summaries covering various threats and infosec industry trends.
New tool—Aurelian: Security firm Praetorian has released Aurelian, a new cloud security reconnaissance framework. It detects secrets, misconfigurations, public exposure, and privilege escalation paths across AWS, Azure, and GCP — from a single CLI.
New tool—Stitch: Google has launched Stitch, a tool for designing user interfaces using artificial intelligence.
New tool—Phantom: Offensive security researcher Mr.Z has released Phantom, a new toolkit for IIS-based lateral movement and code execution within the IIS memory.
New tool—Apatchy: Security researcher Shaq has open-sourced Apatchy, a fuzzing framework for Apache HTTPD.
BSides SF 2026 streams: Live streams from the BSides San Francisco 2026 security conference, which took place over the weekend, are available on YouTube.
BSides Zagreb 2026 videos: Talks from the BSides Zagreb 2026 security conference, which took place earlier this month, are now available on YouTube.
Risky Business podcasts
In this edition of Seriously Risky Business, Tom Uren and Amberleigh Jack talk about how successfully achieving America's war goals could force Iran to double down on cyber power. It's resilient to bombing and is the cheapest, quickest way for the regime to get some wins post-war.
We recently also launched a new podcast series called Risky Business Features. In this episode James Wilson takes a (ridiculously) deep dive into the Coruna exploit kit.




