Risky Bulletin: Former FBI official calls for terrorism designations for ransomware groups that target hospitals and critical infrastructure
In other news: China threatens the EU over new cybersecurity regulations; EU puts up the funds for a sovereign cloud; mysterious data wiper found in Venezuela at the end of last year.

This newsletter is brought to you by Nebulock. You can subscribe to an audio version of this newsletter as a podcast by searching for "Risky Business" in your podcatcher or subscribing via this RSS feed. You can also add the Risky Business newsletter as a Preferred Source to your Google search results by going here.
A former FBI cyber official has urged Congress to investigate if ransomware groups that target hospitals and critical infrastructure can be designated as terrorist organizations.
Former FBI Cyber Deputy Director Cynthia Kaiser says the designation would allow prosecutors access to a broader set of tools and legal levers in tracking and taking down operations.
Kaiser, who served in the FBI for 20 years, including as the agency's Cyber Deputy Director, has also urged lawmakers to examine if ransomware operators can be charged with murder or manslaughter if any attacks lead to a human death.
The former official cited a 2023 study that found that hospital mortality rates increased by 20% during and after a ransomware attack on healthcare organizations.
Speaking at a Homeland Security Committee hearing, Kaiser, who is now senior vice president of the ransomware research center at security firm Halcyon, said her employer is sponsoring a new version of the same study for an updated picture of the ransomware threat after groups have intensified attacks against healthcare orgs over the past decade.
The hearing also looked into how Congress and US lawmakers could also address the rising threat coming from cyber scam compounds and other forms of fraud and scams, which, once again, were the top category of cybercrime losses in the US last year, according to the FBI's yearly cybercrime report.
Back in 2021, the Justice Department elevated ransomware investigations to the same priority as terrorism, in the wake of the Colonial Pipeline incident that caused major fuel shortages across the East Coast.
That prioritization worked wonders. US law enforcement agencies have since cracked down on more than a dozen ransomware groups, including arresting operators, taking down their platforms, and releasing free decryption keys.
Despite this, ransomware groups have continued to operate, which may be a reason why US lawmakers may think it is now time to step up the pressure with the new designation.
Risky Business Podcasts
In this edition of Between Two Nerds, Tom Uren and The Grugq take a deep dive into how a single hacker used OpenAI and Anthropic's tools to help hack nine Mexican government organisations in quick time.
Breaches, hacks, and security incidents
Vercel breach linked to employee account: A recent security breach at cloud hosting platform Vercel has been traced to AI company Context.ai. A Context.ai employee was allegedly infected with an infostealer, which allowed hackers to access the AI company's systems and then pivot to Vercel's Google Workspace environment. The attackers, identified as the ShinyHunters group, used the access to steal credentials for some of Vercel's cloud infrastructure. Data stolen in the incident is now being auctioned online.
Hackers breach France's ID agency: Hackers have breached and are selling data from ANTS, the French government agency that manages identity documents, driving licenses, and vehicle registrations. The French government confirmed a breach on Monday after hackers started selling ANTS data on underground forums last week. The hacker claims to have stolen 12.7 million data rows, although it's unclear how many French citizens are directly impacted. [Clubic // RTL Today]
NSW Treasury staff member arrested for data theft: Australian police have arrested a NSW Treasury staff member for uploading a cache of sensitive documents to a remote server. Jagan Ganti Venkata Satya was arrested on Sunday, two days after the breach was detected internally. Authorities are still investigating who owns the remote server. [The Australian Financial Review]
ETH Limo hijack: A threat actor hijacked the DNS account of the ETH Limo online service. ETH Limo works as a proxy and allows regular internet users to access private websites hosted on .eth domains. The hijack allowed the attacker to control traffic through the proxy and likely redirect users to phishing sites. ETH Limo's DNS provider, EasyDNS, blamed the incident on social engineering and said this was the company's first-ever such incident.
Lovable incident: AI platform Lovable is in the middle of a controversy after it tried to play down a bug in its platform that allowed logged in users to view the data of others, including credentials, chat history, and source code. [Business Insider]
Future Energy Capital BEC incident: An Irish financial services company, Future Energy Capital, is suing its payments operator after the operator failed to detect that a cybercriminal had hacked a Future Energy Capital employee account's email and was giving it bad instructions to send payments to the wrong bank account. The company lost €2.2 million in the incident. [The Irish Independent] [h/t Brian Honan]
Kelp DAO hacked blamed on North Korea: LayerZero, the company behind the Kelp DAO crypto platform, blamed a recent hack of $292 million from its coffers on North Korean hackers. No surprise here!
UltraDNS DDoS attack: A DDoS attack took down UltraDNS for a few hours last week. [h/t RvD]
Mastodon hit by DDoS attack: A major DDoS attack has brought down a large part of the Mastodon social network on Monday. The attack was claimed by the same group that brought down BlueSky at the end of last week. The group goes by the name of the 313 Team and previously launched DDoS attacks against Microsoft 365 earlier this month.
Same group also attacked Mastodon.
— —>realhackhistory.org (@bsky.realhackhistory.org) 2026-04-20T19:31:38.806Z
General tech and privacy
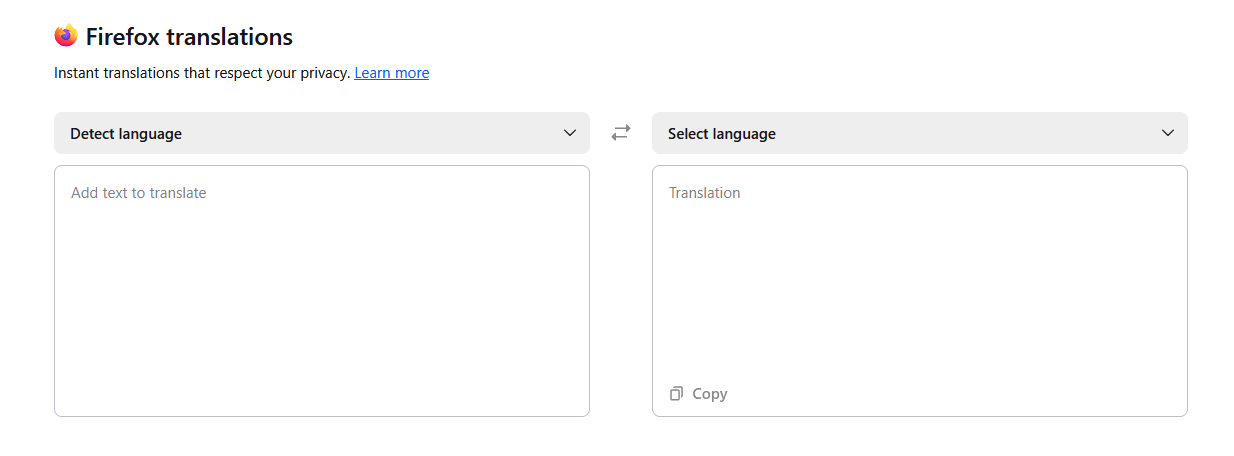
Firefox 150: Mozilla has released Firefox 150. New features and security fixes are included. The biggest feature in this release is the addition of a dedicated translator app at the about:translations URL, as a local, more private alternative to Google and Bing Translate. Users can now also export individual pages from inside a PDF file via Firefox's built-in PDF reader. According to WIRED, Mozilla also used Antrophic's closed-access Mythos agent to find and fix 271 bugs in this Firefox release.
Ruby Central has financial problems: Ruby Central, one of the organizations that manages the RubyGems package repository, is having financial difficulties after its executive director, CFO, and PR agency have left, following a failed bid to hijack control of the RubyGems portal from the community last year.
Dutch reporters track a warship with a BLE tracker: Reporters from Dutch news outlet GLD showed how easy it is to track someone with a Bluetooth tracker these days by sending one device via snail mail to a Dutch NATO warship. Coincidentally, the ship was escorting France's nuclear aircraft carrier Charles de Gaulle in the Mediterranean, which meant you could track France's nuclear arsenal with a $5 device.
Russians bypass internet censorship with foreign eSIMs: Russians are using foreign eSIM cards as a way to bypass the Kremlin's internet censorship machine. Cards bought from neighboring countries are being put in roaming mode and allowed access to all resources without a VPN for only 2,000 rubles per week ($25/w). [h/t therealvladimirputin]
New mega GDPR fine in Italy: Italy's data protection agency is not playing around and has imposed another mega-fine for GDPR violations, this time on the country's own postal service, a fine of €12.5 million.
New Google strike team: Google has allegedly created a secret strike team to improve the company's coding agents and catch up with Anthropic before they run away with the entire AI market. [The Decoder]
Musk snubs French police interview: Elon Musk did not show up to a voluntary interview in Paris this week related to France's probe into his platform X. French authorities are investigating the platform for allowing its AI assistant Grok to produce nude images and CSAM. Musk's absence comes after the DOJ also refused to help French investigators last week. [BBC]
UK launches Telegram investigation: The UK's communications watchdog has launched an investigation into Russian instant messaging app Telegram for hosting CSAM on its platform. Ofcom says it's working with its Canadian counterpart to investigate the issue. If found guilty, Telegram will face a possible fine of up to £18 million or 10% of qualifying worldwide revenue.
Apple to get a new CEO in September: Tim Cook will step down from his role as Apple CEO in September. Cook will move into the role of executive chairman of Apple's board of directors. He will be replaced in the CEO role by John Ternus, senior vice president of Hardware Engineering.
GitHub Copilot changes: Microsoft is preparing to move Copilot from a request-based pricing model to a token/API-based billing later this year. Some changes in preparation for the major overhaul have already been made this week. [Ed Zitron]
AI token subsidies seem to be ending across the industry. GitHub Copilot has paused new signups on multiple plans, removed Opus from $10-a-month subscriptions, and plans to move users to token/API-based billing later this year. Usage quotas are also being reduced and users will hit limits sooner
— Dare Obasanjo (@carnage4life.bsky.social) 2026-04-20T21:40:27.840Z
Government, politics, and policy
EU puts up funds for a sovereign cloud: The European Commission has awarded €180 million to four European companies to host the bloc's digital services on a sovereign cloud for the next six years. Tenders were awarded to Luxembourg's Post Telecom, Germany's StackIT, France's Scaleway, and Belgium's Proximus groups. The four met strict criteria for data privacy and tech stack independence. [Reuters]
OPM to collect federal worker healthcare data: The US Office of Personnel Management is planning to collect healthcare-related information on every US government worker as part of what they call a modernization effort. [FNN]
China threatens EU over new cybersecurity regulations: China has threatened to retaliate against EU companies if the bloc passes its new cybersecurity regulations and push Chinese companies out of its mobile networks. The EU has advised member states to remove Huawei and ZTE equipment from their national networks, but only 13 of the 27 members have followed through. The new draft regulations would make this process mandatory for all members. Beijing says it will impose similar rules and also sue the EU at the World Trade Organization. [SCMP]
Sponsor section
In this Risky Business sponsor interview, Catalin Cimpanu talks with Sydney Marrone, Head of Threat Hunting at Nebulock, about hunting shadow AI agents on corporate networks.
Arrests, cybercrime, and threat intel
Security firm employee pleads guilty to ransomware attacks: A Florida man has pleaded guilty to deploying ransomware and extortion. Angelo Martino conducted the attacks while an employee of US cybersecurity firm DigitalMint. Together with two other cybersecurity professionals, he deployed ransomware and shared data from negotiations with the BlackCat group. The FBI seized more than $10 million from Martino it claims he made illegally. All three have now pleaded guilty. Martino will be sentenced in July while his two accomplices are scheduled for later this month.
Ukraine dismantles bot farm: Ukrainian authorities have dismantled a bot farm that was used to register and manage more than 20,000 online accounts. The accounts were registered using Ukrainian SIM cards and later sold to Russian customers. Ukraine's intelligence service says the bots were then used to spread disinformation or to recruit Ukrainians for acts of sabotage. [The Record]
200+ Japanese firms paid ransoms: More than 200 Japanese companies paid ransomware groups last year, but only about 60% managed to recover their files. More than 500 companies reported getting hit. The companies that chose to restore systems from backups said it took up to a month to do so. [The Mainichi]
Malicious apps hit the Chinese iOS App Store: A cluster of 26 malicious iOS apps have been uploaded on the Chinese version of the Apple App Store. The apps redirected users to phishing pages posing as legitimate cryptocurrency services. The phishing pages tricked users into installing malicious iOS provisioning profiles, which were then used to deploy malicious crypto-wallet apps that intercepted seed phrases. Apple removed all the apps after Kaspersky reported them.
Internet scan surges precede vulnerability disclosures: Mass-internet scanning activity is now preceding vendor vulnerability disclosures on a regular basis. Security firm GreyNoise says that almost two out of three scanning surges precede the revealing of a new vulnerability. The median lead time is 11 days, but sometimes scanning can occur even three weeks before a disclosure.
macOS LOTL: While Living-off-the-Land techniques are a common occurrence on Windows, Cisco Talos looks at all the native macOS tools and features that can also be abused in the same way.
StealTok campaign: More than 130,000 users have downloaded and installed malicious Chrome and Edge extensions that stole their data and tracked their browsing history. The 12 extensions posed as tools to download TikTok videos and were available through the official Chrome and Edge stores. The cluster passed store security checks and operated legitimately for more than six months before activating any malicious behavior. According to security firm LayerX, more than 12,000 users are still running one of the 12.
AI model fingerprinting: AI service company Rival has analyzed and fingerprinted 178 writing genAI models to find out who's copying who and why some identical services cost sometimes 185 times more.
Perforce servers widely exposed on the internet: Almost three-quarters of Perforce P4 source code management servers connected to the internet are misconfigured and leaking source code and sensitive files. The servers are widely used in the video game and animation industry due to their ability to handle large and complex files. An internet-wide scan found more than 4,300 servers with read access exposed online. Another 1,300 also provided write access, while a smaller subset of 223 servers had super user accounts left exposed without a password.
DPRK remote IT worker schemes: Microsoft has shared a bunch of ways to detect North Korea remote IT worker schemes.
Empty email subject line phishing: CyberProof says it's seeing a spike in phishing activity utilizing empty email subject lines as a way to get users to actually click and open the email and read the lure.
DragonForce interview: Threat intelligence analyst Marco A. De Felice has published an interview with the operators of the DragonForce ransomware group.
The Hormuz scams are here: Greek maritime security firm Marisks says scammers are leveraging the strait of Hormuz blockade to target shipping companies with scams, asking for cryptocurrency payments in exchange of safe passage. [The Straits Times]
Malware technical reports
Gentlemen ransomware: The Gentlemen ransomware group has had an explosive start of the year and hacked more than 240 organizations in just three and a half months. The group has 320 victims listed on its dark web portal in total, with 75% being added this year. The sudden spike in activity has made the group one of the most active ransomware operations this year together with Akira and Qilin.
Kyber ransomware: A Rapid7 report looks at the Kyber ransomware and its dual Windows and ESXi encryption capabilities.
"The ESXi variant is specifically built for VMware environments, with capabilities for datastore encryption, optional virtual machine termination, and defacement of management interfaces. The Windows variant, written in Rust, includes a self-described “experimental” feature for targeting Hyper-V."
TwizAdmin: BreakGlass looks at TwizAdmin, a multi-stage malware operation combining a cryptocurrency clipper, ransomware, a RAT, and infostealer capabilities all into one.
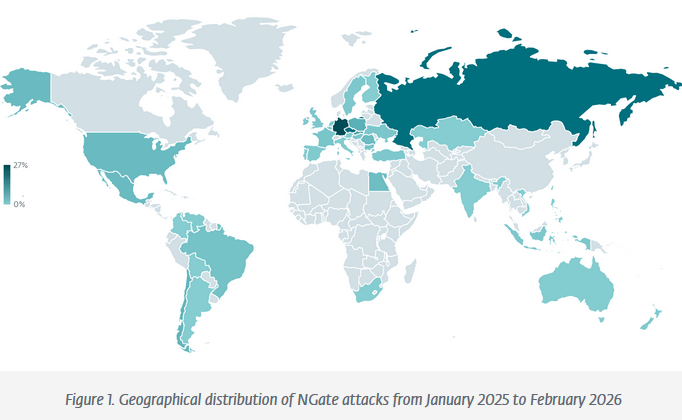
NGate reaches Brazil: NGate, the Android malware that steals a victim's NFC data and relays it to an attacker to approve NFC transactions, has now been spotted in Brazil. Previously, the malware was observed in China, Russia, and a few parts of Europe, before spreading to India, North America, and Australia.
PhantomCLR: CyFirma has published a technical analysis of "a multi-stage, APT-grade post-exploitation framework that demonstrates exceptional operational security discipline across every stage of the attack chain."
Gh0st RAT: Splunk is tracking an adware campaign that's also bundling a version of Gh0st RAT for long-term backdoor access.
Formbook: WatchGuard researchers have spotted a new campaign spreading the good ol' Formbook infostealer, the malware as old as time.
FudCrypt: Ctrl-Alt-Intel takes a look at FUDCrypt, one of today's most popular Cryptor-as-a-Service platforms used in malware operations.

Sponsor section
Agentic AI platform Nebulock pitches its product in one of our recent Snakeoilers episodes.
APTs, cyber-espionage, and info-ops
Lotus Wiper spotted in Venezuela: Russian security firm Kaspersky has found a never-before-seen data wiper that was active in Venezuela at the end of last year and the start of 2026. The timeline the wiper was active matches the US military's operations targeting the Maduro regime. Kaspersky says it found "clear signs" the malware was designed to target specific victims in the country's energy and utilities sector. Venezuela's power grid went down during US military operations, while the country's largest oil producer reported a ransomware attack days before the Maduro regime change. US CyberCommand previously admitted to Congress that it contributed its cyber expertise but did not specify its involvement. Kaspersky tracks this as the Lotus Wiper.
PhantomCore goes after TrueConf: A suspected Ukrainian APT group has hacked and spied on Russian organizations through TrueConf video conference servers. A hacking campaign has been underway since September of last year, and attacks targeted both public and private organizations. Attacks exploited old TrueConf vulnerabilities and then pivoted to other parts of the network. Russian security firm Positive Technologies linked the attacks to a group tracked as PhantomCore. The group also planted keyloggers on the login pages of Exchange servers in a separate campaign last year.
Mustang Panda: Acronis researchers have spotted a new version of Mustang Panda's LOTUSLITE backdoor in campaigns targeting India's banking sector and the South Korean policy and diplomatic circles.
Seedworm's DinDoor: Hunt has found 20 C&C servers exposed online that were used to manage DinDoor infections, a malware previously linked to Iranian APT group SeedWorm, aka MuddyWater.
"DinDoor does not appear to be a single-operator tool. The decoded JWT showed similarities to MuddyWater, while the other sample showed a completely different execution flow while likely targeting a financial services company, something more common of TAG-150/GrayBravo. Encountering yet another malicious file communicating with serialmenot[.]com confirms a multi-tenancy platform under separate credentials distributed to actors by unknown means."
EU sanctions Kremlin disinfo peddler: The European Union has sanctioned Euromore, a Russian media platform spreading Russia's war propaganda in the EU. The EU imposed a second set of sanctions on Pravfond, a foundation involved in spreading false narratives that Russians are being persecuted in neighbouring states as a way to justify military incursions. Since Russia's invasion of Ukraine, the EU has sanctioned 69 individuals and 19 entities, with a large chunk of the sanctions targeting Russia's hackers and info-op operations.
Russian APTs are using AI to hack Europe: Russian state-sponsored hackers are using AI tools to accelerate cyber operations, according to the Dutch military intelligence service's annual threat report. [Politico Europe]
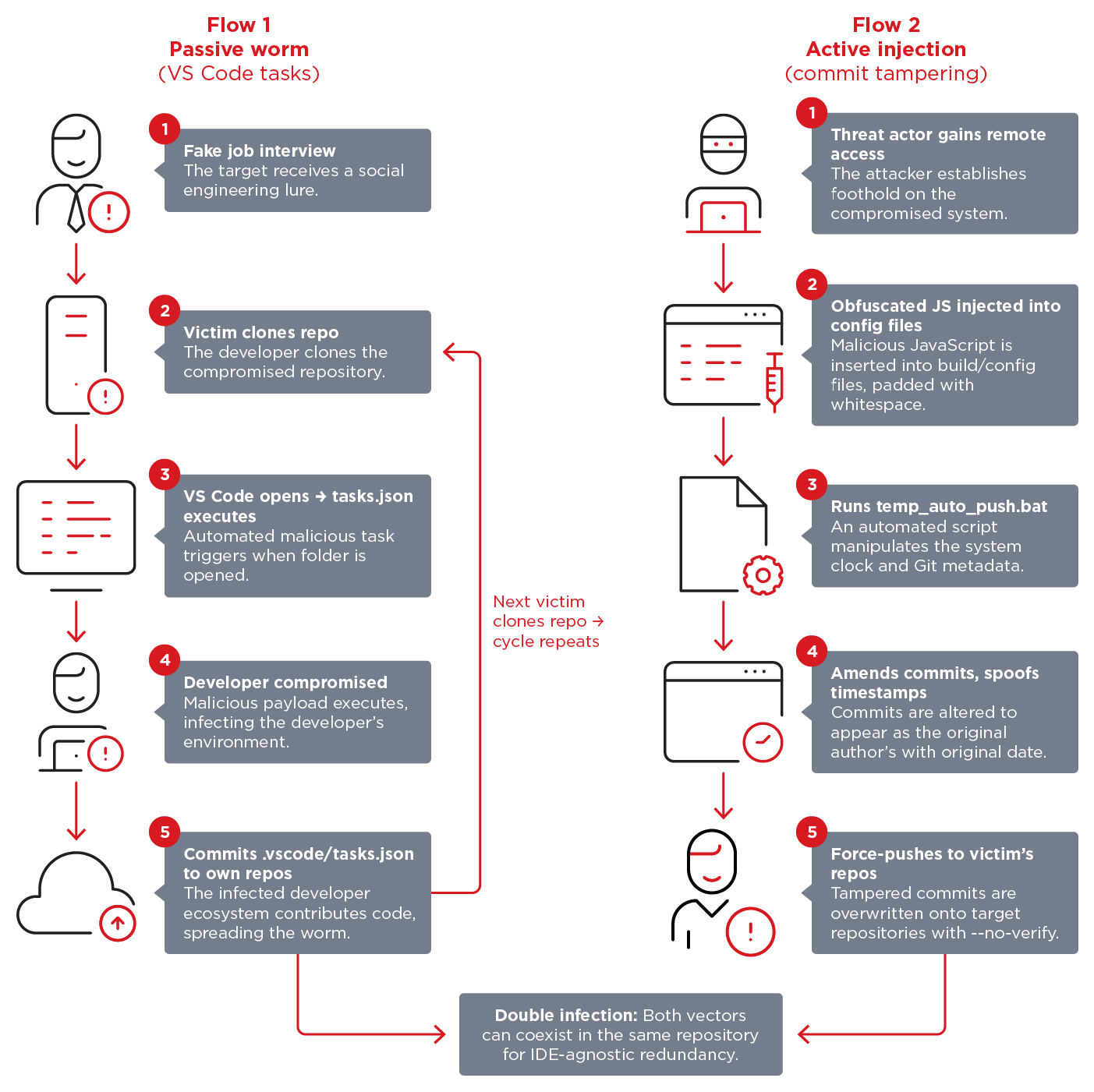
Void Dokkaebi (Famous Chollima): Here's another one of those reports that looks at a North Korean APT group, Void Dokkaebi in this case, using fake job interviews as a lure to get targets to open malware stored in GitHub repositories disguised as job application tests. This appears to be the same group that is also behind the TasksJacker campaign spotted last month.
Vulnerabilities, security research, and bug bounty
KEV update: CISA has updated its KEV database with eight new vulnerabilities that are being exploited in the wild.
- CVE-2023-27351 - PaperCut NG/MF Improper Authentication Vulnerability
- CVE-2024-27199 - JetBrains TeamCity Relative Path Traversal Vulnerability
- CVE-2025-2749 - Kentico Xperience Path Traversal Vulnerability
- CVE-2025-32975 - Quest KACE Systems Management Appliance (SMA) Improper Authentication Vulnerability
- CVE-2025-48700 - Synacor Zimbra Collaboration Suite (ZCS) Cross-site Scripting Vulnerability
- CVE-2026-20122 - Cisco Catalyst SD-WAN Manager Incorrect Use of Privileged APIs Vulnerability
- CVE-2026-20128 - Cisco Catalyst SD-WAN Manager Storing Passwords in a Recoverable Format Vulnerability
- CVE-2026-20133 - Cisco Catalyst SD-WAN Manager Exposure of Sensitive Information to an Unauthorized Actor Vulnerability
Bridge:Break vulnerabilities: Security researchers have found 22 vulnerabilities in serial-to-IP bridges from Lantronix and Silex. The devices are used to connect industrial equipment to normal IT networks. Forescout says the vulnerabilities can be exploited to take over the bridges and modify data, potentially enabling attacks on industrial equipment.
SGLang RCE: An unpatched vulnerability allows threat actors to run malicious code on AI servers via malicious GGUF model files. The vulnerability is in SGLang, a framework used to load AI models. Attackers that can feed malicious model files to AI servers running SGLang can abuse the bug to run their own malicious code. The SGLang project has yet to answer researchers and issue a patch.
Google Antigravity prompt injection: Pillar Security has found a prompt injection in Google's Antigravity agentic IDE that can lead to remote code execution attacks.
Anthropic deploys rogue files: The Claude desktop app is granting itself permission to access browser data, even if some browsers haven't even been installed on a user's PC. The app was spotted placing config files in preset locations for Chromium-based browsers like Brave, Chrome, Edge, or Vivaldi. The config files pre-authorize Claude to interact with the browser even before the user installs it. Researchers say this is a dark pattern that puts user data in danger. [The Privacy Guru]
Can confirm this for Arc, Brave, Edge, Chromium, Vivaldi on my machine: #Anthropic secretly installs spyware when you install Claude Desktop www.thatprivacyguy.com/blog/anthrop...
— Matthias Ott (@matthiasott.com) 2026-04-20T15:11:09.602Z
Infosec industry
Threat/trend reports: BlackBerry, CEPS, Cloud Security Alliance, Cobalt, GreyNoise, JET-CSIRT, Keepit, and NordVPN have recently published reports and summaries covering various threats and infosec industry trends.
Cybersecurity budgets are drying up in Russia: As the Russian economy is hitting a wall, Russian companies are reporting smaller and smaller cybersecurity budgets as most companies are barely getting by. [CNews]
New tool—Clickdetect: Security researcher Vinicius Morais has released Clickdetect, a generic alerting and detection engine that supports any data source and integrates with any webhook.
Risky Business podcasts
In this edition of Seriously Risky Business, Tom Uren and Amberleigh Jack talk about a new Citizen Lab report into Webloc, a tool to identify and track mobile devices. It demonstrates how the collection and sale of mobile phone geolocation data presents privacy and national security risks.
In this episode of Risky Business Features, James Wilson is joined by Brad Arkin who provides a CISO’s perspective on Anthropic’s Mythos. As former CISO at Adobe, Cisco and Salesforce, Brad’s perspective challenges the notion that finding and fixing exploits makes us safer.




