Risky Bulletin: Android looks set to get its own Lockdown Mode
In other news: China overhauls cybersecurity and privacy laws; UPCX crypto platform hacked for $70 million; Greece's controversial intel agency to hire more hackers.

This newsletter is brought to you by Kroll. You can subscribe to an audio version of this newsletter as a podcast by searching for "Risky Business" in your podcatcher or subscribing via this RSS feed.
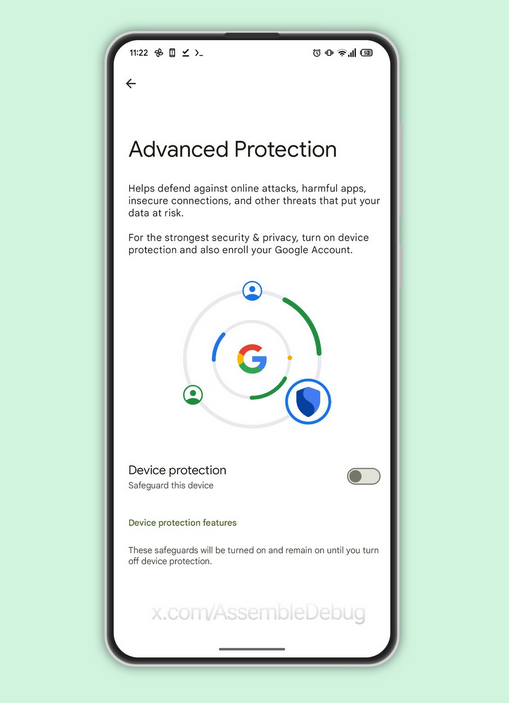
Google has been secretly working on a new super-secure mode for Android that's inspired by Apple's iPhone Lockdown Mode.
According to a placeholder documentation page and based on analysis of Android beta images, the new feature is named the Android Advanced Protection Mode (AAPM).
Just like Lockdown Mode, the AAPM is not intended for regular Android users and was specifically designed for high-risk individuals who may face threats from oppressive regimes, advanced spyware, and rogue network surveillance attacks.
The feature reduces an Android device's attack surface by:
- disabling insecure 2G cellular connections;
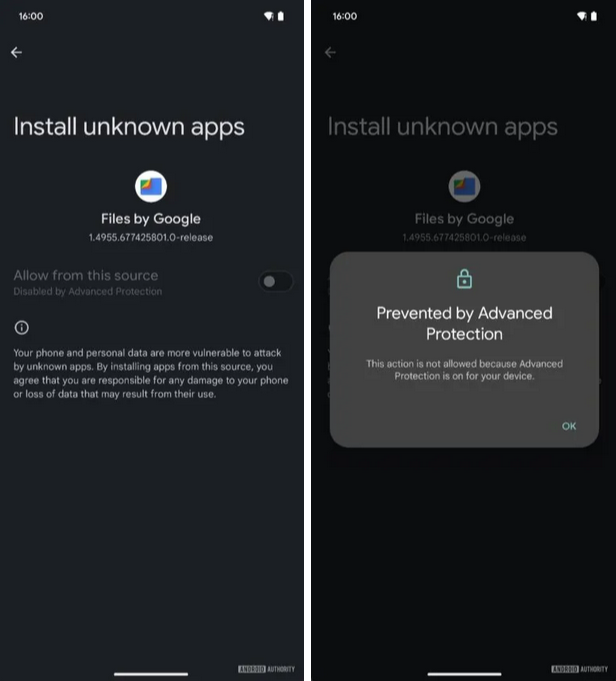
- blocking users from sideloading apps from unknown sources;
- enabling Memory Tagging Extension (MTE), a CPU memory feature that blocks the exploitation of memory-related exploits;
- rebooting devices if they've been locked for more than three days.
This last feature was spotted by Android Authority this week and is also inspired by a similar feature that Apple shipped last October—designed to thwart forensic tools from obtaining data from a locked device, something that journalists and activists detained by oppressive regimes are likely to find useful.
Google has not officially confirmed the new Android Advanced Protection Mode, but quite a large amount of code is already in Android 16 beta releases, which tells me this is quite close to being ready to ship.
There's code for the UI settings from where users can turn on Advanced Protection.
There's also code for the UI that tells users they can't sideload apps.
There's also code for an API to allow apps to detect when the mode has been enabled and optionally apply their own super-secure settings. For example, browsers could disable JIT compilation when the mode is detected active, or IM apps could disable automatic multimedia loading and previewing.
There's also the placeholder for a currently-404ing AAPM documentation page that was created last month.
Knowing how Google operates, this is very likely to be announced at Google's yearly I/O developer conference next month and ship around August-September, when Android 16 is set to release.
If this feature's name sounds familiar, it's most likely an Android version of the Google Advanced Protection Program, another Google security feature that, instead of Android, puts your Google online account in a super secure state. That includes blocking possible takeover attempts by requiring a passkey or security key to log in, enforcing stricter file download rules, and limiting access to a user's data to a very small set of Google and verified third-party apps.
Either way, it's a welcomed sight to see Google invest in porting some of Lockdown Mode's features to Android. There's quite the competition between the two mobile OSes, and it's nice to see that egos didn't get in the way of doing the right thing and protecting users.
Sure, the AAPM might not be on parity with Lockdown Mode right now, which offers a little bit more features, but Apple did have a few years headstart after all.
Risky Business Podcasts
Risky Business is now on YouTube with video versions of our main podcasts. Below is our latest weekly show with Pat and Adam at the helm!
Breaches, hacks, and security incidents
UK Royal Mail hack: A hacker has leaked 144GB of data from the UK postal service Royal Mail. The data was stolen from Spectos, a German company that provides postal and logistics software. Royal Mail has confirmed the breach. The leaked data contains customer personal information, Zoom recordings, mailing lists, and delivery and location data. [Additional coverage in Cyber Daily]

T-Mobile SyncUP incident: The T-Mobile SyncUP GPS tracking service experienced a technical issue this week and has shown the locations of tracking devices to other customers. The incident primarily impacted families that use the devices to track children and their elderly. T-Mobile says the incident "resulted from a planned technology update." [Additional coverage in 404 Media]
PO cyberattack: Hackers have breached the IT systems of Civic Platform, the current pro-EU Polish ruling party. Polish Prime Minister Donald Tusk described the attack as having an "Eastern footprint" and "election interference." Poland is set to hold its presidential election next month. [Additional coverage in Notes from Poland]
UPCX crypto-heist: A hacker has stolen over $70 million worth of crypto assets from the UPCX cryptocurrency payment platform. The company suspended operations to investigate the hack but said all user funds were safe. According to blockchain security firm Cyvers, the hack took place after the attacker gained access to one of the platform's admin-level smart contracts. The incident is this year's second-largest crypto heist by size, second only to the Bybit $1.5 billion mega-hack.

General tech and privacy
Chrome 135: Google has released version 135 of its Chrome browser. See here for security patches and webdev-related changes. The biggest changes in this release include support for the ability to save extensions to Google accounts, LLM assistance in mitigating scams, HTST Tracking Prevention, initial testing of the device-bound session credentials security feature, and an incognito mode that blocks third-party cookies.
Firefox 137: Mozilla has released Firefox 137. New features and security fixes are included. The biggest feature in this release is the addition of tab groups—a feature copied from Chrome, which copied it from Firefox in the first place. Nice going, Mozilla!
Mastodon security fund: The Nivenly Foundation has launched a public fund to help improve Fediverse security features.
ngrok blocks Russian users: Internet tunneling service ngrok has blocked Russian users from its service. The company cited US sanctions against Russia as the reason. ngrok joins a long list of Western companies that are now blocking Russian users from their services.
Apple silently turns on automatic updates: Apple is silently enabling automatic updates for macOS and iOS users. The change rolled out with macOS 15.4 and iOS 18.4 released this week. The move is annoying to some users and sysadmins who typically want to make sure updates don't break systems before applying them. [Additional coverage in OS X Daily]
Amazon gets on the TikTok dance: Amazon has allegedly filed a bid to buy TikTok's US operations. [Additional coverage in Engadget]
Windows Hotpatch goes live: Microsoft has launched Hotpatch for Windows 11, a new feature that applies security updates without the need to immediately restart the OS. Customers will only need to restart systems once per quarter instead of once per month. The feature is only available for enterprise users.
Government, politics, and policy
UK Cyber Security and Resilience Bill: The UK government plans to expand its critical infrastructure sectors with the addition of data centers and managed service providers. The new provision is part of a new cybersecurity bill the government plans to bring before the parliament later this year. The bill introduces new cybersecurity compliance requirements for critical organizations designed to bolster their defenses against cyberattacks. Companies that fail to comply risk fines of up to £100,000/day.
Medical devices cybersecurity: On the day the Trump administration was laying off thousands of HHS and FDA employees, the House Energy and Commerce Committee was holding a hearing on the cybersecurity of aging medical devices, not knowing if there would be anyone to enforce their decisions at the FDA any time soon.
Cyber Innovation Warfare Center: The new revamped US Cyber Command 2.0, as it is called, might include a new unit for developing new cyber warfare technologies, possibly named the Cyber Innovation Warfare Center. [Additional coverage in The Cyber Edge]
Ukraine cyber aid levels fall: The Aspen Institute reports that international cyber aid to Ukraine seems to be waning in recent months, most likely as a shift in US policy and fatigue among private sector companies. [Additional coverage in The Record]
Greece intel agency to hire more hackers: Greece's national intelligence service EYP plans to bolster its cybersecurity forces with 30 new agents by the end of the year. The agency plans to hire over 300 new agents, including for other technical roles. The EYP has a controversial image in Greece because of the 2022 Predatorgate surveillance scandal. The agency used commercial spyware to hack and spy on members of the opposition and journalists on orders from the ruling government. [Additional coverage in eKathimerini]
China to amend cybersecurity laws: The Chinese government is amending its cybersecurity law to increase fines and expand liability for misbehaving companies. The government is increasing fines for companies that fail to report security breaches, collect personal data they aren't entitled, and sell products that don't meet security standards. It also introduces a mechanism to reduce fines for first-time violations, small breaches, or companies that move quickly to reduce harm. As part of the overhaul, China's Cyberspace Administration is also modifying the country's privacy law to reflect its new crackdown on companies that collect too much personal data. This includes new rules for the design of apps, the use of SDKs, and offline use of collected data. [Additional coverage in Hunton] [h/t DataBreaches.net]
Sponsor section
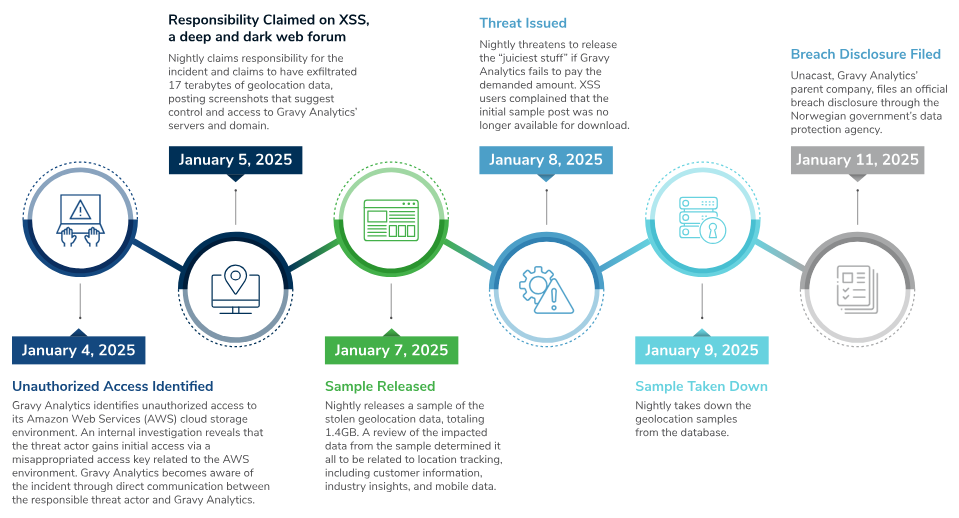
In this Risky Bulletin sponsor interview, Ed Currie from Kroll Cyber talks to Tom Uren about the recent hack of the Gravy Analytics geolocation data provider. He explains the hack and how geolocation data can be used by malicious actors.
Arrests, cybercrime, and threat intel
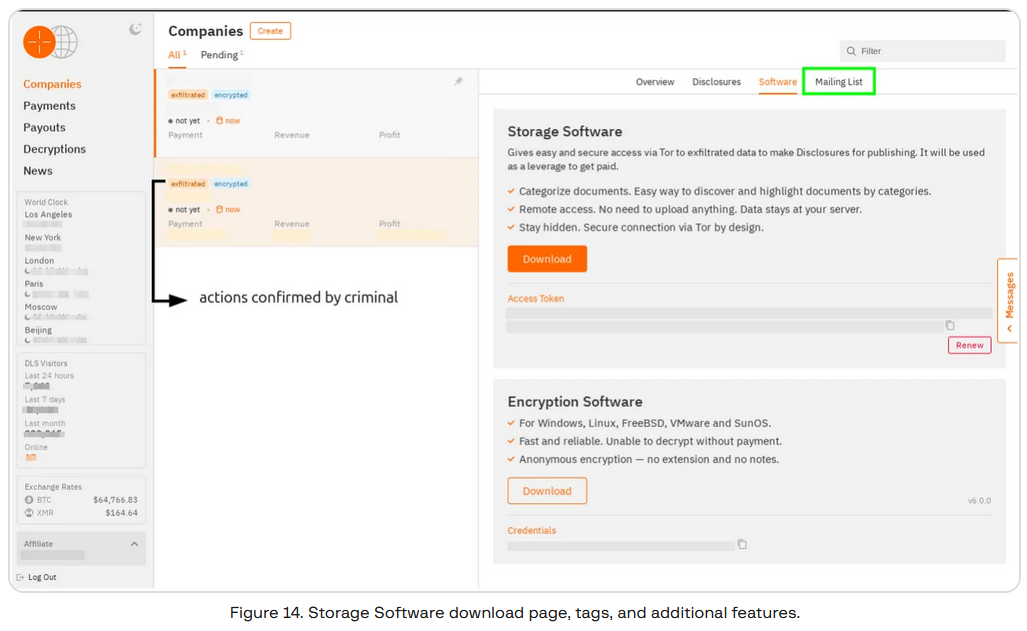
Hunters international prepares to shut down: The Hunters International group is preparing to shut down its ransomware operation and relaunch under a new name of World Leaks—an extortion-only operation. Security firm Group-IB says the move comes as the group developed a new tool called Storage Software that focuses on analyzing and classifying stolen data. The Hunters International group launched at the end of 2023. It is made up of former members of the Hive ransomware group that was disrupted earlier that year.
Black Basta leaks: Intel471 takes another look at the Black Basta ransomware and its recent leak of internal chats.
Babuk2 linked to Bjorka: Trustwave and Rapid7 have linked the newly revived Babuk ransomware brand—tracked as Babuk2—to an infamous data leaker named Bjorka.
Proton66: The DomainTools security team has published a profile on Proton66, a bulletproof hosting network enabling cybercrime operations.
Securing HTTP APIs: The UK cybersecurity agency has issued guidance on how to secure the insecure HTTP-based APIs.
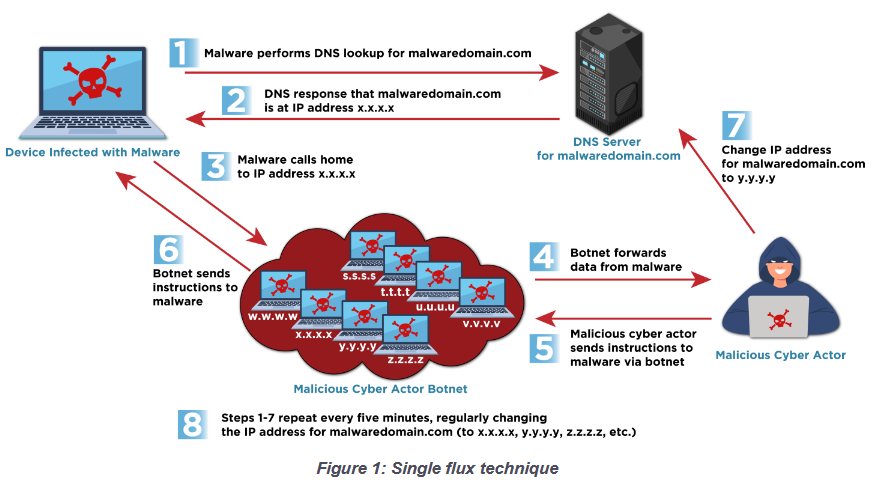
Five Eyes warns about fast flux networks: Cybersecurity agencies from the Five Eyes alliance have published a security advisory on fast flux networks, a service used by cybercrime groups and APTs to disguise their command and control infrastructure.
Stripe API skimming abuse: An online skimming operation is abusing a legacy Stripe API to verify if stolen payment card details are still valid. The skimming operation was active on almost 50 online stores. Security firm Jscramler says a third of them have since removed the malicious code stealing customer payment details.
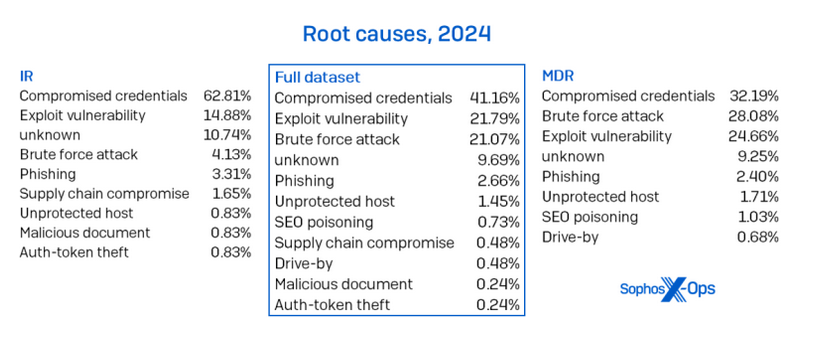
Credentials, the root of all evil: Almost two-thirds of all security incidents investigated by Sophos last year originated from credentials-related root causes, such as leaked passwords, brute-force attacks, or phishing incidents.
Attack of the SVGs: AhnLab and Forcepoint report on the rise in phishing campaigns abusing obfuscated SVG files to redirect users to phishing sites. This is something that Sublime Security also saw earlier this year.
Tax season is here: Microsoft looks at some of the tax-themed phishing campaigns currently targeting US users. It's a yearly tradition in the US, like Christmas!
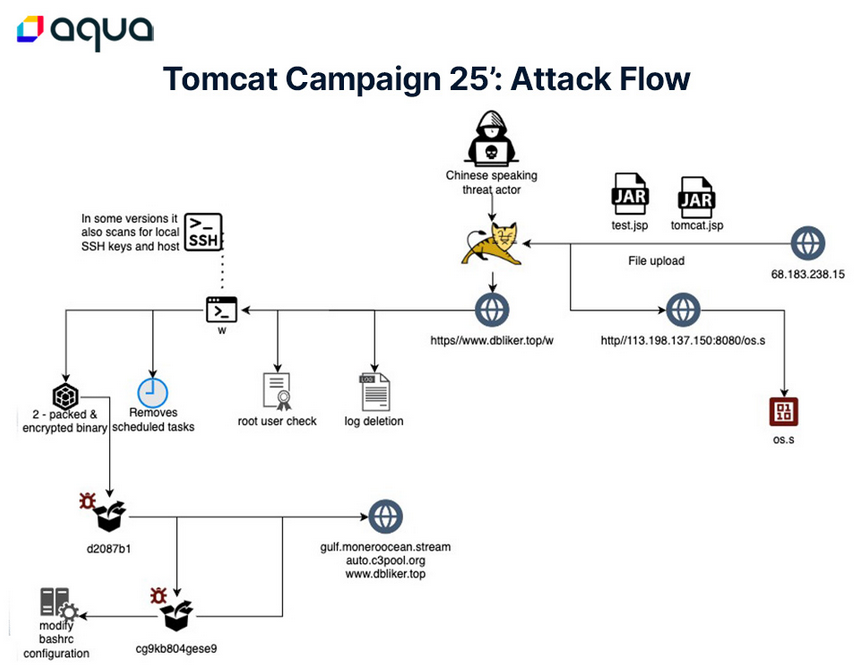
Tomcat campaigns: AquaSec looks at the attacks targeting Apache Tomcat servers using a recently patched bug tracked as CVE-2025-24813. Obviously, this is a crypto-mining op.
Malware technical reports
TookPS downloader: Kaspersky looks at a new malware downloader named TookPS that it first saw used in the wild earlier this year, utilizing DeepSeek as a lure to infect users.
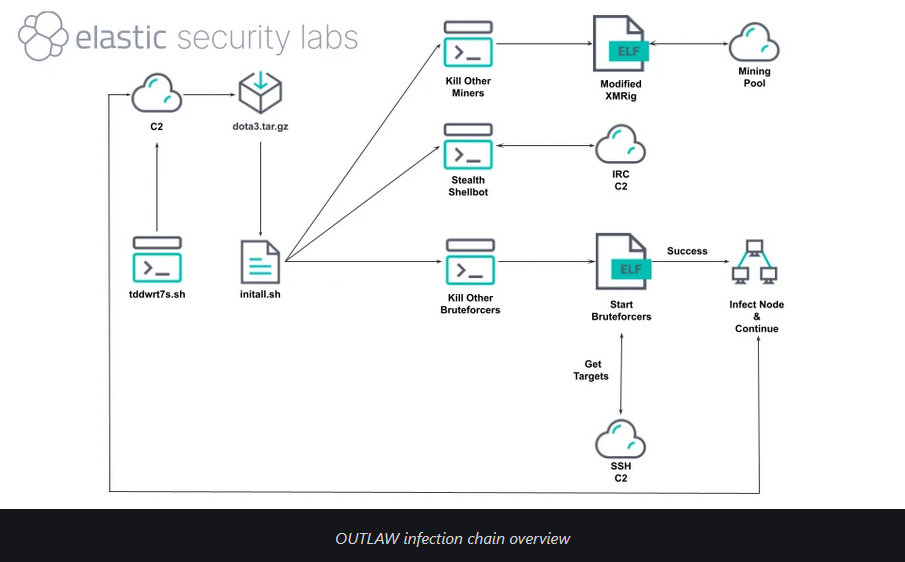
Outlaw crypto-miner: Elastic's security team has published a technical report on Outlaw, a self-propagating Linux-based crypto-miner that's been around for several years now.
"OUTLAW exemplifies how even unsophisticated malware can persist and scale effectively in modern environments. Despite lacking advanced evasion techniques, its combination of SSH brute-force attacks, self-replication, and modular components allows it to maintain a long-running botnet. OUTLAW ensures continuous expansion with minimal attacker intervention by leveraging compromised hosts to propagate infections further."
Sponsor section
The Kroll team takes a look at the cyber risks emerging from leaks at data analytics and aggregators, using the recent leak of geolocation data from Gravy Analytics as a case study.
APTs, cyber-espionage, and info-ops
UAC-0219: CERT-UA warns of a new espionage campaign targeting public administration and critical infrastructure facilities in Ukraine with a piece of PS malware named WRECKSTEEL. The agency has linked to a group it tracks as UAC-0219.
Operation HollowQuill: Seqrite has published a report on Operation HollowQuill, a suspected APT operation targeting Russian R&D organizations.
Konni spear-phishing campaign: Security researcher Priya Patel has published an analysis of a spear-phishing campaign linked to DPRK APT Konni.
UNC5221 deploys new Ivanti zero-day: Ivanti has released security updates to fix an actively exploited zero-day in its Connect Secure, Policy Secure, and ZTA enterprise gateways. The patch fixes a memory buffer overflow that attackers were exploiting for pre-auth remote code execution. Google linked the attacks to a Chinese APT group tracked as UNC5221. The group has a long history of targeting Ivanti products, such as attack waves in January of last year and this year.
Vulnerabilities, security research, and bug bounty
DrayTek reboot loops linked to pre-2020 bugs: Taiwanese company DrayTek says that a recent wave of router disconnects and reboot loops was caused by the exploitation of a pre-2020 vulnerability. Patches have been available since 2020. DrayTek says only routers that ran outdated firmware were affected.
Cisco security updates: Cisco has released three security advisories for various products.
Jenkins security update: The Jenkins project has released a security update to fix two vulnerabilities in its core code and six others in plugins.
WinRAR security update: The WinRAR file archiver has fixed a bug that would have allowed attackers to bypass the Mark-of-the-Web mark on decompressed files. Tracked as CVE-2025-31334.
QuickShell write-up: SafeBreach researcher Or Yair says Google has now patched 10 vulnerabilities in its Quick Share data-transfer utility. Yair disclosed the bugs last year at the DEFCON conference. The bugs allowed threat actors to easily share files with users without their consent.
ZendTo unauth RCE: Project Black has published a write-up on an unauth RCE in the ZendTo file-sharing software. The issue was patched back in 2021, but there's no public CVE.
Halo ITSM pre-auth SQLi: Searchlight Cyber has published a technical report on a pre-auth SQLi vulnerability in Halo ITSM, an IT support management software for cloud environments.
Verizon Call Filter leak: Security researcher Evan Connelly has found a vulnerability in the Verizon Call Filter app's APIO that could have been exploited to leak the data of Verizon customers.
Infosec industry
Threat/trend reports: CERT-PL, Guardio, Netscout, and Sophos have recently published reports and summaries covering various infosec trends and industry threats.

New tool—peeko: A security researcher named b3rito has released peeko, a browser-based XSS-powered C2 tool that leverages the victim's browser as a stealthy proxy inside internal networks.
New tool—DocEx: Dark Space Security has released DocEx, a tool that emulates how APTs exfiltrate sensitive documents.
BSides Seattle 2024 videos: Talks from the BSides Seattle 2024 security conference, which took place last April, are now available on YouTube.
DistrictCon 2025 videos: Talks from the DistrictCon 2025 security conference, which took place in February, are now available on YouTube. This also includes talks from the Junkyard, a separate track for hacking EOL gear.
Risky Business Podcasts
Tom Uren and Patrick Gray discuss how North Korean IT worker scam is shifting towards Europe and employing tactics that make it more dangerous.
In this edition of Between Two Nerds, Tom Uren and The Grugq look at all the strands of evidence that make people think the NSA is a top-tier cyber actor.




