Risky Bulletin: EU finally imposes more cyber sanctions
In other news: US-Israeli strikes killed Iranian cyber chief; UK fixes major bug in Companies House portal; celebrity phisher continued phishing while in detention.

This newsletter is brought to you by Sublime Security. You can subscribe to an audio version of this newsletter as a podcast by searching for "Risky Business" in your podcatcher or subscribing via this RSS feed.
The European Union on Monday imposed sanctions on three hacking groups and two individuals for cyberattacks on its member states.
Sanctions were imposed on Iranian cyber contractor Emennet Pasargad for its hack of French satirical magazine Charlie Hebdo, the 2024 Paris Olympic Games, and a Swedish SMS service.
This is the same group that also meddled in the 2020 US Presidential Election and was later sanctioned three times by the US as well, in 2021, and September and December 2024.
Emennet works under Iran's Islamic Revolutionary Guard Corps (IRGC) and has carried out both stunt-hacks and influence operations.
In addition, the EU also imposed sanctions on two Chinese cyber contractors.
The Integrity Technology Group was sanctioned for running the Raptor Train botnet, while Anxun Information Technology, also known as i-SOON, was sanctioned for espionage campaigns that targeted EU member states.
Both of these groups were also sanctioned by the US Treasury last year, in January and March.
Integrity, a Beijing based company, hacked smart devices and home routers, assembled them into a botnet, and provided that botnet to a Chinese APT group named Flax Typhoon to hide the origin of its attacks as coming from a bunch of residential IP addresses.
i-SOON is a lesser known cyber contractor that came into the limelight in early 2024 when a trove of internal documents were leaked online. The files exposed the company as a cog in China's larger cyber contractor ecosystem and tied its tools and operators to opportunistic espionage operations all over the world.
The leak eventually led to the US indicting the company's two co-founders and eight of their employees. This week's EU sanctions also cover the two i-SOON founders.
Risky Business Podcasts
We launched a new podcast series called Risky Business Features. In this episode James Wilson takes a (ridiculously) deep dive into the Coruna exploit kit.
Breaches, hacks, and security incidents
Companies House mega-bug: The UK government shut down its business web filing service to fix a major vulnerability. The bug could have allowed threat actors with an account on the Companies House portal to view and edit the registration data of other companies. Exploiting the bug required pressing the Back key four times while in the "File for another company" section. Backing out would return the attacker to that company's dashboard with full rights. [Tax Policy Associates] [h/t Sam Bultitude]
OK this is nuts. A vulnerability in the Companies House website that let *anyone* with an account view ***ANY COMPANY'S DASHBOARD***, see all personal info and - I think - modify company records.
— Dan Neidle (@danneidle.bsky.social) 2026-03-13T17:44:11.291Z
Denver crosswalk defacements: Suspected hacktivists have hacked Denver crosswalks to play anti-Trump messages. Crosswalks were modified to play "The walk signal is on, fuck Trump. The walk signal is on, Trump murders children." The hacked devices were disconnected over the weekend. [The Denver Post]
DeKalb ransomware attack: A ransomware attack has disrupted the Sheriff's Department and jail in DeKalb County, Tennessee. The incident has impacted the email servers and the inmate booking system. [DysruptionHub]
Epe breach: Hackers have stolen more than 800 GB of data and 600,000 documents from the Dutch city of Epe. The incident took place last week. It was traced to an employee falling to a ClickFix attack and installing malware on their system.
Sears incident: American retailer Sears left databases from its AI chatbot service exposed online. The databases leaked text and audio logs. [Express VPN]
Intuitive incident: Intuitive, a medtech company that builds surgical robots, has disclosed a security breach linked to a phishing incident. [MedTech Dive]
Mullenweg phishing incident: WordPress creator Matt Mullenweg published a blog post over a recent phishing incident that almost got him.
A scammer was so good at impersonating Apple Support that Matt Mullenweg thanked him for excellent customer service. Then came the phishing link. The attack worked because it felt real. It was real, mostly. That's the bit that should worry you. https://ma.tt/2026/03/gone-almost-phishin/
— Javvad Malik (@j4vv4d.com) 2026-03-17T09:00:19.456236+00:00
General tech and privacy
Age verification provider fined for privacy issues: Spain's data privacy regulator has fined an age verification provider €950,000 for GDPR privacy violations. Yoti allows users to take a selfie and upload a copy of their ID, and then confirm to an online platform that the user is over a specific age without sharing any of their data. Spain's privacy watchdog says Yoti used the collected data for research and development without consent or even prompting users for it. [PPC Land // AEPD ruling PDF] [h/t RVD]
Court overturns Amazon privacy fine: A Luxembourg appeals court has overturned a €746 million fine against Amazon from the country's privacy watchdog. The retail giant was fined in 2021 for breaking the EU's GDPR privacy regulations. The appeals court overturned the fine after Amazon argued on a technicality that the privacy watchdog failed to analyse if it broke GDPR intentionally or by accident.
Digg shuts down beta after bot attack: Digg has shut down its attempted relaunch after the site was flooded with bots and AI-automated accounts. The company says it banned tens of thousands of accounts but just couldn't keep up with the flood. Digg laid off current staff but promised to rebuild its service and relaunch again. [Endgadget]
Alpha-Omega funding for security: Seven of today's top tech companies are offering $12.5 million in funding to open-source projects to improve their security. The seven are Anthropic, AWS, GitHub, Google, Google DeepMind, Microsoft, and OpenAI.
Industry Accord Against Online Scams and Fraud: Eleven companies have pledged to share threat intel with each other on scammers abusing their services. Signatories include the likes of Meta, Microsoft, Google, Amazon, and OpenAI. The companies will also create information sharing groups with law enforcement to accelerate legal takedowns. The new Industry Accord Against Online Scams and Fraud was signed ahead of the UN Global Fraud Summit in Austria this week.

Government, politics, and policy
US-Israeli strikes killed Handala boss: US and Israeli missile strikes have killed a high-ranking Iranian cyber official. Sources have told Forbes that Seyed Yahya Hosseiny Panjaki died in a strike at the end of last month. Pankaji served as a deputy minister of intelligence for Israeli Affairs at Iran's intelligence agency, the MOIS. He was also the leader of a cyber unit that controlled several Iranian hacking groups, including Handala. The group launched a destructive attack against US medical equipment maker Stryker last week.
Canada's Bill C-22: The Canadian government has introduced a new bill that would grant law enforcement agencies more legal powers to track individuals online. The new C-22 Bill upgrades Canada's lawful access laws to allow police access to information about a suspect's identity and possible location. Other details like browsing and social media history, and messages or emails will remain private. The government said it needs to update its antiquated lawful access law to account for the modern internet. [CBC]
DOE to release cyber strategy: The US Department of Energy is expected to release its first-ever cybersecurity strategy. [The Record]
Belgium's Phish Nemo project: Belgium police are offering a free database of phishing sites that telcos can implement and block malicious sites before users can access them. The project is called Phish Nemo.
Sponsor section
In this Risky Business sponsor interview, Catalin Cimpanu talks with Alex Orleans, Head of Threat Intelligence at Sublime Security, about the increase in email attacks leveraging Zoom invites and other video conferencing tools.
Arrests, cybercrime, and threat intel
Celebrity phisher indicted again: US authorities have charged a Georgia man for a phishing campaign that targeted NBA and NFL athletes. Kwamaine Jerell Ford posed as adult film stars and Apple customer support staff to trick victims into accessing phishing pages or handing over passwords. He used the passwords to access accounts, steal credit card details, and pay for personal items. Ford conducted the campaign while at home with an ankle monitor, while serving a prison sentence for another phishing-related charge.
"Fake Prince" scammer arrested in Nigeria: Nigerian authorities have arrested a man on suspicion of stealing $2.5 million from a Romanian businesswoman. The individual posed as Dubai's Crown Prince to trick the victim into sending money for a non-existent humanitarian project. The individual was arrested last month after being identified by a group of journalists. A second victim from Romania has also come forward since the original report. Court documents identify him as Nzube Henry Ikeji, 31, from Abuja, Nigeria. [OCCRP]
Forbidden Hyena: BI.ZONE has published a profile on a financially motivated threat actor named Forbidden Hyena. The group is known to use the Blackout Locker ransomware, recently rebranded to Milkyway.
Shady SDK is shady: A security researcher going by Buchodi has found an encrypted configuration file in the BIGO advertising SDK that can allow its SDK to bypass any domain bans on its main ad delivery network. Not shady at all! </sarcasm>
Malicious PyPI backdoor: Step Security has found a backdoor in a Python package that searches and exfiltrates Bittensor private key material.
Malicious npm versions: Step says a threat actor also compromised two popular npm packages for working with the React framework.
LSPosed abuse enables banking fraud: Threat actors are abusing an Android rooting framework for banking-related fraud. Attackers are deploying the LSPosed toolkit to hijack payment apps and make fraudulent logins and transactions appear as if they were coming from the real owner's devices. The technique allows attackers to bypass a process that binds smartphone IDs and SIM cards to payment app user accounts.
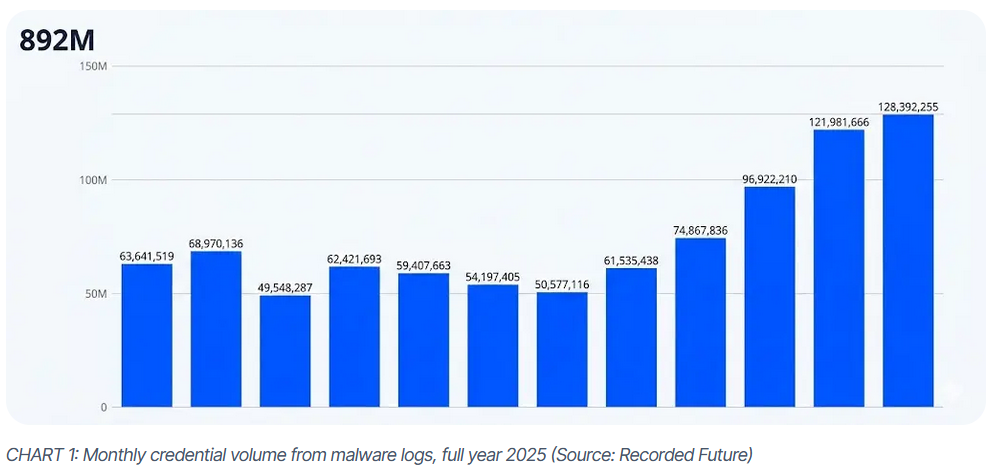
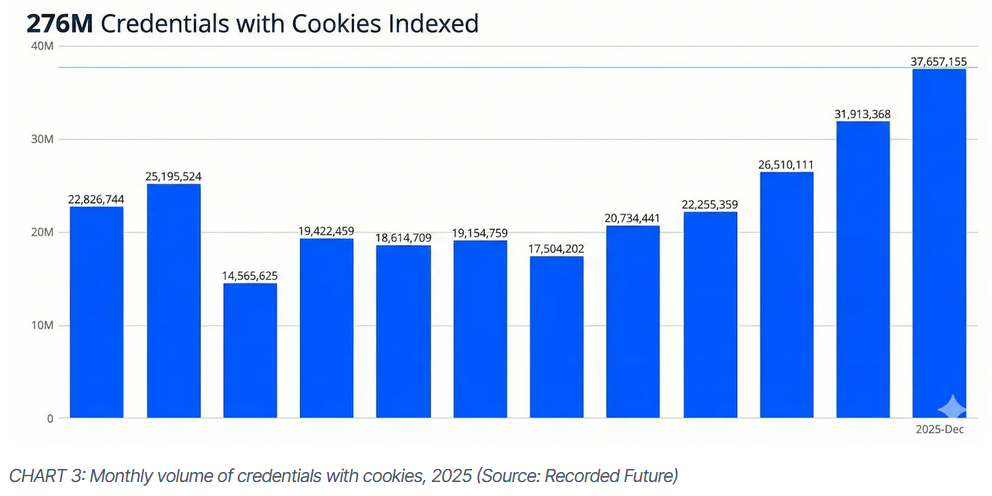
Stealer logs are everywhere: More than 890 million credentials were posted online for sale last year after being stolen using infostealers. Almost a third of the credentials also included cookies, which would allow attackers to bypass MFA challenges. Most of the stolen credentials came from LummaStealer infections. Lumma maintained its top stop even after law enforcement seized the malware's main infrastructure last May.
Ransomware ecosystem evolution: Google Mandiant has an end-of-year report on how the ransomware ecosystem did last year.
- In a third of incidents, the initial access vector was confirmed or suspected exploitation of vulnerabilities, most often in common VPNs and firewalls.
- 77 percent of analyzed ransomware intrusions included suspected data theft, a notable uptick from 57 percent of incidents in 2024.
- In approximately 43% of ransomware intrusions we responded to in 2025, the threat actors were observed targeting virtualization infrastructure, an increase from 29% in 2024.
- REDBIKE was the most frequently deployed ransomware family, accounting for 30 percent of analyzed ransomware incidents.
- Several trends from prior years remained consistent, including a decreased use of certain intrusion tools like BEACON and MIMIKATZ and a plateau in the reliance of remote management tools.

Malware technical reports
Katana botnet: A new IoT botnet has infected over 30,000 Android TV set-top boxes. Named Katana, the botnet exploited Android debug ports left exposed on the devices. The botnet uses a custom rootkit to persist on the devices and uninstalls itself if its command-and-control servers have been down for more than three days. According to Nokia's security team, Katana has already conducted DDoS attacks as large as 150 Gbps. [h/t Jérôme Meyer]
Spark Stealer: G DATA has published a report on Spark Stealer, an infostealer distributed through a massive campaign leveraging fake Minecraft mods.
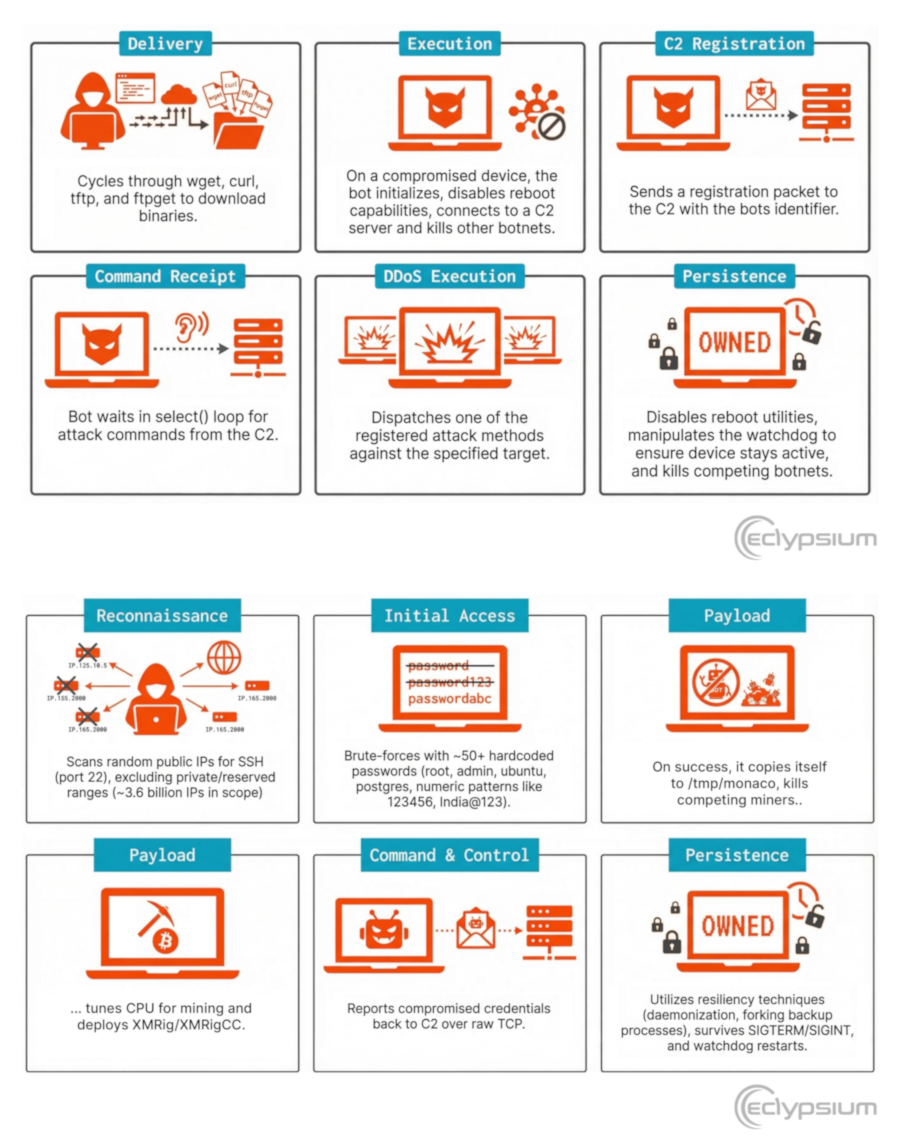
CondiBot and Monaco: Eclypsium has discovered two new malware strains, CondiBot, a new Mirai variant, and Monaco, a new SSH scanner and cryptominer.
GoPix: Kaspersky has spotted a new Windows banking trojan named GoPix targeting Brazil's Pix payment system. The malware works filelessly, performs local MitM attacks, and also intercepts and hijacks the clipboard.
Handala malware: Security engineer Patrick Duggan claims to have found a piece of malware used in the attack on US healthcare provider Stryker. It was uploaded on GitHub and was hidden in a file named CrowdStrike.bin.
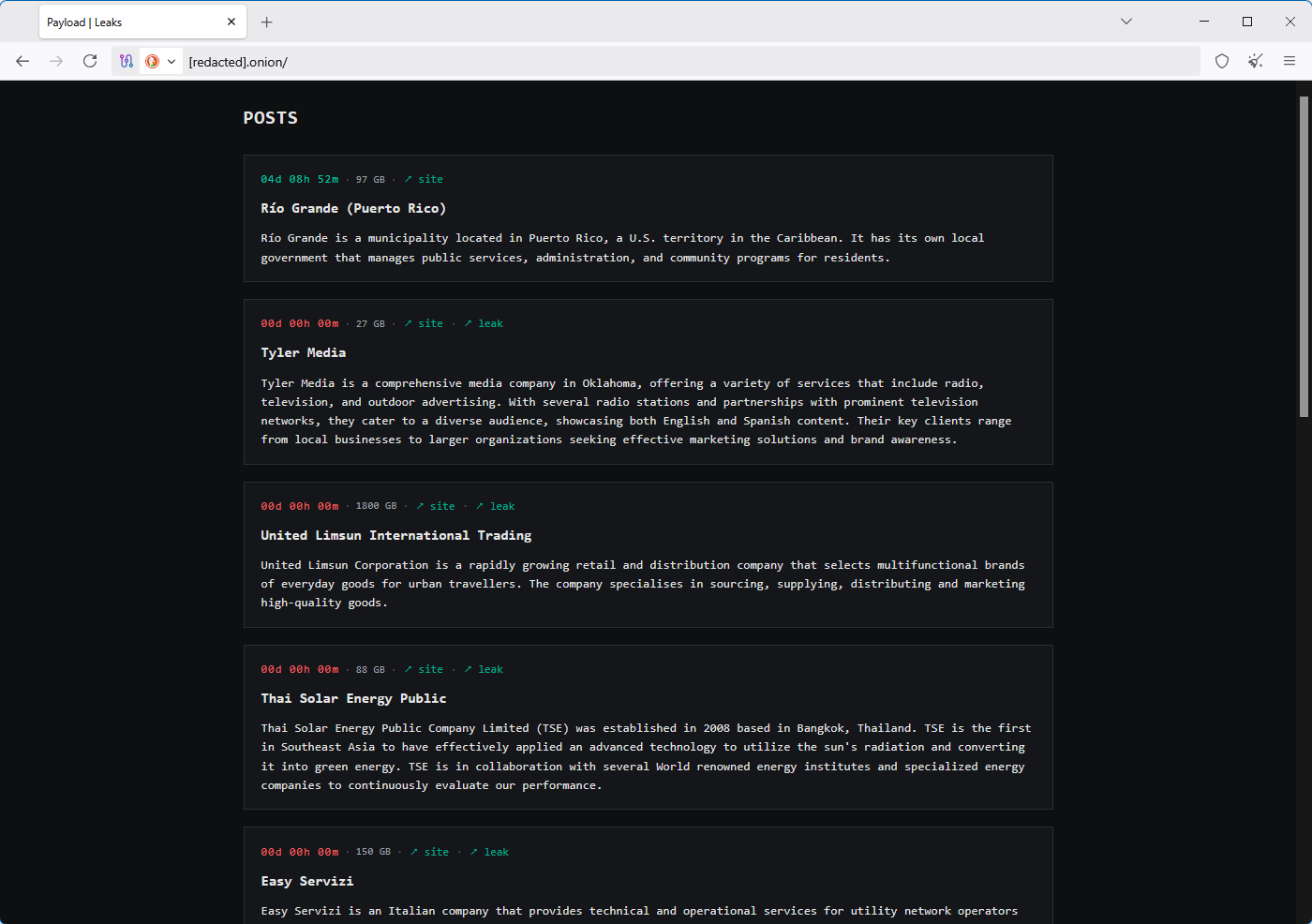
Payload ransomware: There's a new ransomware group in town named Payload.
Warlock ransomware: Trend Micro is seeing new activity from the Warlock ransomware group, an operation previously linked to Chinese operators.
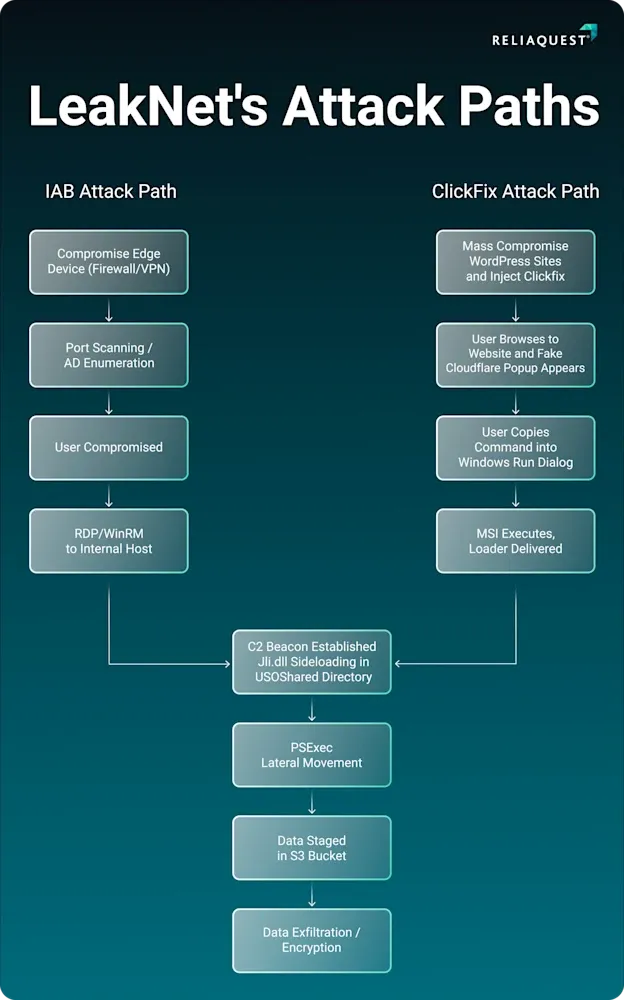
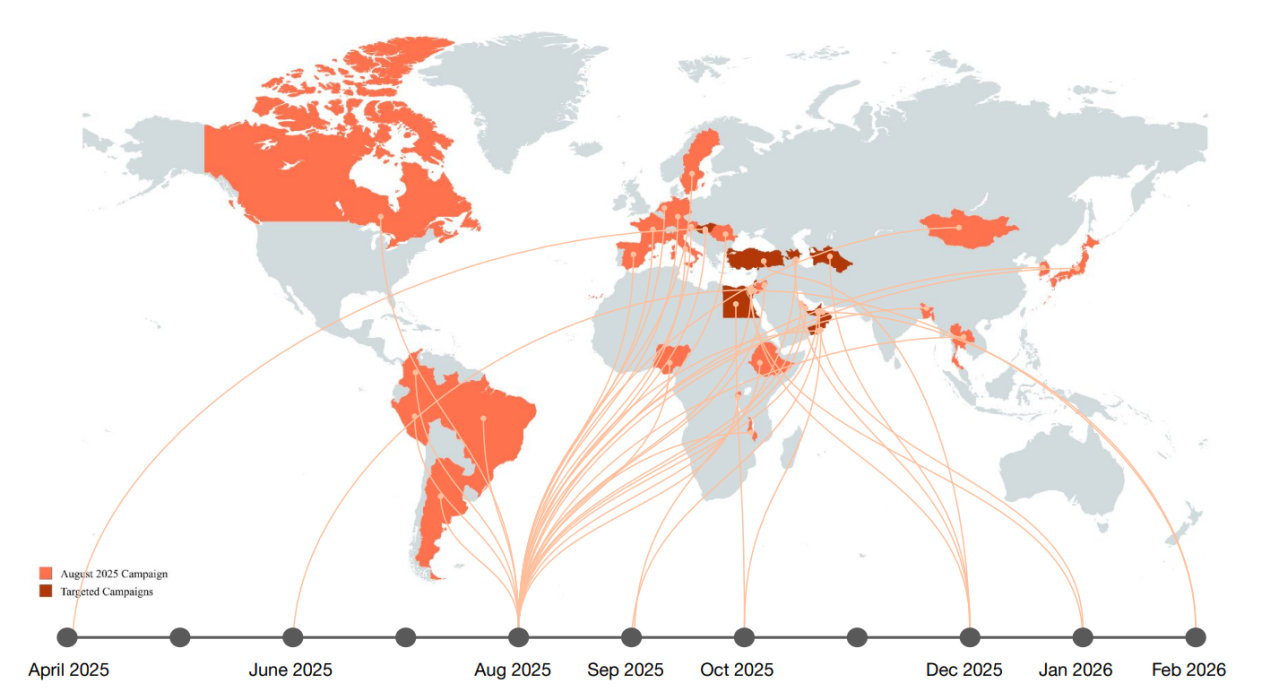
LeakNet ransomware: ReliaQuest looks at LeakNet, a new ransomware operation that launched last August and has now switched to using ClickFix campaigns for initial entry.
Sponsor section
In this sponsored product demo, Sublime Security co-founder and CEO Josh Kamdjou joins Risky Business podcast host Patrick Gray to show off the company's email security platform, including its latest agentic AI bells and whistles.
APTs, cyber-espionage, and info-ops
Chinese info-ops side with Iran: A NewsGuard report looks at the increasing evidence that Chinese influence operations are working to push Iranian narratives surrounding the US' attacks on the country.
RftRAT campaign: Genians looks at a suspected DPRK spear-phishing operation targeting human rights activists. The final payload was the RftRAT.
FAMOUS CHOLLIMA's PylangGhost RAT: Kieran Miyamoto (KMSec) has spotted new DPRK malware on npm.
New APT28 leak: After Hunt found an open directory hosting APT28's Roundcube exploit kit last week, Ctrl-Alt-Intel has now found a second APT28 open directory on the same server, this one holding the group's "C2 source code, additional payloads, telemetry logs, exfiltrated data and evidence of further campaigns."
Boggy Serpens (MuddyWater): Palo Alto Networks has published a report looking at Boggy Serpens campaigns over the past year, most of them relying on phishing for initial entry.
Vulnerabilities, security research, and bug bounty
Xbox One finally got hacked: Security researcher Markus Gaasedelen has used voltage glitching to finally hack the Xbox One, a product that survived almost 13 years without being jailbroken. [Tom's Hardware]
Wing FTP Server RCE: Threat actors are exploiting an RCE in Wing FTP servers. The bug was disclosed and patched last July.
Qihoo ships SSL private key: Qihoo included a SSL private key inside its AI assistant 360 Security Lobster, a commercial wrapper around the open-source AI agent OpenClaw.
CursorJack attack: Proofpoint has discovered CursorJack, a way to abuse Cursor MCP deeplinks (cursor://) for code execution or to install a malicious remote MCP server.
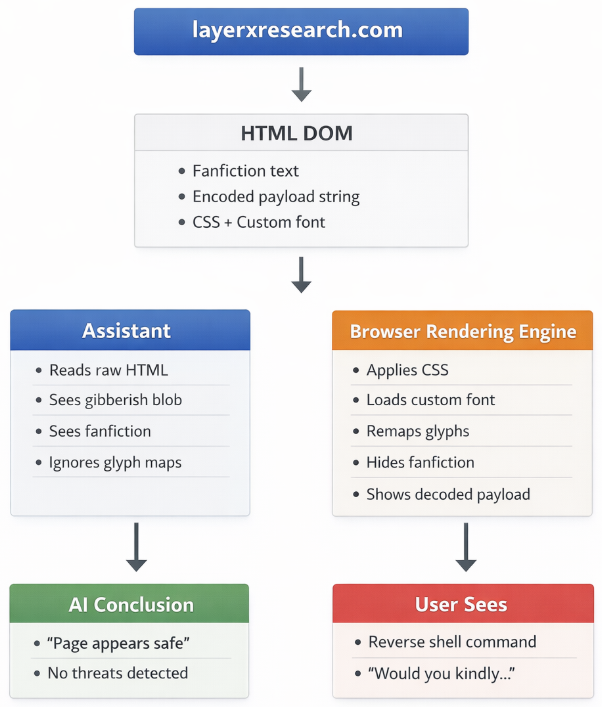
Poisoned Typeface attack: LayerX researchers have found a way to hide malicious AI prompts inside custom web fonts. The attack works because the AI agent reads the text but won't see the malicious instructions/content shown to the user.
Infosec industry
Threat/trend reports: Akamai, Armis, Booz Allen Hamilton, Google, Positive Technologies, and Recorded Future have recently published reports and summaries covering various threats and infosec industry trends.
Risky Business podcasts
In this edition of Between Two Nerds, Tom Uren and The Grugq discuss how bombing Iran changes incentives for Iranian hacker groups. Destroying other ways that Iran might project power could force it to double down on cyber capabilities.
In this edition of Seriously Risky Business, Tom Uren and Amberleigh Jack talk about the newly released Trump Cyber Strategy for America. The ideas in it are fine and occasionally even game-changing, but many of its goals have been undercut by the administration's actions to date.




