Risky Bulletin: FCC relaxes foreign router ban to allow for security updates
In other news: ShinyHunters disrupts schools across US; 21-year-old RCE found in FreeBSD; and another Linux zero-day LPE.

This newsletter is brought to you by Knocknoc. You can subscribe to an audio version of this newsletter as a podcast by searching for "Risky Business" in your podcatcher or subscribing via this RSS feed. You can also add the Risky Business newsletter as a Preferred Source to your Google search results by going here.
The US Federal Communications Commission has updated its ban on foreign-made routers to allow vendors to ship security updates for a longer period of time.
The agency banned the sale of foreign routers in March, but allowed companies to ship security updates for one more year until March 2027.
The FCC says that based on comments from the government and private sector it has now updated this cutoff date to January 1, 2029.
The exemption applies only to security updates that "mitigate harm to consumers" and foreign companies are not allowed to ship new features via this mechanism.
It also covers WiFi hotspot devices, which the FCC considers part of the router category.
The same exemption and new cutoff date for security updates also applies to foreign made drones, which the FCC banned in December and put a cutoff date of January 1, 2027.
While the US government hinted last year at banning Chinese companies DJI and TP-Link from selling their drones and routers in the US, a blanket ban on foreign-made drones and routers came out of the blue and shocked everyone in the industry.
The constant updates these two bans have received on almost a bi-weekly pace shows how little the agency has thought of the possible long-term consequences of its decision.
You'd think a comms regulator would have known networking devices usually remain in their networks for at least a decade and need to receive security updates. Even this two-year extension is not sufficient when we're dealing with routers and hotspots.
You're probably fine with drones, but routers stay connected to the internet at all times and create a wide attack surface for the US companies that still rely on them.
Risky Business Podcasts
The main Risky Business podcast is now on YouTube with video versions of our recent episodes. Below is our latest weekly show with Pat, Adam, and James at the helm!
Breaches, hacks, and security incidents
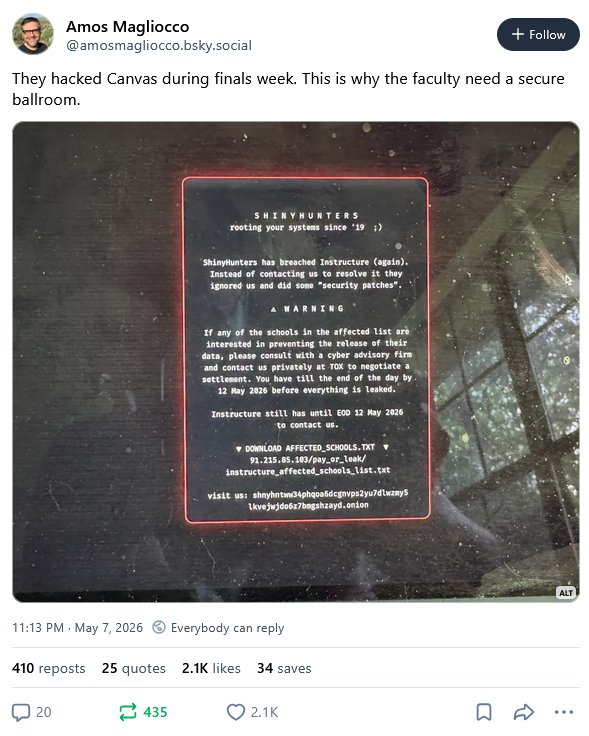
ShinyHunters disrupts classes across US: Hackers have breached and defaced the student management platform of edTech company Instructure. The company placed the Canvas platform in maintenance mode last week after the hackers posted ransom notes on the login screens of some schools. The initial breach took place last month but the ShinyHunters group defaced the login portals after Instructure failed to pay a ransom. The defacement prevented some schools from accessing the platform during end-of-year exams. [TechCrunch // KrebsOnSecurity // Instructure]
TrustedVolumes crypto-heist: Hackers have stolen $6.7 million worth of crypto assets from DeFi platform TrustedVolumes. [Decrypt]
NVIDIA confirms breach: Hackers have stolen the personal data of NVIDIA users who registered for the GeForce NOW service. The breach only impacts Armenian users. NVIDIA says hackers stole the data from the servers of a local regional partner. [NVIDIA // BleepingComputer]
Mexican water utility hacked with AI: Hackers using Anthropic and OpenAI coding assistants breached a water utility in Mexico. The breach took place in February and was part of a larger AI-assisted campaign that targeted the Mexican government for more than three months. The hackers used the AI tools to adapt public available offensive security tools and turn them into a custom hacking framework. The same campaign also breached the Mexican National Electoral Institute and three state governments. [Dragos // CybersecurityDive]
JDownloader got hacked: The website of the JDownloader download manager was hacked and modified to distribute a remote access trojan (RAT). Hackers inserted malware in the app's Windows and Linux installers. The incident took place last week, and the malicious installers were live on May 6 and 7. The attackers didn't ship malicious updates so only new installs should be affected.
Optimed hack: One of Poland's largest medical laboratories has blamed a recent security breach on a Belarussian cybercrime group. Which one? They didn't say, and local media doesn't seem to know either.
Checkmarx hack update: Security firm Checkmarx, which has been dealing with a hack of its GitHub repos, says that hackers have now published a malicious version of its Jenkins AST plugin, which they are in the process of dealing with.
SailPoint breach: SailPoint disclosed a hack of its GitHub repositories via a third-party tool. This is likely connected to the TeamPCP Trivy/KICS supply chain attacks. [h/t Zack Whittaker]
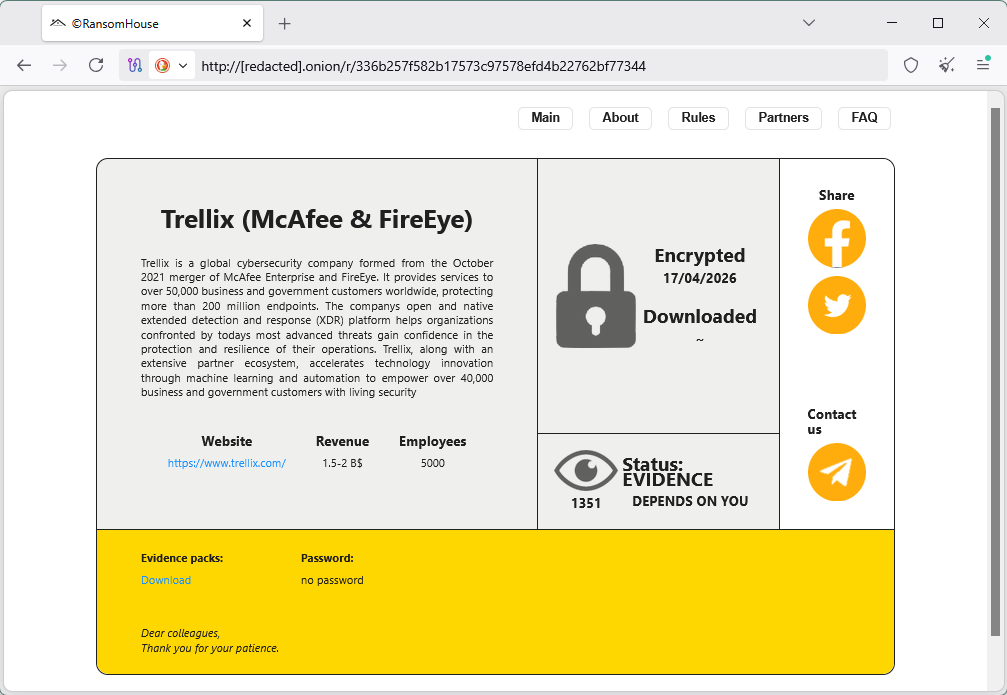
RansomHouse claims Trellix hack: The RansomHouse ransomware group has taken credit for a breach at security firm Trellix. The breach exposed some of the company's source code.
Honduras Gate scandal and subsequent attacks: The Honduras Gate website has faced waves of DDoS attacks after releasing audio recordings of a multi-national plot to destabilize liberal democracies across Latin America. The recordings exposed a secret plan backed by the governments of Argentina, Israel, and the US to fund a platform to publish fake news and misinformation to destabilize the left-wing governments of Brazil, Colombia, and Mexico. Argentinian president Javier Milei has allegedly pledged to contribute $350,000 to the effort. The platform received the blessing of Donald Trump and would be coordinated by former Honduran president Juan Orlando Hernandez. The recordings claim that Israel lobbied Donald Trump to pardon Hernandez earlier this year specifically for this operation. [Hondurasgate // El Pais // La Jornada]

39,618 intentos de ataque a nuestro portal en un solo día. La geolocalización expone un patrón claro y dirigido: los vectores de ataque se concentran específicamente en Estados Unidos e Israel. Adjuntamos el mapeo de la telemetría. pic.twitter.com/SYNjIVsuhl
— Honduras Gate (@HondurasGate) May 8, 2026
General tech and privacy
OpenAI rolls out Spud: OpenAI has rolled out a more permissive AI cybersecurity model for organizations that manage critical infrastructure. The new Spud model was designed for "defensive work, with strong safeguards against misuse. Sources told Axios the model was roughly on par with Anthropic's Mythos. [Axios // OpenAI]
The Dutch fine Yango: The Dutch data protection authority has fined ride-hailing app Yango €100 million for storing the data of Dutch citizens on servers in Russia. The app launched in 2018 and was developed by the former Yandex Taxi team. Finnish and Norwegian authorities previously warned the company in 2023 to stop processing the data of their citizens in Russia.
GM gets a tiny fine: California's data protection agency has fined GM $12.75 million for selling driver driving behavior data to car insurers, which then used the information to increase insurance policies using vague or arbitrary reasons. [CCPA // The Record]

Let's Encrypt stops issuance: Let's Encrypt stopped issuing TLS certificates for almost three hours last week due to a compliance issue.
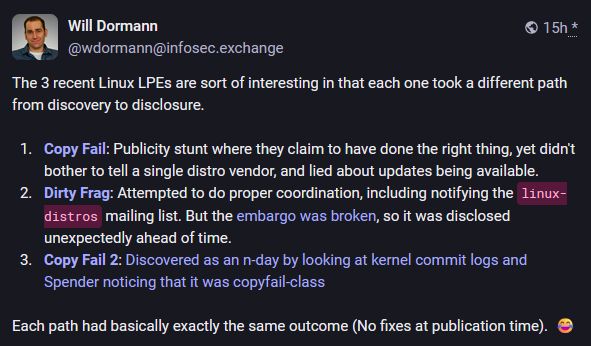
Linux kernel Killswitch feature: The Linux kernel team is reviewing a new proposed security feature that would temporarily disable kernel functions. The new Killswitch feature was proposed following the recent botched disclosures of the Copy Fail and Dirty Frag vulnerabilities. Admins will be able to use Killswitch to disable vulnerable kernel features until patches are available.
Google sabotages de-Googled smartphones: The latest version of the Google reCAPTCHA service blocks Android smartphones from passing a verification and accessing websites if they run a deGoogled Android OS. The blocks are taking place because Google has tied reCAPTCHA to the Google Play service, which is intentionally removed from those devices to prevent Google from tracking users. [ReclaimTheNet]
"The iOS comparison is revealing because Apple devices running iOS 16.4 or later complete the same verification without installing any additional apps. Google didn’t demand iPhone users install Google software to pass the test. Only Android users who refuse Play Services get locked out. The asymmetry reveals what this is really about: not security, but ecosystem control."
France opens investigation of Musk and Twitter (X): French prosecutors have opened a formal criminal probe of social media company X, major shareholder Elon Musk, and former CEO Linda Yaccarino. The Paris Public Prosecutor Office is investigating the company for spreading child sexual abuse images and pornographic deepfakes. French authorities raided X's Paris offices in February. Both Musk and Yaccarino declined to show up for voluntary hearings. X is also under investigation in multiple other countries after its Grok AI generated nude images, including of children. [CNBC // Paris Prosecutor's Office, PDF]

Government, politics, and policy
FCC wants KYC for telcos: The FCC wants American mobile operators to verify the identity of all their customers before activating their service or renewing a contract. Under a new proposed rule, telcos will be required to implement strong Know-Your-Customer measures going forward. The agency says the measure is intended to reduce the number of robo calls. Customers will need to provide a real name and address, along with a copy of a government-issued ID. The proposed rule enters a public comments stage. [JDSupra]
CyberCorps scholarship rebrands to AI: The White House has rebranded the CyberCorps Scholarship For Service program to the CyberAI SFS. The program will refocus on teaching students to use AI for cybersecurity work. None of the 300 students enrolled in the program knew the change was coming. [CyberScoop]
EU calls VPNs a "loophole": The EU's research service has described VPNs as loopholes, as they allow children to bypass age-verification checks. [EU Research Service]
Sponsor section
In this Risky Business sponsor interview, Patrick Gray chats with Knocknoc CEO Adam Pointon about their Greynoise integration.
Arrests, cybercrime, and threat intel
Trenchant exec on the hook for an extra $10m: Former Trenchant executive Peter Williams has been ordered to pay $10 million in restitution to his former employer and its parent company L3 Harris. Williams was sentenced to 87 months in prison earlier this year for selling Trenchant's exploits to a Russian company. The initial sentence also carried a $1.3 million restitution, bringing Williams' total owed to $11.3 million. Trenchant and L3 Harris initially asked the court to approve a $35 million payout for the damage he caused. [Zero Day]
Infosec exec arrested in CSAM investigation: French authorities have arrested a cybersecurity executive for allegedly buying child sexual abuse material from the dark web. Filigran founder Samuel Hassine is allegedly one of the 232 individuals identified by police as buyers on the "Alice with Violence CP" portal. Hassine was supposed to travel to Japan and South Korea as part of the French delegation for Emmanuel Macron's official visit. [Le Libre Penseur // Geopolintel] [h/t M.T.]
Twin pleads guilty to destroying govt DBs: A 34-year-old man from Virginia has pleaded guilty to deleting almost 100 government databases. Sohaib Akhter, together with his twin brother, stole data and deleted databases minutes after they were fired from their government contractor roles. The incident impacted multiple government agencies, including the IRS and the DHS. The brothers allegedly asked an AI chatbot how to remove logs of their actions. Akhter will be sentenced in September. He faces up to 21 years in prison.
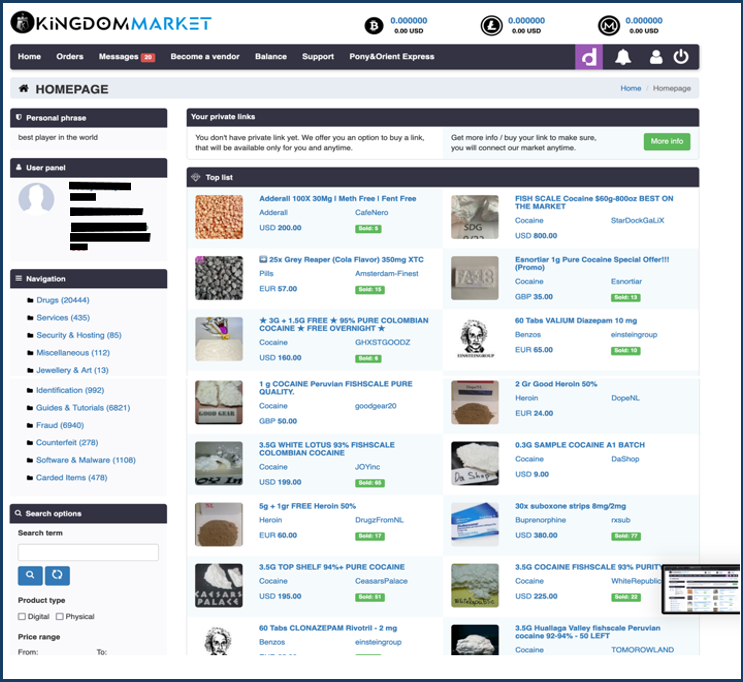
Kingdom Market admin sentenced to prison: A Slovakian national was sentenced to 16 years and eight months in prison for running the Kingdom dark web marketplace. Alan Bill, 33, was one of the site's admins. He managed the Kingdom's web portals, and promoted its products on Reddit and on Dread. Bill was arrested in the US days before German authorities seized the site in December 2023.
Crimenetwork 2 takedown: German authorities have arrested a 35-year-old man who tried to relaunch the Crimenetwork dark web marketplace. The original platform was seized and shut down by authorities at the end of 2024. The new platform launched last year and amassed more than 22,000 users before being seized as well. The site's admin was detained at his home on the island of Mallorca, in Spain.
WhatsApp bans scam accounts in India: Meta has banned 9,400 WhatsApp accounts that posed as government and law enforcement agencies. The accounts were involved in "digital arrest" scams. They contacted victims and requested payment for the release of family members. Most of the accounts were run from Cambodian scam compounds. [NDTV]
Hackers hate genAI too: Cybercriminals are just as annoying with AI-generated slop being posted in underground hacking forums and AI-generated malware as the rest of us. [arXiv // WIRED]
Vercel abuse: Vercel is seeing increased abuse, being commonly used these days to store phishing pages or parts of their code. [Cofense]
Tiflux abuse: Threat actors have found a new RMM tool to abuse, namely Tiflux, a remote management product mainly used in Brazil. [Huntress]
HuggingFace malware: A malicious credentials harvester was found in a popular HuggingFace repository named Open-OSS/privacy-filter. At the time of the discovery, the repository was listed as #1 in HuggingFace's trending section with more than 240,000 downloads. The repo was later removed by the HuggingFace team. Researchers believed the attackers manipulated the platform's Likes feature to help boost the repo's visibility. [HiddenLayer]
npm abused for config storage: A cluster of three npm accounts used 51 libraries over the past four years to abuse npm as a config storage system for their mobile apps. The apps belonged to Chinese sports gambling and pirate streaming platforms. [Panther]
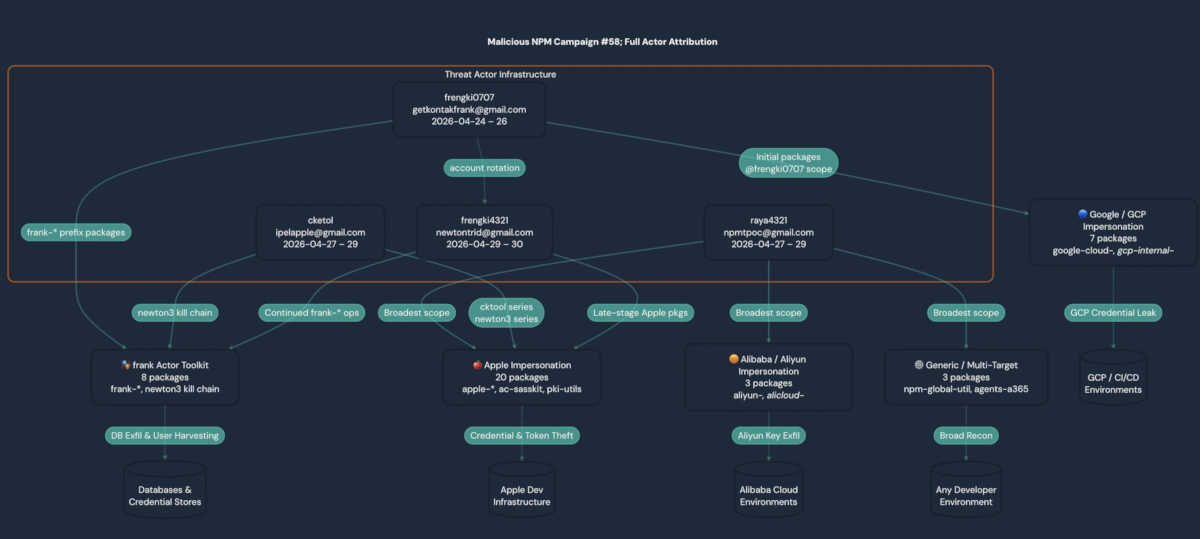
Malicious npm packages: A cluster of 38 malicious npm libraries targeted the internal networks of large tech companies like Apple, Alibaba, and Google. The campaign attempted to compromise dev machines by leveraging a technique known as dependency confusion. The packages deployed malware that attempted to steal npm publish tokens, suggesting the goal was malicious and not bug bounty research. Security firm Panther linked the campaign to "a single Indonesian-speaking threat actor." [Panther]
Malware technical reports
Doko's Panel: Push Security has gained access to Doko's Panel, one of the phishing kits used by groups like ShinyHunters and BlackFile. [Push Security]
Needle MaaS: Security researchers extracted an API key from the Needle malware and then enumerated its backend to retrieve a list of 1900+ victims. The malware is an infostealer with a focus on crypto. [Beelzebub]
Lorem Ipsum backdoor: A new Windows backdoor malware tracked as Lorem Ipsum has been discovered being distributed via poisoned SEO results for Microsoft Teams installers. [BlueVoyant]
"The Lorem Ipsum campaign represents the emergence of a capable, well-resourced, and rapidly maturing mid-tier criminal threat actor whose operational tempo warrants proactive defender attention. The combination of validly signed installers, multi-stage in-memory loader chains, JFIF-disguised C2 traffic, per-victim UUID tracking, and creative dead-drop abuse of a legitimate regional platform produces a meaningfully harder-to-detect delivery and command profile than typical commodity operations, while sustained operational expenditure on disposable domains, short-lived signing certificates, and dedicated hosting points to a meaningful and recurring budget."
PamDOORa Linux backdoor: A threat actor is selling a Linux backdoor named PamDOORa on hacking forums. The developer claims the backdoor can tap into the Linux Pluggable Authentication Module (PAM) stack for persistence. [Flare]
"The threat actor reduced the asking price by nearly 50% (from $1,600 to $900), suggesting either limited buyer interest or an attempt to accelerate a sale."
Jenkins DDoS botnet: A new botnet operation is hacking into Jenkins servers to deploy DDoS malware that attacks game servers. The botnet is targeting Jenkins servers that have left their scripting interface exposed online. The attacks target Jenkins servers running on both Linux and Windows. [Darktrace]
Sponsor section
In this product demo, Knocknoc CEO Adam Pointon walks Patrick Gray through the Knocknoc secure access platform. Knocknoc is a platform that restricts network and service availability to authenticated users via existing network security equipment. Users don't need to install an agent. It also has an identity-aware proxy component that supports web applications and RDP.
APTs, cyber-espionage, and info-ops
NZ sanctions Russian cyber actors: The New Zealand government imposed sanctions on several Russian cyber actors that support Russia's war in Ukraine. Sanctions were levied against Structura and the Social Design Agency, two companies involved in influence operations. Sanctions were also levied against three bulletproof hosting providers, the Aeza Group, MediaLand, and MLCloud. The sanctions targeted the companies as well as their executives. They echo similar sanctions imposed by the US, the EU, the UK, and Australia.
Argentina detains La Compañía disinfo network boss: Argentina has arrested and deported a Russian national linked to a Kremlin disinformation network. Dmitry Novikov, 26, was one of the managers of a group known as "La Compañía" that used fake news and disinformation to attack Latin American governments that support Ukraine. Novikov was also arrested and deported from the Dominican Republic for the same reason last September. [United24] [h/t Daria88S]
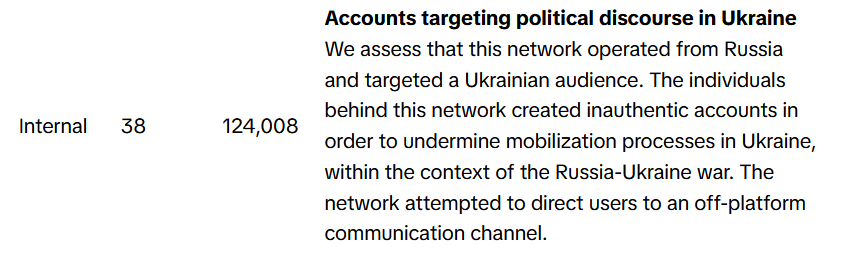
TikTok info-ops summary: TikTok has published its monthly report on covert influence operations the company has spotted on its platform in March this year. The company took down info-ops targeting audiences in Indonesia, Ukraine, Bulgaria, Colombia, Hungary, Armenia, Moldova, and Georgia. Most of these networks have a connection with Russia, promoted Russian interests, or were run from Russia.
Vulnerabilities, security research, and bug bounty
Security updates: ABB, cPanel, Thunderbird.
LiteLLM exploitation: Hackers are exploiting a recent SQL injection vulnerability to take over LiteLLM AI servers. Tracked as CVE-2026-42208, the vulnerability allows unauthenticated attackers to read or write to the server's database. Exploitation is simple and only requires that attackers use a specially crafted Authorization header when interacting with the LiteLLM server. The issue was found by Tencent and patched last month.
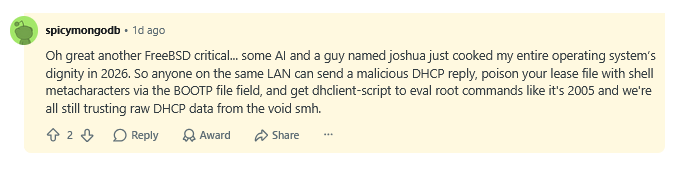
21yo FreeBSD RCE: The FreeBSD team has patched a remote code execution in its operating system that impacts all versions released since 2005. Tracked as CVE-2026-42511, the vulnerability resides in the FreeBSD DHCP client. Threat actors on the same LAN can use maliciously crafted DHCP responses to run code on the OS using root privileges. Exploitation doesn't require any user interaction. [Aisle Security]
"Any attacker able to operate a malicious DHCP server on the same broadcast domain, or spoof one (DHCP is unauthenticated), can feed hostile lease data to the client. On wired networks, that may mean a rogue device on the local segment. On wireless networks, it may mean a malicious access point or, in some environments, another attacker on the same Wi-Fi network able to inject or spoof DHCP traffic. Because DHCP is the default way most systems obtain network configuration, this issue is relevant to a significant portion of FreeBSD deployments."
ClaudeBleed vulnerability: A vulnerability in the Google Chrome Claude extension can allow threat actors to take over the AI agent using hidden prompts and then abuse it to extract and steal browser data. Anthropic didn't fully patch the attack vector, which is still possible. [LayerX]
Yarbo lawn mower vulnerabilities: Security researcher Andreas Makris has found three vulnerabilities in Yarbo autonomous lawn mowers and snow blowers that can be used to remotely take over the devices. [The Verge]
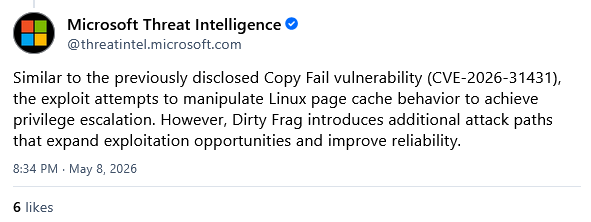
Dirty Frag Linux zero-day: Linux distros are hurrying to patch a new vulnerability disclosed last week going by the name of Dirty Frag (CVE-2026-43284). Details and proof-of-concept code were published after a security embargo was broken on Thursday. The vulnerability is a privilege escalation bug that can allow attackers with access to a system to run malicious code as root. Dirty Frag impacts all Linux distros released since 2017. It is the second Linux security flaw disclosed to the public this month without having proper patches after a first one named Copy Fail. In the meantime, researchers also found a variant of the Copy Fail bug, named Electric Boogaloo. [AWS // Microsoft // Qualys // Red Hat // Wiz]
Infosec industry
Threat/trend reports: Arete, BlackFog, Capital One [PDF], DCSO, HiddenLayer, Human Security, Rostelecom, and Thales have recently published reports and summaries covering various threats and infosec industry trends.
Cloudflare layoffs: Cloudflare will lay off more than 1,100 employees as it incorporates AI tooling into its processes. The layoffs will take place during the second quarter and cover almost a fifth of the company's total workforce. Cloudflare shares dropped 19% last week, but they are up 30% for the entire year. [Reuters]
The disappearing complex malware write-ups: Security researcher Dominik Reichel published an op-ed looking at how and why there are fewer and fewer in-depth reports on complex malware and hacking techniques. I fully agree with Dominik here and it's basically some of the same stuff I would have told you too. The cybersecurity landscape is repetitive content, the same blog post after the same blog post, and I'm the cursed one who has to read it for this newsletter. :((
New tool—Fenrir: Security researcher Tahaa Farooq has released Fenrir, a credential harvesting framework leveraging eBPF.
SREcon Americas 2026 videos: Talks from the USENIX SREcon 2026 Americas conference, which took place in March, are now available on YouTube.
DistrictCon 2026 videos: Talks from the DistrictCon 2026 security conference, which took place in January, are available on YouTube.
Risky Business podcasts
In this episode of Risky Business Features, James Wilson chats with Niels Provos about his research into using older AI models to successfully hunt for 0day vulnerabilities.




