Risky Biz News: Programmers will need to learn to love MFA, even if they like it or not
In other news: Almost $2 billion worth of crypto lost in H1 2022; a look into the BraZZZerSFF cybercrime service; and Signal and DigitalOcean impacted by third-party breaches.
This newsletter is brought to you by Airlock Digital, Proofpoint, RunZero, and Thinkst Canary. You can subscribe to an audio version of this newsletter as a podcast by searching for "Risky Business News" in your podcatcher or subscribing via this RSS feed.
The maintainers of the RubyGems package index announced on Monday plans to enforce multi-factor authentication (MFA) requirements for the owners of any Ruby library that has crossed a total of 180 million total downloads. Plans are also being made to broaden this requirement to authors of less popular libraries, although no deadlines are currently set in stone.
By taking this route, RubyGems now joins PyPI (Python), npm (JavaScript), NuGet (.NET), and GitHub itself as major developer platforms where MFA is required in one form or another.
For example, starting this spring, npm began requiring all library authors for its package repository to have MFA enabled to be able to publish new versions of their tools.
Shortly after, NuGet began enforcing a similar policy for all accounts.
Last month, PyPI also began requiring that all owners of libraries in the Top 1% of downloads have MFA enabled, and they also went a step further by gifting 4,000 hardware security keys to maintainers.
While CPAN (Perl), Crates (Rust), and Maven (Java) have not made any announcements on this subject, this reporter understands that discussions are taking place in the backrooms of two of these portals on taking similar steps, with projects waiting to see if the aforementioned services (PyPI, npm, and NuGet) see any meaningful disruption or decrease to login and contribution flows.
TIL #crates.io has no #2FA for login/pub. crates and the pub.token is stored in plaintext on your HD! Also it has no built-in way for deprecation. You just have to say that in the readme or you have to "yank" every published version one by one. In that respect #npm is way better!
— Mathias Panzenböck (@bloodyalbatross) 2:16 AM ∙ Apr 24, 2022
Even if not a package repository in itself, GitHub is often used by the maintainers of various other libraries to host their code. GitHub knows this and the central role it plays in securing many open-source libraries and package repositories, many of which pull package releases straight off its platform.
Earlier this year, GitHub announced that all users who contribute code on any GitHub.com project will be required to enable one or more forms of MFA by the end of 2023.
Some developers might not be in the mood to solve MFA challenges when logging into their package accounts or when pushing some tiny code update via an API or CLI tool, but the writing is slowly starting to appear on the wall, and the writing says that MFA will soon become a de-facto login security standard for most package repositories and DevOps platforms.
You can easily attribute this trend to a broad push for MFA across the entire IT industry but also to the increasing number of incidents where weak account security for some small open-source library has led to massive disruptions across software supply chains.
Breaches and hacks
Signal impacted in Twilio breach: Secure instant messaging service Signal notified 1,900 customers this week whose phone numbers were exposed in a breach at Twilio, a company Signal uses for phone number verification services. Signal is one of the 125 customers whose data was exposed in the Twilio breach, which the company disclosed last week.
DigitalOcean breach: Cloud hosting platform DigitalOcean said that a threat actor gained access to its MailChimp account, which the company was using as an email delivery service, and abused this access to reset passwords for a handful of customer accounts. DigitalOcean said it found out about the hacks after Mailchimp suspended its account, rather than Mailchimp informing the hosting provider. Mailchimp took similar steps to suspend accounts of various cryptocurrency platforms, which appear to have been the primary target of this intrusion. Despite the hack taking place on August 8, the email service provider took days to notify its customers. DigitalOcean said it dumped Mailchimp's services following the hack and also began notifying its own customers as well.
Oh, that pesky supply chain issue.
— Will Gregorian (@WillGregorian) 10:49 PM ∙ Aug 15, 2022
SEC charges: The US Securities and Exchange Commission charged 18 individuals and corporate entities for their roles in a fraudulent scheme in which dozens of online retail brokerage accounts were hacked and used to purchase micro-stocks and manipulate their price and trading volume. According to the SEC, 31 brokerage accounts were hacked and abused in this scheme between late 2017 and early 2018, earning the hackers more than $1 million in illicit proceeds.
Crypto hacks in H1 2022: Blockchain security firm SlowMist has published an overview report [PDF] of the cryptocurrency security scene for the first half of the year. The company said that in H1 2022, cryptocurrency platforms lost $1.976 billion worth of cryptocurrency during 187 security incidents. The company's report echoes similar figures put out by Chainalysis.
CS:GO trading portal hacked: CS.Money, a marketplace for trading CounterStrike Global-Offensive game items, said it was hacked over the weekend and lost $6 million worth of player items. The site's admins said they are now working to recover the stolen items.
As it was agreed with other services, 20000 skins that were identified as stolen will not be available for sale and trade.
— CS.MONEY (@csmoneytrade) 6:43 PM ∙ Aug 15, 2022
@buff163 @SkinBaronEN @CsDealsOfficial @tradeit_gg @GamerPayGG @csgofloat @swapdotgg @BitSkinsCom @WAXPEER @bleikstore @lisskins_owner @hellcasecom ...
1/2
YouTube royalties scam: A Billboard investigation found that two Arizona men swindled tens of Latin music artists out of more than $23 million in YouTube royalties via a fake company that tricked YouTube into thinking it owns the rights to the artists' music. Impacted musicians include the likes of Daddy Yankee, Anuel AA, Julio Iglesias, and more.
GFB breach: Grupo Financiero Banorte, Mexico's second-largest bank, had the data of more than 10 million of its customers leaked on an underground cybercrime forum last week after it tried to intimidate the site and force it to remove a topic advertising its data for sale. As reporter Brian Krebs reports, the site's admin responded by purchasing the data and leaking it themselves as a way to counter the bank's claim that the news of a potential hack was "fake news."
The admin of the cybercrime forum Breached said they just received a cease and desist letter claiming the forum thread where a Mexican bank's data was being sold was fake news and harming the bank's reputation. The admin responded by purchasing the data and leaking it. Whoops.
— briankrebs (@briankrebs) 4:16 PM ∙ Aug 12, 2022
General tech and privacy
Aggressive data broker: Kochava, an Idaho-based data broker, has sued the FTC after the US agency inquired into its data handling practices, including its sale of geolocation data. In a statement to the WSJ, Kochava called the FTC's current investigation "manipulative" and "based on completely false pretenses,"
“Kochava said it has recently introduced a new capability . . . aimed at improving consumer #privacy, a privacy block that removes health services #locationdata from its marketplace, & that the FTC doesn’t understand how its business works” #DataVampires putting up smoke&mirrors https://t.co/RlFQAFysKo
— Gert-Jan Kroese (@koekelinus) 11:26 AM ∙ Aug 16, 2022
Monero gets more private: Monero, the privacy-oriented decentralized cryptocurrency project, underwent a planned hard fork event on Saturday, introducing new features to boost its privacy and security.
Wickr gets support for military use: Amazon has launched a Wickr plugin for the Android Team Awareness Kit (ATAK), an SDK for developing smartphone geospatial infrastructure apps. ATAK is often used in developing Android apps for military use, and the Wickr plugin will allow Amazon to sell its AWS Wickr secure comms platform to the US and other NATO and non-NATO military forces. Amazon acquired Wickr in June last year.
Government, politics, and policy
Micro-grid tech tested at DEF CON: The Pentagon tested its micro-grid technology, which it plans to deploy to 134 Army bases in the coming years, at the DEF CON security conference, allowing participants to attempt to hack it, Cyberscoop reported.
Governments better at the zero trust thingey: A report published on Tuesday by Okta has found that government agencies are far ahead of private corporations when it comes to implementing zero trust architectures. From NextGov's coverage of the Okta report:
One reason the government has been ahead of industry counterparts is federal mandates regarding zero trust. In May 2021, President Joe Biden issued an executive order to strengthen federal government computer systems and networks via zero-trust architecture, among other things. In September 2021, the administration released draft zero-trust architecture guidelines. Agencies have until the end of September 2024 to meet five zero trust goals: identity, devices, networks, applications, and data.
Cybercrime and threat intel
ShinyHunters arrest: More details are emerging about the arrest and extradition procedure of Sébastien Raoult, a 21-year-old French student from the city of Epinal in eastern France, a suspected member of the ShinyHunters hacking group that was detained in Morocco last month.
Australian smisher detained: Australian police have detained a 30-year-old man for his role in a cybercrime syndicate who used SMS phishing to hack, access, and steal money from bank accounts. According to the Australian Federal Police, the group has been operating since 2018, and they began tracking the group in September 2021 as part of Operation Iasion. Another gang member, a 39-year-old from Sydney, was also detained last year in November.
Another set of malicious Python libraries: Cehckmarx's security team discovered over the weekend a PyPI account hosting a dozen malicious Python libraries that used names similar to legitimate packages. The 12 libraries initially contained functionality to collect information on infected hosts but were later updated on Sunday with a function to launch DDOS attacks against CounterStrike 1.6 gaming servers.
My developer friends, the python libraries under this account hxxps://pypi.org/user/devfather777/ downloads malware to your computer. The library names mimmick original libraries but with slight differences in spelling. Watch carefully!
— פַּיטָן (@mirac_dasmine) 9:43 PM ∙ Aug 14, 2022
In addition, DevOps security firm Snyk also made a similar finding of its own over the same weekend, finding a different PyPI account hosting another set of 12 malicious libraries, this time configured to steal Discord and Roblox credentials, along with any payment information. Checkmarx and Snyk's findings come after two incidents involving malware-laced Python libraries were also discovered last week.
BraZZZerSFF network: CSIS's Benoit Ancel has published an overview of BraZZZerSFF, a fast-flux network provided by cybercrime groups to other cybercrime groups to anonymize malicious web infrastructure. Ancel said he was able to collect information from the service for almost four years because of "a simple mistake made by a [BraZZZerSFF] operator." Ancel said he shared information obtained through this leak with industry partners and only published his findings after the misconfiguration was fixed and after the service's popularity began to decline.
New ransomware making the rounds: A new ransomware strain named IceFire is currently making the rounds. According to reports, the ransomware is being used in targeted attacks, and the group behind it is also running a "leak site" for shaming victims who refuse to pay.
@demonslay335 So, getting close to half a year when I first tweeted about this IceFire ransomware (and until now, not even one single tweet by anyone else). The gang now has a leak page too, that is a bit unusual/strange...
— MalwareHunterTeam (@malwrhunterteam) 2:21 PM ∙ Aug 16, 2022
🤔
Victims started to appear on BC forums: bleepingcomputer.com/forums/t/77581…
Old-school DDoS tools making a comeback: DDoS mitigation service Radware reported on Tuesday that old-school DDoS attack tools had made a comeback in 2022 to the detriment of IoT botnets and cloud-based DDoS services. This included simple denial-of-service tools, such as HOIC, HULK, LOIC, and Slowloris. The company attributed this comeback to the rise of a new wave of hacktivists in Asia, the Middle East, Russia, and Ukraine.
Malicious browser extensions: According to a report from Russian security firm Kaspersky, the company said it blocked more than 1.3 million users who tried to download and install malicious or unwanted browser extensions in the first half of the year. The report is based on the company's own telemetry, so the actual number is far, far larger.
The most common threat in the first half of 2022 was the WebSearch family of adware extensions, able to collect and analyze search queries and redirect users to affiliate links.
Malware technical reports
Black Basta: Deep dive into the code of the Black Basta ransomware gang.
BlackGuard infostealer: And here's a similar report on the BlackGuard infostealer, this one from F5's Aditya Sood.
SocGolish: GoDaddy's Sucuri team has published an overview of SocGolish, a JavaScript malware framework used to deliver malware to users via fake browser update sites.
Bugdrop: Mobile security firm ThreatFabric found a new Android malware dropper named BugDrop that already includes bypasses for security features found in Android 13, which is set to be released next month.
APTs and cyber-espionage
Microsoft disrupts SEABORGIUM ops: Microsoft's security team said it disrupted infrastructure used by the SEABORGIUM threat actor to launch cyber-attacks against NATO countries, particularly in the US and the UK. The group, also known as ColdRiver (Google), Callisto (F-Secure), and TA446 (Proofpoint), used LinkedIn accounts to perform reconnaissance against targeted organizations and spear-phishing emails to deliver malicious documents and links to AITM phishing sites, according to Microsoft's MSTIC team.
Shuckworm attacks: After CERT-UA published some new Gamaredon/Armageddon/Shuckworm IOCs last week, Symantec also has a report on this group's recent operations as well.
RedAlpha: Recorded Future has published a report on the recent campaigns of RedAlpha, a Chinese APT group primarily targeting humanitarian, think tank, and government organizations globally. RF analysts believe RedAlpha is made up of "contractors conducting cyber-espionage activity on behalf of the Chinese state." The company has been tracking this group since at least 2018 [PDF].
Patchwork APT: Researchers from Chinese security firm Know Chuangyu 404 Lab published a report on recent Patchwork APT attacks across South Asia.
Vulnerabilities and bug bounty
New technique: Bluefrost researchers have published details about a new technique to abuse the Windows segment heap metadata to turn a heap overflow into an overlapping chunk allocation.
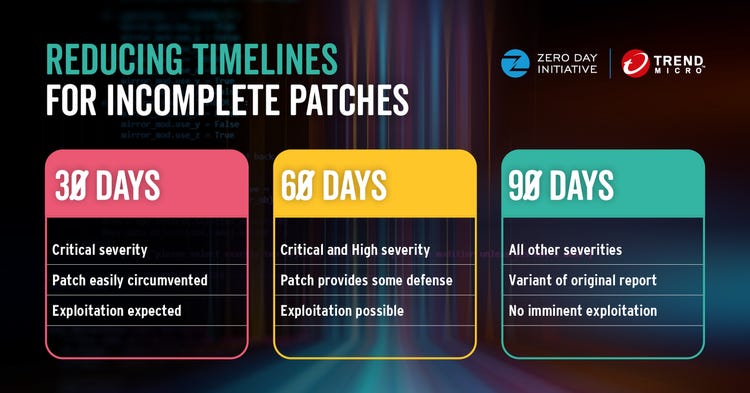
ZDI adjusts disclosure timelines: Trend Micro's Zero-Day Initiative project said last week during a presentation at the Black Hat security conference that it will change its disclosure timeline rules. Companies will still have 120 days at their disposal to fix bugs reported by ZDI representatives, but if the bug has been patched incorrectly, they will receive 30, 60, or 90 days to repatch it instead of another 120 days. ZDI said they are taking this step after seeing an increase in faulty patches. [Additional coverage in Decipher]
Infosec industry
OAN banned: Pro-Trump news outlet One America News (OAN) was banned from the DEF CON hacking conference last week for violating its privacy policy for "repeatedly taking photo and video showing people's faces without the consent of those individuals," Motherboard's Lorenzo Franceschi-Bicchierai reported.
APT activity at Black Hat: Politico reported (paywalled) last week that the Black Hat conference's security team "found malware linked to an unnamed nation state on the device of an attendee."
New tool—TeamFiltration: TrustedSec's Melvin Langvik has open-sourced a new tool named TeamFiltration, a cross-platform framework for enumerating, spraying, exfiltrating, and backdooring Office 365 AAD accounts.




