Risky Bulletin: Cybercrime losses passed $20 billion last year
In other news: Authorities disrupt APT28 router botnet that intercepted email logins; Iran hacks PLCs across US; exploitation wave hits ComfyUI and Flowise AI servers.

This newsletter is brought to you by application allow-listing software maker Airlock Digital. You can subscribe to an audio version of this newsletter as a podcast by searching for "Risky Business" in your podcatcher or subscribing via this RSS feed. You can also add the Risky Business newsletter as a Preferred Source to your Google search results by going here.
Americans have lost almost $21 billion to cybercrime last year, more than any other since the FBI began tracking cybercrime data 25 years ago, the FBI said in its yearly Internet Crime Report [PDF].
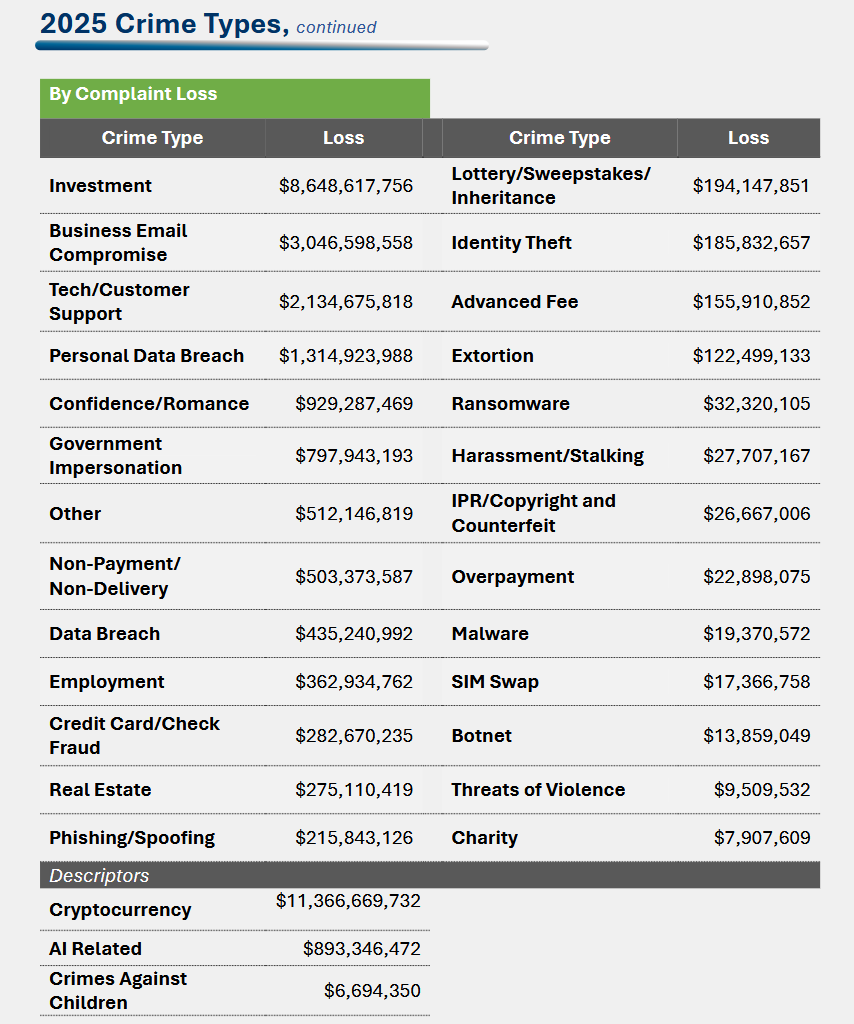
Investment scams were again the top category in terms of losses, with $8.6 billion reported stolen, and almost $6.2 billion of that sum being stolen as cryptocurrency.
Cyber-enabled fraud accounted for 85% of last year's losses, almost $17.7 billion.
Investment scams has been the category with the biggest reported losses in the report since 2022, with total losses rising every year, so it's no surprise here and anyone watching the infosec space was anticipating this result.
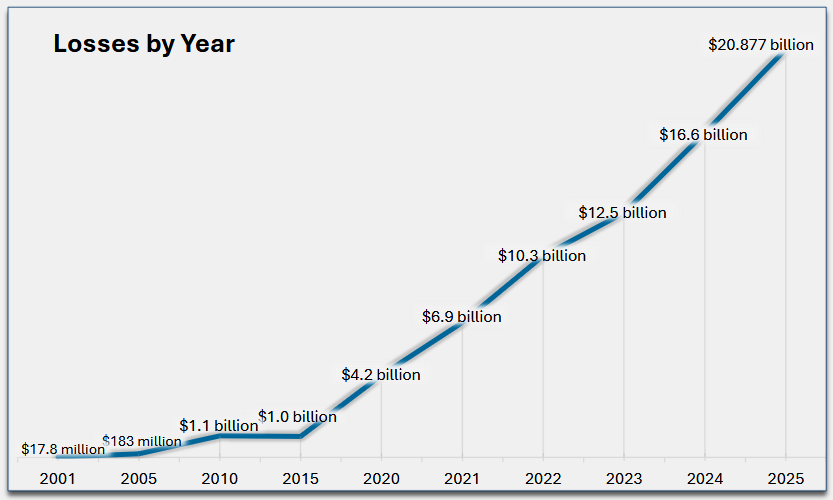
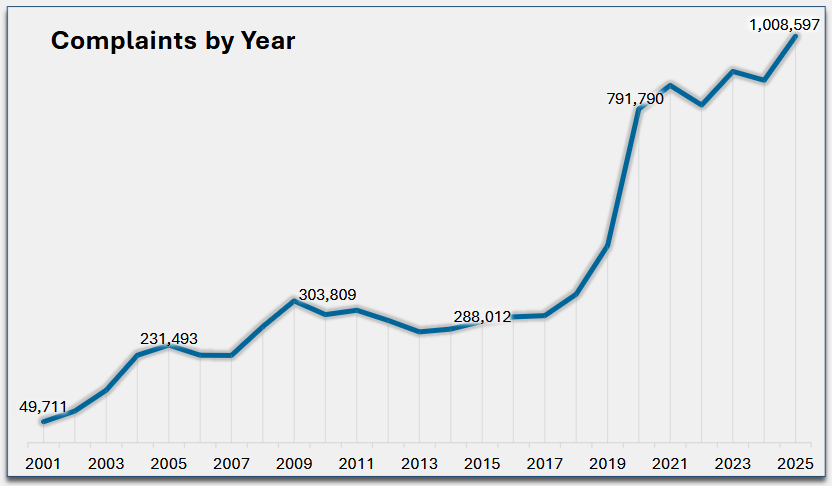
Last year was also the first time the FBI received more than one million cybercrime reports.
The agency says it is now receiving more than 3,000 complaints per day, a sign of the significant uptick in cybercrime operations.
All in all, the FBI IC3 Internet Crime Report is one of the most important indicators of cybercrime activity around the globe and is often used to inform and guide law enforcement crackdowns and legislative decisions.
Previous reports played a major role in a White House executive order signed early last month, with the Trump administration telling law enforcement agencies and the Justice Department to prioritize going after online cyber scam operators.
The order also involved the State Department, instructing the US embassies and state officials to pressure foreign governments that shelter cyber scam compounds to crack down on the problem.
Both Myanmar and Cambodia have already started moving against their sprawling cyber scam compound ecosystem, but that was mostly because of Chinese pressure rather than the US.
However, recent reports suggest that criminal syndicates are moving operations to new safe havens, such as Africa and the Middle East, and even some former Soviet states and parts of Europe.
It's definitely not a problem that will go away any time soon, mainly because of the ungodly amount of money cybercriminals are making, money that they often throw at authorities to look the other way.
Risky Business Podcasts
In this special documentary episode, Patrick Gray and Amberleigh Jack take a look back at hacking throughout the 1990s, from the feel-good vibes of the early hacking communities to the antics of young hackers who wound up on the run from the FBI.
Breaches, hacks, and security incidents
Drift hack linked to North Korea: North Korean state hackers built a fake trading company and even met Drift employees at conferences before stealing $280 million from the platform. The attackers spent months building trust with their targets before compromising their devices using malicious Apple TestFlight app and VS Code extensions. Hackers used the compromised systems to multi-sign the transactions that emptied Drift's treasury last month. Investigators linked the attack to a group known as Citrine Sleet (UNC4736, AppleJeus). [CoinTelegraph // Drift post-mortem]
Major law firm hack: A major US law firm confirmed a security breach after hackers posted customer materials online. The breach was traced back to a successful phishing attack. Jones Day is one of the biggest American corporate law firms, employing more than 2,400 lawyers. It is also known for representing US President Donald Trump in his 2016 and 2020 election campaigns. [Reuters]
Canadian telcos report breaches: Two Canadian telecommunications companies have reported data breaches last month. Freedom Mobile, Rogers, and its subsidiary Fido have notified customers of the incidents. The incidents appear to be related to a breach at Canadian business outsourcing company Telus Digital. [The Globe and Mail] [h/t Alex Rudolph]
Cyber "event" disrupts security alarm system provider: A mysterious cybersecurity incident has disrupted the BAT-MINI security alarm system across the US. The system was down for two days between April 2 and 4 last week. The system's vendor, Uplink, has not shared any details about the root cause. [DysruptionHub]
Betterment post-mortem: The Betterment investment platform has published a post-mortem of its January security incident. The company tracked down the incident to a social engineering attack of one of its employees that allowed hackers to access a marketing platform and email customers waves of crypto scams.
Rostelecom DDoS attack: While DDoS attacks have taken out some smaller telcos since Russia's invasion of Ukraine, a pretty considerable one hit Rostelecom enough to cause sprawling outages across Russia. Or at least that's what Russian authorities are saying. It could be Rostelecom going down in its attempt to block VPNs. If you know Russia well enough, you know not to take what state media reports as facts. [TASS]
General tech and privacy
Anthropic announces cybersecurity initiative: Anthropic has granted over 40 tech companies access to a new AI agent for cybersecurity defense work. The new Mythos agent was designed to help companies find vulnerabilities in their code. The company has also donated $4 million to open-source security organizations to help fund the patching of some of the found issues.

Russian internet freedom deteriorates to historic levels: Russia's internet freedom score has fallen to a lowly 4/100, on par with China and Iran, and only surpassed by the DPRK's 0/100. Eleven countries had a 92 score, the highest in the ranking.
Hilarious Copilot ToS change: Microsoft has updated the Copilot terms of service to describe its AI agent as "for entertainment purposes only" and warn customers to not use it for any advice, as it will make mistakes. This is classic lawyer speak for a bad product, which this super-genius company spent years shoving into everything. [Mashable]
Meta wants to shutter Oversight Board: Meta executives have held conversations about cutting the funding of its Oversight Board, effectively gutting the organization. [Platformer]
"The sides are currently negotiating a compromise that would allow the board’s work to continue in some form. But a raft of options remain on the table, including a break with Meta that would see the board’s trust create a new entity that performs similar work for other tech platforms."
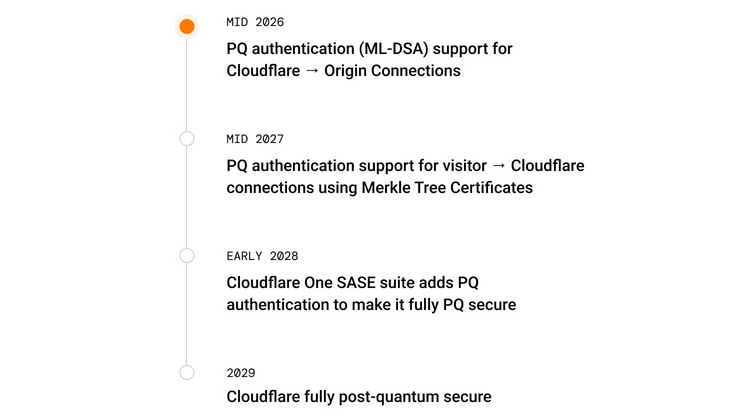
Cloudflare sets 2029 PCQ deadline: Cloudflare plans to secure all of its cloud systems against post-quantum encryption attacks by 2029. The company has accelerated its PQC roadmap after Google made a similar announcement last month. Cloudflare and Google both cited recent advances in post-quantum computers.
Government, politics, and policy
Roskomnadzor VPN ban causes banking outage: The Russian government's attempt to block VPN traffic caused a major banking outage at the end of last week. Point of sales and ATM transactions were down for hours early on Friday. According to Russian tech experts, the issue was caused by Russian banks using VPN tunnelling technologies to handle some data transfers. Once banking transactions were restored, Russia's internet agency tried to hide its mistake by ordering some news sites to take down articles.
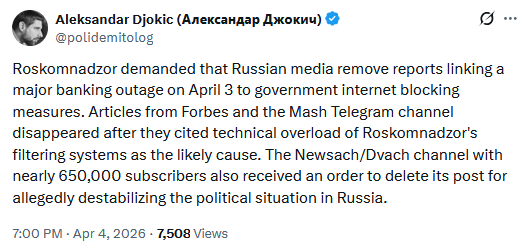
Kremlin turns on Telegram: Now that the Russian government has its own IM app in MAX, Russian officials are intensifying their attacks on Telegram. After accusing the company of violating data privacy and information security laws, officials claim Telegram is also in violation of Russia's securities and banking laws for hosting online casinos and sports betting on its platform. [TASS]
Smaller CISA budget comes with new cuts: CISA will likely have to cut new staff as part of a proposed White House budget for the next fiscal year. A budget proposal unveiled last week would cut $707 million from CISA's 2027 budget. The proposed budget would cut another 867 CISA jobs. The new cuts would bring CISA's total workforce to 2,865, almost half the size it had when Donald Trump retook office. The new budget also cuts a program that scans for vulnerabilities in critical infrastructure and field support teams for local governments. It also fully eliminates CISA's 14-person election security program, because elections aren't really that important in dictatorships/faux-democracies. [CybersecurityDive]
Life in America is something else: For some unknown reason, Florida is allowing its Fish and Wildlife Conservation police to carry out lookups against Flock's license plate reader database on behalf of ICE. As several people have pointed out on social media—"stick to protecting the animals, plz." [404 Media]
CAFCYBERCOM gets a badge: The Canadian Armed Forces Cyber Command (CAFCYBERCOM) has revealed its official badge.
"The badge reflects CAFCYBERCOM’s mandate to defend CAF networks, carry out cyber operations, and support CAF operations at home and abroad. Its design symbolizes strategic agility, technical precision, and service to Canada. The green and black field reflects the Command’s integration of signals intelligence, electronic warfare, and cyber operations across the digital and electromagnetic domains. The green represents signals intelligence heritage, while the black represents electronic warfare and operations within the contested electromagnetic spectrum. The chess knight represents the deliberate application of cyber capabilities in both defensive and offensive contexts. A lightning bolt and interlaced rings highlight operational precision and expertise in signals intelligence, while the Royal Crown and maple leaves affirm constitutional authority and national service. The Command’s motto, Sapere Aude, “dare to know”, underscores the intellectual rigour and professional discipline required to operate in a contested digital and electromagnetic environment."

Sponsor section
In this Risky Business sponsor interview, James Wilson chats with Airlock Digital co-founders, David Cottingham and Daniel Schell, about how they’re moving up the stack from file-based allowlisting to application-based allowlisting. David and Daniel explain how they’re making a seamless and quite logical move into application allowlisting, but with a new take on the technique.
Arrests, cybercrime, and threat intel
Germany identifies UNKN: A key member of the REvil and GandCrab ransomware groups has been identified as a 31-year-old Russian national named Daniil Maksimovich Shchukin. Shchukin went online as UNKN (Unknown) and served as co-admin and public figure for both groups. He was identified as UNKN by German authorities last week. He was also indicted in the US but his role in the gang was never revealed. According to a CCC talk from 2023, his last known location was Antalya, Turkey, where he fled from Russia with his wife after the start of the Ukrainian war. [KrebsOnSecurity]
Spyware maker sentenced to time served: The founder of spyware company pcTattletale has avoided jail time. Bryan Fleming was sentenced last week to time served and a meager fine of $5,000. He pleaded guilty in January to creating and selling the spyware after he was charged last year. Fleming shut down pcTattletale in 2024 after his company leaked customer data. [TechCrunch]
SMS blaster arrested in Brazil: Brazilian authorities have arrested a suspect for running a fake mobile base station from his apartment on the 14th floor of a residential condominium in Sao Paolo. The fake mobile tower was being used as an SMS blaster to send mobile spam. The device was detected by Brazil's communications watchdog using specially designed equipment. Anatel held workshops last year to teach local telcos on how to spot fake base stations. [CommsRisk]
Trump family business tied to scam operators: An OCCRP investigation surfaced a joint business between the Trump family and three individuals linked to the Prince Group, a former major operator of cyber scam compounds.
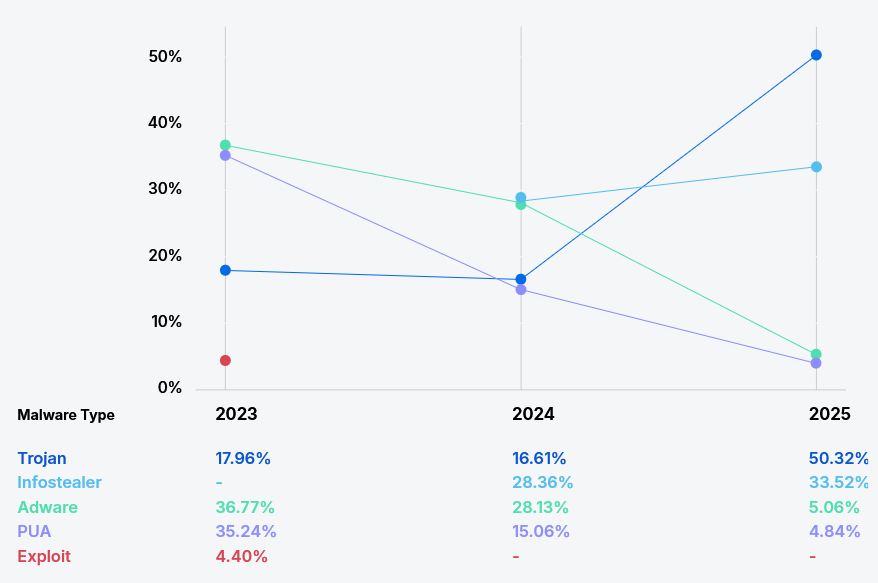
RATs and infostealers dominate macOS malware trends: Infostealers and remote access trojans accounted for almost 85% of all macOS malware detections last year. The number has skyrocketed from only 17% two years before. The change is a direct result of multiple turnkey macOS infostealers being broadly available on hacking forums since 2023. [Jamf]
Winter Olympics saw huge waves of DDoS attacks: Netscope reports that DDoS activity during this year's Milano Cortina Winter Olympic Games were 6 to 10 times larger than what that period of the year usually sees.
UNC6783 (Raccoon) group conducts extortions: A threat actor using a public persona named Raccoon is extorting several high-value corporate entities. The attacker is social engineering employees via live chats to access fake Okta login pages. Google's security team has tracked attacks against several dozen major companies. Google tracks this attacker as UNC6783.
New Hive0117 attacks in Russia: After a campaign last year, the Hive0117 hacking group is back at targeting Russia again.
Watch Wolf attacks: An e-crime group named Watch Wolf is running phishing campaigns targeting Russian financial institutions, targeting employees with the DarkWatchman RAT.
APT-Q-27: Breakglass has released new IoCs for APT-Q-27, a suspected Chinese e-crime group that typically targets the gambling sector.
ComfyUI crypto-mining campaign: A threat actor is abusing misconfigured ComfyUI backends to deploy cryptocurrency miners on high-capacity cloud servers. Compromised systems are also enrolled in a proxy network. Censys says the attacker is also exploiting Redis databases in a separate campaign.
Active Magecart campaign: Sansec has found a web skimmer (Magecart) script on almost 100 stores, with the malicious code hidden inside an invisible SVG element.
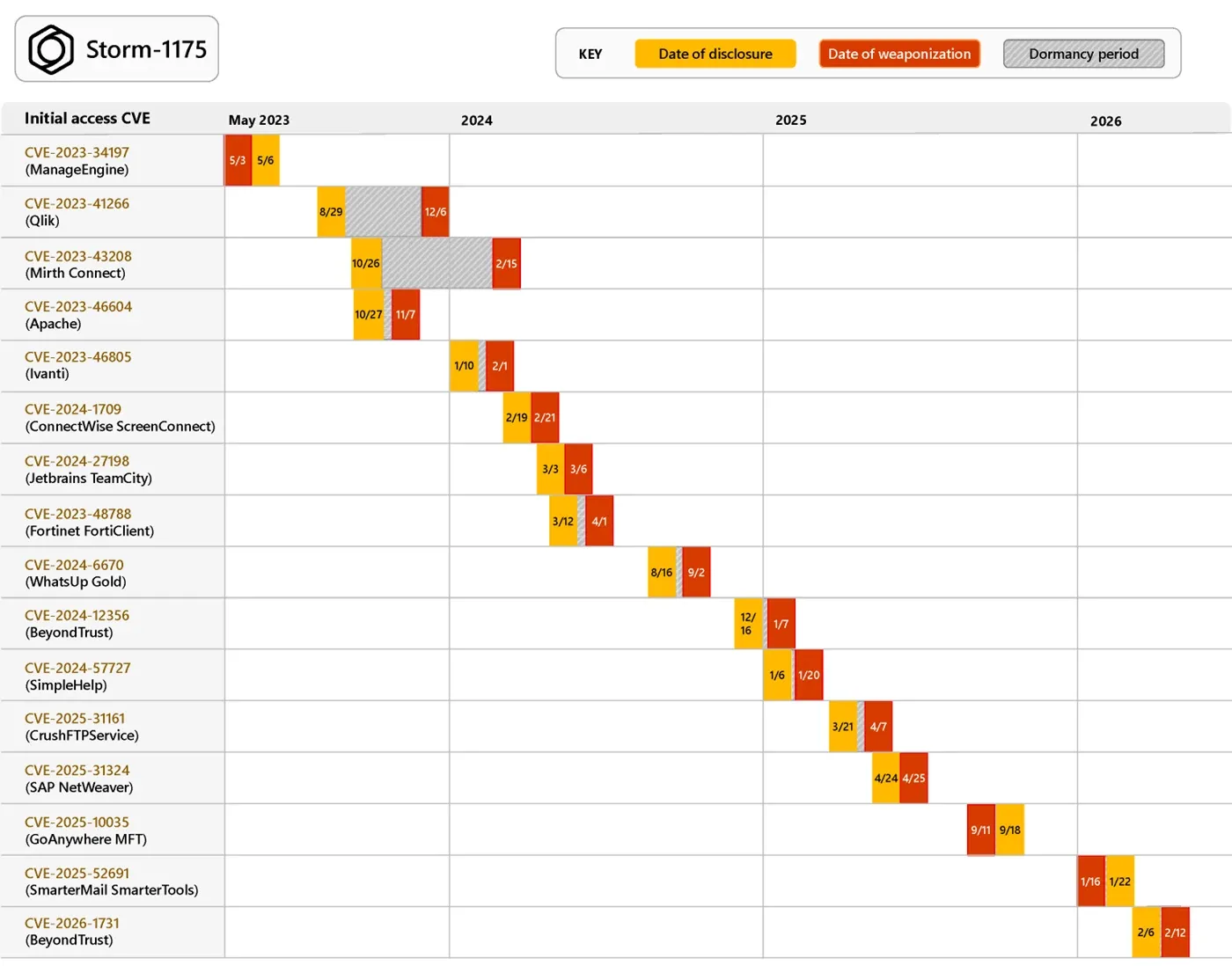
The prolific Storm-1175 group: A Chinese cybercrime group has used zero-days to deploy the Meduza ransomware. Microsoft linked the Storm-1175 group to zero-days in the GoAnywhere MFT file-sharing software (CVE-2025-10035) and SmarterMail email server (CVE-2025-52691). In addition, the group has also used 14 other vulnerabilities very shortly after public disclosure. Microsoft says the group moves rapidly from initial compromise to ransomware deployment and rotates exploits on a regular basis.
Malware technical reports
AncientNET / Zyre botnet: There's a new Gafgyt variant in town. Named AncientNET (Zyre), this one goes after internet-exposed WebDAV servers.
NightSpire ransomware: The Huntress team has published a technical analysis of NightSpire, a ransomware strain first seen last year.
Shub Stealer: Walmart security researcher Jason Reaves looks at Shub Stealer, a relatively new macOS infostealer.
New Remus infostealer: Gen Digital researchers have found a new infostealer named Remus that was developed from the base of the old LummaStealer.
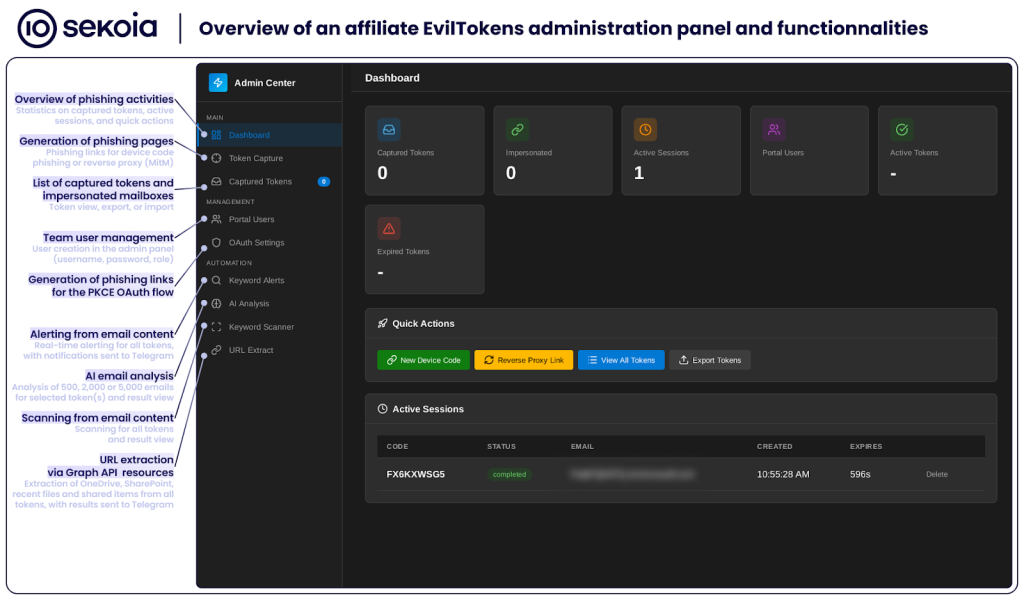
EvilTokens PhaaS: Sekoia has published part two of its analysis of EvilTokens, today's most popular service used for device code phishing operations. Part one is here.
Sponsor section
In this product demo of the Airlock Digital application control and allowlisting solution, Patrick Gray speaks with Airlock Digital co-founders David Cottingham and Daniel Schell.
APTs, cyber-espionage, and info-ops
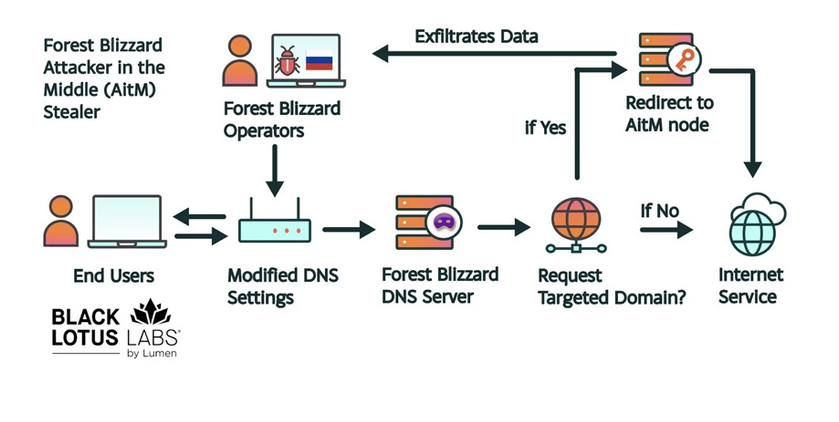
Authorities disrupt APT28 router botnet: Russian military hackers have compromised thousands of routers across the globe to redirect select authentication traffic to phishing pages. Most of the compromised devices are MikroTik and TP-Link routers. The phishing pages targeted email server login pages and Microsoft accounts. Known victims have been identified in Africa, Southeast Asia, and Central America. The botnet was linked to APT28 (Forest Blizzard), a collection of cyber units from Russia's military intelligence service GRU. US authorities, Microsoft, and Lumen Technologies disrupted the botnet this week. The UK NCSC, which first spotted this operation, has also published an advisory.
Iranian hacks of PLCs cause disruption across US: Iranian threat actors are hacking internet-exposed programmable logic controllers (PLCs). CISA and the FBI say disruptions have been reported across the US. The attacks have targeted Rockwell and Allen-Bradley PLCs. [CISA // FBI security advisory, PDF]
New OtterCookie servers: Walmart security researcher Jason Reaves has uncovered new command and control servers for OtterCookie, an infostealer used by North Korean state hackers.
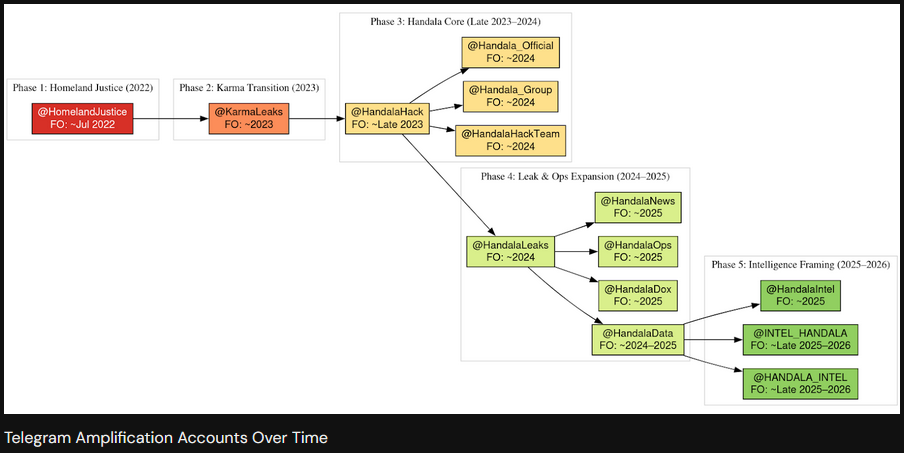
Handala and MOIS: The security team at DomainTools has published an analysis of the Handala hacking group and how it and fellow groups Homeland Justice and Karma should be treated as components in Iran's MOIS intelligence service, and not unique and independent threat actors.
"These personas function as interchangeable operational veneers applied to a consistent underlying capability. Their purpose is not to reflect organizational separation, but to enable segmentation of messaging, targeting, and attribution while preserving continuity of infrastructure and tradecraft. Across all observed phases, the actors exhibit clear temporal continuity, shared infrastructure patterns, and a repeatable operational workflow. The persistence of these elements, despite rebranding, indicates centralized direction and capability management."
Vulnerabilities, security research, and bug bounty
Recent security updates: Android, Apache ActiveMQ, D-Link, Firefox, Grafana, Kubernetes.
Flowise RCE enters active exploitation: Threat actors are launching attacks on Flowise, a web-based tool for building and deploying agents. The attacks are leveraging a major vulnerability patched last September. Tracked as CVE-2025-59528, the bug allows remote unauthenticated attackers to inject and run commands on the Flowise server. The vulnerability has a severity rating of 10 and attacks were first spotted this week by VulnCheck.
Intego LPE: Quarkslab researchers have found LPE vulnerabilities in the Intego antivirus, for both the macOS and Windows.
GrafanaGhost attack: Noma's Sasi Levi has published a write-up on GrafanaGhost, an attack that bypasses Grafana AI protections to exfiltrate data from corporate environments.
Apache ActiveMQ RCE: Horizon3 has published a write-up on CVE-2026-34197, an authenticated RCE in Apache ActiveMQ that impacts all versions released over the past 13 years. Horizon3's Naveen Sunkavally says Claude found the bug in around 10 minutes.
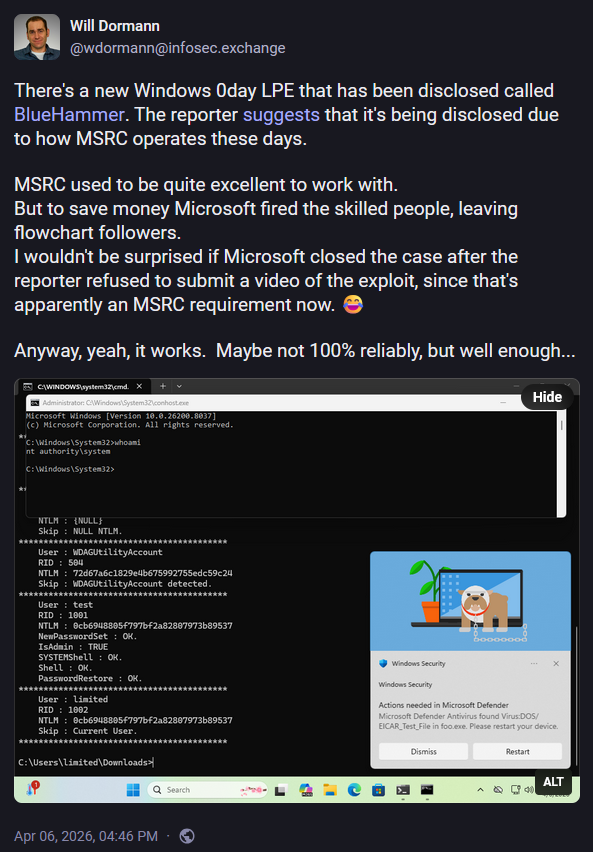
Exploit code published for BlueHammer zero-day: A disgruntled security researcher has published proof-of-concept code for a Windows zero-day. Named BlueHammer, the zero-day can be used to elevate privileges on Windows. The researcher released the exploit code after what appears to have been a disagreement with the Microsoft Security Researcher Center, the Microsoft team that handles the company's bug bounty program.
Infosec industry
Threat/trend reports: Blackpoint Cyber, Cloudwards, CDW, Fable Security, Jamf, and SANS have recently published reports and summaries covering various threats and infosec industry trends.
New Bitsight CEO: Security firm Bitsight has appointed John Clancy as its new CEO.
"Clancy succeeds Steve Harvey, who is stepping down after six years of leadership. During his tenure, the company quadrupled in size and further established itself as a trusted partner to organizations worldwide. He will remain an advisor to the Board of Directors."
New tools—pqcrypto: Paragon Initiative has released two open-source tools, ext-pqcrypto and pqcrypto_compat, to help the PHP community protect their projects against post-quantum encryption attacks.
Risky Business podcasts
In this edition of Between Two Nerds, Tom Uren and The Grugq discuss how Iran's cyber forces have been used during the ongoing war so far.




